Combating Corruption: Improving Department of Defense Support in Attacking the Corruption, Transnational Organized Crime, and Transregional Terror Organization Nexus
David Jennen and Charles Barham
Introduction
It is 11 September 2015, the anniversary of the al-Qa’ida attacks against the United States. The team is in place, and the target comes into view. He has just arrived at the Tocumen International Airport in Panama City, Panama on an international flight from the United Arab Emirates (UAE). He is not a terrorist, just a criminal, if you can use the term “just a criminal” to describe him. The order is given, and members of the U.S. Drug Enforcement Agency (DEA), acting as part of an Interagency Task Force (IATF), confront and arrest him, a non-kinetic event. Several days later he is extradited to the U.S. where he eventually receives prison time and a hefty fine.

Figure 1 - Altaf Khanani, Former Head of the Al Zarooni Exchange
(Courtesy of Immigration and Customs Enforcement, Department of Homeland Defense)
The target in this case was Altaf Khanani, the head of a transnational criminal organization (TCO) known as the Al Zarooni Exchange, responsible for laundering billions of dollars in organized crime proceeds annually in support of multiple TCOs as well as designated terrorist groups across the globe. His arrest demonstrated the U.S. government’s commitment to targeting criminals who blur the line between drug trafficking, terrorism, and organized crime.[i]
The U.S. Department of Defense (DoD) supported, as a member, the IATF that spent years building the case, obtaining a grand jury indictment, and ultimately arresting Khanani and disrupting his operation. DoD representatives were, and still are, embedded in the DEA and other departments. But DoD interagency (IA) support is often limited to activity linked to counter narcotics per Section 1022 of the National Defense Authorization Act.
DoD is an active participant, in varying degrees, in combating TOC due to the linkage to terror and drugs. Both TOC and TTOs are supported by corrupt individuals and networks. Therefore, the corruption, TOC, and TTO nexus should be given greater attention. DoD’s supporting role should be increased to include combating corruption where objectives include prevention of TTO external operations with appropriate, strategies, policies, and authorities.
The Threat
Transregional Terror Organizations.[ii] Violent extremist organizations (VEO) vary in terms of their scope and reach. For the purposes of this paper our focus is on the TTO, i.e. al-Qa’ida and ISIS, whose reach cuts across DoD Geographic Combatant Command boundaries. In defeating a TTO our initial goal is to reduce the TTO to a sub-transregional status or capability. At this point it becomes a violent extremist organization and might be further reduced or defeated.
But TTOs are not nation states and they lack the legitimate systems and processes to generate revenues and transport personnel and commodities, either within or between countries. In order to support their operations TTOs have turned to TOC networks for funding and logistics.[iii] Corruption also underpins both TOC and TTO operations. This includes corrupt government officials, and corrupt individuals employed by licit businesses.
Transnational Organized Crime.[iv] TCOs threaten the United States for two principle reasons. First, TOC networks threaten U.S. national interests. TOC, like TTOs, find it easy to develop and mature in unstable countries or failed states with weak rule of law. They penetrate both government institutions and licit businesses where they increase corruption and contribute to increased instability. TOC has become increasingly complex and significantly threatens U.S. and international security by expanding their reach into areas that present a threat to public safety, public health, governmental institutions, and economic stability.[v]
Secondly, TOC threatens U.S. national security interests through their increasing support to TTOs and their operations. TCOs often do not support TTO activities because they agree with their objectives, but rather to enjoy the monetary profits and to exploit the resultant instability and lawlessness within nation states who lose the ability to provide rule of law due to TTO activity. TCOs do this without regard to long-term consequences.[vi]
TCOs participate in numerous types of profit-motivated crime in multiple countries. These activities include, but are not limited to: money laundering, terrorist financing, drug trafficking, human trafficking, and weapons trafficking.[vii] Corrupt government and licit business individuals facilitate these operations by directing compliance assets away from TOC, not asking questions, or simply looking the other way. Bribery, fraud, and other forms of corruption allows TOC access to border crossings, passports and visas, and secure facilities.[viii]
TOC criminal activities, intimidation, and corruption facilitates instability in nations which further supports TOC development, and gives rise to TTOs. As documented in the “Strategy to Combat Transnational Organized Crime”, TTOs are turning to criminal networks for financial and logistic support.[ix]
Corruption. Former Secretary of State Kerry referred to corruption as a "root cause of violent extremism”.[x] All countries possess some varying levels of corruption. But where corruption begins to reach “grand” levels you see a correlation between TTOs, TOC, and corruption. Where corruption is high, instability is high and TOC and TTOs flourish.[xi] Afghanistan is a good example. The country long suffered from a weak central government and a lack of rule of law. Corruption developed as a way of life. The injustice and criminal activity of warlords, local power brokers and patronage networks created fertile ground for extremist ideology. VEOs like the Taliban developed in response to these conditions and eventually took control of the country.
At the higher levels you will find corrupt individuals who are directly supporting TOC and TTOs. In some countries, this type of corruption is so wide spread and pervasive they can be referred to as having a “culture of corruption”. This type of systemic corruption uses sophisticated networks that leverage the various instruments of national power for their own personal gain.[xii] These individuals usually control resources or other assets which they influence to facilitate the operations of TOC and TTOs. In addition to providing support to TOC and existing TTOs, grand corruption can also contribute to the formation of new TTOs.[xiii] Where corruption, TOC, and TTOs intersect represents a nexus. Understanding these networks and their nexus helps us understand the links between corruption, TOC and TTOs. It also informs our strategy and plans for attacking them.
The Strategy
The impact of TOC did not go unnoticed by the global community. The United Nations hosted a convention against TOC in Palermo, Italy from 12 to 15 December 2000. The result was General Assembly Resolution 55/25, and three supporting protocols. The conference signified member state recognition of the critical nature of TOC and the willingness to address it [xiv]
Unfortunately for CTOC efforts, following the 9/11 attacks, U.S. attention shifted to counter terrorism. Ten years later, the White House released its “Strategy to Combat Transnational Organized Crime” in 2011. This Strategy articulates a “whole-of-government approach”, integrating all the tools of American power to combat TOC, and among other objectives, to prevent the criminal facilitation of terrorist activities.[xv] This position was most recently reiterated in a Presidential Executive Order on Enforcing Federal Law with Respect to Transnational Criminal Organizations and Preventing International Trafficking.[xvi]
Within DoD, the strategic document that shapes and informs our operations is the National Military Strategy (NMS). The NMS is nested under the White House Strategy and states that in concert with all elements of national power (whole-of-government approach) and international partnerships, U.S. military efforts aim to disrupt TTO planning and operations, degrade support structures, remove leadership, interdict finances, impede the flow of foreign fighters, counter malign influences, liberate captured territory, and ultimately defeat them. It acknowledges that in many locations, TTOs coexist with transnational criminal organizations, where they conduct illicit trade and spread corruption, further undermining security and stability.
Therefore, the NMS goes on to state that defeating TTOs also requires an understanding of the relationships between TTOs and TOC. By gaining insights into the TTO/TOC nexus allows us to better target and disrupt corruption enabled TOC support to TTOs in the various unstable countries around the world.[xvii]
With this guidance in mind, one of DoD’s stated end is the disruption and defeat of TTOs. To achieve this end, we must degrade these transregionally capable organizations to a “sub-transregional” level –a strategic win. DoD can achieve this end by way of disrupting the transnational criminals who facilitate TTO funding streams, acquisition of weapons and ammunition, recruitment, and movement of fighters. As previously discussed, transregional terror activity requires the corrupt access of transnational criminal enterprise to government and licit business. Focusing on the critical requirement of corruption and its associated vulnerabilities within lawful structures plays to nation state strengths and institutional competencies. Removing corrupt “gatekeepers” greatly disrupts TTO external operations.
Attacking the Corruption, Transnational Organized Crime, Transregional Terror Organization Nexus
Achieving the ends expressed in the aforementioned strategy documents requires a whole-of government approach. Many of DoD’s IA partners exercise unique authorities not granted to the military.
Various IATF like organizations exist where IA coordination occurs with the intent of producing effects against corruption, TOC or TTO. Focusing these efforts against common interest with limited resources is critical to IA and DoD success. TTO requirements for external operations is a good focal point. As a general rule, TTO critical capabilities can include freedom of movement to resupply and recruit; as well as financial and logistics access. Supporting these critical capabilities are critical requirements such as TOC networks.[xviii] Corrupt individuals or entities support these networks, as well as the TTOs. Therefore, any pressure that an IATF can apply against these critical capabilities and requirements will affect TTO operations.
Again, TTOs turn to TOC to generate, store, move and use funds and logistics support, as well as freedom of movement to resupply and recruit. TOC as non-State actors, rely on corrupt officials and or weak rule of law to conduct their operations. Similar to TTOs, we can focus our efforts against TOC as well. The focal point for TOC is usually its net profit.[xix] Corruption enables TOC success. Any efforts an IATF can take to seize assets, freeze assets, or attack corrupt officials will impact TOC operations. As an IATF determines what actions to take in combating corruption they should follow a defined process which allows the IATF to tailor and focus their IA system of networks to defeat a designated target network (see Figure 2 – Combating Corruption Process).
DoD, our IA colleagues, and our partner nations all have priorities, specific objectives and targets. Where there is commonality between the three, these targets are formally identified by the IATF and prosecuted following the process depicted in the “Combating Corruption Process”. Again, these targets could be TCOs or corrupt officials that facilitate their operations. In the initial step following target identification the IATF develops various inputs from corruption vector sources (government, military, licit business, and patronage networks) as well as TOC functions, into COAs. The IATF then war-games these COAs by looking at various effects or actions they might take, predicting the target’s reaction to those effects, then determining
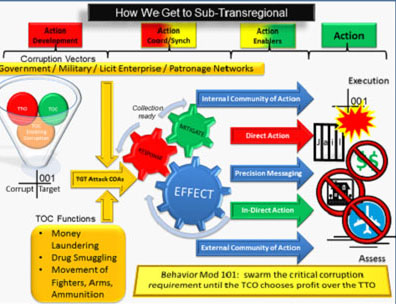
Figure 2 – Combating Corruption Process (Courtesy of David Jennen)
how we can mitigate those responses. Once the IATF develops its suite of actions, it considers its own enablers. The environment will determine the degree to which these enablers are internal (confined to one nation) or external (spans multiple nations). Enablers include authorities and permissions and are coupled with an information operations component where precise messaging is designed to influence the behavior of both corrupt individuals and criminals to end their TTO support. The output is a defined target with a suite of synchronized IA actions with DoD support. It represents the consideration of a whole of national and international instruments of power approach. The final step in this process is a feedback loop where the IATF assesses the effects of the action upon the target and considers follow-on engagements and or modifications to the suite of actions.
To better achieve these outcomes DoD needs to expand its authorities. Adding corruption to the definition of illegal means within Section 1022 of the National Defense Authorization Act is a good initial step. A separate authority facilitating DoD participation in these activities is a better long-term solution. DoD must update its strategy documents to reflect the importance of combating corruption in irregular warfare.
Bibliography
Carlson, Thomas S., United States Navy, “The Threat of Transnational Organized Crime to U.S. National Security: A Policy Analysis Using a Center of Gravity Framework”, 1997: http://www.globalsecurity.org/military/library/report/1997/Carlson.htm
Cassin, Richard L. , The FCPA BLOG, , August 25, 2016, http://www.fcpablog.com/blog/2016/8/25/john-kerry-corruption-is-root-cause-of-terrorism.html
Chayes, Sarah, Corruption and Terrorism: The Causal Link, Carnegie Endowment for International Peace, May 12, 2016. http://carnegieendowment.org/2016/05/12/corruption-and-terrorism-causal-link-pub-63568
D’Alfonso, Steven, Journal Article, “Why Organized Crime and Terror Groups Are Converging”, September 4, 2014. https://securityintelligence.com/why-organized-crime-and-terror-groups-are-converging/
Executive Office of the President of the United States: National Security Staff, Strategy to Combat Transnational Organized Crime, (U.S. Government Printing Office, Washington DC, July 2011): i. http://www.whitehouse.gov/sites/default/files/microsites/2011-strategy-combat-transnational-organized-crime.pdf
Joint Publication 3 – 26 “Counter Terrorism”, 24 October 2014. Page I – 3. http://www.dtic.mil/doctrine/new_pubs/jp3_26.pdf
The National Military Strategy of the United States of America, 2015, page 8. http://www.jcs.mil/Portals/36/Documents/Publications/2015_National_Military_Strategy.pdf
Novakoff, Renee, Journal Article, “Transnational Organized Crime: An Insidious Threat to U.S. National Security Interests”, Prizims 5, # 4, page 143. http://cco.ndu.edu/Portals/96/Documents/prism/prism_5-4/Transnational%20Organized%20Crime.pdf
Presidential Executive Order on Enforcing Federal Law with Respect to Transnational Criminal Organizations and Preventing International Trafficking, The White House Office of the Press Secretary, 9 FEB 2017; https://www.whitehouse.gov/the-press-office/2017/02/09/presidential-executive-order-enforcing-federal-law-respect-transnational
Tackle Instability and Terrorism by Fighting Corruption, Transparency International, 4 February 2015, http://www.transparency.org/news/feature/tackle_instability_and_terrorism_by_fighting_corruption
United Nations Convention against Transnational Organized Crime and the Protocols Thereto, United Nations Office on Drugs and Crime, https://www.undoc.org/unodc/treaties/CTOC/
U.S. Department of the Treasury, Press Release, “Treasury Sanctions the Khanani Money Laundering Organization, 11/12/2015.
https://www.treasury.gov/press-center/press-releases/Pages/jl0265.aspx
End Notes
https://www.treasury.gov/press-center/press-releases/Pages/jl0265.aspx
[ii] Joint Publication 3-26 “Counterterrorism” states that “transnational political movements that use unlawful violence to advance their objectives are referred to as Violent Extremist Organizations” (for this paper we address the TTO subset) “and are de facto terrorists.”
[iii] Renee Novakoff, Journal Article, “Transnational Organized Crime: An Insidious Threat to U.S. National Security Interests”, Prizims 5, # 4, page 143. http://cco.ndu.edu/Portals/96/Documents/prism/prism_5-4/Transnational%20Organized%20Crime.pdf
[iv]The White House’s 2011 “Strategy to Combat Transnational Organized Crime” defines TOC as “those self-perpetuating associations of individuals who operate transnationally for the purpose of obtaining power, influence, monetary and/or commercial gains, wholly or in part by illegal means, while protecting their activities through a pattern of corruption and/ or violence, or while protecting their illegal activities through a transnational organizational structure and the exploitation of transnational commerce or communication mechanisms.”
[v] Joint Publication 3 – 26 “Counter Terrorism”, 24 October 2014. Page I – 3. http://www.dtic.mil/doctrine/new_pubs/jp3_26.pdf
[vi] Ibid.
[vii] Steven D'Alfonso, Journal Article, “Why Organized Crime and Terror Groups Are Converging”, September 4, 2014. https://securityintelligence.com/why-organized-crime-and-terror-groups-are-converging/
[viii] Tackle Instability and Terrorism by Fighting Corruption, Transparency International, 4 February 2015, http://www.transparency.org/news/feature/tackle_instability_and_terrorism_by_fighting_corruption
[ix] Executive Office of the President of the United States: National Security Staff, Strategy to Combat Transnational Organized Crime, (U.S. Government Printing Office, Washington DC, July 2011): i. http://www.whitehouse.gov/sites/default/files/microsites/2011-strategy-combat-transnational-organized-crime.pdf
[x] Richard L. Cassin, The FCPA BLOG, , August 25, 2016, http://www.fcpablog.com/blog/2016/8/25/john-kerry-corruption-is-root-cause-of-terrorism.html
[xi] Tackle Instability and Terrorism by Fighting Corruption, Transparency International, 4 February 2015, http://www.transparency.org/news/feature/tackle_instability_and_terrorism_by_fighting_corruption
[xii] Sarah Chayes, Corruption and Terrorism: The Causal Link, Carnegie Endowment for International Peace, May 12, 2016. http://carnegieendowment.org/2016/05/12/corruption-and-terrorism-causal-link-pub-63568
[xiii] Ibid.
[xiv] United Nations Convention against Transnational Organized Crime and the Protocols Thereto, United Nations Office on Drugs and Crime, https://www.undoc.org/unodc/treaties/CTOC/
[xv] Executive Office of the President of the United States: National Security Staff, Strategy to Combat Transnational Organized Crime, (U.S. Government Printing Office, Washington DC, July 2011): i. https://obamawhitehouse.archives.gov/administration/eop/nsc/transnational-crime/summary
[xvi] Presidential Executive Order on Enforcing Federal Law with Respect to Transnational Criminal Organizations and Preventing International Trafficking, The White House Office of the Press Secretary, 9 FEB 2017; https://www.whitehouse.gov/the-press-office/2017/02/09/presidential-executive-order-enforcing-federal-law-respect-transnational
[xvii] The National Military Strategy of the United States of America, 2015, page 8. http://www.jcs.mil/Portals/36/Documents/Publications/2015_National_Military_Strategy.pdf
[xviii] Joint Publication 3 – 26 “Counter Terrorism”, 24 October 2014. Page IV – 10. http://www.dtic.mil/doctrine/new_pubs/jp3_26.pdf
[xix] CDR Thomas S. Carlson, United States Navy, “The Threat of Transnational Organized Crime to U.S. National Security: A Policy Analysis Using a Center of Gravity Framework”, 1997: http://www.globalsecurity.org/military/library/report/1997/Carlson.htm
About the Author(s)
Comments
Writing assignments is a…
Writing assignments is a crucial and challenging responsibility. Each student is aware of the requirements for success. I agree with you that success comes from hard work, but I also believe that students' writing quality might be affected by a lack of time or knowledge. That is why most students use the https://essayreviewsbro.com/fresh-essays-review/ site to request reviews of essay writing services so they can pick the best one for themselves.
