Terrorism and Social Media (TASMConf): International Conference - 25-26 June 2019 - Swansea University, Wales, UK - Radical Islamist Focused Presentations OSINT Listing
Robert J. Bunker and Pamela Ligouri Bunker

The 2019 Terrorism and Social Media (TASM) conference took place on 25 and 26 June 2019 at Swansea University Bay Campus, Wales, United Kingdom. The conference was organized by Swansea University’s Hillary Rodham Clinton School of Law and its Cyber Threats Research Centre (CYTREC), with the support of the VOX-Pol Network of Excellence. It brought together a broad range of researchers, policy-makers, and practitioners from a total of 23 countries, including the United Kingdom, United States, Canada, Australia, Ireland, France, Holland, Poland, Israel, and Ukraine. It featured three keynote presentations and hosted twenty-five panels with more than seventy-four other speakers over six breakout session sequences each lasting one and one-half hours over the two-day event. The conference utilized the Twitter hashtag: #TASMConf for tweets related to its activities. A selection of these tweets can be viewed here.
Keynotes were provided via the a Conversation with the Global Internet Forum to Counter Terrorism (GIFCT) panel (Dr. William McCants—Google, Dr. Erin Marie Saltman—Facebook, and Adam Hadley—Tech Against Terrorism) along with traditional presentations provided by VOX-Pol Research Fellow J.M. Berger, author of Extremism (The MIT Press, 2018), and Dr. Krisztina Huszti-Orban, adjunct professor of law and research fellow at the Human Rights Center of the University of Minnesota. An after dinner speech by Lord Alexander Carlile, former Independent Reviewer of Terrorism Legislation for the UK from 2001-2011, was also provided. Additional special elements of the conference were a pre-conference event “Advancing Collaborative Research and Understanding of Online Counterterrorism: An Evening with Facebook” and the post-conference “TASM Sandpit: An opportunity to form a team and secure funding for a research project,” supported by Swansea University’s CHERISH-Digital Economy Centre and Facebook.

Keynote Speaker: VOX-Pol Research Fellow J.M. Berger

Keynote Speaker: Human Rights Center of the University of Minnesota Research Fellow Dr. Krisztina Huszti-Orban
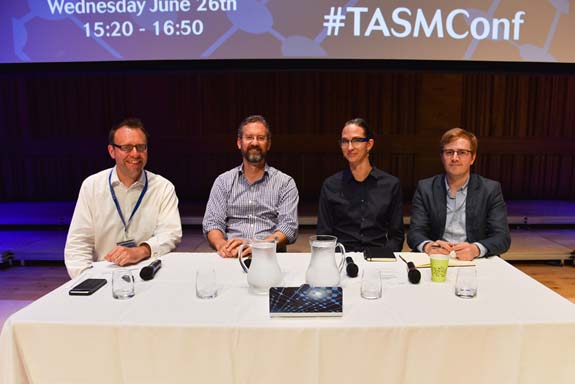
Global Internet Forum to Counter Terrorism (GIFCT) Panel (Left to Right; Prof. Stuart Macdonald—Moderator, Dr. William McCants, Dr. Erin Marie Saltman, and Adam Hadley)
Specific panels addressing radical Islamist use of social media for terrorism related purposes and Western responses were: Non-English Language Propaganda, ISIS Media Communication, Telegram, South and South-East Asia, Africa, Online ISIS Propaganda and Radicalization, Islamic State Media Output, Cyber and Influence Operations, and Videos and Videogames. Terrorist groups (Sunni) addressed in these panels are: Al Qaeda, Al-Shabaab, Ansar al-Sharia, Boko Haram, Islamic State (Daesh), and the Taliban—with IS being by far the most focused upon jihadi terrorist group covered. The radical Islamist focused presentations delivered at the conference—along with the presenter(s) name (affiliation), their Twitter ID, and presentation abstract—(per the attendee overview of breakout sessions/abstract listing) are as follows:
• Islamic State’s Hashtag War: Terrorism and the Jewish Community; Representative from the Community Security Trust; N/A;
Focusing on an Islamic State (IS) social media campaign, this presentation will track the origin and journey of a violent antisemitic IS Twitter hashtag urging attacks against Jews globally by using the hashtags #attack_theJew/#slaughter_theJew. The presentation will set out how Islamic State’s online strategy involved capitalising on an existing Twitter campaign urging attacks against Jews, and propelled it on to a global stage, stamping its authority and ownership over the campaign by appropriating violent and explicit imagery, videos and phrases that it shared amongst its global network. The presentation will set out how the IS campaign dwarfed the original local Twitter campaign and pointed towards the ability of IS to capitalise on real world events, surpass the politics and barriers of local groups and utilise social media to reach a global audience.
• Monitoring a periphery of extremism - Education of disintegration in Online Dawah Videos on German YouTube; Till J. Baaken and Friedhelm Hartwig (Modus; Centre for Applied Research on Deradicalisation); @tillbaaken & @modus_zad;
Epic stories, anāshīd and the friendly Imam from next door – Online Dawah videos are as diverse as the people watching them. These videos do not specifically endorse violence, but can serve as a gateway to interpretations of Islam, which open young people to exploration of more radical interpretations of the religion and in the worst case, towards a path of violence. Defining a periphery is one of the major challenges in the triad of freedom of religion, preventing radicalisation early on, and monitoring content by academics. Exemplified by the scene in Germany it will be discussed how a periphery of extremism engages with its audience using different forms of output online. An analysis of YouTube videos shows a wide array of content disseminated from a multitude of channels. After having examined YouTube using the method of First impression Screening (FIS) a qualitative thematic approach brings to light the hot topics, narratives, actors, and trends in this periphery. Peripheral actors show a high level of professionalism, flexibility, and creativity in reacting to the questions and needs of individuals looking for spiritual or life guidance. On the other hand, more traditional means like the singing of anāshīd as well as storytelling are employed to influence the target group emotionally. Additionally, leading German activists are well embedded in the dynamic transnational network of worldwide Salafi and Wahhabi content production such as the translation of lectures, books, sermons, videos, and images. First findings of the project in the form of a typology of different videos as well as the major trends and actors will presented
• User-generated, pro-Islamic State media in tertiary languages: Bushra and Georgian-language propaganda; Bennett Clifford (George Washington University Program on Extremism); @_bCliff;
At their peak of production, Islamic State (IS) media divisions produced and translated content into a litany of world languages, providing a worldwide, multilingual base of supporters with accessible content. “Top-down” production and dissemination of Islamic State media products in a handful of official languages—namely Arabic and English—continues to receive a lion’s share of scholarly analysis on the topic, sometimes at the expense of exploring unofficial media and media in less common languages. As a test case of how individual bases of supporters respond to the lack of officially-produced IS media in their native languages, this study analyzes a corpus of over 200 images produced by the media outlet “Bushra” (Omen) and disseminated via its Telegram channel. Analysis of this case shows that producers of tertiary language propaganda oftentimes have more leeway to blend top-down messaging with local issues and grievances. If successful, unofficial distributors can and do play a role in convincing IS central media outlets to produce official content in tertiary languages. This example of bottom-up diffusion of localized, unofficial content is highly significant for future efforts to understand the interplay between official and unofficial jihadi media.
• Berita Nusantara Dari Daulah Islam: A Qualitative Analysis of Islamic State’s Al-Fatihin Magazine; Jade Parker (Columbia University); N/A;
In 2016, the Islamic State released its first edition of Al-Fatihin magazine aimed at drawing on support for the organization in southeast Asia. The publishers then fell silent for over two years and relaunched the Indonesian-language series in 2018. In light of the formal recognition of “Islamic State - East Asia Province” by Islamic State Central in the summer of 2018, this paper seeks to provide a qualitative examination of Al-Fatihin’s social, political, and ideological themes used to target Indonesian and Malaysian-speaking audiences and contribute to the discourse on the Islamic State’s official strategic communication strategy for their southeast Asian affiliate.
• Radical Islamist English-Language Online Magazines: AQ & IS Approaches, Interactions with Perpetrators, and Futures; Pamela Ligouri Bunker (TRENDS Research & Advisory) and Robert J. Bunker (Safe Communities Institute (SCI) at the USC Price School of Public Policy); @DocBunker;
The presentation will provide an overview of a multi-year research project conducted for SSI, US Army War College resulting in the publication of two books [one published; Radical Islamist English-Language Online Magazines and one forthcoming; The Islamic State English-Language Online Magazine Rumiyah (Rome)]. It will begin with an overview of the two-linked projects and explain the place of English-language online magazines within the larger context of Radical Islamist social media. It will then give an overview of Al Qaeda and Islamic State approaches to their English- language online magazines (as well as eBooks), noting the differing strategic approaches. Selected interactions between perpetrators of terrorist incidents directed against the West and IS/Rumiyah magazine will then be discussed related to the time frame of this magazine’s publication (Sept 2016- Aug 2017). These interactions focus on perpetrator self-identification as an IS operative, known associations, contraband IS materials, and the use of magazine TTPs as well as magazine/greater IS declared links (such as the ‘Soldier of the Khilafah’ designation) back to the perpetrator. The final section of the presentation will discuss the future of radical Islamist English-language online magazine use and the benefits a magazine format has for cohesive narrative articulation versus other social media approaches.
• Transmitting the Caliphates, Real and Imagined; Haroro Ingram (George Washington University Program on Extremism), Jade Parker (Columbia University), Craig Whiteside (US Naval War College), Audrey Alexander (George Washington University Program on Extremism) and Daniele Raineri (Il Foglio);
@haroro_ingram, @cyberAOR, @CraigAWhiteside, @Aud_Alexander & @DanieleRaineri;
The Islamic State media department has morphed into a world class media enterprise with a sizable presence in local markets, concrete influence over its global media affiliates, and an expansive online presence. This research paper builds on a previous history of the media department to trace its efforts since 2016 to survive a sustained counter-terrorism campaign designed to reduce its impact on global populations. The focus of the paper is to answer questions on the organizational design, technology, and leadership of the department. Using primary source material, the research highlights the careful line Islamic State media officials walk in controlling content while still maximizing its distribution to consumers.
• From Telegram to Twitter: The Lifecycle of Daesh Propaganda Material;
Mohammed Al Darwish (M&C Saatchi World Services); N/A;
The paper examines the ways through which Daesh official media channels and “fanboys” utilise Telegram to disseminate propaganda material. The paper charts Daesh’s efforts to push its content past Telegram into Twitter and the role “fanboys” play in promoting that content. Therefore, it lists the typical life-cycle of sharing a propaganda material: from Daesh channels announcing the imminent release of a propaganda material, to fanboys urging each other to prepare to “invade” Twitter by supplying already activated Twitter accounts and passwords, to finally Daesh releasing the content and fanboys’ uploading it on multiple social media and content sharing platforms. As such, the paper looks at some of the ways Daesh sympathisers have been using popular online storage websites to multiply the content online along with their use and calls for popular hashtags to be used when sharing Daesh material on Twitter.
• ISIS Culture on Telegram; Chelsea Daymon (American University); @cldaymon;
Culture is an instrumental element in understanding the ecosystem and functions of a group. Culture provides unity, identity, and belonging, while helping to define shared patterns among members. Definitions of culture vary; however, it can be agreed that culture helps shape the customs, beliefs, and social behaviors of individuals, making it a powerful component for understanding groups. Despite its loss of territory, supporters of the Islamic State of Iraq and al-Sham (ISIS) are still active on the encrypted messaging platform Telegram. Official and semi-official channels continue to disseminate breaking news announcements, magazines, videos, photo reports, and other informational products, while pro-ISIS chats expand on these by offering a hybrid version of jihadi culture found in the online environment. There are cultural similarities between the online and offline environments, while there are also differences. Understanding jihadi culture in the online setting, is of vital importance since terror groups are utilizing platform like Telegram at an unprecedented rate. One could even argue that with its loss of territory, online jihadi culture, helps sustain ISIS in the long- term ensuring a continuation of ideas, support, and mobilization, which future groups will learn from.
• Investigating the digital caliphate on Telegram platform through the digital ethnography: from jihadi multi-level propaganda to a multi-actor service network;
Nicolò Giuseppe Spagna (Catholic University of Sacred Heart in Milan); N/A;
The study analyzes the digital jihadist movement on Telegram platform through the digital ethnography approach. The process used to collect information has involved a participant observation within the digital platform took nearly a year. The proactive monitoring has permitted to capture how jihadist movement organize the communication strategy and protect its virtual network. Relevant is the trust-building process based on the linguistic, religious and the co-optation system, important factors also for understanding the jihadi multi-level propaganda. In addition, this study shows that the jihadi extremists consider Telegram platform not a simple messaging application, but an extension of the caliphate – a sort of digital dawla - that provides several services to users (e.g., propaganda and instructions on cybersecurity, operational security, propaganda design). In other words, jihadists Telegram channels play a key role in communication between users generating a multi-services actor network.
• Evaluating local efforts in Mindanao to confront Islamic State East Asia ‘influence operations’; Haroro J. Ingram (George Washington University Program on Extremism); @haroro_ingram;
In the aftermath of the Maute-Hapilon led siege of Marawi, Philippines in 2017, local civil society groups mobilized to confront Islamic State East Asia (ISEA) ‘influence operations’ across Mindanao. The case of Islamic State East Asia in the Philippines offers important insights into the interaction of top-down (e.g. Islamic State outreach to the region) and bottom-up (e.g. local actor outreach to Islamic State) forces and its implications for how local civil society combats these threats. Drawing on the findings of an 18-month study, this paper analyses the campaign, message, roll-out and evaluation design of two civil society run campaigns that fused offline and online efforts to confront violent extremist influences in their local areas. It then presents the ‘reach’ and ‘impact’ evaluation results for each campaign and identifies key ‘lessons’ for scholars and practitioners.
• Indonesian online extremism: latest trends and techniques; Mark Wilson (Jane’s by IHS Markit); @M_DubU;
Following a spate of terror attacks in May, the Indonesian authorities renewed their online crackdown on Islamist extremism. Open source research and social media monitoring from Jane’s indicates this crackdown has been only partially effective, with online Indonesian militants still able to spread their messages on various social media platforms and websites. This briefing will explore where these online militants are currently operating online and look at the roles they play, the tactics they use to evade crackdowns, and which platforms they may be heading to next.
• The Islamic State’s Manipulation of Gender; Kiriloi M. Ingram (University of Queensland); @KiriloiIngram;
This paper analyses how Islamic State’s (IS’s) propaganda construct, use and prioritise masculine and feminine norms and practices, and explores the interrelationship of both constructed models of gender. Furthermore, it situates these dynamics within IS’s broader information operations strategy to mobilise a global audience and subsequently identifies why men, women, and their stipulated gender roles are imperative for IS as an organisation. I argue that IS constructs a Manichean perception of the world between the revered in-group and malevolent out-group. These bifurcated macro identities are subdivided into micro gendered identities, or male and female archetypes. These gender archetypes are used by IS to compel men and women to identify with in-group archetypes, to thus influence the formation of male and female audiences’ identities in order to catalyse radicalisation and mobilise support for the in-group (IS). Moreover, there is a distinct symbiotic relationship between the use and prioritisation of male and female archetypes and this interdependence enhances the overall objective of IS’s propaganda campaign: to offer audiences an alternative frame through which to understand the world and, to mobilise support for IS.
• Boko Haram’s Online Presence: An Overview; Bulama Bukarti and Mubaraz Ahmed (Tony Blair Institute for Global Change); @bulamabukarti & @MubarazAhmed;
The study of terrorist groups’ use of the internet has largely neglected the online presence of Boko Haram, whose internet-based activity stretches back to 2010, while the group’s militant activities have burgeoned beyond Nigeria and spread across the Lake Chad Basin. This paper seeks to draw the attention of academics and policymakers to the vast plethora of Boko Haram content that remains available online, in spite of international efforts to tackle terrorist groups’ exploitation of the internet. It will present an overview of the evolution of Boko Haram’s online activity, looking at how the group has used social media platforms for recruitment and propaganda purposes, the role of mainstream media outlets in amplifying the group’s messaging, and identifying the significant ideological features of the group’s propaganda. The paper will also examine the online activity of Boko Haram’s different factions, exploring the types of content they are producing, the platforms they are using, and delving deeper into the output of the factions, in particular looking at how online activity fits with the group’s broader strategy and objectives. Concomitantly, it will assess the current level of response from governments, tech companies and civil society organisations to the group’s online activities.
• Ansar al-Sharia in Tunisia’s Facebook Mobilization; Aaron Y. Zelin (Washington Institute for Near East Policy and Brandeis University); @azelin;
The 2011-2013 time frame at the outset of the Arab uprisings and before the reemergence of the Islamic State is an overlooked period in the literature on jihadi media usage, strategy, and mobilization. While most historic groups aligned with al-Qaeda remained glued to password- protected forums and subsequently adopted Twitter and Telegram in 2013-2015 for official media distribution, new ‘Ansar al-Sharia’ groups that were founded after the uprisings began to use Facebook. One case in particular is unique: Ansar al-Sharia in Tunisia (AST). AST was not based in a war zone, but in a transitioning democracy. AST was not using terrorist tactics, but attempting to conduct dawa and social service activities. AST was not a group operating as minority Muslims within society as European jihadi dawa groups had been previously. It was very much a social movement, but unlike most social movements that attempted to garner more rights and justice within society, AST was attempting to build a theocracy and shadow state. Therefore, it is not an easily compare case amongst historic jihadi groups either within the broader Middle East conflict zones or homegrown movements in the West. As a consequence, AST’s Facebook campaign had a different type of relationship to members of its group, the broader Tunisian public, as well as the global jihadi community. It allowed for different types of connections and interactions not possible with a clandestine group, one closed off to the dark corners of the Internet, or not open to society. This provided different dynamics for recruitment, mobilization, and interaction locally, which helped to strengthen bonds and connect individuals amongst current and new members of the organization that was not previously possible or has really been seen since within the jihadi milieu.
• Propaganda or Not? The Persistence of the ‘Al-Qaeda Narrative’ in Boko Haram Studies; Jacob Zenn (Georgetown University); @BokoWatch;
It has often been assumed that the public messages of Al-Qaeda and Boko Haram about each other from as early as Usama Bin Laden’s first mention of Nigeria in 2003 were bluster to exaggerate both groups’ international and expansionist credentials. However, the emergence of primary source documents of the private correspondences between these groups now reveals that most of their public messaging, in fact, corroborated what the groups were actually doing behind-the-scenes. Why would al-Qaeda telegraph the financial and training support it was providing to Boko Haram when it could tip off intelligence agencies to their activities? This article theorizes that al-Qaeda understood that intelligence agencies were already tracking their activities and its public messaging served two specific purposes: first, to alert al-Qaeda and Boko Haram members not involved in leadership decision-making about al-Qaeda’s forthcoming support; and, second, to confirm to leaders who were “in the know” that such support was bound by a public oath of commitment. The article contributes to the literature on al-Qaeda and Boko Haram and weighs in on the debate about whether primary sources from al-Qaeda and Boko Haram that are now published online are “propaganda” and academically unreliable or not. The articles also contributes to providing methods that analysts can use to distinguish between “aspirational messaging,” which is a form of propaganda, and “operational messaging,” which reflects actual operational activities.
• Between the ‘camp of falsehood’ and the ‘camp of truth’: exploitation of propaganda devices in the Dabiq online magazine; Miron Lakomy (University of Silesia); N/A;
The paper discusses results of a research project which aims to identify the most important propaganda methods exploited in the former flagship magazine of Daesh - Dabiq. The content analysis was based on the Institute for Propaganda Analysis’ concept of propaganda devices. It consisted of seven devices: name-calling, glittering generalities, transfer, testimonial, plain folks, card-stacking, and bandwagon. The research project adopted both qualitative and quantitative approaches. This paper argues that name-calling and glittering generalities, based on the use of “bad names” and “virtue words,” were among the most frequently used, in order to create a black and white vision of the world, composed of only two groups: the camp of truth (i.e. IS) and the camp of falsehood (infidels en masse). Transfer, which is defined as the use of the authority of someone widely respected, was also commonly exploited in all issues of Dabiq. It was manifested by frequent references to the Quran, Allah's commands, the Prophet's and Sahabah's actions (being “role- models”), as well as to Islamic scholars. This was done to present IS as the only “true” embodiment of the caliphate. Bandwagon, based on the use of the “follow the crowd” logic, was usually manifested by suggestions that masses of Muslims support IS and celebrate its victories. Card-stacking, defined as obvious lies, as well as testimonials, were noticeable, but much less frequent. Finally, the rarest and least important device was plain folks, whereas the mujahidin in the magazine were predominantly presented as unique and extraordinary Muslims.
• The online behaviours of Islamic State actors in America (2013-2018); Joe Whittaker (Swansea University); @CTProject_JW;
There is a considerable degree of ambiguity in Terrorism Studies and counter-terrorism practice surrounding the phrase “online radicalisation” – both in relation to the process of radicalisation itself, as well as how the Internet's role can shape it. This research adds to the dearth of empirical data by analysing the online behaviours of over 200 Islamic State terrorist actors in America, discerning their pathways into their eventual activity and assessing the role of the Internet in that pathway. Data were collected via open-sources including criminal justice documents, journalistic sources, government reports, and academic literature. Following on from the work of Gill et al. (2015), it disaggregates a number of behaviours that can be described as aspects of “online radicalisation” and offers a number of descriptive statistics and multivariate tests to offer insight on the role of the Internet in contemporary trajectories into terrorism.
• On Understanding Online Radicalism: A Case Study on ISIS Propaganda; Mariam Nouh (University of Oxford), Jason R.C. Nurse (University of Kent) and Michael Goldsmith (University of Oxford); @Mary_n0, @jasonnurse & N/A;
The Internet and Online Social Networks in particular have changed the way that terrorist and extremist groups can influence and radicalize people. Recent reports show that the mode of operation of these groups starts by exposing a wide audience to extremist material online, before migrating them to less open online platforms for further radicalization. Thus, identifying radical content online is crucial to be able to limit their reach and the spread of the extremist narrative. In this study, we identify several markers including textual, psychological, and behavioural, that together allow for the classification of radical content. We adopt a data-mining approach to computationally analyse extremist propaganda, determine a textual model of radical content, and create a psychological profile of known radicals. Our results show that radical users do exhibit distinguishable psychological properties. These properties can be utilized as signals for detecting radicalization activities. We believe that this approach will have significant implications on improving the existing efforts on detecting evidence of online radicalism and combat extremist narrative and recruitment campaigns.
• Determining the ‘Stateness’ of Islamic State According to their Video Propaganda;
Moign Khawaja (Dublin City University); @MoignKhawaja;
The birth and existence of the “Islamic State” generated a lot of international controversy, both in terms of its “Islamic” identity and its functioning as a “State.” While the Islamic aspect of IS has been highly debated, the state aspect needs to be challenged. IS supporters argue their state had its own borders, government institutions, army, and a powerful media, just like any other modern state. They also insist that almost all modern states came into existence out of terrorism and it is not just unique to IS. Many experts agree that the most accepted requirements for determining the existence, hence legitimacy, of a state in international law is the following criteria stipulated in the 1933 Montevideo Convention on the Rights and Duties of States: i) a permanent population, ii) a defined territory, iii) an effective government, and iv) a capacity to enter into relations with other states. Taking these criteria into account, can the “Islamic State” be recognised as a sovereign international state? Did the “Islamic State” manage to fulfill the statehood conditions expected from any modern state? My research aims two following objectives (i) address IS statehood claims by contrasting their propaganda videos which showcased its claims of running an effective government, depicted lifestyle of the population living within its territory, with established norms, theories and conventions of international law and diplomacy (ii) how IS effectively used social media to project its claims of statehood.
• The Islamic State Reader: Strategic communications lessons from Islamic State’s Fall & Rise & Fall, 2007-18; Haroro Ingram (George Washington University Program on Extremism), Craig Whiteside (US Naval War College) and Charlie Winter (King’s College London); @haroro_ingram, @CraigAWhiteside & @charliewinter;
Despite the flood of research that has emerged since the establishment of its so-called “caliphate” in 2014, persistent myths continue to shape public understanding of the movement now known as the Islamic State. Going beyond the descriptive and the sensationalist, our co-authored book The Islamic State Reader presents milestone doctrinal texts and media releases from Islamic State to trace the group’s path from failed pseudo-state in Iraq to standard-bearer of the global jihad. In this paper we draw on this study to identify ‘lessons’ for not only understanding the group’s approach to propaganda, especially its use of the Internet, but its implications for practitioners across civil society, public and private sectors responsible for combating the group’s ‘influence operations’.
• Online Counter-Narratives in East Africa: Successes and Challenges; Sara Zeiger (Hedayah); @sarazeiger & @Hedayah_CVE;
Despite the relatively low internet access in most East African countries, the use of online and social media spaces for recruiting young people to join Al-Shabaab has the potential to grow in the coming years. This paper will investigate the use of counter-narratives in East Africa to prevent violent extremism in the online space. The paper will leverage the existing East Africa collection in Hedayah’s Counter-Narrative Library, and draw out some recommendations for current and future online counter-narratives for the region. In addition, it will provide some preliminary analysis through 3 case studies of online counter-narratives in East Africa in terms of their effectiveness.
• @UKAgainstDaesh: Winning a Digital War?; Anna Kruglova (Queen’s University Belfast); @Anna13058990;
The question of ISIS online propaganda has been widely discussed by scholars. Significantly less attention is dedicated to attempts to counter this propaganda. While there are some works that look at the UK efforts to find an effective digital response to ISIS they normally just compare UK and US Twitter accounts but do not assess their effectiveness in relation to ISIS themselves. At the same time, since both ISIS-associated and UK-led accounts are essentially aimed at getting followers and effective delivery of their message to followers, all general criteria of successful social media marketing (followers engagement, consistency of posting, tags usage, finding the niche the balance of posting of original materials and retweeting and replying, conversational tone, right timing, visualisation, finding the style) can be applied to assess both sides’ online strategy. The goal of this research is, therefore, to assess both ISIS and UK-led accounts against those criteria and make the conclusion about the effectiveness of their social marketing strategies. The general argument of this research is that the UK marketing strategy is much less effective than the one of ISIS even after the group's defeat. From its very creation, the UK's account suffered from several serious issues which have not changed over time. They are the following: 1) Boring content; 2) Very official style; 3) Lack of interactivity; 4) Lack of attractive visual representation; 5) The content targets Western audience rather than Muslims; 6) The strategy is not adapting to changes in ISIS-led social media.
• Is Twitter a Gateway to Terrorist Propaganda? A Study of Outlinks Contained in Rumiyah- Mentioning Tweets; Stuart Macdonald (Swansea University), Daniel Grinnell (Cardiff University), Anina Kinzel (Swansea University) and Nuria Lorenzo-Dus (Swansea University); @CTProject_SM, N/A, @CTProject_AK & N/A;
This presentation focuses on the attempts by the so-called Islamic State (IS) to use Twitter to disseminate its online magazine, Rumiyah. Our previous work on this topic found that IS disseminator accounts were mostly young, had very few followers (sometimes none at all) and received few retweets. They were, in effect, throwaway accounts that were used to try and signpost users to copies of Rumiyah on other platforms. In this study, we build upon this previous work by examining this strategy in greater detail and evaluating its effectiveness. The dataset for the study consisted of a total of 11520 tweets that both mentioned the term ‘Rumiyah’ and contained an outlink. These tweets contained a total of 892 distinct outlinks. The presentation will detail the hostnames that were most commonly contained in these outlinks and the types of content that the outlinks led to, before examining in greater detail the 381 outlinks that led to a full-copy PDF of Rumiyah. Based on these findings, the presentation will conclude by evaluating Twitter’s attempts to prevent its platform being used as a gateway to jihadist propaganda and identifying challenges facing policymakers seeking to suppress such content.
• Spiders and Flies: The Use of Cyberwarfare in the online war against ISIS; Daniel Cohen (The Interdisciplinary Center (IDC) Herzliya); N/A;
One analogy for the actors arrayed on the virtual battlefield is the comparison between spiders and flies. Modern non-state actors, such as terror organizations, are reminiscent of flies – a constant nuisance carrying disease wherever they go. They are inherently flexible, operating across borders and without standard constraints. In contrast, government agencies – virtual spiders – spin their webs in strategic locations and patiently await their prey. In the world of cyber space, collaborative efforts are difficult, and it is even more difficult to collaborate in the fight against ideological terrorism. A unique recent case study illuminates the challenges faced by the U.S state department and Pentagon with the conducting of influence operations campaigns and cyber warfare attacks against the ISIS since 2015. This online campaign demonstrated the extent to which a relatively weak non-state actor – ISIS – can project power and cause damage on a global scale. The paper will examine strategies and operational activity of this unique case study that illustrates an approach whereby cyber and influence operations are conducted as two distinct offensives against a singular opponent.
• Are jihadists losing control online?; Peter King (Independent consultant); N/A;
The presentation will look at the state of play of jihadist groups' efforts to regulate the online behaviour of their supporters within their networks on social media platforms, focusing mainly on Arabic-language networks on Telegram. Specifically, it will look at Islamic State group (IS)'s attempts to prevent its supporters from engaging in any discussions online and how these appear to have failed. The presentation will discuss the disruption of networks, both in the past and today, and the impact this has had on jihadist groups' ability to control debate and keep supporters in check. It will also investigate the impact of perceived infiltration activity by intelligence agencies, both in shifting the focus of supporters' online energies and undermining trust. It will compare examples of alleged infiltration of online networks in the past with more recent allegations. Specifically, it will look at multiple allegations since late 2017 that intelligence agencies have been operating networks of online activists posing as Islamic State (IS) supporters with the aim of undermining the group and challenging it ideologically. Some have been linked with CVE efforts in the West.
• Trends in ISIS’s systemic exploitation of the web and social media; Laurence Bindner and Raphael Gluck (The JOS Project); @LoBindner & @Einfal;
The latest trends in ISIS online activities may be compared to its military and insurgency operations on the field. During a first stage, as ISIS controlled a territory, a young generation of jihadists openly took possession of parts of the digital space with an “occupation” of the web, so to speak. During a second stage, following ISIS’ military setbacks, the group morphed back into an insurgency, increasingly operating underground. A similar phenomenon seems to have taken place online, where ISIS opted for more operational security and partially migrated to encrypted apps such as Telegram. Lastly, as ISIS continues to carry out hit and run operations on the field, the group shows particular resilience and endurance in its media jihad. How does ISIS deploy tactics to circumvent censorship on major platforms? How do they use the web in a systemic approach to keep disseminating their content? How do they segment between platforms according to the types of online activities? What is ISIS’ overall digital strategy, both to spread of propaganda and from an operational capacity (in a defensive and offensive perspective)? This paper expands on several articles written by the authors, in particular “Wilayat internet: ISIS resilience across the internet and social media” focusing on the whack-a-mole game played by cyber jihadists on social media, and on the analysis of the dissemination extent and longevity across the web for jihadist materials.
• Critical Analysis of Taliban’s Videos: Intermodal Competition, Reinforcement and Conformity; Weeda Mehran and Tony Lemieux (Georgia State University); @WeedaMehran & @aflemieux;
The Taliban banned watching TV and taking photos when in power, however, after being ousted in 2001, the group has harnessed the power of stories, images, videos and anasheed to promote its propaganda campaign. There is a prolific literature on the Taliban and their propaganda material. The focus of these studies has by and large been analysing online texts, night letters and magazines, while Taliban’s videos has relatively remained under-studied. The Taliban has produced volumes of videos that depict “mujahidin’s battles”, the Emirate’s “governance” activities and training camps to mention the most prominent themes. In this paper, we analyse more than 100 Taliban videos through a multimodal/multi-semiotic critical analysis lens. This method allows us to bring into light some of the inter-modal dynamics such as reinforcement, redundancy, competition or lack of it between visual, text and audio semiotics. Taking a critical approach, the paper also discusses what is put on display and how these intermodal dynamics influence those displays.
• Call of Jihad: The gamification of violent extremism; Nick Robinson (University of Leeds), Maxime Bérubé (Université de Montréal), Imogen Richards (Deakin University) and Joe Whittaker (Swansea University); N/A, N/A, @imogen_richards & @CTProject_JW;
This presentation reviews the literature on gamification and violent extremism and describes how videogames and videogame representations are deployed on new and social media by jihadist organisations. For several years, ‘gamification’, (including elements of competition, rules of play, and point scoring), has had a discernible impact in a variety of contexts. This has been so in many online, non-gaming environments, especially when this type of engagement is facilitated by the affordances of new and social media architecture, and when the audience is receptive to gamified modes of communication (Hamari, Koivisto, & Sarsa, 2014). A review of the extant literature tells us that organisations within the global jihadist movement (GJM) are increasingly featuring gamification, and gaming-related music and imagery, in their online propaganda. This intensification of activity is in part due to the 21st century diversification of the actors involved in the production of jihadist communications, and also to the evolution of new information and communication technologies that render extremist communications widely accessible. Gaming, gamification, and its social media correlates can be broadly conceptualised as ‘influence techniques’, which have likewise been extant in far-right propaganda and that of regional jihadist organisations such as Hezbollah. Gamification on the part of the GJM and in particular ‘Islamic State’, has been comparatively recent.
• Grading the Quality of ISIS Videos: Assessing Changes in Technical Sophistication of Digital Video Propaganda Across Time; Cori E. Dauber ) and Mark D. Robinson (University of North Carolina at Chapel Hill); @CoriDauber & N/A;
Our methodology for the grading of jihadist video propaganda makes it possible to compare the relative quality of videos in a quantitative way. One potential application of this method is the development of specific “aesthetic fingerprints,” unique styles that could allow us to identify (and therefore trace) the Islamic State or AQ Hitchcock, Spielberg, or J.J. Abrams. We have continued to apply our method to videos of multiple groups, and the stark difference in rates of change across groups presents an opportunity. While HTS, or Al-Shabab, may try to imitate the qualitative successes of IS, their videos have improved gradually over a long period of time. Boko Haram, though, produced material that did not appear to change at all – until a sudden jump in quality resembling that of typical IS, complete with markers of typical IS output, apparently overnight. This suggests that individual media makers can be identified and traced. As they move, their unique aesthetic “fingerprints” will be carried with them. IS documents released by the CTC reveal a media checklist that makes the group’s quality standards clear.
An aggregate Twitter handles listing for academic and professional researchers looking at radical Islamist groups’ utilization of social media and Western responses (from the above presentations) for OSINT monitoring and tracking purposes is as follows:
@aflemieux
@Anna13058990
@Aud_Alexander
@azelin
@_bCliff
@BokoWatch
@bulamabukarti
@charliewinter
@cldaymon
@CoriDauber
@CraigAWhiteside
@CTProject_AK
@CTProject_JW
@CTProject_SM,
@cyberAOR
@DanieleRaineri
@DocBunker
@Einfal
@haroro_ingram
@Hedayah_CVE
@imogen_richards
@jasonnurse
@KiriloiIngram
@LoBindner
@Mary_n0
@M_DubU
@modus_zad
@MoignKhawaja
@MubarazAhmed
@sarazeiger
@tillbaaken
@WeedaMehran
An earlier conference—TASMConf 2017—also took place related to this subject matter (with keynote videos provided). A selection of papers from the 2017 conference was published as a special (double) issue of Studies in Conflict and Terrorism titled “Islamic States Online Activity and Responses” (Vol. 42, Iss. 1-2, 2019). For more information concerning the 2019 Terrorism and Social Media conference, email tasmconf@swansea.ac.uk.
About the Author(s)
Comments
I have recently watched a…
I have recently watched a record of this Terrorism and Social Media conference as I was preparing for my college project. As a student of Swansea University, I am pretty busy with my college assignments, and often use help of such services as https://assignmentbro.com/au/university-assignment-help to complete my assignment. I think that it is great initiative that allows students to focuse on the subjects that really matter.


