Cyber Integrating Architecture
Brett Lindberg, Stephen Hamilton, Brian Lebiednik and Kyle Hager
This article is the latest addition to the U.S. Army TRADOC G2 Mad Scientist Initiative’s Future of Warfare 2030-2050 project at Small Wars Journal.
Introduction
Designating cyber as a domain within the Multi-Domain construct illuminated a gap in the ability for the Army (as a component of the joint force) to simulate Cyber and Electromagnetic Activities (CEMA) in conjunction with the traditional land domain via integrated Live, Virtual, and Constructive (LVC) environments [1]. The ever-increasing pace of cyber technologies requires the Army to procure solutions that are flexible and capable of adapting to current advances in the cyber domain. Many companies and organizations have attempted to fill this shortfall with different technologies that have not been fully tested or integrated into existing simulation environments or maneuver exercises [2][3].
Notably, the Army has created cyber ranges within different organizations to test CEMA capabilities that have not integrated well with other simulation environments or lacked real-world cyber effects [4]. The goal of the Persistent Cyber Training Environment (PCTE) is to interconnect cyber ranges for the purposes of training the Cyber Mission Force (CMF) [5]. This does not support the Army's key role as the Land Component Commander (LCC) and the forces on the ground that have CEMA enabled systems. Similarly, Capture-the-Flag (CTF) exercises train cyber soldiers and while many line soldiers may participate, they do not inform the vast majority of the force [6]. Many Combatant Commands and Services have stood up standalone cyber ranges to model their specific theater or service, but these ranges do not interconnect and are specifically configured to translate data between cyber simulation components. One example of this, Pacific Command (PACOM) has the Cyber Operational Architecture Training System (COATS) that creates its own Data Exchange Model to translate different simulators so that they can translate effects in their overall cyber range [7]. Homegrown solutions do not scale and cannot replicate across the Army, because of the specific patchwork that engineers use to make the simulations communicate with one another. This leaves the Army with several cyber environments to test different effects but no federated simulation environment to test and simulate cyber effects on Battlefield Operating Systems (BOS).
In Modeling and Simulation has six communities: acquisition, analysis, experimentation, intelligence, testing and evaluation, and training [1]. Each of these communities must replicate Cyber and Electromagnetic Activities (CEMA) in order to inform the community of potential gaps in how the Army conducts operations. To limit these gaps, the communities use simulations to evaluate their specific input and provide useful data to inform the forces that will conduct these operations. As the Secretary of Defense stated soldiers should experience twenty-five bloodless battles in simulators before facing their first one [8]. Failure to replicate the real environment, can lead to communication fratricide, either by jamming, intercommunication problems, or self-denial-of-service; inability to detect and identify cyber-attacks on a tactical network; or inability to train as we fight in simulations.
Simulators provide a spectrum of realism for the communities to perform their individual requirements. The spectrum ranges from the most realistic simulation that resembles actual combat to imaginative scenarios that do not remotely resemble actual combat. Live-fire exercises provide the most combat-like simulations that we can safely recreate. Unfortunately, these exercises are both time and resource intensive, so they cannot always be used for training, testing, and experimentation.
Contrast this with a simulation where generals move pieces on maps. The generals may array their forces and provide them with missions while employing a third party to provide an enemy reaction. This process, known as war gaming, is widely employed in the Military Decision-Making Process (MDMP) [9]. This provides the commander with different strategies and potential enemy reactions to select the commander's preferred Course of Action (COA).
Current Cyber Environments
Cyber ranges and tactical combat simulators comprise the two types of simulations currently available. As different organizations develop their environments to satisfy their requirements, they failed to integrate the two types of simulators. Each environment has a specific end-state, set forth by the procuring organization that may not allow for additional functionality as technology progresses. Often, these simulations have custom interconnections to allow for simulators to communicate with one another that an engineer has invested massive amounts of time. For instance, three cyber ranges from PACOM [7], the PCTE [5], and the Army Cyber Battle Lab [10] all claim to address cyber simulations yet do not communicate with one another, simulate many CEMA effects, and account for war fighting functions. They do not rely on a standard data exchange format or allow for interconnectivity, therefore they become standalone solutions.
Cyber Ranges
Cyber ranges allow for operators in the cyber environment to train and operate in a closed network to test different capabilities that may be used exclusively in the cyber domain [11]. Operators are able to integrate and test their tool sets to attack different targets as they relate to the network and devices that normally operate inside of a simulated Internet infrastructure, such as in military, industrial, or commercial networks, without causing actual affects to real systems. The continued integration of cyber elements into other platforms, left many of these systems unable to integrate and support larger exercises. For instance, a Brigade Tactical Operations Center (TOC) operates many integrated platforms that communicate and provide the commander a Common Operating Picture (COP). Testing cyber capabilities against these systems has been limited and the current cyber ranges do not allow for easy access to these physical battlefield networks [12].
Ranges, such as the PCTE [5], allow for the development of cyber tools and training in a simulated, closed network environment. These ranges concentrate on red team and blue team training and mission rehearsal for Cyber Mission Forces (CMF) [13] [14]. While the CMF needs these ranges for their own training, they remain only a piece of the overall solution that the Army needs to inform all of the simulation communities.
Tactical Combat Simulators
Current battlefield simulators have the ability to iterate through many discrete COA to achieve different end-states with opposing forces [15]. These simulations provide commanders from battalion to corps level the ability to change and evaluate their COAs against a simulated enemy. In each simulation, the commander arrays their forces on the battlefield against a known enemy template. As the simulation is executed, forces attrite based on probabilities of kinetic effects, whether that be a movement, firepower, communication, or catastrophic kill [16]. Commanders are forced to respond to enemy reactions and counteract, modify the arrangement of forces, or maneuver to obtain the tactical advantage [9].
CEMA effects in this field are rudimentary as the physical domain remains the key focus area of the simulators. Simulators are able to replicate simple attacks such as jamming and increased latency in networks [12]. More sophisticated attacks including gaining unauthorized access to BOS, spoofing Global Positioning Satellite (GPS) location data, or data manipulation of network traffic represent some of the shortfalls in current simulated environments. The communities largely use these simulators to test and evaluate everything from training to acquisition.
Criteria
To properly evaluate any simulation environment, there must be a set list of criteria to evaluate and assess against [16]. Below, we list several requirements that must be met by any simulation to convey the importance of the cyber domain to a commander. Additionally, we provide a list of cyber exploits that must be available to both the commander and his adversary in the simulation thereby providing a commensurate training environment for both combatants.
Interoperability
Any Live, Virtual, or Constructive (LVC) environment must be able to bridge the gap between all of the domains available to commander. Many of the simulators in production can interact with different systems to provide a more holistic view of the scenario and a better simulation environment. This allows for any of the communities to interact with the simulator and provide a meaningful response. Often when integrating different simulators, engineers must create custom code to translate effects from one simulator to another. Custom code creation results in upgrading components of the simulators which creates an additional difficulty for continued operation and integration. Providing a common data exchange model will prevent each federation from creating a COATS-like solution [7]. Therefore, as a requirement any simulation system needs to contain a common interface for integration with other systems.
LVC Environment
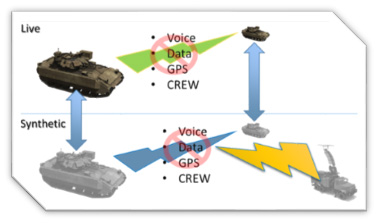
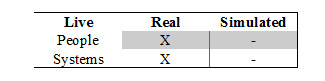
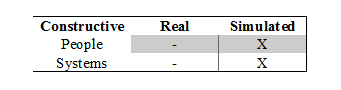
The proposed solution for a CEMA simulation must fall into one of the LVC simulations [16]. For completeness, this section describes each of the different simulation environments and the expected requirements for each in a cyber simulation. The 2x2 matrix with real or simulated soldiers and systems describes possible environments available.
Live: The proposed solution for a CEMA simulation must fall into one of the LVC simulations [16]. For completeness, this section describes each of the different simulation environments and the expected requirements for each in a cyber simulation. The 2x2 matrix with real or simulated soldiers and systems describes possible environments available.
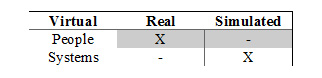
Virtual: A virtual simulation involves real people and simulated systems [16]. Soldiers use simulated systems to train on equipment or systems to improve their proficiency. Examples include flight simulators, call for fire, basic rifle marksmanship simulators such as the Engagement Skills Trainer (EST), or network simulators [4]. Virtual simulations provide good platforms for repeated soldier training, but lack aspects of a real system.
Constructive: Constructive simulations involve simulated soldiers and systems [16]. In these types of simulations, the operator arrays simulated systems and soldiers in a scenario. When these simulations are executed, the operator may have limited or no interaction with the simulation to influence or affect the outcome. These simulations help research and development, or evaluate a multitude of COAs. They can be run repetitively, with reproducible simulated outcomes based on the input data. Examples of constructive simulations include One Semi-Automated Forces (OneSAF) or Joint Land Component Constructive Training Capability - Multi-Resolution Federation (JLCCTC-MRF) [17] [18]. These simulations are leveraged to inform research and development, and strategic decision making yet provide little training value to individual soldiers.
Cyber Effects
Integrating cyber into these simulators can be challenging, therefore we propose using the Intrusion Kill Chain methodology with some caveats [19]. Lockheed Martin designed the Intrusion Kill Chain to provide a framework for US-CERT activities inside a computer network. We expand this to include CEMA on the battlefield and potentially less sophisticated attacks that an Advanced Persistent Threat (APT) would entertain on sensitive economic, proprietary, or national security information. Below is a non-exhaustive list of potential network exploitations and effects that an adversary could achieve that should be tested in a battlefield simulation.
- Reconnaissance
- Radio Frequency (RF) Identification
- RF Direction Finding
- Enumeration Attacks
- Port Scanning
- Denial of Service
- Radio Jamming
- Flood Attack
- GPS Spoofing
- Initial Entry
- Default or Weak Password
- Phishing/Spear Phishing
- Trojan Horse
- Privilege Escalation
- Root Access
- Control Flow Manipulation
- Control System Manipulation
- Data Manipulation
- Man-in-the-Middle Attacks
- Message Spoofing
- Server Manipulation
- Log Alteration
- Persistence
- Lateral Movement
- Data Exfiltration
- Beaconing
Evaluation Metrics
To properly evaluate any simulation there must be an established list of requirement or metrics to evaluate them against [20].
- Realistic - be realistic and comparable to warfare
- Repeatable - run several times with different outcomes, based on the supplied conditions
- Robustness - have a variety of cyber capabilities as outlined in III-C
Idealistic Simulation
The ideal simulator for the Army must integrate each of the domains and satisfy the interaction needed by each of the six simulation communities. Many solutions exist in the Army's inventory but do not communicate well with one another leading to the problem discussed in III-A. Creating a common framework for the simulators in existence and holding those organizations responsible for their interoperability, as they build out CEMA effects, will help to solve this problem. For simplicity, we have chosen to concentrate on the most realistic simulations, Live and Virtual.
Live
CTCs already simulate a majority of the battle domains within a contained scenario with clear Lines of Effort (LOE) and Rules of Engagement (ROE). Augmenting this simulation with a CEMA solution would provide the rotating forces with the ability to train in the cyber domain. To do this the rotating unit would need Tactical Control (ADCON) of a CEMA cell. These rotations occur but only on a limited basis [21]. The TACON CEMA cell allows the unit to detect, deter, prevent, and recover from cyber-attacks.
The Opposing Forces (OPFOR) are outfitted with an attack and exploit cyber cell that specializes in CEMA exploitation. The ROE for the enemy cell allows them to attack the network, provided an entry into the network or in advanced cases no network access. The cell would utilize on-net exploitation systems (i.e. Kali Linux), Commercial-of-the-Shelf (COT) Unmanned Aerial Vehicles (UAV), GPS spoofers, and an assortment of friendly force systems (commensurate with the rotating force) [22]. Using these systems, OPFOR could traverse through the exploitation cycle described in III-C.
All tactical systems will be virtualized to allow for OPFOR to operate without potentially destroying or degrading real systems. While this cannot be done with the actual equipment itself, the simulation can provide proxy clients for each of these systems so that the OPFOR can attack virtual systems. The unit can still operate their real equipment to the point where the communications are steady and the S6 has configured the systems. Then the unit switches to virtual clients running the same operating system and configurations of their network.
Virtual
The virtual realm of simulation provides a larger array of simulations to choose from, in this instance a full Brigade Combat Team (BCT) or Battalion (BN) simulation are considered. Headquarters units will continue to utilize Knowledge Management and network operations in support of their maneuver components. This allows for exploitation of the Battle Command Systems (BCS) such as Command Post of the Future (CPOF) or Force XXI Battle Command Brigade and Below (FBCB2), as well as the network attack and defend aspect of cyber warfare [23].
This simulation could easily run within a building with a physical divider separating the friendly and OPFOR with ROE that prevents communication other than through the simulation. Using reproducible scenarios, friendly forces would receive a mission to execute within a specified time frame. The friendly forces would have time to emplace and configure all of their systems to include network and maneuver elements. After the allotted time, the OPFOR would encounter the friendly forces and react to these maneuvers with both kinetic and CEMA actions as they would in combat.
Evaluation
Evaluation of the different architectures requires some scenario development to accurately evaluate the performance and execution of the solution. We propose several scenarios that create a cyber challenge to simulate an actual cyber event.
Scenario 1: GPS Spoofing
Mission: 1st Squadron of the 73rd Cavalry Regiment (CAV) conducts screening forward of 325th Airborne Infantry Regiment (AIR) in order to identify enemy positions and avenues of approach for the main effort.
Scenario: Charlie Troop, 1-73 CAV, identifies Arianian forces advancing along Route Gold. The Forward Observer (FO) identifies the grid coordinates with a mounted laser range finder and Defense Advanced GPS Receiver (DAGR). This message is relayed to the Fire Direction Center (FDC) for a subsequent fire mission.
Arianian Forces have equipped high power GPS spoofing equipment on their lead convoy element placing the elements of 1-73 CAV locations on their DAGR and Force XXI Battle Command Brigade and Below (FBCB2) 2 KM north of their current position. When the FO calls for fire on the advancing enemy elements, this position places them danger close to the fire mission.
The gun line conducts the fire mission with a 155 mm High-Explosive rounds. The round lands near the FO and his platoon destroying Mine-Resistant Ambush Protected (MRAP) vehicles and wounding personnel, subsequently identifying the friendly position to the Arianian forces. The Arianian forces then maneuver on Charlie Troop before the Quick Reaction Force (QRF) can react to the situation, destroying the entire cavalry troop.
Scenario 2: FBCB2 Compromise
Mission: 2nd HBCT of the 1st Infantry Division conducts route reconnaissance of Route Patton in order to allow non-combatant supply convoy access to the Atropian people.
Scenario: 1st BN of the 63rd Armor Regiment (AR) conducts movement to contact along Route Patton to clear enemy forces. Arianian forces have obtained an FBCB2 from a Non-Mission Capable vehicle abandoned following a previous combat engagement. The Arianian forces begin placing enemy force icons in 1st BN of the 18th AR's Area of Operation (AO), forcing the Division to redirect 1-63 AR to maneuver to assist 1-18 AR. On route Patton, Arianian forces interdict and commandeer the supply convoy.
Scenario 3: Command and Control Compromise
Mission: 1st CAV secures AO Eisenhower vicinity Ganja in order to deny freedom of maneuver to Arianian forces.
Scenario: 1st CAV Headquarters prepares operations to secure AO Eisenhower within Assembly Area (AA) MacArthur. Opposing Forces (OPFOR) have gained access to the Knowledge Management Systems used by 1st CAV. OPFOR leverage their access to manipulate data throughout the Operations Order (OPORD) that would locate linkup points and AAs by more than 4 KM off for friendly units and accelerate the execution time for the initial movement by one day, leaving the first unit without reinforcements, QRF, or fires support for 24 hours.
On H-hour minus 1, scouts depart AA MacArthur to screen for follow-on friendly forces. The scouts arrive at their designated position where OPFOR have established a deliberate ambush on the friendly maneuvering unit. When the scouts radio back, 1st CAV does not have any arrayed forces to support their efforts.
Scenario 4: TOC Discovery
Mission: Alpha Company 1st BN of the 75th Ranger Regiment conducts security operations vicinity Baku in order to provide covert QRF for follow-on forces.
Scenario: Elements of Alpha Company, 1-75 Rangers conducted a covert infiltration and established a safe house on the outskirts of Baku, providing over watch and advanced reconnaissance. Despite superb noise and light discipline, the Rangers present a large electronic signature as attempting to maintain communication; Very High Frequency (VHF) radios on the objective and High Frequency (HF) Communication for communicating with friendly forces off the objective. Using RF detection and direction finding capabilities, Arianian forces identify communication signal emissions from the safe houses. With the derived intelligence, the Arianian forces coordinate a deliberate attack on the safe house. The Arianians orchestrate a complex attack on the safe house, inflicting casualties and capturing the remainder the unit.
Potential Observations
Each of the six simulation communities would benefit from the ability to replicate CEMA in simulations. Notably the acquisition, testing, and experimentation communities stand to benefit from a codified simulation environment permitting better preparation and equipping of forces that will encounter cyber on the battlefield.
Training and operations communities would employ the simulation for training the force, while providing more realistic simulated outcomes. It is unclear whether or not commanders have fully grasped the cyber domain and the implications of their systems while employed. Currently, commanders may never experience a cyber-attack, limiting their experience in identifying cyber-attacks or how to react to such an event. To experience this in a training environment would prove an invaluable training in order to educate commanders about their systems and improve the performance of their operators.
Training does not stop with commanders. A simulation environment provides the CMF with another opportunity to employ their skillsets in a training environment. The CMF could use this as a live virtual force on force training with red and blue teams. These types of training events are invaluable to network operators and although some cyber ranges can support these exercises, integrating this training into real mission platforms would provide a more realistic scenario than the virtual capture-the-flag. Empowered by these simulators, the CMF could conduct penetration tests against BOS and identify vulnerabilities in the systems.
Conclusion
The Modeling and Simulation community needs a solution to model and simulate the cyber and electromagnetic effects on the battlefield. Crucial to this would be the interoperability and integration of existing and future simulations through a federated simulation environment. The community would benefit by improving the variety of potential CEMA and effects in the Multi-Domain Battle architecture. When the soldiers on the battlefield encounter a cyber or electromagnetic effect on the battlefield, it could prove disastrous should it be their first.
References
[1] “Management of Army Modeling and Simulation,” Washington, DC, May 2014.
[2] S. Leblanc et al., “An Overview of Cyber Attack and Computer Network Operations Simulation,” Boston, MA, Jul. 2015. [Online]. Available: https://dl.acm.org/citation.cfm?id=2874983
[3] F. Machado, A. Costa and J. Rezende, “Use of Simulation to Achieve Better Results in Cyber Military Training,” Dec. 2015. [Online]. Available: http://ieeexplore.ieee.org/abstract/document/7357620/?reload=true
[4] J. Davis and S. Magrath, “A Survey of Cyber Ranges and Testbeds,” PO Box 1500, Edinburgh South
Australia 5111 Australia, Oct. 2013. [Online]. Available: http://www.dtic.mil/docs/citations/ADA594524
[5] C. Heininger, “Army Taps Innovation for Cyber Training,” U.S. Army, Nov. 2016.
[6] S. Stover, “Cyber Brigade Soldiers Excel in All-Army Cyber-Stakes Competition,” U.S. Army, Nov. 2017.
[7] D. Wells and D. Bryan, “Cyber Operational Architecture Training System - Cyber for All,” I/ITSEC, no. 15108, 2015.
[8] “Soldier Performance is Focus of Close Combat Task Force,” Association of the United States Army, Apr. 2018.
[9] “Commander and Staff Organization and Operations,” Washington, DC, May 2014.
[10] D. S. Staff, “Army gets closer on Battle Lab,” Defense Systems, May 2015.
[11] C. Pham et al., “Cyris: A Cyber Range Instantiation System for Facilitating Security Training,” Ho Chi Minh City, Vietnam, Dec. 2016. [Online]. Available: https://dl.acm.org/citation.cfm?id=3011087
[12] K. Varshney, M. Pickett and R. Bagrodia, “A Live-Virtual-Constructive (LVC) Framework for Cyber Operations Test, Evaluation and Training,” Baltimore, MD, Nov. 2011. [Online]. Available: http://ieeexplore.ieee.org/abstract/document/6127499/
[13] M. Pomerleau, “Army Spearheading Cyber Persistent Training,” DefenseNews, Aug. 2016.
[14] “Army Shines Spotlight on Cyber Training Growth,” I/ITSEC 2017 Official Daily News Digest, Nov. 2017.
[15] I. Cil and M. Mala, “A Multi-Agent Architecture for Modelling and Simulation of Small Military Unit Combat in Asymmetric Warfare,” Mar. 2010. [Online]. Available: https://www.sciencedirect.com/science/article/pii/S0957417409005521
[16] A. Tolk, “Engineering principles of combat modeling and distributed simulation,” Hoboken, NJ, Mar. 2012.
[17] “One Semi-Automated Forces (OneSAF).” [Online]. Available: https://www.leidos.com/sites/default/files/responsive/Products/Simulation/15-0282-1127v1-OneSAF Brochure.pdf
[18] “Lockheed Martin to Provide U.S. Army with Simulation-based Command and Battle Staff Training System.” [Online].
Available: https://m.lockheedmartin.com/us/news/pressreleases/2013/april/lockheed-martin-to-provide-u-s-armywith-simulation-based-comma.html
[19] E. M. Hutchins, M. J. Cloppert, and R. M. Amin, “Intelligence-driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains,” Leading Issues in Information Warfare & Security Research, vol. 1, no. 1, p. 80, 2011.
[20] R. Sargent, “Verification and Validation of Simulation Models,” Feb. 2013. [Online]. Available: https://link.springer.com/article/10.1057/jos.2012.20
[21] S. Stover, “Cyber Activities at the National Training Center Support Real World Operations,” U.S. Army, Feb. 2018.
[22] “Our most advanced penetration testing distribution, ever.” [Online]. Available: https://www.kali.org/
[23] S. Diallo et al., “Integrating CPOF, JSAF and OneSAF through CBMS,” Jun. 2013. [Online]. Available: http://www.dtic.mil/dtic/tr/fulltext/u2/a604474.pdf
