The New Battlespace: Cartels, Technology, and the Future of SOF in the Americas

Vanda Felbab-Brown, El Centro Fellow and Director of the Initiative on Nonstate Armed Actors at the Brookings Institution, and Diana Paz García, Senior Research Assistant at the Strobe Talbott Center for Security, Strategy, and Technology, examine the evolving crime-terrorism nexus in “How technology is transforming crime and terrorism.”
The authors argue that emerging technologies are reshaping how nonstate armed actors generate revenue and project power, emphasizing that “new technologies…are eroding the traditional benefits and reasons for holding territory.” Technological transformation among Transnational Criminal Organizations (TCOs) and extremist networks is a global trend, but it carries direct implications for cartel activity in Mexico and across Latin America, where groups such as the Sinaloa Cartel rely on synthetic drug production, AI-enabled fraud, and cryptocurrency laundering to reduce dependence on physical terrain while expanding their transnational operations.
Money Without Land, and Weapons without Smuggling: “New technologies, such as synthetic drugs production, digital payment systems, AI, and networked devices, are eroding the traditional benefits and reasons for holding territory, especially its role in generating revenue. AI-enabled scams, online fraud schemes, ransomware operations, and cryptocurrency-based laundering can now yield earnings larger than the taxation of legal or illegal economies…. Increasingly effective 3D printing and other forms of additive manufacturing will reduce the need to procure weapons from the illicit international market… offering advantages like self-sufficiency and simplified logistics.”
Attacks Without Bombs, and Violence Without Fighters: “Remote platforms, including inexpensive aerial drones—whether military-grade drones leaking from wars or modified commercial models—are making it possible to carry out killings and assassinations from great distances in criminal contexts, not just in wars or insurgencies. Nor will violence be limited to kamikaze drones dropping from the sky onto targeted government officials or noncompliant extortion victims. With a few keystrokes, attackers can compromise critical infrastructure… Turning ordinary household systems into instruments of lethal harm will vastly expand the tactical options and target sets for terrorists and criminals… The territorial model of terrorist finance and criminal governance has been highly labor-intensive… As everyday objects are turned into explosives and drones are used for killings and territorial control, the number of hitmen and rank-and-file combatants will shrink radically.”
Crime Without Labor: “AI systems and other technologies will allow groups to expand their operations without having to enlarge their workforce. A small number of people running automated scams, deepfake-enabled identity fraud, and algorithmic phishing can impact millions of victims at minimal cost… Paradoxically, this shift toward learner criminal operations will occur just as broad segments of the population, including many middle-class professionals, will likely face job losses driven by AI adoption.”
The cumulative effect of these shifts points to a global reconfiguration of how transnational criminal and terrorist networks define and contest power. While technology reduces dependence on territory and labor, it does not altogether eliminate the strategic value of physical space or human networks. Instead, it focuses on protecting key geographic nodes and critical data infrastructure/ecosystems that support digital and kinetic operations. For cartels in particular, this evolution suggests a hybrid model in which localized territorial control seeks outsized influence and impact through diffuse, technology-enabled revenue generation and the projection of violence across borders.
The Real Estate of Value: For some militant groups, having a rebel state with large land and people to control is their primary goal and infuses their identity… having access to a physical haven beyond the reach of law enforcement—such as territory shielded by a rival state—will continue to offer significant advantages… The world’s littorals will rise in importance. That doesn’t mean that nonstate armed actors will constantly need to possess long coastlines, but they will benefit from frequent access points… [and] remote violence and digital crime, like the overall digital economy, will depend on physical materials, data centers, and energy flows. Localities rich in critical minerals, rare earth elements, water, energy production, and data infrastructure will be priority targets for a wide range of actors.
Data: The Most Precious Asset of All: Data, and the ability to protect or exploit it, will become the most important asset. The capacity to collect information, break into rivals’ systems, and shield one’s own data from hostile breaches will define advantage… Instead of controlling large territories and managing populations at scale, militants’ and criminals’ offensive and defensive operations will increasingly revolve around dominating digital infrastructure and manipulating information flows.
For SOCSOUTH and USSOCOM, these trends demand a recalibration of how USSOF conceptualize foreign internal defense, intelligence gathering, and operational design in the Western Hemisphere. TCOs and extremist networks will continue to leverage technology to generate revenue, project power, and evade state control, which further weakens partnered nation governance capacity and legitimacy, risking the shift toward criminalized state structures if left unaddressed.
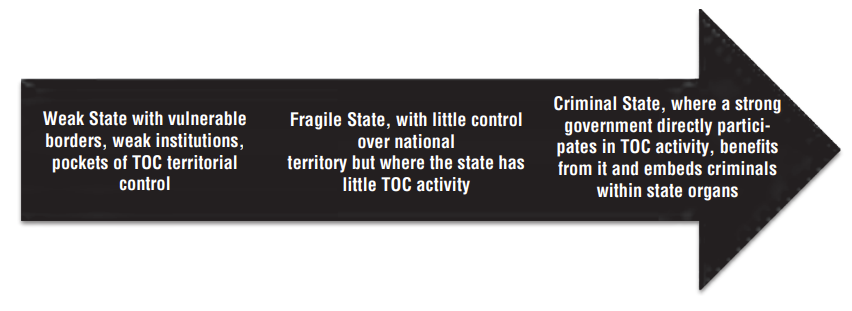
The Continuum from Weak States to Criminal States
Source: “Transnational Organized Crime, Terrorism, and Criminalized States in Latin America”
As Felbab-Brown and Paz García assess, “the fight between security services and illicit actors will pivot toward a contest over data control in a complex, crowded, and highly transparent battlefield,” where actors that can manipulate or exploit information gain decisive advantages. Cartel adaptation through low-signature, technology-enabled operations undermines approaches that prioritize territorial disruption and leadership targeting alone. USSOF must therefore bolster partner resilience by enabling their ability to operate in contested information environments, secure critical infrastructure, and counter technologically enabled coercion. The operational environment will reward forces that can identify and disrupt dispersed, multidomain threats within in a long-running competition in which advantage favors to those who can outpace its adversaries in technological adaptation.






