Messengers of a Drug War in the Cyberspace: The Case of Tamaulipas
Messengers of a Drug War in the Cyberspace: The Case of Tamaulipas
Guadalupe Correa-Cabrera, Rajendra G. Kulkarni, Patrick R. Baxter, and Naoru Koizumi
This article applies Social Network Analysis (SNA) toward a preliminary understanding of the relationship between the various actors that communicate on social media platforms (essentially through Twitter), report situations of risk, and inform about matters of organized crime, violence, and insecurity in the Mexican state of Tamaulipas. The analysis finds that dynamics of violence and organized crime in this region have spilled over into the cyberspace. It also identifies a close relationship between law enforcement agents, state and local politicians, local and national reporters, “citizen journalists,” as well as key anonymous social media users that represent a variety of interests—including possibly those of corrupt authorities and even organized crime. The present study highlights the preponderance of anonymous accounts when reporting about organized crime in Tamaulipas.
Tamaulipas: A “failed state” in times of a “drug war”
Tamaulipas is a border state located in Mexico’s northeast that has been marred by extreme violence in the past decade and a half, and has experienced the presence of and confrontation among very violent groups of organized crime (frequently called “cartels”), such as Los Zetas, the Gulf Cartel, and more recently of new criminal cells. These new smaller, but still very violent criminal groups, have emerged as a result of divisions within the main regional criminal organizations that were once dominant. Such schisms have derived from territorial disputes or direct encounters with law enforcement—that at times have acted in favor of one crime group or the other—in the context of Mexico’s “drug war.”[1] It is worth mentioning that in Tamaulipas, for the past few decades, there has not been a clear distinction between political institutions, law enforcement, and organized crime. Some have even referred to Tamaulipas as a “failed state.”[2] The political protection of the so-called drug cartels that operate in this Mexican state by government authorities of all levels has been historical. In fact, the origins of the Gulf Cartel seem to be tightly linked to political power at the highest levels.[3]
Multiple homicides, kidnappings, forced disappearances, extortion practices, and a significant number of violent crimes have characterized the regular dynamics in this state during drug war times—and particularly in its main border cities (Nuevo Laredo, Reynosa and Matamoros). What is more, Tamaulipas seems to be run by parallel governments formed by criminal actors (or cartels) that have challenged the monopoly of the legitimate use of violence that the State possesses.[4] This relationship seems to have permeated deeply into the political power hub of the state of Tamaulipas as evidenced by the recent indictment of two of its former governors—Tomas Yarrington Ruvalcaba (1999-2004) and Eugenio Hernández Flores (2005-2010)—derived from their past ties with the Gulf Cartel and the Zetas.[5] Moreover, the current governor of Tamaulipas, Francisco Javier García Cabeza de Vaca is undergoing a criminal investigation and a process of impeachment. Mexico’s congress voted to impeach him on charges of money laundering, tax evasion, and organized crime.[6]
Utilization of social media in drug war times
The political, social, and criminal dynamics in Tamaulipas are vividly—and often accurately—represented in social media, particularly in Twitter, Facebook, Instagram, and a series of local blogs that specialize on reporting violent acts and situations of risk (SDRs for its acronym in Spanish). In other words, the relationship between the different political, social, and even criminal actors in drug war times—and in the current era of extreme violence in Tamaulipas—is well represented in social media, especially in Twitter. When the Zetas and the Gulf Cartel began an extremely violent dispute for Tamaulipas key territories that caused terror among the inhabitants of several cities of the state, numerous members of the civil society started to report situations of risk, mainly via Twitter. They connected through specific hashtags with other social media users located in different cities.[7]
Due to the fact that Tamaulipas citizens were extremely fearful—considering the very high levels of violence and brutality exercised by the organizations that were fighting for the control of key territories in the state—some found safety in the anonymity that Twitter allowed. They started to use this social media platform on a regular basis to alert their relatives, acquaintances, and other members of their communities about the presence of organized crime in certain zones and the occurrence of situations that could put their communities at risk. This phenomenon has been defined as “citizen journalism,” and was praised initially by many, who considered it as relevant community service and possibly a form of citizen security.[8] The first appearance of these anonymous social media “citizen journalist” accounts began around the time that Los Zetas formally split from the Gulf Cartel in early 2010.
Eventually, a greater number or “anonymous” social media (mainly Twitter) users reporting on violence and organized crime in Tamaulipas started to appear in the cyberspace. They were not necessarily “citizen journalists,” but placed or introduced themselves as part of that category. In fact, some seem to represent the interests of local or state politicians, law enforcement, and even of organized crime.[9]
A “drug war” in the cyberspace
The use of social media by criminal groups can be traced back to the “homemade confession followed by execution” videos that transnational criminal organizations started to publish online in the early 2000s, and boomed by 2010. Platforms through which social media users from “cartel-controlled” territories reported situations of risk or criminal activity—such as YouTube, Twitter, Snapchat, Instagram, Facebook, as well as the surge of a myriad of online blogs (most notably “El Blog Del Narco”)—became a window into, and subsequently, a tool for criminal groups[10] as well as their supporters (e.g., corrupt politicians). Hence, these electronic platforms became digital battlefields where messages and taunts were thrown back and forth between alleged members of criminal groups, law enforcement agents, businesspersons, and politicians of all levels.[11]
When analyzing messages in the social media about drug-related violence, organized crime in general (and drug cartels in particular) “cannot be excluded or pigeonholed into the traditional narratives of true crime and criminal justice theory. Traditional and social media have become battlefields,” where reports of security risk situations (shootouts, criminal activity, etc.) represent a form of communication that often exhibits the close relationship between criminal organizations and government players.[12]
Traditional media—such as newspapers, radio, and TV—have been subjugated and coerced by both government authorities and private criminal actors for quite some time in Tamaulipas. In this context, social media platforms (frequently used by so called “citizen journalists” reporting situations of risk) were initially considered reliable and unbiased sources of information on organized crime and drug-related violence in the state. However, “that does not seem to be the case anymore.”[13] The execution of regional individuals involved in the reporting of violent events and organized crime activity, as well as the seemingly biased content of some anonymous accounts—targeting a particular criminal organization and not all of them—appear to indicate the presence of criminal organizations in the cyberspace.[14]
Intelligence agencies and law enforcement can also take advantage of the anonymity allowed in social media to advance their objectives and conduct criminal investigations. It is possible that these agencies are conducting undercover investigations and covert operations in the cyberspace in Mexico. Moreover, it seems that violence attributed to criminal groups has been recently used to justify a militarized response by the Mexican government. One can observe actors who appear with citizen profiles, and introduce themselves as citizen journalists, but seem to have close connections with government agencies of different levels. Also worthwhile noting is the presence of social media users “with military profiles not directly associated with the armed forces, but whose activity may hint that they [keep] a direct link with the government.” Such a phenomenon of paramilitary nature in social media is known as cyberparamilitarism.[15]
Hence, one can argue that the cyberspace has acted as a new stage for what seems to be a hybrid war in Mexico,[16] and has apparently provided a testing laboratory for national security agencies, or local and state law enforcement authorities. In the context of an ostensible hybrid warfare in cyberspace, the phenomenon of cyberparamilitarism and other unconventional and counterinsurgency tactics have apparently characterized the conflict in Tamaulipas. It is plausible that some anonymous accounts—that portray themselves as citizen journalists covering security issue in this Mexican state—are really using cyberparamilitary tactics to advance the goals of state or federal law enforcement.[17]
Overall, the evolving dynamics in the state of Tamaulipas regarding security and criminal activity appear to reflect in the interactions of key players in social media (particularly in Twitter)—including accounts of politicians, law enforcement agencies/agents, activists, journalists, and anonymous accounts (representing a myriad of interests). Hence, the present analysis is an initial effort to analyze these key players, potential affiliations, networks, and roles within these networks. This is a very preliminary study about the central actors that have participated as messengers in what seems to be a hybrid cyberwar in Tamaulipas. This Mexican state has experienced extreme levels of violence and brutality, and a number of actors prefer to conduct their investigations and implement their communications strategies in the cyberspace.
Methodology
SNA of thirty actors
The present article applies Social Network Analysis (SNA)[18] to explore the relationships among different key actors who communicate in social media platforms—essentially through Twitter—about drug-related violence and organized crime activity taking place in the Mexican state of Tamaulipas. We analyze thirty Twitter accounts that we believe are among the most relevant ones for this study.
The selection of these accounts involved several steps and a process of “media curation”, i.e., frequent monitoring of networks and key accounts tweeting about organized crime and violence in Tamaulipas for approximately 10 years (since April 2010).[19] We first generated five classes of Twitter accounts representing the major groups of actors that interact in the cyberspace, performing a particular role in the so-called drug war. This classification included: i) government authorities, ii) law enforcement agents/agencies, iii) federal and local politicians, iv) journalists, and v) anonymous Twitter users. The last category was divided into three subgroups of actors who were possibly: a) citizen journalists, b) law enforcement undercover agents, or c) members of criminal groups.[20]
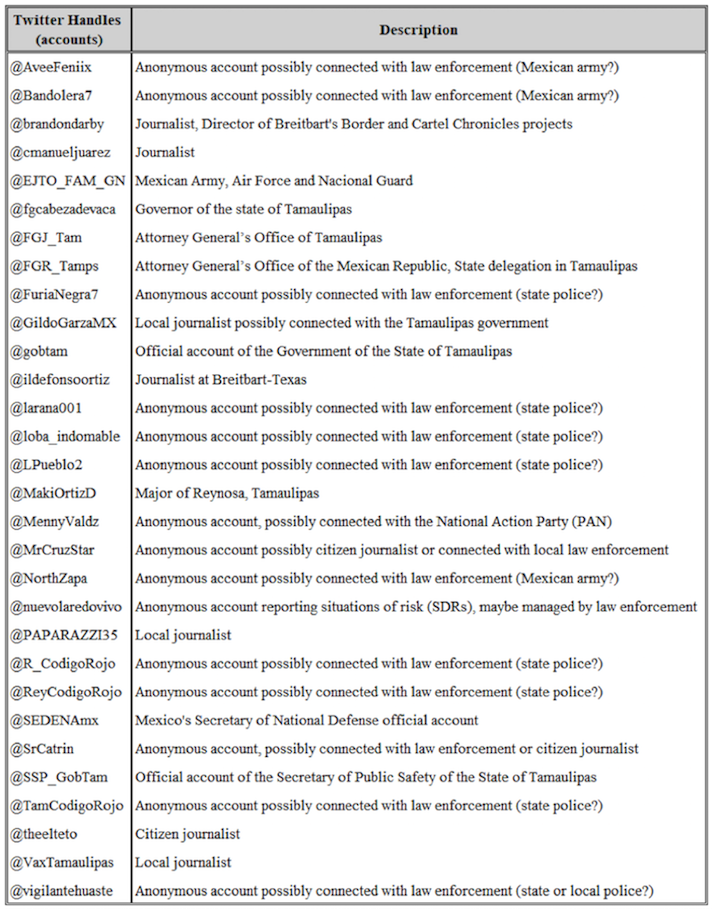
In the initial set, the first four categories included 25 accounts each, while the last group was comprised of 75 accounts, which were divided into the three subgroups. This list was shared with an expert on security in Tamaulipas who had been involved in the same type of social media curation process as the one performed for the present project. We then analyzed the general content of tweets by each of these accounts, from which we selected what we believed were the most relevant accounts. In this process, those accounts deactivated by users and cancelled by Twitter, as well the accounts whose tweets do not focus mainly on Tamaulipas were removed. This set included 138 accounts (see Appendix 1) on which we applied SNA.[21] The list was then reduced to thirty accounts based on the results of the preliminary SNA and our knowledge of the network—obtained after 10 years of monitoring its activities. For clarity purposes and for a better visualization of the network, the least relevant/central accounts in the previous exercises were eliminated.[22] Below is the list of the thirty accounts and a general description of their activities or alleged professional roles (see Table 1).
This list included a number of anonymous accounts, such as @AveeFeniix, @Bandolera7, @FuriaNegra7, @larana001, @loba_indomable, @LPueblo2, @MennyValdz, @MrCruzStar, @NorthZapa, @nuevolaredovivo, @R_CodigoRojo, @ReyCodigoRojo, @SrCatrin, @TamCodigoRojo, @theelteto, and @vigilantehuaste. Most of these accounts focus almost exclusively on reporting about situations of risk, organized crime activities, confrontations between criminal organizations, and encounters of criminal groups with law enforcement. The content of their communications includes gore and blood videos and photographs that present a situation of maximum alert/fear in Tamaulipas; some of these images seem to have been captured by law enforcement or criminal paramilitary groups in the first place (see examples in Appendix 2).
The description of the alleged professional roles of these Twitter accounts required a thorough analysis of the content of their communications and a careful monitoring of their interactions (see Table 1). The networks of these anonymous accounts, their followers and “accounts they follow” also informed us of their possible objectives and agendas. Some of them appeared to be more connected with the goals of certain politicians, law enforcement and criminal groups than those of service/community work. Moreover, some of the narratives created in the cyberspace related to Tamaulipas security issues appeared to be the work of the military, law enforcement, and/or intelligence agencies, while others appeared to be the real actions of criminals or members of the civil society. It is worth noting that these are preliminary observations. In the present study, attribution was not always possible with the available information. This has to do with the fact that most of the events analyzed here are possibly connected to organized crime and illicit activities, which are difficult to assess with complete accuracy.
Table 1. Thirty Twitter Accounts
Social Network Analysis (SNA)
Thirty Twitter accounts associated with key actors specified in Table 1 were analyzed. There are a number of properties associated with each Twitter account: For example, each Twitter account “follows” other Twitter users and has specific “followers.” We extracted the number of other Twitters accounts that each of the thirty Twitter accounts “follows.” The analysis was carried out using the “follow” network built from the thirty Twitter accounts. The time period of analysis was 3 January 2020 to 19 April 2020. The Twitter “follow” and “followers” lists were extracted with Python script (https://www.python.org/) on an Anaconda/Spyder platform (https://anaconda.org/anaconda/spyder). The output was processed and the networks were visualized and analyzed using the social network analysis software Gephi (https://gephi.org).
The remainder of this section describes key concepts of our methodology with the help of a hypothetical “follow” network, and presents the outcomes related to the “follow” network of the thirty Twitter accounts. Note that, by definition, a “follow” network is a directed network where an edge connecting two nodes has a direction, typically from a Twitter account (source node) to another Twitter account (target node).[23]
Consider a “follow” network G (N, E) where N represents number of “nodes” and E are directed “edges” (connections with a direction) between these N nodes. The G (N, E) directed network is built using the “follow” property of pre-selected S Twitter accounts and their T Twitter followers defined as:
?=,,?-1., ,?-2.,⋯,,?–?.,⋯,?–?.. ,
?=,,?-1., ,?-2.,⋯,,?–?.,⋯,?–?.. ,
#,?.=? and #,?.=?, then
?=#,?.+#,?.=?+?, and
T >> S
Assume the number of target nodes is greater than the number of source nodes, then one of the plausible “follow” network has each of the “source nodes” (S) connected to all “target nodes” (T), then the total number of edges E = #(S) * #(T) = n * m. For example, consider a 5 node network consisting of 2 source nodes (S1and S2) and three target nodes (T1, T2, T3), such that each source node follows all 3 target nodes; in that case, the total number of edges are: 2 * 3 = 6.However, that is just one plausible configuration among many. The other configurations could be: each source node follows different set of target nodes, for example, S1follows T1 and T2 while S2 follows T3. In that case the total number of edges is just 3.
Yet another configuration is such that S1 follows T1 and T2, while S2 follows T2, T3, and S1. Thus, the total number of edges is 5. Alternately, both S1 and S2 not only follow all three target nodes, but they also follow each other. Then the total number of edges is 8. In brief, depending on the configurations, the same set of source and target nodes may have total number of edges that as few as 3 to as many as 8. In general, the total number of edges between n source nodes and m target nodes may be expressed as:
? ⋛( ? ∗ ?)..[24]
Next, we briefly discuss the properties associated with a directed network.
In- and out-degree
“In-degree” [Id] of a node refers to number of in-coming connections from other nodes, while “out-degree” [Od] refers to number of out-going connections from a node to other nodes. In the case of a Twitter follow network G (N, E) with a set of S source nodes and a set of T target nodes, the following holds:
For any source node Si, the out-degree Od (Si) is at least 1 and may be as high as (n-1) + m.
The latter case represents the situation where a source node has out-going connections to not only all the target nodes m, but also to all other source nodes, excluding itself. On the other hand, a source node Si may have in-degree that ranges between zero and (n-1).
Id (Si) = {0, 1, … , n-1}.
The cases of zero and n-1 occur when no other source node has out-going connections to Si and when all other source nodes have out-going connections to Si, respectively.
For any target node Tj, the in-degree Id (Tj) = {1, … , n}. The lower and upper bound cases of 1 and n occur when only a single source node Si has out-going connection to Tj and when each of the n source nodes has one out-going connection to a target node Tj, respectively. For any target node Tj, its out-degree is always zero, i.e., Od (Tj) = 0.
Degree centrality
In the case of an undirected network, i.e., where the connections have no directions, the ‘degree centrality’ of a node is measured as the total number of edges that the node has.[25] It is used as an indicator of how influential a node is; the higher the degree, the more influence that node may have in the network. For directed networks, there are two sets of degree centrality measures, one for the ‘in-degree’ and the other for the ‘out-degree’. The number of incoming connections or in-degree measure of a node represents the degree of “popularity” of that node in the network. The out-degree measure of a node represents how “social” that node is in the network. The two statistics are reported in our analysis. In the context of the present study, the out-degree measure reports the total number of outgoing connections associated with each of the thirty selected Twitter profiles, that is, the total number of accounts a specific user follows. In-degree reflects how many of the initial thirty identified users follow a particular account of interest. It is worth nothing that for each Twitter user account, we extracted only the other Twitter user accounts that a specific user follows, and do not extract who that users’ “followers” are.[26]
Network path length
In a directed network, a path is defined as a directed chain of interconnections, starting with a source node Siand ending in a target node Tj, where the chain of interconnections are facilitated by zero or more other source nodes. Thus, for a Twitter follow network G (N, E), the shortest path could be one, connecting the source and the target nodes directly, while, in an extreme case, the shortest path could be n, in which case a source node Si is connected to the target node Tj through a series of interconnections involving all other n-1 source nodes Sj≠i. The shortest path is the main factor determining the score of betweenness node centrality for each node. Betweenness node centrality, which is explained next, is one of the measures that the current study used to evaluate the level of influence that each node has in the network.
Betweenness node centrality
For each node k, in a network of N nodes, its betweenness node centrality BNC(k) score is measured as the number of times that node appears in all the shortest paths Pi,j between any two nodes i and j found in the network where:
???,?.=,? ≠? ≠? –,?–?,?..
The node that appears in the shortest paths most frequently is considered to be the most central node in that network. In a social network analysis, the betweenness score of a node is another way to measure how influential that node is in that network.
Bridging centrality
Bridging centrality of a node represents the ability of that node to serve as a bridge between different densely connected parts of a network.[27] Each densely connected part is also referred to as a “community” where the nodes within each community have similar connectivity[28] Bridging centrality (BC) of a node is computed as a combination of two properties, BNC as described above and bridging coefficient (BCoeff) of the node:
??(?–?.)= ???,,?–?.. ×??????,,?–?..
While BNC is a global property representing the relative importance of the node in comparison to all other nodes in the network, BCoeff is a local property representing the relative importance of the node in comparison to the connected nodes only. BCoeff is calculated as:
??(?–?.)= ???,,?–?.. ×??????,,?–?..
Thus, bridging centrality (BC) measures the rate of incoming information that the node blocks from outflowing to other connected nodes. The higher the value of BC, the more critical the node is in limiting the global flow of information. It is similar to a bridge, which connects two or more population centers on either side of the bridge. The bridge can become a bottleneck and thus is a critical node in that network. In the present work, we will identify which node among all the nodes is the bridge node in the Tamaulipas network.
Results
Classification of actors
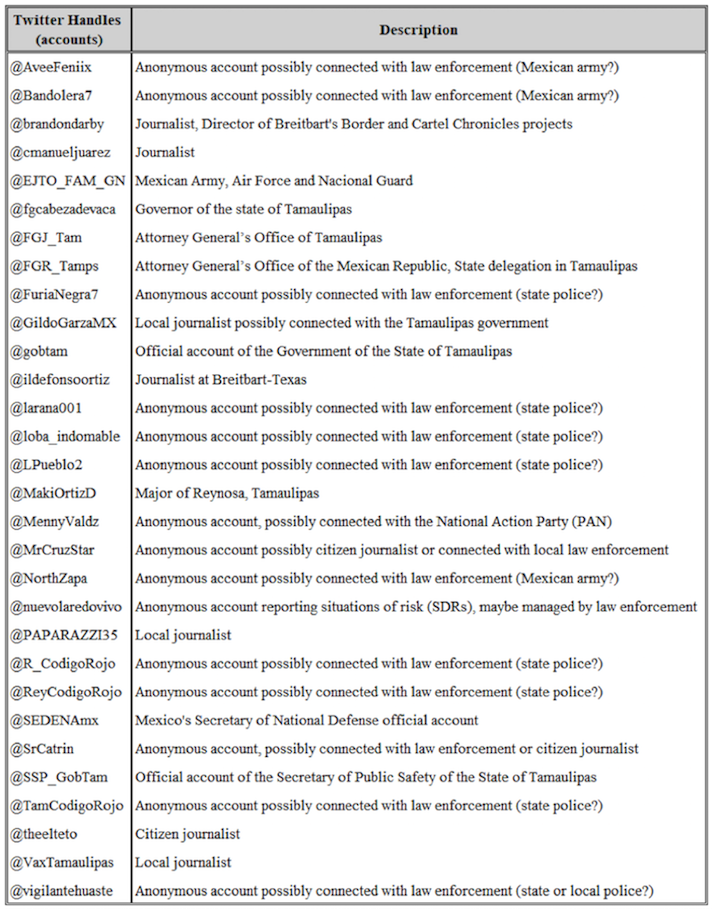
After analyzing in- and out- degree connections of the thirty Twitter accounts selected for this study, three clear actor classifications emerged. They are summarized in Table 2.
Table 2. Actor Classification
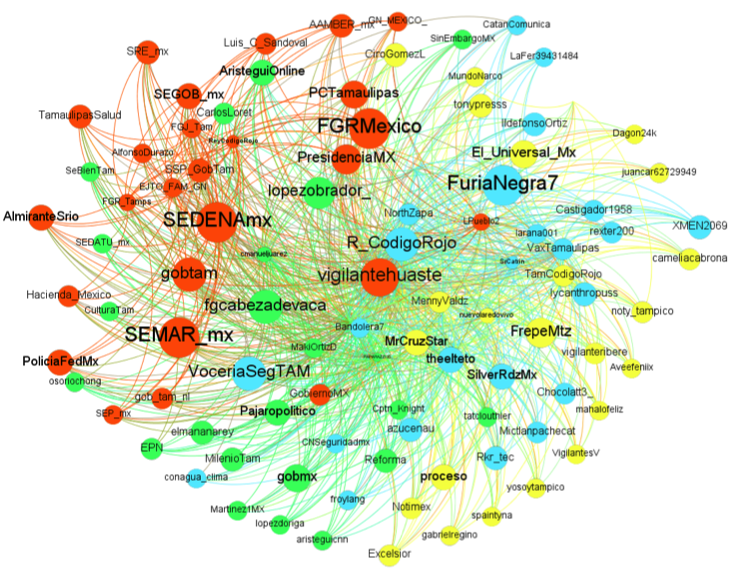
Overall Tamaulipas network
Figures 1 and 2 visualize the in- and out-degree networks of the core users. In total, 21,917 nodes were identified, with 28,935 links connecting the network over 11 distinct communities (represented by each color) interconnected with average path length of 3.8 (i.e., on average shortest path between any two random nodes is connected via 3.8 nodes). The distribution of the path length was skewed with the furthest is connected via five (5) accounts and the majority is connected via 3-4.5 accounts. In the figures, those accounts reporting more connections are presented in larger font.
Examples of key actors include @MrCruzStar—an anonymous account, who tweets and follows a vast number of Twitter accounts within this network (6,721 followers, with 12 direct follows). Similarly, @vigilantehuaste (2199, 18), @R_CodigoRojo (504, 16), @FuriaNegra7 (180, 19), and @fdcabezadevaca (415, 16), all are heavily connected within the community. Most of these accounts are anonymous, except @fdcabezadevaca, which is the official account of the governor of the state of Tamaulipas.
Key preachers include @FGRMexico, @SEMAR_mx, @SEDENAmx, @VoceriaSegTAM, and @gobtam; all are followed by 16 or more key actors in the network. This means that Twitter accounts of government agencies or those representing law enforcement agencies, the military and the navy serve as reference to other accounts interested in the topic of security.
Key followers include @theelteto, @brandomdarby, @GildoGarzaMX, @PAPARAZZI35, @AveeFeniix, @MennyValdz, @Bandolera7, and @cmanueljuarez, all with at least 1,000 out-degree connections, who follow less than 10 key actors in the community. This list includes anonymous accounts possibly connected with law enforcement and journalists (most of them local).
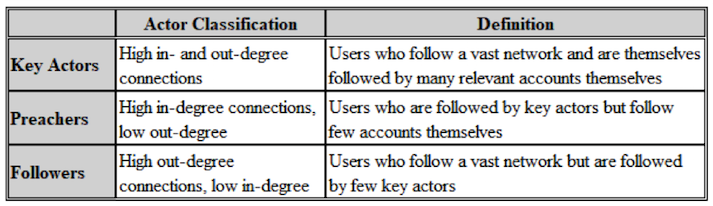
The centrality statistic is perhaps the most interesting one, crediting five users. @vigilantehuaste, @theelteo, @PAPARAZZI35, @MennyValdz, and @MrCruzStar together comprise roughly 65% of the central network of these key actors, reported in Table 3 below. It is worth noting that most of these central actors are anonymous accounts, who seem to have a variety of interests—and not all of them seem to be connected.
Table 3. Central Network Statistic
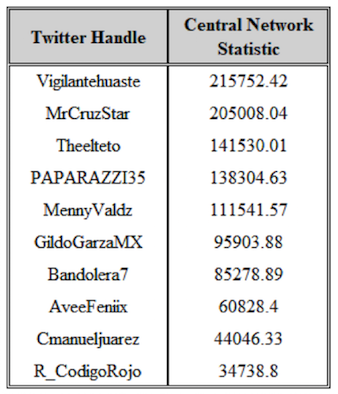
Figure 1. In-Degree Complete Network of Key Actors
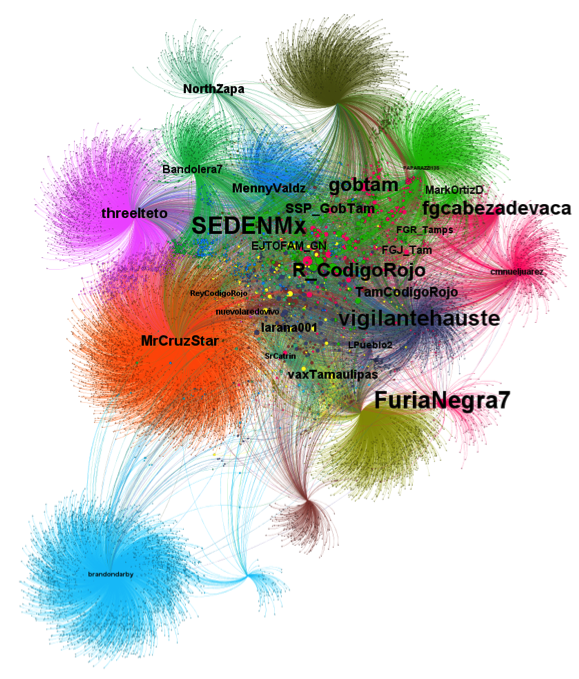
Figure 2. Out-Degree Complete Network of Key Actors
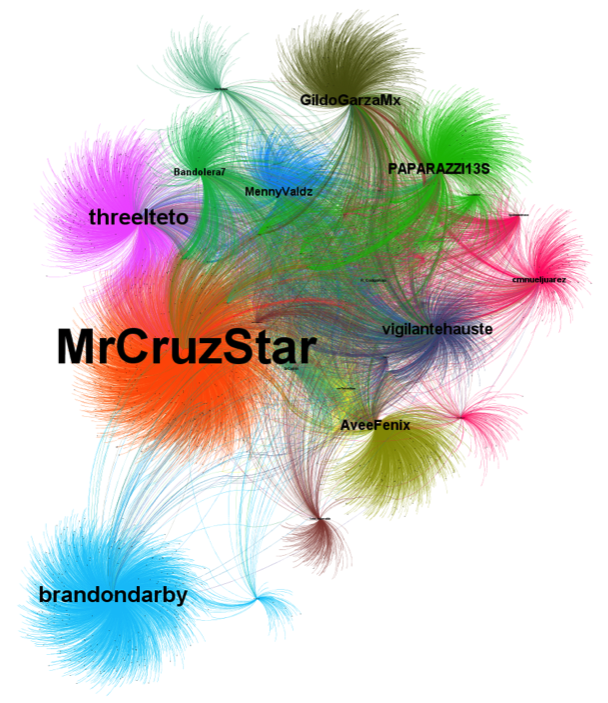
Highly connected Tamaulipas network
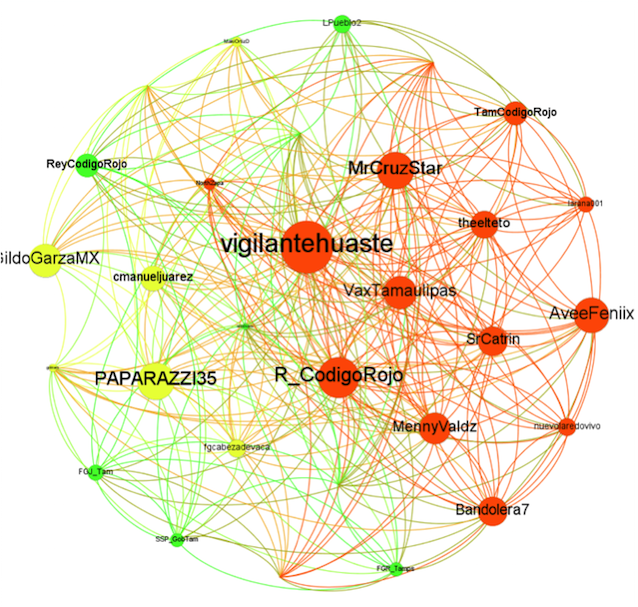
Figures 3 and 4 report overall in- and out-degree measures for each of the core users. Here, we limited the social network analysis to include only those actors[29] with 14 or more connections. The network connecting the 30 identified nodes had 3 distinctive communities (represented by a different color) and 310 edges in total. The orange community includes essentially anonymous accounts, the yellow community includes journalists and politicians, and the green community is mainly formed by accounts of law enforcement (federal and state). The average path length of the network was 1.42. In the figures, those accounts reporting more connections are represented in larger font.
Examples of key actors include @MrCruzStar—an anonymous account who tweets and follows a vast number of Twitter accounts within this network (19 followers, with 12 direct follows). Similarly, @vigilantehuaste (27, 17), @R_CodigoRojo (21, 15), and @VaxTamaulipas (17, 10), all are heavily connected within the community. It is interesting that most of these key accounts are anonymous.
Key preachers include again mostly accounts of state and federal government agencies, law enforcement, the Mexican military and navy, such as @FGRMexico, @SEMAR_mx, @SEDENAmx, @VoceriaSegTAM, and @gobtam. They follow 16 or more key actors in the network.
Key followers include @PAPARAZZI35, @AveeFeniix, @GildoGarzaMX, @MennyValdz, @SRCatrin, and @Bandolera17, all with at least 15 out-degree connections, who follow less than 10 key actors in the community. The centrality statistic is perhaps the most interesting, crediting @vigilantehuaste, @R_CodigoRojo, and @MrCruzStar. The three together comprise roughly 50% of the central network of these key actors (see Table 4 below). It is worth noting that also according to these indicators, the majority of the most relevant accounts are anonymous ones. These tendencies are maintained (more or less), when the social network analysis includes some accounts with less than 14 connections within the community (for example, see Appendix 3: SNA of accounts with 9 or more connections). The communities identified in most of these exercises differentiate between government/law enforcement accounts (orange), journalists (green), and two big groups of anonymous accounts (blue and yellow). These two communities formed mainly by anonymous accounts might be connected with two different groups or actors: i) state or local government officials, or ii) citizen journalists having nothing to do with law enforcement or local politicians. There is also the possibility that these communities include criminal actors.
Table 4. Central Network Statistic (14 or more connections)
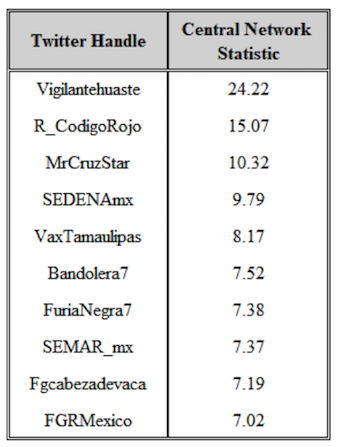
Figure 3. In-Degree Complete Network of Key Actors (14 or more connections)
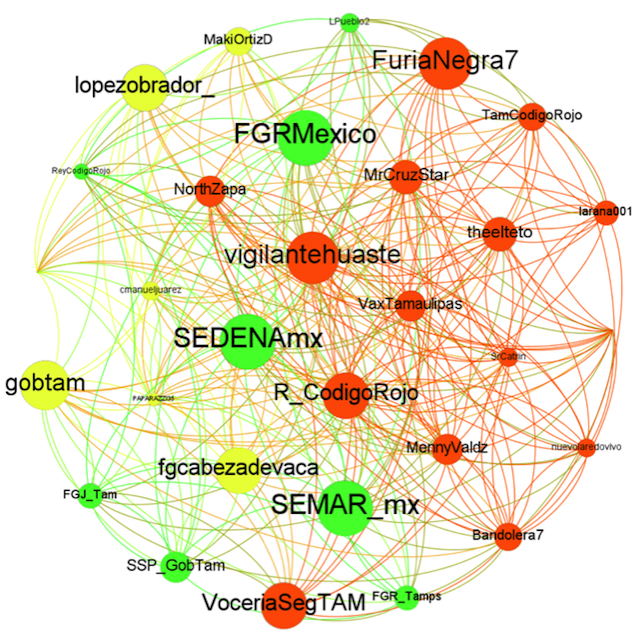
Figure 4. Out-Degree Complete Network of Key Actors (14 or more connections)
Bridge Centrality Index
When the BC index is computed for all the actors (nodes) of the Tamaulipas network, a new key actor emerges based on its relatively high bridge centrality measure. Highlighted in Figure 5, @Larana001 accounts for nearly all the bridge centrality, valuing nearly 27 times that of @TamCodigoRojo and 200 times that of @fgcabezdevaca (the account of the governor of Tamaulipas), bridging roughly 12,331 nodes (~56%) and 18,568 links (~64%) connected within two degrees of separation. It is worth noting that most of the accounts that appear below are directly linked or “allegedly” connected with the government of the state of Tamaulipas
Table 5. Bridge Centrality Index

Figure 5. Bridge Centrality Index of Key Users

Discussion
The present study analyzed the partial network of cyberspace communicators interested in matters of organized crime and drug-related violence in the Mexican state of Tamaulipas. In other words, this work was the first attempt to analyze the network of messengers of a drug war in the cyberspace. From a list of thirty relevant Twitter accounts that inform about—or are interested in—matters of security and organized crime in Tamaulipas, we identified key actors, their relevance and general roles within the network (as “preachers” or “followers”).
Overall, a social network analysis of these Twitter accounts demonstrated the presence of different communities of actors depending on their professional goals and agendas (journalists, government actors and distinct communities of private anonymous actors). At the same time, such analysis highlighted the preponderance of anonymous accounts reporting situations of risk or brutal actions of organized crime with agendas that are not clear at first sight. After a process known as media curation[30] and the conduction of informal content analysis, it appears that many of these accounts are connected with law enforcement, particularly state or local law enforcement. Many of these accounts seem to get their information from official sources or government agencies. The information obtained is still preliminary and therefore it is still difficult to allege the consistent presence of cyberparamilitarism.[31] However, there are some elements that point into that direction. A systematic effort to conduct a thorough content analysis of the messages communicated by these accounts as well as an increase in the sample size of relevant accounts are warranted to better capture the dynamics of the network.
Social media platforms such as Twitter can show us the tacit relationships between key government actors—such as Mexico’s military (SEDENA and SEMAR) and the Attorney General’s Office (Fiscalía General de la República, FGR)—, security agencies, state police, state and local governments, journalists, and seemingly private individuals—whose publications seem to be privy to exclusive, off the record information, and tend to be centered around crime alerts, security policies, and political events. While this may seem run-of-the-mill reporting, one hypothesis could be that the relationship between security agencies, state officials, and these private users might be an example of the “weaponization” of social media by organized crime groups to achieve goals beyond the drug trade, in complicity with political actors. This does not seem implausible considering that two former Tamaulipas governors were indicted in the United States for money laundering and connection with organized crime, and one—the current governor of the state, Francisco Javier García Cabeza de Vaca—is in the process of being impeached in Mexico for similar reasons.
It is also very important to monitor the activity, language, and content of the Twitter messages more closely, as well as the images shared by the anonymous accounts that focus almost exclusively on reporting situations of risk and activity of certain groups of organized crime in the state of Tamaulipas. We included several of these accounts in the current study and they ended up being central in the present social network analysis. Most of these anonymous accounts present themselves as “citizen journalists” and some of them might be independent, while others might work for different interests, including government agencies or even for criminal groups. The days of shock/gore videos and so-called citizen journalist reporting—once very frequent in Tamaulipas (Nava 2011)—seem to be gone. The current armed actors in Tamaulipas (including armed forces, the state police, drug cartels and criminal paramilitary groups) “have adopted and molded the cyberspace into another battlefield through which the aim is to achieve a myriad of goals in a seemingly bloodless campaign” (Nava 2020).
For example, certain (but not all) anonymous accounts that portray themselves as “citizen journalists” are also responsible for creating and reinforcing a narrative about the nature and prevalence of organized crime that seem convenient for particular interests (maybe related to government agencies, maybe criminal groups or maybe both). This type of accounts, apparently based in Tamaulipas, often provide selective coverage of primarily the aftermath of acts of violence. However, this coverage is not always reliable. Consider, for instance, the following episode:
As observed on September 5, 2019, in Col. Valle de Anahuac in Nuevo Laredo, several particularly prominent anonymous “citizen journalists” reported information about supposed chases and confrontations preceding a supposed shootout between CAIET [Centro de Análisis, Información y Estudios de Tamaulipas], an elite police unit reporting directly to the governor of Tamaulipas and what were initially reported as members of the elite inner circle, Tropa del Infierno, of the Cartel del Noreste (CDN), a faction of the now-defunct Los Zetas. These accounts published photographs showing the bodies of seven individuals dressed in military-style uniforms with weapons nearby and reported that these young men and women were elite sicarios killed in a shootout with police. It was later revealed that the police had kidnapped these individuals, forced them to dress in military-style uniforms, and then executed them all at different locations in and around the house. From surveillance footage, it was later revealed that the police even towed a vehicle to the crime scene, which was supposedly involved in the chase and confrontation. After this information was widely reported in the Mexican media, these accounts that were involved in fabricating the story about a confrontation went on the attack against the local human rights defender. They claimed he was corrupt and that the evidence did not really show what Tamaulipas investigators later determined was evidence: that eight CAIET officers had been involved in a conspiracy to commit these extrajudicial executions. Arrest warrants were issued for these eight officers.[32]
These anonymous accounts are possibly connected to the Tamaulipas state police and state government overall, and some of them are included in the present analysis. Their Twitter messages show a bias in favor of the actions of the Tamaulipas police—and particularly of its elite body, previously called CAIET (Center for Analysis, Information and Studies or Centro de Análisis, Información y Estudios de Tamaulipas), now known as GOPES.[33] This elite police has been linked to a number of high-level crimes and has been accused of maintaining connections with organized crime. Hence some social media users analyzed here might also be connected with criminal groups (local or transnational). In Tamaulipas, there is no clear distinction between politics/law enforcement and organized crime. Hence, these dynamics seem to be reproduced in the cyberspace. Some of the accounts we have analyzed might be also linked to criminal groups or so-called cartels.
The present study shows the relative greater significance of anonymous accounts in overall communications through Twitter regarding violence, insecurity and organized crime in Tamaulipas, Mexico. There seems to be coordinated messaging between the governor of this state, anonymous (maybe paramilitary) social media accounts, and local journalists. It is worth noting that not all the anonymous accounts included in this study are necessarily connected with law enforcement. Some of these accounts might be genuinely “citizen journalists.” Some of them started to report situations of risk in a systematic way since 2010. That is the case of @MrCruzStar, who was clearly a “citizen journalist” in the first years of the armed conflict in Tamaulipas.
It is difficult to assert “who is who” in the cyberspace, particularly when reporting about organized crime, drug trafficking, and illicit activities in general. It is thus important to do further research on this subject, analyze larger networks, and assess them at different moments in time. The actors, motives, and relationships associated with these phenomena change and evolve over time. Individuals and groups come and go; power structures change; political and strategic alliances form and dissolve. One should then continue monitoring communications in social media platforms connected to matters of security and organized crime in extremely violent regions of states like Tamaulipas. What happens in the cyberspace seem to resemble what happens in real life. The present study shows how the drug war in Tamaulipas has also turned into a cyberwar.
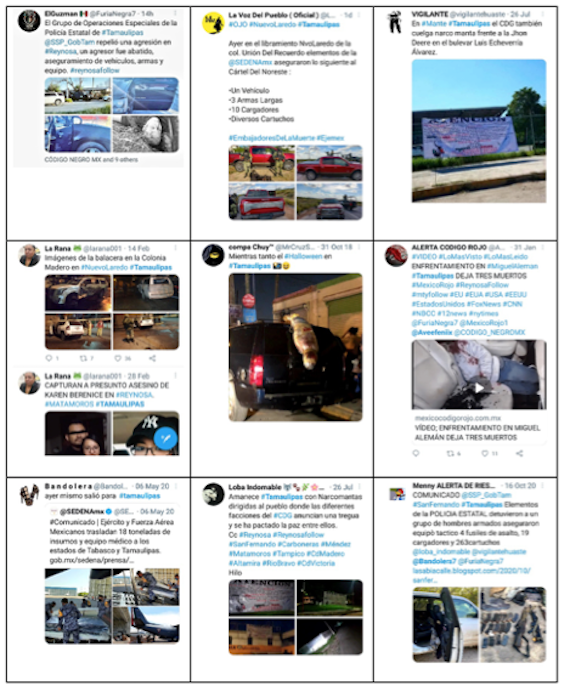
Appendix 1: Original List of Accounts Related to Security Issues in Tamaulipas (138)
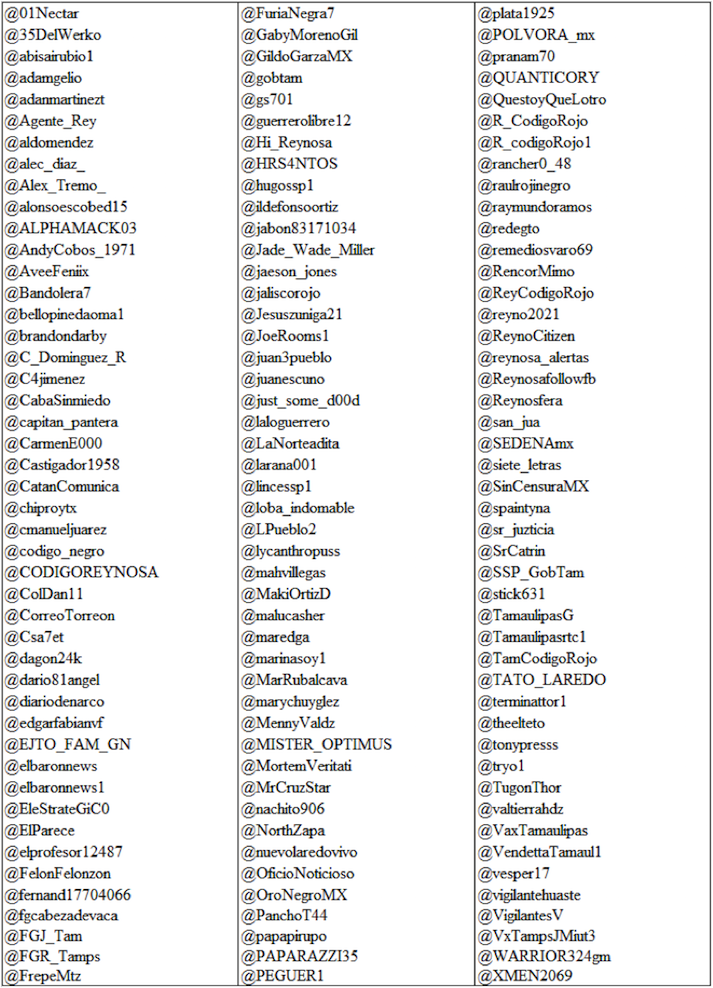
Appendix 2: The Messages of Anonymous Accounts
Appendix 3: SNA of Accounts with 9 or more connections within the community
Figure A1. In-Degree Complexity Network of Actors (9 or more connections)

Figure A2. Out-Degree Complete Network of Key Actors (9 or more connections)
Keywords: Social Network Analysis, social media, Twitter, organized crime, Tamaulipas
Acknowledgements: The authors thank José Nava for his help identifying the Twitter accounts used in the present study, and analyzing dynamics in the cyberspace related to security issues and criminal activity in Tamaulipas. We also thank Hadiyyah Abdul-Jalaal for her value work as research assistant for this project.
Endnotes
[1] Guadalupe Correa-Cabrera, Guadalupe. “Violence on the ‘Forgotten’ Border: Mexico’s Drug War, the State, and the Paramilitarization of Organized Crime in Tamaulipas in a ‘New Democratic Era.’” Journal of Borderlands Studies. Vol. 29, no. 4. November 2014: pp. 419-433, https://www.tandfonline.com/doi/abs/10.1080/08865655.2014.982888.
[2] Gary Hale. “A ‘Failed State’ in Mexico: Tamaulipas Declares itself Ungovernable.” James A. Baker III Institute for Public Policy, Rice University. 25 July 2010, https://www.bakerinstitute.org/files/466/.
[3] Carlos Antonio Flores Pérez, “Political protection and the origins of the Gulf Cartel.” Crime, Law and Social Change. Vol. 61, no. 5. 2014: pp. 517–539, https://www.semanticscholar.org/paper/Political-protection-and-the-origins-of-the-Gulf-Pérez/114f7f6eb85a72708d2859cbf6af3b7807ea5ceb. Also see, Carlos Antonio Flores Pérez, Historias de Polvo y Sangre: Génesis y Evolución del Tráfico de Drogas en el Estado de Tamaulipas. Mexico City: CIESAS (Centro de investigaciones y Estudios Superiores en Anthropologia Social), 2014.
[4] Guadalupe Correa-Cabrera, Michelle Keck, and Jose Nava, “Losing the Monopoly of Violence: The State, a Drug War, and the Paramilitarization of Organized Crime in Mexico (2007–2010).” State Crime Journal. Vol. 4, no. 1. Spring 2015: pp. 77–95, https://www.jstor.org/stable/10.13169/statecrime.4.1.0077.
[5] Juan A. Lozano, “Ex-Mexico Governor Pleads Guilty to Money Laundering in US.” Associated Press. 25 March 2021, https://apnews.com/article/government-contracts-mexico-smuggling-money-laundering-drug-cartels-938fdc5dafea237b4d2017d229cf6cd2.
[6] Fabiola Sánchez, “Mexican Border Governor Impeached for Alleged Tax Evasion.” Associated Press. 30 April 2021, https://apnews.com/article/tax-evasion-health-coronavirus-594d2b8509558a059540dd70844dcf70.
[7] Guadalupe Correa-Cabrera, María Fernanda Machuca, and Ruth Ann Ragland, “Citizen Journalism: From Thomas in Boston to Twitter in Tamaulipas: A Case Study.” The Journal of Social Media in Society. Vol. 5, no. 3. 2016: pp. 283-315. https://www.thejsms.org/index.php/JSMS/article/view/196.
[8] José Nava, “Gagging the Media: The Paramilitarization of Drug Trafficking Organizations and Its Consequences on the Freedom of Press in the Texas-Tamaulipas Border Region.” Unpublished M.A. thesis, Interdisciplinary Studies in Sociology. Brownsville, Texas: University of Texas at Brownsville, 2011.
[9] Nilda M. García, Mexico’s Drug War and Criminal Networks: The Dark Side of Social Media. New York: Routledge, 2020. Also see, Guadalupe Correa-Cabrera, “Militarización y Redes Sociales: La Guerra Virtual contra la Delincuencia Organizada en México,” in Efrén Sandoval Hernández, Eds., Violentar la Vida en el Norte de México: Estado, Tráficos y Migraciones en la Frontera con Texas. Mexico City: CIESAS (Centro de investigaciones y Estudios Superiores en Anthropologia Social), Plaza y Valdés, 2018, pp. 183-220.
[10] Ibid. García, Drug War and Criminal Networks.
[11] José Nava, “The Drug War in Cyberspace in Tamaulipas.” Unpublished manuscript, 2020.
[12] Ibid. p. 2.
[13] Ibid. p. 3.
[14] Op. Cit. García, Mexico’s Drug War and Criminal Networks at Note 9.
[15] See chapter 6 of Guadalupe Correa-Cabrera, Los Zetas Inc.: Criminal Corporation, Energy and Civil War in Mexico. Austin: University of Texas Press, 2017: p. 148.
[16] On hybrid warfare in Mexico see Teun A. Voeten, Mexican Drug Violence: Hybrid Warfare, Predatory Capitalism and the Logic of Cruelty. Bloomington: Xlibris, 2020.
[17] Op. Cit. Correa-Cabrera, “Militarización y Redes Sociales” at Note 9.
[18] On SNA see Stephen P. Borgatti, Martin G. Everett, and Jeffrey C. Johnson, Analyzing Social Networks. London: Sage, 2018. Also see Stanley Wasserman and Katherine Faust, Social Network Analysis: Methods and Applications. Cambridge: Cambridge University Press, 1994.
[19] On the concept of media curation see Guadalupe Correa-Cabrera, “Metodologías de Investigación, Crimen Organizado y Análisis de Redes Sociales: Un Estudio de Caso en la Frontera.” Revista Latinoamericana de Metodología de la Investigación Social. Vol. 21, no. 11. April-September 2021: pp. 69-81, http://relmis.com.ar/ojs/index.php/relmis/article/view/metodologias_de_investigacion_crimen/179.
[20] Due to the fact that these anonymous accounts, there is space for speculation and there is not complete certainty that the accounts selected in these three subgroups were placed correctly.
[21] See a detailed explanation on centrality measures below at Note 25.
[22] The most relevant accounts in this exercise are those that are in general more active, and comment essentially about the topic of security and organized crime in Tamaulipas.
[23] It is also possible for a target node to “follow” back a source node. In that case, the directed edge connecting the two is from target node to source node; that is distinct from the edge connecting source node to target node.
[24] Yet, another plausible configuration is where all nodes follow each other. In that case, there is no distinction between source and target nodes, and although it is a directed network, this configuration gives rise to a fully connected network of N nodes and E edges, where ?=? × ?−1.
[25] On centrality measures and social networks see Kousik Das, Sovan Samanta, and Madhumangal Pal, “Study on Centrality Measures in Social Networks: A Survey.” Social Network Analysis and Mining, Vol. 8, no. 1. 2018: pp. 1-11. https://doi.org/10.1007/s13278-018-0493-2.[26] To illustrate this point, consider Figure 1 below, a “directed” network diagram where connections are shown as “directed” edges with arrows pointing to the direction of connections between these nodes.
Figure 1. In- and out- degree illustration
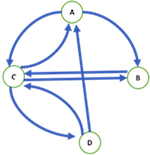
The in-degree and out-degree computation for Figure 1 would be the following:
- Node A has two in-degree (incoming from C and D) and two out-degree connections (outgoing to B and C).
- Node B has two in-degree (incoming from A and C) connections, but only one out-degree (outgoing to C).
- Node C has three in-degree (incoming from A, B and D) and three out-degree connections (outgoing to A, B and D).
- Finally, node D has one in-degree (C) and two out-degree connections (A and C).
[27] Arun Kumar Baruah and Tulsi Bora, “Bridging Centrality: Identifying Bridging Nodes in Transportation Network.” International Journal of Advanced Networking and Applications, Vol. 9, no. 6. 2018: pp. 3669-3673. http://oaji.net/articles/2017/2698-1528119000.pdf.
[28] Here the phrase “densely connected” refers to high connectivity within a local group of nodes compared to connectivity to nodes that are outside that local group.
[29] The terms “node” and “actor” are used interchangeably throughout this paper.
[30] Op. Cit. Correa-Cabrera, “Metodologías de Investigación, Crimen Organizado y Análisis de Redes Sociales” at Note 19.
[31] On this phenomenon, see Op. Cit. Correa-Cabrera, Los Zetas Inc. See also Op. Cit. Correa-Cabrera, “Militarización y Redes Sociales” at Note 15.
[32] Email sent by Twitter user @ElParece. More information of this incident can be found in the blog post authored by this same account entitled “The Shadow War,” which can be found in https://narco.news/the-shadow-war.
[33] GOPES stands for Grupo de Operaciones Especiales (or Special Operations Group). It is a “SWAT-style reaction force that was formed in mid-2020 to carry out high-profile security operations against organized crime groups.” It replaced the CAIET. This elite state police force has been frequently accused of committing extortions, participating in crimes and forced disappearances, and for its alleged links with organized crime. A dozen members of the GOPES have been implicated in the massacre of 19 migrants in the Mexican border municipality of Camargo, Tamaulipas in January of 2021. See Parker Asmann, “US-Trained Police Implicated in Mexico Migrant Massacre.” InSight Crime. 3 February 2021, https://insightcrime.org/news/us-trained-police-mexico-migrant-massacre/.






