Western Jihadist Threats to the Military
Sam Mullins
Introduction
In a recent high-profile terrorism case in the U.K., a British-born ISIS sympathizer named Junead Khan was convicted for plotting to attack and kill U.S. military personnel stationed in Britain.[1] His plan was to ram into a vehicle carrying American soldiers and then behead the incapacitated victims. Had police intervened at any point, the intention was to detonate a pressure cooker bomb, committing suicide in the process and maximizing the number of casualties. Far from being an isolated case, this is just one of a long list of attacks on military personnel which have been planned and sometimes executed by Western jihadists. Indeed, Khan appears to have been directly inspired by the events of May 22nd, 2013, when an off-duty British soldier, Fusilier Lee Rigby, was run down and hacked to death by two extremists on the streets of Woolwich, east London.[2] Plots and attacks like these understandably grab headlines and result in at least temporarily heightened force-protection measures. However, little effort has been made to systematically analyze Western jihadist threats to the military, which of course are not limited to the U.K. and are both diverse and ongoing. Drawing upon a variety of cases involving Europe, North America and Australia, this article identifies a range of overlapping external and internal threats and discusses implications for military security.
External Threats
In this context, external threats involve civilian jihadists acting against domestic military targets from outside of the organization. Most notably, this includes planned and/or executed terrorist attacks as well as malicious hacking operations aimed either at defacement, disruption or acquisition of sensitive information. A third type of external threat involves the acquisition of military materials such as manuals, weapons or other items, though not necessarily for use against military targets.
Terrorist Attacks against Domestic Military Targets
Since 2001, there have been at least 38 plots by civilian jihadists to attack domestic military targets in the West, 26 of which were thwarted (see Table 1 below) and 12 of which (i.e. 32%) were actually executed (see Table 2).[3] Among the thwarted attacks, 19 of these (i.e. 73%) occurred after 2008 and the majority occurred either in the U.S. (38%) or U.K. (35%). Twelve plots (46%) were aimed at military bases, with the intention of using bombs and/or firearms to kill personnel inside; another nine (35%) were aimed at soldiers off-base (whether specific individuals named in the media or else anyone identifiable as a member of the armed services); a further two plots (8%) were aimed at recruitment centers; one group was targeting a town, Royal Wootton Bassett in the south of England, due to its role in the repatriation of British soldiers killed in Afghanistan and Iraq;[4] and in the final two remaining cases, the specific target was unidentified.
The intended modus operandi of thwarted attacks has mostly consisted of explosives (38%) and firearms (31%), although knives (in Junead Khan’s case combined with use of a motor vehicle) have become more common from 2014 onwards. Notably, this has occurred after the murder of Lee Rigby in 2013, which suggests a contagion effect. Also of note is the fact that just five plots could be considered operationally capable at the time of arrest, one involving firearms and the rest involving knives. Among thwarted plots, the closest that anyone came to manufacturing viable explosives was the so-called Sauerland Cell in Germany, but security services had swapped the group’s hydrogen-peroxide for a 3% solution that rendered their efforts useless.[5] The Sauerland Cell was also one of just six cases involving support from a foreign terrorist organization (FTO).[6]
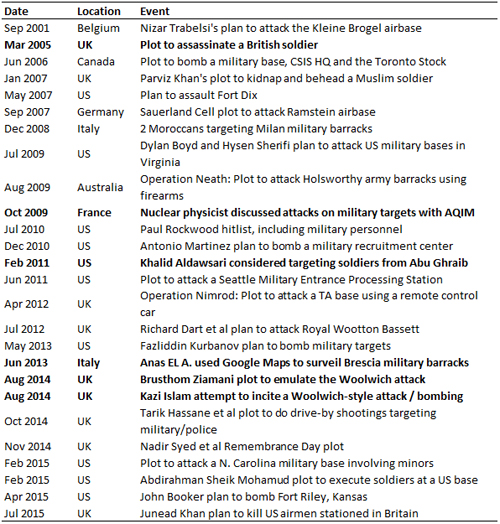
Table 1. List of thwarted terrorist plots involving civilian jihadists in Western countries targeting the military (2001–2015). Cases highlighted in bold involved lone individuals, i.e. no other active accomplices or informants.
Turning our attention to attacks which were actually executed against domestic military targets in Western countries, all twelve of them occurred after 2008. Four attacks took place in France, there were three attacks in Canada and two in the U.S., while Italy, Germany and the U.K. have experienced one apiece. The majority of attacks (7 out of 12, or 58%) were conducted against soldiers in public places. These include the shooting of two U.S. soldiers at Frankfurt airport in March 2011[7]; the assassination of three French soldiers in two separate attacks by Mohamed Merah in Toulouse and Montauban in March 2012[8]; the stabbing of a soldier at a train station in Paris in May 2013[9]; the killing of two Canadian soldiers in separate incidents in Saint-Jean-sur-Richelieu (using a motor vehicle[10]) and Ottawa (firearms[11]) in October 2014; and the attempted running over of four soldiers guarding a French mosque in Valence in the southeast of France in January 2016.[12] A further three attacks (25%) took place on military installations. The first was an attempted suicide bombing of military barracks in Milan in October 2009[13]; the second was the May 2013 stabbing of a French gendarme in Roussillon[14]; and the last was the fatal shooting of four U.S. Marines and a sailor at a Navy Reserve Center in Chattanooga, Tennessee in July 2015 (which was preceded by a drive-by shooting at a nearby Armed Forces Career Center[15]). Recruitment centers were also attacked on another two occasions: a fatal drive-by shooting in Little Rock, Arkansas in June 2009,[16] and the stabbing of two Canadian soldiers in Toronto in March 2016.[17]
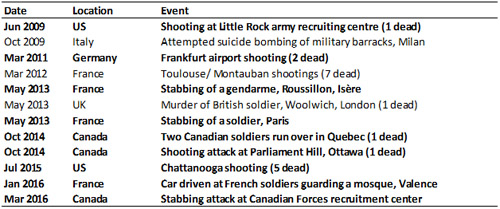
Table 2. List of terrorist attacks executed by civilian jihadists in Western countries targeting the military (2001–2016). Cases highlighted in bold involved lone individuals, i.e. no other active accomplices or informants.[18]
Five of the above incidents (i.e. 42%) involved firearms; four (33%) involved knives (combined with the use of a motor vehicle in the murder of Lee Rigby); another two attacks (17%) involved vehicles only; while explosives were used (unsuccessfully) on just one occasion. In total, seven of these attacks resulted in fatalities, five of which involved firearms and five of which targeted soldiers while off-base. Just one individual had established links to a FTO – namely Mohammed Merah, who had previously trained with militants in the Afghanistan-Pakistan border region and claimed to be acting on behalf of al-Qaeda (AQ).[19]
In light of these developments, it is clear that although Western jihadists still prefer soft, civilian targets, they have increasingly targeted the military –as well as police– since 2009.[20] This may be in part because they are regarded as more prestigious and morally defensible by the perpetrators; however there is no obvious reason for the timing of the increase, other than perhaps the aforementioned contagion effect, whereby plotters are inspired by the actions of others. The countries where the military is most likely to be targeted are the U.S., U.K. and France, although it is worth noting that Canada suffered three attacks within a relatively short space of time (which prompted a review of security at all Canadian military installations[21]) and of course no country is immune. Based on what we have seen so far, the most likely scenario for an externally-generated attack against domestic military targets involves small, freelance groups or lone-actors who are lacking FTO support, using firearms or other readily-available weapons (vehicles and knives) to ambush soldiers in public places. Nevertheless, in light of the recent, successful use of triacetone triperoxide (TATP)-based explosives in France and Belgium, more sophisticated attacks of course cannot be ruled out.
Malicious Hacking Attacks
A more recent development, which gathered pace during 2015, has been the use of hacking techniques, either to deface or disrupt military (as well as other government and non-governmental) websites and/or to steal and publish sensitive information online. Two online groups have been particularly active in targeting the military – namely the ‘CyberCaliphate’ (CC) and the ‘Islamic State Hacking Division’ (ISHD). Exactly who and how many individuals have been responsible for these groups is unknown; however, a central figure in both appears to have been Junaid Hussain, a British jihadist who was previously convicted of hacking offences in the U.K. and was eventually killed in a U.S. drone strike in August 2015.[22] Together, the CC and ISHD have been credited with at least eight hacking attacks against Western military targets (although one is disputed and another three apparently utilized open source information rather than hacking), while others have carried out at least five similar operations (see Table 3 below).[23]
The vast majority of these attacks have involved the online publication of personally identifiable information (PII) of military personnel, other government officials and sometimes family members. Details vary but have included names, photographs, physical as well as IP addresses (some accompanied by satellite imagery), phone numbers, email accounts and passwords. Besides generating a sense of fear or unease, causing embarrassment and financial loss, as well as demonstrating the ability to compromise seemingly secure government systems (which no doubt delivers a boost to terrorists’ morale), such operations are clearly intended to incite and facilitate attacks. As the ISHD declared in March 2015, “These kuffar [infidels] that drop bombs over Syria, Iraq, Yemen, Khurasan [Afghanistan] and Somalia are from the same lands that you reside in, so when will you take action? Know that it is wajib [religious obligation] for you to kill these kuffar [infidels]! and now we have made it easy for you by giving you addresses, all you need to do is take the final step, so what are you waiting for? Kill them in their own lands, behead them in their own homes, stab them to death as they walk their streets thinking that they are safe”.[24]
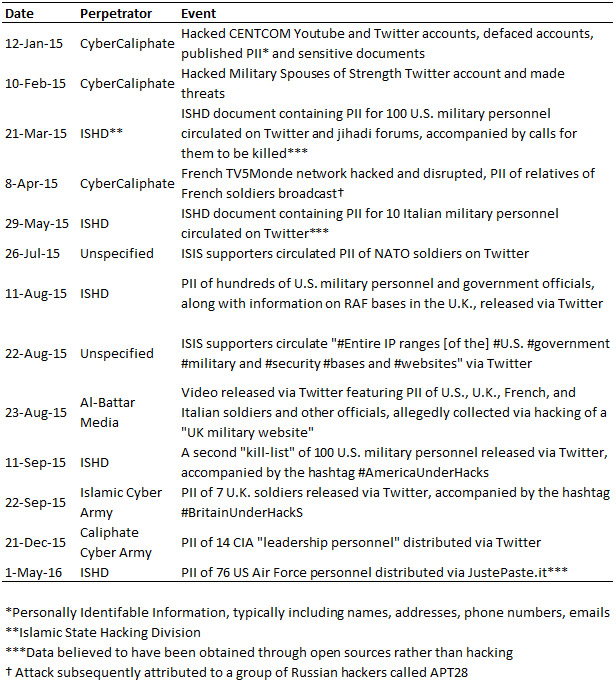
Table 3. Hacking operations against Western military targets, January – May 2016.
Fortunately, as of May 2016, there are no indications that military personnel identified in hacking operations have been targeted for physical attacks. Nevertheless, the calls for violence continue. Indeed, the above-quoted ISHD document, along with PII for a hundred U.S. military personnel, was widely circulated online by jihadist sympathizers – most notably Terrence McNeil, a hospital worker from Ohio, who was subsequently charged with soliciting murder.[25] More worrying still, rather than relying on general appeals, hackers have also directly urged specific individuals to act upon the information they have acquired. Prior to his death, Junaid Hussain was in communication with a number of Western jihadists involved in planning/executing attacks, including Junead Khan, whom he offered to provide home addresses of British soldiers.[26] Hacking operations have also continued despite Hussain’s demise and are now clearly an established tool in the repertoire of jihadist activity. In light of such persistence, it is entirely possible that hacking techniques will become more sophisticated over time and that the virtual and physical operations of Western jihadists will intersect violently in the future.
Acquisition of Military Materials
A third area of concern is where Western, civilian jihadists have tried or successfully obtained military knowledge, expertise, equipment and/or weaponry. Although such materials have not necessarily been intended for use against domestic military targets, they of course raise terrorist capabilities and –depending on the origins of the material– may fall under the military’s overall responsibility. The most common type of activity here involves the acquisition of military training and field manuals. Although these can now easily be found online, it is worth noting that in fact the so-called “al-Qaeda Manual” –recovered from the Manchester home of Abu Anas al-Liby in May 2000[27]– was largely based upon U.S. military training manuals stolen during the 1990s by an Egyptian AQ operative named Ali Mohamed[28] (see more under the heading of “Infiltration” below). Since then, numerous Western jihadists have been found in possession of official military instructional materials, which they often share with associates, although there is little evidence of the knowledge within being applied. In one such case in the U.S., an individual named Barry Bujol Jr. had acquired a number of restricted American military manuals, which he emailed to an informant, whom he believed to be a member of AQ, in the hope that the “brothers” overseas would then be able to overcome American forces.[29]
In similar vein, others have acquired a variety of equipment with direct military application in Western countries, which they then supplied to terrorists overseas. For instance, during 2003 and 2004, Mohammed Junaid Babar (an American who worked closely with jihadists from the U.K.) delivered money, “night vision goggles, sleeping bags, water proof socks, water proof ponchos and other military gear” to a senior AQ figure based in South Waziristan.[30] Of course, such items can be legally purchased by members of the public, meaning they are unlikely to be acquired from strictly military sources. Of far greater concern is the acquisition of restricted military hardware and weapons. In addition to copious amounts of hydrogen peroxide, the aforementioned Sauerland Cell was in possession of 26 military detonators.[31] In September 2012, a pair of French jihadists threw a hand grenade into a Jewish supermarket in Paris,[32] while more recently, Islamist terrorists in Europe have proven capable of obtaining military-grade weapons with apparent ease. Most of these, it seems, originate in the Balkans or Eastern Europe and are trafficked to countries like France where anyone with the right connections can buy them.[33] However, it is also possible that weapons belonging to Western militaries may end up in the hands of terrorists. In 2002 an Australian Army captain stole ten M72 rocket launchers from a facility just outside of Sydney. The leader of an Islamist terror-cell, Mohamed Ali Elomar, subsequently purchased five of those launchers (which have yet to be recovered) from an organized crime figure named Adnan Darwiche.[34] Of course this was a single incident, rather than necessarily being indicative of a broader trend, yet it serves as a reminder that any criminality or corruption within the military may serve as a point of vulnerability that both organized criminals and terrorists alike can potentially exploit. Worryingly, in July 2015 it was reported that around 180 detonators and a dozen blocks of plastic explosive had been stolen from an army base in the south of France[35] and it is not uncommon for both military and law enforcement agencies to “lose” significant amounts of weaponry and related accessories.[36] In light of Western jihadis’ well-established interest in obtaining such materials, there is an obvious need to ensure they are appropriately secured and accounted for.
Internal Threats
The manifestation of internal jihadist threats is often similar to external (i.e. civilian) threats – the key difference being that the perpetrators are current members of the military. They include infiltration, insider attacks and espionage. A fourth type of threat, which is closely related, involves former members of the military who become involved in terrorism after they leave the service.
Infiltration
Deliberate infiltration of the military by individuals who are already radicalized blurs the line between external and internal threats. It naturally begins as an external threat but then becomes internal if/when the individual in question succeeds.[37] By far the most successful example of infiltration was by Ali Mohamed, who was an officer in the Egyptian Army before joining the al-Jihad organization in 1981 and thereafter becoming a core member of AQ and one of the principle planners behind the East African embassy bombings of 1998.[38] In 1984 he briefly volunteered as an informant for the CIA, before the agency realized he was up to no good and cut him loose. Remarkably, he went on to serve in the U.S. Army for more than three years, based at Fort Bragg in North Carolina, and gained American citizenship. During that time, he was assigned to teach fellow soldiers about Middle Eastern politics, culture and religion. As noted above, he also used the opportunity to steal a variety of military documents, which he used to create terrorist training manuals for AQ. In his spare time, he provided training to a group of extremists in New York and New Jersey, including some of the first World Trade Center bombers, and in 1988 he even fought against the Soviets in Afghanistan whilst on leave. Although Mohamed left active military service in 1989, he joined the Army Reserve and in 1992 became an informant for the FBI, not long before travelling to Africa to conduct surveillance of potential targets for attack. It was only after those attacks took place that he was eventually arrested and imprisoned.
Contemporary Western jihadists generally lack the skill and sophistication of an operative such as Mohamed, yet some have nevertheless still tried to infiltrate the military as a means of gaining access to training, weaponry and combat zones, and/or to conduct attacks. In October 2008, an individual named Abdel Hameed Shehadeh from New York attempted to enlist in the U.S. Army with the apparent intention of deploying to Iraq where he would then desert and fight against American soldiers.[39] However, his application was denied when it was discovered that he had concealed a previous trip to Pakistan, where he had tried, unsuccessfully, to go and join the Taliban. In another more recent case, John Booker Jr., from Topeka, Kansas, had successfully enrolled in the Army in February 2014 with the intention of committing an insider attack. He was scheduled to report for basic training but was discharged after it was discovered he had expressed a desire for violent jihad and martyrdom on social media. He was then arrested in April 2015 and ultimately pleaded guilty to attempting to bomb the Fort Riley military base.[40]
Both Shehadeh’s and Booker’s efforts were extremely crude and neither really succeeded in infiltrating the armed forces. It is worth noting, however, that Booker had been posting comments in support of violent jihad long before applying to join the military and it was only after the FBI alerted the Army that they became aware and expelled him.[41] Moreover, although there is no evidence to suggest that Islamist extremists are systematically attempting to infiltrate Western militaries, the number of reported incidents has grown. For instance, in 2012 the FBI was said to be tracking approximately a hundred suspected Islamist extremists within the U.S. military (around 12 of whom were believed to be “serious” threats)[42] while more recently, Spanish,[43] French[44] and German[45] authorities have expressed similar concerns. Despite this, there are few concrete examples to be found and reports generally fail to distinguish between deliberate infiltration of the military (i.e. by individuals with a pre-existing extremist mindset and hidden agenda) versus radicalization and expression of extremist beliefs after having joined. Nevertheless, as the above examples illustrate, there are clear incentives for jihadists to try and infiltrate military organizations and the threat is believed to be significant enough to warrant the introduction of additional security measures in some countries. In Germany, for example, there are now plans to perform background checks on all new recruits, rather than just those working with classified material or in sensitive positions.
Insider Attacks
A second internal threat involves the planning and execution of jihadist-inspired attacks by serving members of the military against fellow soldiers. To date, the author is aware of just four such cases, all involving Americans, who appear to have radicalized as individuals within the military, rather than infiltrating with the pre-existing intention of conducting an attack (see table 4 below).
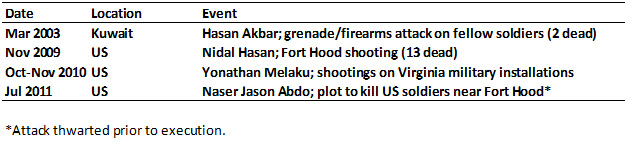
Table 4. Insider plots and attacks committed by military members, at least partly motivated by extreme Islamist beliefs. Cases highlighted in bold involved lone individuals, i.e. no other active accomplices or informants.
In the first of these cases, Hasan Karim Akbar, then a sergeant in the Army, launched an attack shortly after 1am at Camp Pennsylvania in Kuwait on March 23, 2003, just a few days before members of the 101st Airborne Division stationed there were due to deploy to Iraq.[46] After throwing grenades into tents where fellow soldiers were sleeping, he opened fire with his rifle, killing two officers. Although there is no evidence to suggest that Akbar was directly inspired by jihadists, the prosecution described his actions as “hate-filled, ideologically driven murder” and his primary goal appears to have been to prevent his victims from killing Muslims in Iraq.[47] Both his actions and his motivations are therefore sufficiently similar to include Akbar’s case in the current analysis, whether or not it is classed as an act of terrorism. In the second case, Major Nidal Malik Hasan, an Army psychiatrist, entered the Soldiers Readiness Processing Center at Fort Hood, Texas in the early afternoon of November 5, 2009.[48] Armed with a handgun, he shouted “Allahu Akbar!” before opening fire on those inside, killing twelve service members and one civilian before being incapacitated by civilian police officers. Although the Department of Defense (DoD) still classifies this as an act of “workplace violence”, Hasan had received ideological advice from Anwar al-Awlaki via email and claimed to be acting in defense of the Taliban within the context of what he perceived was a war against Islam.[49]
In the third insider attack case, there was damage to buildings but no fatalities. Between October and November 2010, a young Marine Corps Reservist, Lance Corporal Yonathan Melaku, conducted a series a five nighttime shootings targeting military installations in Virginia, including the National Museum of the Marine Corps, the Pentagon, and recruitment centers for the Marine Corps and U.S. Coastguard. He was eventually apprehended on June 17, 2011 in Arlington Cemetery –adjacent to Fort Myer– in possession of a backpack containing shell casings, components for an improvised explosive device (IED) and jihadist literature.[50] In the fourth and final case, Private Naser Jason Abdo was arrested at a hotel in Texas on July 27, 2011. In his room was a handgun, precursor materials for making an IED and the now-infamous Inspire magazine article, “How to Make a Bomb in the Kitchen of Your Mom”. As Abdo admitted to federal agents, his plan was to bomb a restaurant in the vicinity of Fort Hood which he knew to be frequented by American soldiers, after which he would shoot any survivors. He was thwarted only because he had aroused the suspicion of an alert sales clerk while purchasing smokeless gunpowder and other materials at a nearby gun store.[51]
Although we cannot necessarily generalize from just four cases, each of the perpetrators exhibited some important similarities that may be useful in the identification and prevention of similar attacks in the future. To begin with, they each had histories of problematic conduct and in three of the four cases were underachievers who failed to fit in. Akbar had previously been demoted, was known for falling asleep during meetings and was said to have an “attitude problem”.[52] Hasan had been disciplined for unprofessional conduct in 2007 for inappropriate discussion of religion, underperforming in his duties and being overweight.[53] Melaku meanwhile had been awarded the National Defense Service medal and Marine Corps Reserve medal;[54] however, he was also charged in May 2011 –just a few months prior to his attacks– with two counts of grand larceny (i.e. theft) in relation to a series of motor vehicle break-ins.[55] Finally, Abdo was said to have “horrible” rapport with his peers and in the weeks prior to his arrest had gone absent without official leave after being found in possession of child pornography.[56]
In addition, for three of these individuals problems had arisen in relation to religion. Akbar had skipped the 1991 Gulf War on religious grounds and had complained of racism and being harassed because of his faith.[57] Hasan had given a number of presentations with Islamist themes, including one in 2007 entitled “The Koranic Worldview as it Relates to Muslims in the U.S. Military” in which he declared that “It’s getting harder and harder for Muslims in the service to morally justify being in a military that seems constantly engaged against fellow Muslims.”[58] Lastly, Abdo had complained about being unable to properly observe Ramadan and in 2010 refused to deploy to Afghanistan because of his faith, eventually being granted conscientious objector status the following year.[59] Impending deployment may also have served as a trigger or catalyst for violence for both Akbar and Hasan.
Of course, refusal to do one’s duty based on religious (or, for that matter, any other) grounds is problematic. In the case of Hasan, his behavior in the years preceding the attack at Fort Hood has since been described as “overt displays of radicalization” and a missed opportunity for earlier intervention.[60] However –while preventative action must be pursued whenever possible– it is important to note here that none of these four individuals openly expressed their intention to commit acts of violence. It was later found that Akbar had written about his desire to kill soldiers in his personal diary, but of course this was private.[61] A far more significant indicator was Hasan’s communication with Anwar al-Awlaki, who was by that time already a suspected terrorist. As a result, Hasan was briefly investigated by the FBI; however they failed to piece together the extent of his communications and ultimately dismissed them as “research”, given his documented interest in Islamist ideology.[62] Contact with known or suspected terrorists should represent a major red flag, yet in this case was overlooked. In the other three remaining cases such connections were absent altogether. Indeed, notwithstanding Hasan’s links to Awlaki, all four inside attackers were lone actor terrorists, which severely limits opportunities for detection. In cases like this, the expression of “extremist” beliefs (in this context, including the perceived incompatibility between faith and military service), must be taken very seriously, especially when accompanied by a history of behavioral and/or mental health problems.[63] Such indicators may well stop short of establishing clear terrorist sympathies or violent intent, but they may still provide grounds for some form of intervention. Pending the results of an investigation, this might potentially include restriction of access to firearms, revocation of security clearances, mandatory counselling, voluntary or involuntary discharge or other measures depending on the specific case and tools available. Yet it is also worth bearing in mind that disciplinary or other measures based on low-level potential indicators of radicalization, perhaps including faith-based grievances, may present procedural and even legal difficulties. Ultimately, based on the empirical record, insider attacks by Western military recruits are likely to remain rare, yet cannot be ruled out in future, meaning that clear, preventative policies must nevertheless be in place.
Espionage
A third internal threat involves espionage, i.e. stealing of sensitive information, by service members with a jihadist agenda. There have so far been just two confirmed cases that the author is aware of, both in the U.S., plus one suspected case in France. In the first case, a Navy signalman named Hassan Abu Jihaad (originally Paul Hall) sent classified information about battleship movements to a pair of British jihadists while serving aboard the USS Benfold between August 2000 and September 2001.[64] He was honorably discharged in 2002 and was not arrested until 2007, eventually receiving a sentence of ten years for disclosing national defense information. The second case involved another convert to Islam, a specialist in the National Guard named Ryan Anderson. Between January and February 2004, a few weeks before he was due to serve in Iraq, he attempted to make contact with Islamist extremists online and supplied information –including details of U.S. Army movements, troop strength, tactics and weapons systems– to individuals he believed were members of AQ (in reality the FBI[65]). A military tribunal found him guilty of attempting to provide intelligence to the enemy and sentenced him to life in prison. Finally, in January 2015, French police discovered that a female gendarmerie named Emmanuelle C. –also a convert, who was reportedly in a relationship with a wanted criminal and confederate of French jihadist Amedy Coulibaly– had accessed the “suspect person’s file” more than sixty times without authorization. Although it is unclear exactly what she did with the information that she accessed, she was dismissed from her job and given a year of probation.[66]
In comparison to the insider attack cases described above, the recorded instances of espionage appear to have been even more low-key, with –from what is publicly known– little indication of the perpetrators’ extremist beliefs and no reported history of problematic conduct during their military careers. However, for espionage to occur there must necessarily be some form of contact with external parties, which represents a key point of vulnerability. Neither of the first two offenders were particularly discreet. In the former case, Abu Jihaad used his official Navy email address and it is doubtful that such a case would go undetected for so long in the post-9/11 era (it seems he was eventually discovered only after 9/11 due to the arrest of his contacts in the U.K.[67]). In the latter case, Anderson had a long history of reaching out to others on a variety of online forums and –having turned to extremism–eventually came into contact with an Internet vigilante (someone posing as a jihadist) who then passed his information to the FBI.[68] Less is known about the French case, but she clearly failed to effectively hide her criminal associations. In today’s world, it seems quite unlikely that jihadist “spies” would be so careless. In addition, the widespread availability of encrypted software, now included in day-to-day applications, means that similar, contemporary offenders may find it easier to conceal their communications. As a result, the point of acquisition of sensitive materials and any other suspicious behavior within the workplace become even more important as potential opportunities for detection and intervention.
Military Veterans Involved in Terrorism
Analytically –since military veterans become civilians once they leave active duty– we now come full circle, as internal threats merge back into the external category. Although it has become an issue of increasing concern, there is a long history of former members of Western (as well as other) militaries becoming involved in violent jihad. In the U.S., military veterans were part of the very first jihadist networks that emerged during the late 1980s and early 1990s, with close ties to the New York and New Jersey terror-cells responsible for the first World Trade Center attack and the related plot –overseen by Omar Abdel Rahman– to bomb various New York landmarks. They included individuals such as Ephron Gilmore aka Tahir (allegedly an instructor at AQ’s al-Farooq camp in Afghanistan[69]), Clement Rodney Hampton-El (one of the “landmarks” plotters and an active supporter of the Bosnian mujahideen[70]), Abu Ubaidah Yahya (aka Carl Taylor, who provided training in the U.S. and assisted Hampton-El’s efforts in the Balkans[71]) and “Abu Abdullah” (who led a team of fourteen former American soldiers, again in support of the mujahideen in Bosnia[72]).
Similar examples have continued to come to light. In late 2001, shortly after being discharged from the Australian Army, suffering from post-traumatic stress disorder (PTSD), a former private named Matthew Stewart made his way to Afghanistan where he joined the Taliban and AQ. In October 2015 he resurfaced in Syria as a member of Jabhat al-Nusra (JN), using the name Usama Hamza Australi.[73] Several more American veterans have also tried and occasionally succeeded in joining terrorist organizations overseas, including Craig Baxam,[74] Eric Harroun[75] and Tairod Pugh.[76] According to the German military counterintelligence service, 29 former Bundeswehr soldiers have travelled to Syria and Iraq to join extremist groups[77] and at least ten French soldiers have reportedly deserted and done the same.[78] While the vast majority of these individuals have joined terrorist-insurgencies overseas (becoming so-called foreign fighters), some have also been involved in planning domestic attacks. For instance, in July 2015 it was revealed that a former signalman in the French navy, identified as Djebril A., had been plotting, along with three confederates with links to the so-called Islamic State (IS), to kidnap and behead the commanding officer at Fort Bear on the south coast of France.[79] In a previous case uncovered in 2007, a former cadet in the British Territorial Army, who had been jailed for assaulting a fellow cadet and was suffering from significant mental health problems, was convicted of planning an attack on his old base from within prison.[80] In October 2014, a radicalized US Navy veteran named Zale Thompson took things a step further, assaulting a group of New York City police officers with an axe before being shot and killed.[81]
The overall number of Western military veterans becoming involved in Islamist terrorism appears to be small, yet still significant. It is particularly troubling, given the knowledge and skills that such individuals possess, which can potentially be transferred to organizations like AQ and IS and be put to use in planning and conducting domestic attacks. From the military’s perspective, there is relatively little that can be done once an individual leaves the organization – especially if there are no signs of radicalization beforehand, in which case it essentially comes down to the work of intelligence and law enforcement agencies. However, if a person is identified as a potential violent extremist prior to leaving active duty, steps should be taken to reduce the level of risk if possible and clear policies must be in place to enable the notification of civilian security services and/or support agencies.
Summary and Concluding Remarks
Western jihadist threats to the military can be divided into overlapping external and internal categories, depending on the status of the perpetrators. Chief among the external threats are domestic plots and attacks, which have become significantly more frequent in recent years. The plots most likely to come to fruition involve lone actors using firearms, motor vehicles and/or knives to ambush soldiers in public places. Although such attacks are exceptionally difficult to prevent, basic measures such as raising awareness among troops, avoiding wearing uniforms or insignia in public and travelling in groups of two or more, can significantly reduce the likelihood of casualties. As with all of these threats, it is also important to establish lines of communication with relevant civilian law enforcement and intelligence agencies to facilitate timely sharing of information and effective collaboration if and when necessary.
A second external threat that has become increasingly frequent in recent years involves hacking of government computer systems in order to obtain sensitive information – in particular PII for military members and their families, who may then be targeted for attack. Military organizations obviously have a responsibility to maintain adequate security for websites and online databases and efforts must be made to document all relevant breaches of security, to review the techniques that Western jihadi hackers and their allies are employing and to identify the specific vulnerabilities they have so far exploited, in order to harden online defenses.[82] Individual service members may also contribute by maintaining basic online security – for example, safeguarding personal information on social media and taking steps to avoid falling victim to phishing scams or viruses.
The third and final external threat involves jihadist acquisition of potentially dangerous military materials, ranging from training manuals to weapons and related accessories. Given that it is not uncommon for such materials to go missing and sometimes end up on the black market, it would seem prudent for those responsible to review their security arrangements.
Internal threats are much less common and yet also more troubling when they occur. To date, there have been very few verifiable examples of premeditated infiltration of the armed forces by Western jihadists and recent attempts have been lacking sophistication. Nevertheless, there are clear incentives for trying to infiltrate the military and authorities in a number of countries have expressed concern over this issue. The obvious implication is to ensure adequate background checks for all new recruits (to include reviews of social media, travel patterns, associations and any information held by law enforcement and intelligence agencies).
The most serious internal threats are insider attacks conducted by radicalized individuals against fellow soldiers. Such cases have been mercifully rare and so far have occurred only in the American military. Based on this limited experience, they are most likely to be conducted by lone individuals (though perhaps in communication with known extremists or terrorists) and may display a history of problematic conduct, underachievement and faith-based grievances – most notably the increasingly fervent belief that being a Muslim is incompatible with military service. Some of these individuals may also exhibit mental health problems, although this is by no means guaranteed. Importantly, the inside attackers seen to date (at least those in the West) did not overtly express their intention to commit acts of violence. This means that the threshold for preventative intervention must come earlier, based on the above-noted indicators. The French Defense Security Protection Department (DPSD) has identified the following, additional factors as potential signs of extremism: “changes in dress, recurrent sick leave, [suspicious] travel, or theft of supplies or materiel.”[83] Accessing extremist websites or possession of related propaganda materials may also be added to this list. In reality, indicators of potential extremism may be weak, however, within such highly regulated and fraternal organizations, the chances that insider threats will be identified are increased.
Another internal threat –albeit extremely rare– involves espionage. The cases so far have been amateur and their impact minimal, although more serious instances cannot be ruled out in future. Potential warning signs might include any of the indicators noted above, naturally including contact with known extremists or visitation of related websites or other online platforms. In the absence of specific indications of jihadist tendencies, potential warning signs are likely to be similar to “ordinary” insider threats, which are covered in routine training.
Finally, it is now well-established that small, yet significant numbers of Western military veterans are becoming involved in violent jihad following their departure from the armed services. As noted above, it is important to share information on any suspected extremists with civilian security services as they transition to civilian life (if not before) but in the absence of prior indicators of radicalization there is little that military organizations can do, other than cooperate with subsequent investigations.
In conclusion, Western jihadist threats to the military have grown significantly in recent years. In particular, the most likely threats are external and come in the form of physical and cyber attacks, although it would clearly be a mistake to ignore internal threats, which have produced almost as many fatalities despite being less common. As much as the threat has grown, the overall likelihood and impact of Western jihadist actions against domestic military organizations remain relatively low. Moreover, the risk of both external and internal threats can be significantly mitigated by way of relatively basic security procedures. Western militaries must remain cognizant of “home-grown” jihadist threats and should certainly review security measures in line with this article. There are no grounds for complacency, yet there is also little reason for panic.
End Notes
[1] Tom Whitehead, “Isil Offered British Soldier Details for Fanatics to Attack Here as Delivery Driver Guilty of Plot to Kill US Troops” The Telegraph, April 1, 2016, http://www.telegraph.co.uk/news/2016/04/01/delivery-driver-guilty-of-isil-plot-to-kill-us-troops-in-uk/. Accessed April 1, 2016.
[2] Vikram Dodd and Josh Halliday, “Lee Rigby Murder: Michael Adebolajo and Michael Adebowale Found Guilty” The Guardian, December 19, 2013, http://www.theguardian.com/uk-news/2013/dec/19/lee-rigby-murder-michael-adebolajo-adebowale-guilty. Accessed December 19, 2013.
[3] Figures based upon databases for the U.S., U.K., Canada and Australia maintained by the author, with additional data for Europe based on Petter Nesser, “Chronology of Jihadism in Western Europe 1994–2007: Planned, Prepared, and Executed Terrorist Attacks” Studies in Conflict and Terrorism, (2008), 31 (10), 924–946; Petter Nesser, “Toward an Increasingly Heterogeneous Threat: A Chronology of Jihadist Terrorism in Europe 2008–2013” Studies in Conflict and Terrorism, (2014), 37 (5), 440–456. A number of additional cases where military targets were mentioned by plotters in passing but were not clearly focused upon are excluded from this analysis. Also excluded are an additional 12 plots targeting police, 10 of which were executed.
[4] “UK Trio Jailed for Preparing Acts of Terrorism” BBC News, April 25, 2013, http://www.bbc.com/news/uk-22294720. Accessed April 27, 2013.
[5] German security services had in fact switched the group’s hydrogen-peroxide for a lower concentration that would not create a viable explosive. This notwithstanding, they had acquired all of the necessary precursor components for manufacturing an extremely powerful improvised explosive device by the time of their arrest (Quirine Eijkmann, “The German Sauerland Cell Reconsidered” Perspectives on Terrorism, (2014) 8 (4) http://www.terrorismanalysts.com/pt/index.php/pot/article/view/363/html). Accessed April 20, 2016.
[6] An additional six cases involving planned attacks on domestic military targets also had links to FTOs but they were not seemingly involved in the plot.
[7] David McHugh, “Suspect Admits Killing US Airmen at German Airport” Associated Press, http://www.google.com/hostednews/ap/article/ALeqM5jH9IrV69nlJItBoYxnIi5ORZzJpg?docId=559fbc5fee164c5ebe0b325cc6d7f74d. Accessed September 3, 2011.
[8] “Toulouse Shootings: A Timeline of Events” The Guardian, March 22, 2012, http://www.theguardian.com/world/2012/mar/22/toulouse-shootings-timeline-mohamed-merah. Accessed April 23, 2016.
[9] “Paris Soldier Stabbing Suspect Hit With Terror-Linked Charges” France 24, May 31, 2013, http://www.france24.com/en/20130531-judge-charges-suspect-french-soldier-stabbing-attempted-murder-terrorism?ns_campaign=editorial. Accessed May 31, 2013.
[10] Ian Austen, “Hit-and-Run That Killed Canadian Soldier is Called Terrorist Attack” New York Times, October 21, 2014, http://www.nytimes.com/2014/10/22/world/americas/canadian-soldier-run-down-in-what-officials-call-act-of-terror-dies.html?emc=edit_tnt_20141021&nlid=59679535&tntemail0=y. Accessed October 21, 2014.
[11] Jordan Press, Mark Kennedy and Ian Macleod, “Ottawa Gunman Michael Zehaf-Bibeau Invoked ‘Jihad’ in Video Shot Minutes before Deadly Rampage” National Post, March 5, 2015, http://news.nationalpost.com/2015/03/05/ottawa-gunman-michael-zehaf-bibeau-invoked-jihad-in-video-shot-minutes-before-deadly-rampage/. Accessed March 7, 2015.
[12] Nicole Deshayes, “Driver Had 'Martyr' Aim in Attack on French Soldiers: Prosecutor” Yahoo News, January 2, 2016, https://www.yahoo.com/news/driver-wanted-kill-soldiers-guarding-french-mosque-prosecutor-154049063.html?ref=gs. Accessed January 2, 2016.
[13] Federico Bordonaro, “The October 2009 Terrorist Attack in Italy and its Wider Implications” CTC Sentinel, (2009) 2 (10) http://www.ctc.usma.edu/wp-content/uploads/2010/08/Vol2Iss10-Art2.pdf. Accessed September 21, 2012.
[14] Note that the perpetrator in this case was a lone actor who cried “Allahu Akbar!” during the assault and was found to be in possession of “Islamic fundamentalist literature” but was also suffering from mental health problems (“Isère. Un Déséquilibré Blesse un Gendarme D'un Coup de Couteau” Ladepeche.fr, May 7, 2013, http://www.ladepeche.fr/article/2013/05/07/1621397-isere-desequilibre-blesse-gendarme-coup-couteau.html. Accessed May 29, 2013; Kim Willsher, “French Anti-Terrorism Police Hunt Man Who Stabbed Soldier” The Guardian, May 27, 2013, http://www.guardian.co.uk/world/2013/may/27/french-anti-terrorism-hunt-man-stabbed-soldier. Accessed May 31, 2013.
[15] Kristina Sgueglia, “Chattanooga Shootings 'Inspired' by Terrorists, FBI Chief Says” CNN, December 16, 2015, http://edition.cnn.com/2015/12/16/us/chattanooga-shooting-terrorist-inspiration/index.html. Accessed December 16, 2015.
[16] Daveed Gartenstein-Ross, “GUEST POST: Abdulhakim Mujahid Muhammad (Carlos Bledsoe): A Case Study in Lone Wolf Terrorism” Jihadology, December 23, 2013, http://jihadology.net/2013/12/23/guest-post-abdulhakim-mujahid-muhammad-carlos-bledsoe-a-case-study-in-lone-wolf-terrorism/. Accessed October 23, 2014.
[17] Richard Warnica, “Suspect said ‘Allah Told Me to do This’ During Double Stabbing at Canadian Forces Recruitment Centre, Police Say” National Post, March 15, 2016, http://news.nationalpost.com/toronto/ayanie-hassan-ali. Accessed March 15, 2016.
[18] Note that the French National Gendarmerie falls under the responsibility of the Ministry of Defence. For the purposes of this analysis, gendarmes are therefore included as “military”, while regular police forces are excluded.
[19] “French Shooter Mohammed Merah Directed By Moez Garsalloui” SITE Intelligence Group, January 15, 2014, https://news.siteintelgroup.com/Featured-Article/french-shooter-mohammed-merah-directed-by-moez-garsalloui.html. Accessed March 15, 2016; Henry Samuel and Fiona Govan, “I am on an al-Qaeda Mission, Taunts Besieged Gunman who Shot Children” The Telegraph, March 21, 2012, http://www.telegraph.co.uk/news/worldnews/europe/france/9159322/I-am-on-an-al-Qaeda-mission-taunts-besieged-gunman-who-shot-children.html. Accessed March 15, 2016.
[20] This adds support to more tentative findings from a study of European jihadist plots published in 2014 (Petter Nesser and Anne Stenersen, “The Modus Operandi of Jihadi Terrorists in Europe” Perspectives on Terrorism, (2014) 8 (6), http://www.terrorismanalysts.com/pt/index.php/pot/article/view/388/771.
[21] Murray Brewster, “Security on Military Bases to be Reviewed by All-Party Commons Committee” CTV News, April 7, 2016, http://www.ctvnews.ca/politics/security-on-military-bases-to-be-reviewed-by-all-party-commons-committee-1.2849039#_gus&_gucid=&_gup=twitter&_gsc=EOaB0rK.
[22] Spender Ackerman and Ewen MacAskillin, “Junaid Hussain: British Hacker for Isis Believed Killed in US Air Strike” The Guardian, August 27, 2015, http://www.theguardian.com/world/2015/aug/27/junaid-hussain-british-hacker-for-isis-believed-killed-in-us-airstrike. Accessed April 23, 2016; “'The Islamic State Hacking Division': The Ardit Ferizi Network” Flashpoint, October 23, 2015, https://www.flashpoint-intel.com/home/assets/File/Flashpoint_ArditFeriziNetwork_Oct2015%281%29.pdf. Accessed April 23, 2016; Stalinsky and Sosnow, “Hacking in the Name of the Islamic State (ISIS)”.
[23] Data derived from: Benjamin Runckle, “Is the Islamic State a Cyber Threat?” War on the Rocks, September 9, 2015, http://warontherocks.com/2015/09/is-the-islamic-state-a-cyber-threat/. Accessed April 8, 2016; “Caliphate Cyber Army Disseminate Purported “CIA Leadership Home Addresses”” SITE Intelligence Group, December 21, 2015; “Former Islamic Cyber Army Hackers Release Alleged British Soldiers’ Info, Deface British Websites Under “#BritainUnderHackS” Campaign” SITE Intelligence Group, September 22, 2015; Steven Stalinsky and R. Sosnow, “Hacking in the Name of the Islamic State (ISIS)” MEMRI, August 21, 2015, http://www.memri.org/report/en/0/0/0/0/0/0/8714.htm. Accessed August 21, 2015.
[24] Stalinsky and Sosnow, “Hacking in the Name of the Islamic State (ISIS)”.
[25] “Ohio Man Indicted for Soliciting the Murder of Members of the U.S. Military” US Department of Justice, December 8, 2015, https://www.justice.gov/opa/pr/ohio-man-indicted-soliciting-murder-members-us-military. Accessed April 19, 2016.
[26] Dominic Casciani, “How Islamic State Group Supporters Targeted the UK” BBC News, April 1, 2016, http://www.bbc.com/news/uk-35893097. Accessed April 1, 2016.
[27] Michael Dobbs, “Britain a Refuge for Mideast Dissidents” Washington Post, October 7, 2001, https://www.washingtonpost.com/archive/politics/2001/10/07/britain-a-refuge-for-mideast-dissidents/45633c48-c5cc-49c5-846b-8479cab09c62/. Accessed April 23, 2016.
[28] Lawrence Wright, The Looming Tower: Al-Qaeda and the Road to 9/11 (New York: Alfred A. Knopf, 2006) 225.
[29] United Sates v. Barry Walter Bujol Jr, Application for a Search Warrant, United States District Court for the Southern District of Texas, Case 4:10-mj-00486, May 28, 2010, http://www.investigativeproject.org/documents/case_docs/1590.pdf. Accessed December 16, 2011.
[30] United States v. Mohammed Junaid Babar, United States District Court Southern District of New York, Case 04 CR. 528, June 3, 2004, http://www.investigativeproject.org/documents/case_docs/853.pdf. Accessed October 27, 2009.
[31] Eijkmann, “The German Sauerland Cell Reconsidered”.
[32] “French Jihadists Face Trial for Jewish Grocery Attack” The Local, November 13, 2015, http://www.thelocal.fr/20151113/20-french-jihadists-face-trial-over-on-jewish-grocer. Accessed April 23, 2016.
[33] Naina Bajekal and Vivienne Walt, “How Europe’s Terrorists Get Their Guns” Time, December 7, 2015, http://time.com/how-europes-terrorists-get-their-guns/. Accessed April 19, 2016.
[34] Geoff Chambers, “Pendennis Nine Terror Cell: Bush Hunt for Weapons Stash” Herald Sun, September 14, 2014, http://www.heraldsun.com.au/news/pendennis-nine-terror-cell-bush-hunt-for-weapons-stash/news-story/29e19544323ec140b03a08777bac18f3. Accessed April 19, 2016.
[35] Yves Mamou, “France: Jihad Infecting Army, Police” Gatestone Institute, March 16, 2016, http://www.gatestoneinstitute.org/7624/france-jihad-contaminating-army-police. Accessed April 20, 2016.
[36] See for example: Brigitte Bureau and Giacomo Panico, “Canadian military unable to account for all lost weapons” CBC News, March 8, 2016, http://www.cbc.ca/news/canada/ottawa/dnd-lost-weapons-registry-1.3481073. Accessed April 19, 2016; Stephen Stock, Michael Bott and Felipe Escamilla, “Unaccounted For: Hundreds of Guns Lost or Stolen From Bay Area Police Agencies Since 2010” NBC News, November 16, 2015, http://www.nbcbayarea.com/investigations/Unaccounted-For-Hundreds-of-Guns-Lost-or-Stolen-From-Bay-Area-Police-Agencies-Since-2010-350768311.html. Accessed April 19, 2016.
[37] Note that Mohamed Merah (cited above) had unsuccessfully applied to join the armed services in France on two separate occasions – once in 2008 and again in 2010. However, there is no evidence that he had ulterior motives at the time.
[38] See Peter Lance, Triple Cross: How Bin Laden’s Master Spy Penetrated the CIA, the Green Berets, and the FBI (New York, Harper Collins), Kindle Edition; Wright, The Looming Tower.
[39] “Hawaii Resident Charged with Making False Statements in a Matter Involving International Terrorism” Federal Bureau of Investigation, October 26, 2010, https://www.fbi.gov/newyork/press-releases/2010/nyfo102610.htm. Accessed April 23, 2016.
[40] “Kansas Man Pleads Guilty in Plot to Explode Car Bomb at Fort Riley in Manhattan, Kansas” United States Department of Justice, February 3, 2016, http://www.justice.gov/opa/pr/kansas-man-pleads-guilty-plot-explode-car-bomb-fort-riley-manhattan-kansas. Accessed February 4, 2016.
[41] Jana Winter, “GI Jihadi: Ex-Army Recruit's Online Terror Threats Exposed” Fox News, April 1, 2014, http://www.foxnews.com/us/2014/04/01/exclusive-self-professed-jihadist-was-weeks-away-from-basic-army-training.html. Accessed April 20, 2016.
[42] Dina Temple-Raston, “FBI Tracking 100 Suspected Extremists in Military” NPR, June 25, 2012, http://www.npr.org/2012/06/25/155710570/fbi-checking-100-suspected-extremists-in-military. Accessed April 20, 2016.
[43] Soeren Kern, “Spain: Islamic Radicals Infiltrate the Military” Gatestone Institute, November 22, 2013, http://www.gatestoneinstitute.org/4061/spain-military-islamic-radicals. Accessed April 20, 2016.
[44] Mamou, “France: Jihad Infecting Army, Police”.
[45] Michael Fischer and Susann Prautsch, “Are Islamists Using the German Military as Training Ground?” DPA, April 12, 2016, http://www.dpa-international.com/news/top_stories/are-islamists-using-the-german-military-as-training-ground-a-48933067-img-0.html. Accessed April 20, 2016.
[46] Manuel Roig-Franzia, “Army Soldier Is Convicted in Attack on Fellow Troops” Washington Post, April 22, 2005, http://www.washingtonpost.com/wp-dyn/articles/A7210-2005Apr21.html. Accessed April 7, 2013.
[47] “Profile: US Soldier Hasan Akbar” BBC News, April 29, 2005, http://news.bbc.co.uk/2/hi/americas/4496989.stm. Accessed April 7, 2013.
[48] Madeleine Gruen, “The Massacre at Fort Hood” NEFA Foundation, February 2010, https://s3.amazonaws.com/hsnnetwork/pdf/NEFA+Report+Massacre+at+Ft+Hood.pdf. Accessed April 23, 2016.
[49] “Hasan: ‘I Was Defending My Religion’” BBC News, August 18, 2013, http://kdhnews.com/military/hasan_trial/hasan-i-was-defending-my-religion/article_efda373c-07b7-11e3-9ff9-0019bb30f31a.html. Accessed August 20, 2013.
[50] “Alexandria Man Charged with Shooting at Military Buildings in Northern Virginia” Federal Bureau of Investigation, June 23, 2011, https://www.fbi.gov/washingtondc/press-releases/2011/alexandria-man-charged-with-shooting-at-military-buildings-in-northern-virginia. Accessed April 23, 2016.
[51] “Police Say Arrest of Soldier Foiled "Terror Plot"” Reuters, July 28, 2011, http://www.reuters.com/article/us-usa-soldier-forthood-idUSTRE76R49R20110728. Accessed April 23, 2016.
[52] Roig-Franzia, “Army Soldier Is Convicted in Attack on Fellow Troops”.
[53] Gruen, “The Massacre at Fort Hood”.
[54] “Marine Reservist in Custody after Pentagon Scare” Fox News, June 17, 2011, http://www.foxnews.com/us/2011/06/17/suspect-idd-in-pentagon-suspicious-items-probe/. Accessed June 29, 2011.
[55] Caitlin Gibson, “Pentagon Shooting Suspect Melaku Convicted of Unrelated Larceny Charges” Washington Post, November 14, 2011, https://www.washingtonpost.com/local/pentagon-shooting-suspect-melaku-convicted-of-unrelated-larceny-charges/2011/11/14/gIQAheqGMN_story.html. Accessed April 21, 2016.
[56] Manny Fernandez and James Dao, “Soldier Arrested in Suspected Bomb Plot Had Series of Disputes with Army” New York Times, July 29, 2011, http://www.nytimes.com/2011/07/30/us/30awol.html?_r=2. Accessed December 24, 2011.
[57] Madeleine Gruen, “Backgrounder: Sgt. Hasan Akbar” NEFA Foundation, January 2010, http://www.nefafoundation.org/miscellaneous/nefa_akbarbackgrounder.pdf. Accessed April 7, 2013; Roig-Franzia, “Army Soldier Is Convicted in Attack on Fellow Troops”.
[58] Gruen, “The Massacre at Fort Hood”.
[59] “Rogue U.S. Soldier Planned to Detonate Bombs at Fort Hood and then Shoot Survivors” Daily Mail, November 9, 2011, http://www.dailymail.co.uk/news/article-2059362/Rogue-U-S-soldier-planned-detonate-bombs-Fort-Hood-shoot-survivors.html. Accessed December 24, 2011.
[60] Joseph I. Lieberman and Susan M. Collins, A Ticking Time Bomb: Counterterrorism Lessons from the U.S. Government’s Failure to Prevent the Fort Hood Attack (Washington DC: U.S. Senate Committee on Homeland Security and Governmental Affairs, 2011) 31 http://www.investigativeproject.org/documents/testimony/377.pdf. Accessed March 10, 2011.
[61] Gruen, “Backgrounder: Sgt. Hasan Akbar”.
[62] Lieberman and Collins, A Ticking Time Bomb, 8.
[63] Note that only one inside attacker had a documented history of mental health problems – namely Hasan Akbar, who had been diagnosed with depression aged 14, seemingly suffered from sleep apnea as an adult and was also seen talking to himself while on duty (Gruen, “Backgrounder: Sgt. Hasan Akbar”).
[64] “Former Member of U.S. Navy Sentenced to 10 Years in Federal Prison for Disclosing Classified Information” United States Department of Justice, April 3, 2009, https://www.justice.gov/opa/pr/former-member-us-navy-sentenced-10-years-federal-prison-disclosing-classified-information. Accessed April 23, 2016.
[65] “Military Jury Convicts Soldier of Trying to Help al-Qaeda” USA Today, September 3, 2004, http://www.usatoday.com/news/nation/2004-09-03-anderson_x.htm. Accessed January 31, 2012.
[66] Mamou, “France: Jihad Infecting Army, Police”.
[67] “Former Member of U.S. Navy Sentenced to 10 Years in Federal Prison for Disclosing Classified Information”.
[68] “Mom by Day, Terrorist Hunter by Night” ABC News, June 5, 2006, http://abcnews.go.com/http://abcnews.go.com/. Accessed June 2, 2010.
[69] J.M. Berger, Jihad Joe: Americans Who Go to War in the Name of Islam (Washington DC: Potomac Books, 2011) 61–64; Transcript of FBI interview of El Sayyid Nosair, December 27, 2005, http://www.scribd.com/doc/35687185/FBI-302-El-Sayyid-Nosair-12-20-05. Accessed November 17, 2011.
[70] Berger, Jihad Joe, 12, 51–78; United States v. Omar Ahmad Ali Abdel Rahman et al, United States District Court Southern District of New York, Case S5 93 CR. 181 (MBM), August 2, 1995, http://hurryupharry.org/wp-content/uploads/2010/05/US-vs-Omar-Ahmad-Ali-Abdel-Rahman.pdf. Accessed August 11, 2012.
[71] Berger, Jihad Joe, 12, 64–69; United States v. Omar Ahmad Ali Abdel Rahman et al.
[72] “Bosnian Mujahedeen Will Welcome, Not Threaten, U.S. Soldiers” Associated Press, December 4, 1995, http://groups.yahoo.com/group/istiqlal/message/11222. Accessed November 25, 2011.
[73] Michael Safi and Joshua Robertson, “How a Queensland Man Went from Australian Soldier to al-Qaida Militant” The Guardian, October 27, 2015, http://www.theguardian.com/world/2015/oct/27/how-a-queensland-man-went-from-australian-soldier-to-al-qaida-militant. Accessed October 28, 2015.
[74] “Former U.S. Soldier Who Sought to Join Terrorist Group Convicted and Sentenced to Seven Years in Prison
Defendant Destroyed Computer Evidence Before Leaving the U.S. to Join the Foreign Terrorist Organization al Shabaab in Somalia” Federal Bureau of Investigation, January 13, 2014, http://www.fbi.gov/baltimore/press-releases/2014/former-u.s.-soldier-who-sought-to-join-terrorist-group-convicted-and-sentenced-to-seven-years-in-prison. Accessed January 19, 2014.
[75] “Former U.S. Soldier Charged with Conspiring to Use Destructive Device While Fighting with al Qaeda-Affiliated Group in Syria” Federal Bureau of Investigation, March 28, 2013, http://www.fbi.gov/washingtondc/press-releases/2013/former-u.s.-soldier-charged-with-conspiring-to-use-destructive-device-while-fighting-with-al-qaeda-affiliated-group-in-syria. Accessed April 7, 2013.
[76] “Jury Finds Air Force Veteran Guilty in First Conviction After Trial in the United States for Attempting to Travel Overseas to Join ISIL” United States Department of Justice, March 9, 2016, https://www.justice.gov/opa/pr/jury-finds-air-force-veteran-guilty-first-conviction-after-trial-united-states-attempting. Accessed March 10, 2016.
[77] Fischer and Prautsch, “Are Islamists Using the German Military as Training Ground?”
[78] Mamou, “France: Jihad Infecting Army, Police”.
[79] “France Foils Terror Beheading Plot at Base” Sky News, July 17, 2015, http://news.sky.com/story/1520790/france-foils-terror-beheading-plot-at-base. Accessed April 22, 2016.
[80] “'Sick' Bomb Planner is Locked Up” BBC News, July 28, 2009, http://news.bbc.co.uk/2/hi/uk_news/8172933.stm. Accessed June 29, 2010.
[81] Peter Foster and Rob Crilly, “New York Axe Attacker: Navy Veteran who Converted to Islam” The Telegraph, October 24, 2014, http://www.telegraph.co.uk/news/worldnews/northamerica/usa/11186983/New-York-axe-attacker-Navy-veteran-who-converted-to-Islam.html. Accessed October 24, 2014.
[82] Note that an earlier review of jihadist hacking operations concluded that “the overall impact and sophistication of jihadist hacktivists’ attacks have been relatively low and will likely remain as such in the near term” (Christopher Heffelfinger, “The Risks Posed by Jihadist Hackers” CTC Sentinel, (2013) 6 (7), https://www.ctc.usma.edu/posts/the-risks-posed-by-jihadist-hackers. Accessed October 22, 2015). The successful hacking of government/military websites during 2015 arguably represents an escalation of such operations in terms of the profile and sophistication of the targets, as well as the sensitivity/value of some of the data acquired, it is unclear whether the techniques being used have become more refined.
[83] Mamou, “France: Jihad Infecting Army, Police”.
