Phreaker, Maker, Hacker, Ranger: One Vision for Cyber Support to Corps and Below in 2025
Erick Waage
Overview
The operationalization of the Cyberspace Domain at the tactical-level continues to exacerbate both tactical theorists and practitioners alike. For theorists, much of this stress and anxiety stems from a deficiency in unclassified historical examples and the abstractness of cyberspace as a warfighting domain. The lack of historical examples and cross-domain nature of cyberspace makes it difficult to fit cyber-related tactical concepts into traditional doctrine. For tactical practitioners who employ troops on the battlefield, the lack of a concise and communicable Mission Essential Task List (METL) to assist commanders in understanding, visualizing, and describing operational concepts to their staffs continues to limit cyberspace integration into maneuver. The purpose of this paper is not to provide a concrete solution on which to base the tactical-level operationalization of cyberspace off of, but rather to establish an intellectual target reference point for Army thinkers to “adjust fire” off of as they develop the Army’s cyber way-ahead for the next decade. This paper proposes one hypothetical task organization structure in the form of a Cyber Electromagnetic Activities (CEMA) Troop and an example METL that could exist in the Army in 2025. Additionally, the paper offers a hypothetical operational narrative for one potential application of CEMA at the tactical-level that could become a reality for the Army over the next decade and beyond. To nest under ARCYBER’s ongoing initiative to operationalize cyberspace at the tactical edge, this paper will refer to tactical-level CEMA as Cyber Support to Corps and Below (CSCB).
Organization
The proposed CSCB Troop consists of three platoons, each consisting of three teams; an operations element with an attached liaison cell; a traditional troop headquarters element; and a command team. The CSCB Troop has coordinating relationships with CEMA Cells established at the Brigade Combat Team (BCT) level and subordinate Defensive Cyberspace Operations (DCO) sections. Below is a graphical depiction of the task organization of a CSCB Troop.

Figure 1: CSCB Troop Task Organization in 2025
Troop Composition and Coordinating Units.
- Command Team. Due to the time and experience required to develop cyberspace related skill-sets and sensitive Joint, Inter-agency, Intra-governmental, and Multi-national (JIIM) engagement requirements, the CSCB Troop will require an O-4 and E-9 to lead it.
- Headquarters Section. Traditional specialty elements, such as supply, arms room, and training room, will be housed here.
- Operations Section. The purpose of the operations element is to integrate and synchronize troop operations with the BCTs that the troop is supporting and National-level assets that are in turn supporting the troop and its customers. The operations element maintains a coordinating relationship with the BCT CEMA Cell.
- National Asset Reach-back Section (NAR). Some of the capabilities that BCT’s will require will be non-organic to the CSCB Troop and strategic in nature. The NAR will act as a conduit between the BCT CEMA Cell and the National-level service providers in the JIIM. The NAR will be able to translate tactical effect requirements from customers to strategic-level service providers.
- BCT CEMA Cell Section. Each BCT will possess a CEMA Cell primarily composed of CEMA planners as the intellectual agents, organic to the BCT, for integrating non-organic CEMA assets into BCT planning and operations. The CEMA Cell will maintain a habitual relationship with the CSCB Troop it is aligned with. The CEMA Cell will also manage the employment of the BCT’s organic DCO element.
- BCT DCO Section. Subordinate to the BCT CEMA Cell, the BCT DCO Section is organic to the BCT and will focus on defending BCT enterprise networks while it conducts both forward operations and CONUS-based rear operations.
- Fabrication and Maker Platoon (FMP). This platoon will provide technical solutions to BCTs via CSCB Troop Field Technicians. These technical solutions or tools will range from Commercial-off-the-Shelf (COTS) to Government-off-the-Shelf (GOTS) equipment and capabilities. The use of open-source hardware and software will enable the FMP to rapidly fabricate both mission-specific CEMA tools or produce multiple CEMA tools to equip its assigned BCT. FMP will be resourced with COTS/GOTS materials from a forward staged, expeditionary facility similar to the Rapid Equipping Force’s Expeditionary Lab. Acquisition for materials will follow a process similar to one employed by U.S. Special Operations Command’s Special Operations Research, Development, and Acquisition Center. If FMP cannot fabricate a tool to accomplish a tactical effect, it will pass the request up to the CSCB Troop Operations Element to determine if there is a National asset capable of achieving the requested effect. Additionally, integrating with the Joint Improvised-Threat Defeat Agency, the FMP will be able to reverse-engineer adversary technical tools collected from the field to enable the CSCB to counteract those tools or employ them for CSCB’s own use. FMP itself will be composed of three teams of equal capability.
- Field Technician Platoon (FTP). With the ability to utilize CEMA tools while employing sound fieldcraft, CSCB Troop Field Technicians will operate at the tactical edge and integrate cyberspace into maneuver. FTP will be the primary medium for small unit leaders to pass up effect requests or capability gap requirements to the CEMA Cell, CSCB Troop, and subsequently to FMP. Also, the FTP will collect adversarial technical tools from the battlefield and pass them to the FMP for reverse-engineering. A cyber leader field course, similar in spirit to the U.S. Army Ranger School, will provide fundamental small unit cyber leadership and fieldcraft to a field technician core cadre. The FTP will possess its own individual tactical equipment and mobility platforms, and it will be composed of three teams of equal capability.
- Analysis and Dissemination Platoon (ADP). The ADP will focus primarily on cyber-related monitoring and intelligence though other forms of collected intelligence will be included in production, to support the BCT’s common operating picture and leader decision-making. ADP will also act as the point of dissemination to the BCT and intelligence community. The ADP will be composed of three teams of equal capability.
FMP, FTP, and ADP Platoon Structure and Training Cycle
Each of these platoons will contain three subordinate teams: Team One, Team Two, and Team Three. Numbered teams from each platoon will work together to form a team grouping; that is FMP Team One, FTP Team One, and ADP Team One will form Team One Grouping. Team groupings (TG) will habitually work together during collective training and forward operations, but will work separately during individual training. Each TG will rotate through a three phased cycle: Individual Training Phase, Collective Training Phase, and Ready Phase. Ideally, these phases will be synchronized with supported BCTs.
CSCB Troop Organizational Placement
There are three courses of action (COAs) for location of the CSCB Troop ranging from BCT to Corps.
- COA One - Decentralization. This COA places one CSCB Troop organically into each BCT to enable operational and tactical control of the troop by the BCT commander.
- COA Two - Centralization. A centralized solution, this COA calls for the creation of one CSCB Regiment consisting of four squadrons. Each of the first three squadrons would be regionally aligned with two geographically-based Unified Combatant Commands (UCC). The fourth squadron would be aligned with U.S. Special Operations Command. Each squadron contains four CSCB Troops. The CSCB Regiment would be consolidated at Ft. Meade, MD for better access to the JIIM community. The regiment and each of its squadrons would possess an operational CONUS-based joint operations center to monitor and support operations in their assigned combatant commands.
- COA Three – Hybrid Solution. This hybrid solution consists of the creation of a CSCB Regiment consisting of three squadrons. Each squadron would be aligned with and co-located with one of the three Army Corps. The CSCB Regimental headquarters would be located at Ft. Meade, MD for better access to the JIIM community. The regiment and each of its squadrons should possess an operational CONUS-based joint operations center to monitor operations assigned to their Corps’ subordinate units.
Example CSCB Troop METL
The below non-exhaustive, example METL is derived from existing Army Tactical Tasks (ART) located in Army Universal Task List, FM 7-16, and does not include ARTs derived from the yet published FM 3-12 (Cyberspace Operations). Note that a tactical task is “a specific activity performed by a unit while executing a form of tactical operation or form of maneuver. It may be expressed as either an action by a friendly force or effects on an enemy force” (FM 7-16, 7-1). For a CSCB Troop METL, actions and effects occur either through or in cyberspace and the electromagnetic spectrum (EMS), and they may be coupled with physical, land maneuver to effectively employ tools or facilitate access to networks and sensors.
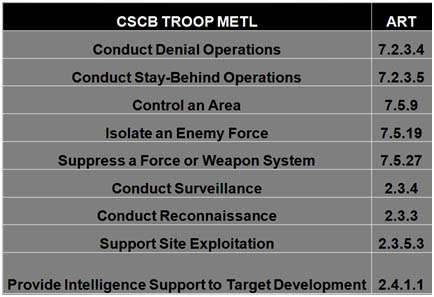
Figure 2: CSCB Troop Example METL
Hypothetical CSCB Troop Operational Narrative. This narrative is broken into five phases: identification of the capability gap, formal request, technical solution build, CSCB integration into the maneuver plan, and the afterward.
- Identifying the Capability Gap. In 2025, a company commander responsible for an Atropian town district is unable to effectively secure the district due to adversarial guerilla activity. Consequently, one of the company commander’s platoon leaders engages the attached CSCB FTP as to whether they possess a capability to identify a pattern in guerilla movements. The platoon leader states that his platoon conducted several stay-behind operations to observe guerilla movements, but effective guerilla counter-surveillance rendered the operations ineffective. The FTP lead recommends to the platoon leader and company commander that they conduct an area reconnaissance and place COTS tools to facilitate remote electronic reconnaissance. The remote electronic reconnaissance could achieve the same effect as the intended stay-behind operation, but without generating the same physical signature that the guerilla counter-surveillance is attempting to identify. Note that electronic reconnaissance is defined as the “detection, location, identification, and evaluation of foreign electromagnetic radiations” (FM 3-38, 4-6). With the company commander’s approval, the FTP lead initiates movement with his or her supporting ADP team to identify potential EMS radiations associated with the guerillas and advises the FMP team to begin building a technical solution composed of COTS hardware and software to fill the capability gap.
- Formal Request. Though the BCT S3 and S2 have not yet approved a formal request for CSCB support, the CSCB team begins initiating the analysis and pooling organic technical resources to begin building requisite tools. With ongoing assistance from the FTP lead, the requesting company commander fills out a formal effects request form on an automated system. This automated system enables visibility, validation, and/or approval from the CSCB lead field tech, battalion staff and command, BCT staff and command, CSCB Troop operations officer, and CSCB Squadron staff and command. While the request is being processed, the FMP, which has received intelligence from the ADP identifying likely guerilla EMS radiation operating on Transmission Control Protocol/Internet Protocol (TCP/IP), is building the technical solution. As the cyberspace effect will occur entirely in or through the local network, the BCT Commander possesses the requisite authority to approve the operation.
- Technical Solution Build. Given the requirement from the company commander, via the FTP lead, the FMP determines that a network of electronic reconnaissance nodes is required to characterize guerilla EMS radiations. However, to exfil the information collected from the nodes without creating a physical signature that guerilla counter-surveillance can detect, the FMP must also build its own TCP/IP-based mesh-network to remotely exfil collected information to a gateway node. The gateway node, located outside the town and guerilla counter-surveillance range, will require physical access to retrieve the collected electronic reconnaissance information. Using COTS hardware and software, the FMP team, which is co-located with the BCT headquarters, begins constructing the requisite mesh-network and electronic reconnaissance nodes.
- CSCB Integration Into Maneuver Plan. With the mesh-network and electronic reconnaissance nodes built, the FTP lead integrates the technical solution into the company’s maneuver plan. The CSCB’s support operation will take place in three phases. All three phases of the CSCB’s support operation are integrated into three chronological area reconnaissance patrols conducted into the town by the maneuver platoons with an integrated FTP team. In the first phase, an area reconnaissance patrol establishes the nodes for the mesh-network. In the second phase, a second area reconnaissance patrol embeds the electronic reconnaissance nodes into the mesh-network. In the third phase, an area reconnaissance patrol retrieves collected data from the gateway node. The electronic reconnaissance nodes accumulate information, and at a predetermined time exfil the information to the gateway node. The FTP lead then passes the information to the ADP for analysis and dissemination to the BCT CEMA Cell and CSCB troop. The below figures graphically depict the first two phases:

Figure 3: FTP Emplacement of Mesh-Network Nodes

Figure 4: FTP Emplacement of Electronic Recon Nodes
- Afterward. With the intelligence yielded from the ADP analysis and subsequent identification of guerilla movement patterns, the BCT commander orders a company raid on several specific compounds in the Atropian town district. The BCT CEMA Cell requests that the CSCB TG assist in isolating the targeted compounds by denying guerilla use of the power grid in a specific section of the town. After counsel with the FMP, FTP and ADP, the TG lead determines that they cannot support the request with the CSCB Troop’s organic assets. Further, the BCT Commander lacks the approval authority to conduct the operations due to the international borders and networks that the operations will likely cross through. The TG lead forwards the request to the CSCB Troop NAR Cell which coordinates with the JIIM for strategic-level resources, services, and approvals to fulfill the BCT CEMA Cell’s request for a tactical effect.
Conclusion
The Army and its partners in academia and industry must continue to identify ways to maintain relative advantage over our adversaries in the frayed seam between the land and cyberspace domains. The CSCB Troop organization, example CSCB Troop METL, and fictional CSCB Troop operational narrative presented in this paper are intended to demonstrate to the reader a concept, not a complete solution, for further development of CSCB doctrine, organization, training, material, leadership and education, personnel, facilities, and policy solutions.
The views expressed in this article are those of the author and do not reflect the official policy or position of the United States Military Academy, Army Cyber Command, the Department of the Army, US Cyber Command, the Department of Defense, or the US Government.
