Virtual War – A Revolution in Human Affairs
Stefan J. Banach
War, of any kind, is the ultimate failure of mankind. Yet, in the course of human endeavors, we have found another way in which to wage global war – in this case, Virtual War in Virtual Battle Space. The “Technology Singularity” espoused by Vernor Vinge and Ray Kurzweil, is the fundamental source and accelerant for Virtual War. [i] The Vinge and Kruzweil articulation of the “Singularity” of biological and machine intelligence is much closer than most of us understand. The majority of the people in the world are caught up in the inertia of everyday activities, and the emergence of Virtual War is opaque to most of us. To that end and for clarity, the world is experiencing Virtual War – A Revolution in Human Affairs.
Virtual War transcends the “normal” revolutions in military affairs or traditional security rubrics that are discussed in Pentagon forums, within the defense industrial base and among law enforcement agencies. Virtual War is drastically transforming global human affairs as we know them, and in ways that we do not yet understand. Eric Schmidt got it right when he opined that, “the Internet is the first thing that humanity has built that humanity doesn't understand, it is the largest experiment in anarchy that we have ever had.”
Carl von Clausewitz defined war in his legendary tome, On War. His definition of war follows:
War is nothing but a duel on an extensive scale. If we would conceive as a unit the countless number of duels which make up a war, we shall do so best by supposing to ourselves two wrestlers. Each strives by physical force to compel the other to submit to his will: his first object is to throw his adversary, and thus to render him incapable of further resistance. War therefore is an act of violence to compel our opponent to fulfil our will.[ii]
As a former wrestler, I believe that Virtual War provides unprecedented opportunities to destroy or control the will of an opposition actor, with an unceasing cadence of global virtual munitions from an increasing number of delivery platforms. Virtual War does not require an act of violence to succeed in controlling the will of an individual, group or population. This is an important distinction and opportunity, relative to war, which occurs in Physical Battle Space.
Virtual War is a global systems approach to achieve social control. Virtual War heuristics include: offensive and defensive cyber capabilities, social media, information operations (e.g. “Fake News”), artificial intelligence, stealth technologies and cloaking techniques. The end game is to control and influence the will of a person, group, or larger population to achieve ideological objectives over time in support of a cause or a specific sponsor.
The Good News. As we are seeing every day, Virtual War is truly transformational and will continue to change all of our lives in ways that are difficult to fathom. Kurzweil notes the following positive aspects of the emerging technological changes in his 2005 publication, The Singularity is Near:
Revolutions in genetics, nanotechnology and robotics will usher in the beginning of the Singularity. Sufficient gains in genetic technology should make it possible to maintain the body indefinitely, reversing aging while curing cancer, heart disease and other illnesses. Much of this will be possible thanks to nanotechnology, the second revolution, which entails the molecule by molecule construction of tools which themselves can "rebuild the physical world." For example, nanotechnology-based manufacturing devices in the 2020s will be capable of creating almost any physical product from inexpensive raw materials and information. Finally, the revolution in robotics will really be the development of strong Artificial Intelligence (AI), defined as machines which have human-level intelligence or greater. This development will be the most important of the century, "comparable in importance to the development of biology itself.” [iii]
The United States, and indeed the world, is experiencing the birth pains of the coming exponential technological change that Vinge and Kurzweil predicted in the 1990’s, and in 2005. The “2020’s” noted above, from Kurzweil’s manuscript, are just years away. Nevertheless, inane debates about whether the Singularity will occur in five years or fifty years, misses the point completely in the context of history. Billions of years in evolutionary technological advancements serve as a backdrop, and we are behind the power curve, relative to the substantial changes that are right in front of us.
Let the drastically reduced lifespans of commercial companies be a guide in this regard. The average age of an S&P 500 company is currently under 20 years, decreased from 60 years in the 1950s, according to Credit Suisse. The Wall Street firm says the trend is accelerating and blames the disruption on unprecedented technological advancements. In that vein, Andy Serwer, Editor-in-Chief of Yahoo Finance, asked this important question at the 2018 Davos World Economic Forum, “If robots, AI, nanotechnology, machine learning, and 3D printing are going to be doing all the work, what the heck will human beings do nine to five?” This question portends more challenges than simply the re-training and the re-education of a pending massive unemployed work force. The world has seen, since the events on 9/11, that large populations of unemployed or under-employed people are not helpful in terms of maintaining global security and stability. Tangentially, sixteen years of attrition warfare and the banality associated with fighting predominantly in Physical Battle Space are financially unsustainable. The National Security Act of 1947, which is the basis of U.S. National Security, is seventy-one years old and is collapsing under the weight of Virtual War exigencies. As Peter Drucker noted, “The greatest danger in times of turbulence is not the turbulence; it is to act with yesterday's logic.”
The New Normal. Inherent in Virtual War, is the unprecedented kinetic maneuvering of one civilian population against another, which has produced hundreds of mass casualty events around the world, since 9/11. The civilian vs. civilian terror attacks, on 9/11, were planned using the Internet of Things (IoTs) – in Virtual Space - prior to the execution of the physical attacks on the respective civilian targets in the United States.[iv] Hundreds of other terror attacks have taken place around the world since 9/11, and were planned and coordinated in Virtual Space before the horrific attacks took place in Physical Space. What will the world’s security paradigm for warfare and law enforcement look like when the Internet of Things (IoTs) evolves to the Internet of Everything (IoET), that includes much more powerful Nano-Biologically enhanced human beings?
Non-lethal Virtual Space activities also occur continuously around the world in social and political domains that target domestic and foreign matters, with the aim to gain and maintain control of a particular narrative to influence an audience to act in a certain ideological manner. The growing liminality which exists today, by way of virtual space activity, is causing a truth crisis, as the velocity of human interaction and the velocity information is at an all-time high. The average person does not know what to believe given the ubiquity of information and the obvious bias in government and within traditional and non-traditional media sources.
On the socio-economic front, there is a growing divide between the rich and poor, as the middle class struggles with sustainability. There is also a widening chasm between globalist and nationalist. The 1648 Westphalian nation-state model is at odds with a growing number of emergent empowered actors who do not rely on monolithic state entities to govern their behavior in virtual or physical space. Each of these aforementioned variables are all interdependently joined and, to varying degrees, are technologically driven fissures in the world today.
The stark changes that we are seeing today have been forecasted by many people dating back to John von Neumann and Alan Turing in the 1930s during their foundational work in computer experimentation and nascent artificial intelligence theory.[v] More recently, our national and international leadership, is having difficulty framing and naming the emergent exponential technological changes that are impacting us in new ways every day. Today we are seeing the symptoms of technological change in our daily lives, but are not synthesizing the interrelated patterns of activity, and do not know how to cope with the exponential change.
Prophetic Warning. Per Kurzweil’s prose, these forecasted changes will be tantamount to a technological tsunami - which is now at our doorstep, in the context of the evolutionary timeline. Given the accelerating pace of technological advancements, we should expect significant social change. An unprecedented rupture of all the classic: learning, leadership, management, strategy development, planning and governance archetypes, that are in existence today, is absolutely possible.[vi] This externality will move the world from its current state of complexity to chaos. The end result will be the first of many instances where biological and machine intelligence forever transforms warfare and our existence as we know it. The pending exponential technological advancements will move civilization to a completely new era.[vii] This will be an era where humans will not be able to survive without machine intelligence, augmented synthetic strength and artificial stealth capabilities on the web or in physical space.[viii] Subterranean and extra-terrestrial options will be sought to support life and will be made possible by new technological advancements, that were previously unimaginable. The nation-state or actors who can learn the fastest, and optimally frame and reframe their strategies the best, will rule the day in a world that fights predominantly in Virtual Space, and only as necessary in Physical Space, as it is too costly on multiple fronts.
Framing and Naming the Virtual War Paradigm. The United States’ leaders, who have responsibility to win the Nations wars, have lost personal mastery for warfare in our time. The U.S. is fighting the wrong war, with the wrong policies, strategies, doctrine, tactics, techniques and procedures. The logic for warfare in our time is askew as we have seen at previous junctures in history. The value of mechanization versus the horse and the application of air power on modern battlefields during the 1919-1939 inter-war period, are notable historical examples where new technological advantages, were not immediately appreciated by “the experts.”
Asymmetric Warfare, Political Warfare, Gray Zone Operations, Hybrid Warfare, Cyber Warfare, Cognitive Maneuver, et al., are competing heuristics that are bantered about continuously in security think tanks and in the halls of the Pentagon in an attempt to frame and name the paradigm for warfare in this era. Each of the aforementioned warfare nomenclatures and frameworks, that are being used to describe warfare today, are propagated in the Virtual Domain and are further shaped in the Cognitive and Moral Domains, before they are manifested in the Physical Domain environments, which include: air, land, sea and outer space. The entity that controls the Virtual Domain and masters Virtual War Campaigning first, will indirectly achieve social control, and will win every war they engage in, at pennies on the dollar. The Russian Gerasimov Doctrine and the Chinese 2025 Strategic Plan are both indirect approaches to achieving social control of both domestic and foreign populations through the use of Virtual War technology driven conventions.
The Goal of Virtual War. Social Control is the goal of Virtual War. China and Russia are well suited in this pursuit given their respective repressive governance cultures. Invoking Sun Tzu is appropriate as he summed up the goal of Social Control in this quote, “The supreme art of war is to subdue the enemy without fighting.” Global “Social Control” is possible for the first time in the history of the world. Burgeoning Social Control capabilities are nested in: global satellite imagery, swarms of civilian and military aerial drones, public camera surveillance systems in our “smarter cities”, iPhone tracking protocols, Fitbit devices, the internet, artificial intelligence, DNA, Social Security numbers, Driver’s License numbers, Credit Reports, online personal health records, and all the associated digital personal and financial contrivances which exist today.
In the years ahead, the Social Control challenge will become acute as every human being will potentially have bio-medical nanotechnologies embedded in them to ensure optimal health. Each of these medical Nano devices will have a digital interface that presents both new opportunities for increased wellness and new vulnerabilities. Humans will be susceptible to the traditional biological viruses which exist today. New technologies will need to be developed to protect us from artificial virus “infections” that could be mass transmitted in targeted societies, using the embedded Nano medical implants that will serve as the host within our bodies.
The synthesis of each of these personal data points, technologies and capabilities into a coherent global Virtual War Campaign Plan is possible now. The United States desperately needs a “Virtual Manhattan Project” to Design a national security policy, strategy and doctrine that will prevent the attainment of a global “Social Control” capability by China, Russia or another empowered set of actors. This should be a civilian led, U.S. government agency and military supported, “Whole of Nation” enduring Design effort; and it should be something our Allies support.
The Merits of Virtual War. Virtual War schemas enable an actor to gain and maintain 24/7 indirect global influence, with people and machines, at a fraction of the investment with plausible deniability. This approach reduces risk to the mission and the risk to “physical assaulting forces”. Virtual War techniques also eliminate the tyranny of global strategic & operational reach that are limiting variables for physical battle space forces. Theater-level access and early entry conundrums are also expunged and “Virtual Warriors” are now capable of delivering virtual munitions on demand to advance national policy objectives for scenarios involving China, North Korea, Russia & Iran, which was not possible before. Virtual War will continue to change international law vis-à-vis what constitutes an act of war, and it will also challenge the longstanding cognitive and moral standards for what constitutes a just war.
The New Maginot Line. Metaphorically, the overwhelming propensity for Physical Battle Space Maneuver is the United States’ modern-day Maginot Line. Like the French, from 1919-1939, the U.S. has spent more money than all of its Allies combined in the Global War on Terrorism (GWOT) since 2001, executing Physical Battle Space Maneuver activities. Like the French prior to WWII, the United States’ leadership is preparing for the last war it won and does not see the Virtual Blitzkrieg that is upon it every day. There is an ongoing complete envelopment of all the significant U.S. national interests by way of Virtual War - or - Virtual Battle Space Maneuver, and it is happening right in front of us.
Creating an effective Virtual War acumen requires a systemic reframe of leadership development and the creation of non-standard doctrine, tactics, techniques and procedures for how our national security forces and law enforcement agencies compete in Virtual Space. Virtual Space is the decisive terrain and securing it is the decisive operation. Military operators and law enforcement agents should not proceed in to Physical Battle Space without first gaining and maintaining Virtual Battle Space superiority. All U.S. national security forces and law enforcement agents require a new suite of Virtual Weapons Systems to win the Nation’s wars. What Virtual War non-standard doctrine and weaponry needs to be developed and fielded? When will our operators and agents be taught, armed and trained in their use? These are incredibly important questions that should guide our thinking and strategic focus, if we desire to remain a superpower country going forward.
Reframing U.S. National Security. The U.S. Department of Defense (DoD) is not structured to learn about Virtual War and is incapable of keeping pace with the interactive complexity that is generated on today’s Virtual Battlefields. The DoD of the United States will never win another war – as structured and as led. This is not a pejorative statement intended for any current or past leader, who has served in the DoD. Rather, this observation addresses an a priori reasoning culture that has been created and sustained within the DoD since its founding in 1949. The DoD hierarchical learning system is incapable of keeping pace with the emergent rhizomic learning system that is organically deployed in virtual space by billions of actors each day. The power leadership and the single loop learning “Process Trap” that has engulfed the U.S. security apparatus has made our country non-competitive in global security matters for the long-term.
The future U.S. security apparatus must be inundated with “disruptors” and there needs to be shared leadership between the private and public sectors for the defense of the United States if we have any chance of competing on a global scale. Doing the same thing, and expecting a different result, after sixteen years of attrition warfare more than fulfills Eisenstein’s definition of insanity. Peter Senge’s Fifth Discipline provides some of the answers to this conundrum. Personal mastery in warfare can only be achieved by adjusting the mental models and structures that are in use today. Enterprise-wide systems thinking and the establishment of a team learning culture, beyond DoD boundaries, is required to create a “Whole of Nation” shared vision for how to win wars now and in the future. Using the full range of the strategy palette and the methodological strategy development techniques espoused by Martin Reeves and Henry Mintzberg is essential. The leading change and the design principles authored by John Kotter and Bryan Lawson, and so many others, are also critical and should be considered as we Design the future.
The decisive arm of war and conflict now, is the U.S. National Industrial Base. The U.S. citizenry possesses the means to fight and win on Virtual Battlefields. The U.S. citizenry live and operate, unknowingly, in a Virtual Battlespace that they call home and work. With a few exceptions, the American people and U.S. industry are on the sidelines; for now. Virtual War requires triple loop learning solutions. If we are to be successful, a completely new set of governing principles must be designed, outside the existing DoD paradigm, to live, fight and prosper in Virtual Battle Space. The national security approach that the U.S. uses in the future cannot be structured or operate the way our defense apparatus does at the moment.
The Arnold Avatar. Enemies of the United States learned after the 1991 Gulf War that it is a fool’s errand to fight the U.S. military in direct combat. The many actors who comprise the system of opposition to the U.S. are much more willing to engage in an algorithm vs. algorithm virtual battle, vice a tank on tank battle in physical space. The rivals of the U.S., have used the indirect approach in Physical Battle Space for nearly two decades, by employing individual or small groups of assailants, in terror attacks that produce tremendous carnage as seen in Paris, London and Orlando; and many other locations.
Virtual War presents a new repertoire of instruments for a friendly or opposition agent to groom targets and networks without immediate detection or reprisal. The Arnold Avatar is one such technique. This approach consists of four scenarios. The first scenario is to deceive your opposition over the course of a series of human to human engagements until the target is positioned for elimination, arrest or exploitation. The second pillar in the Arnold Avatar approach is for a single human, or small group of humans, to establish an online identity and influence a targeted population via social media to achieve desired behaviors in physical space. Human to machine and machine to machine spoofing operations are the other two techniques inherent in the Arnold Avatar that should be used on daily basis in a Virtual Battle Space Maneuver Campaign Plan. (Note Figure #1 below).
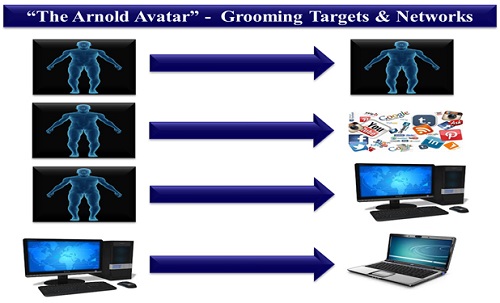
Figure #1
Holographic Armored Formations. Virtual projections of tank and other armored vehicle holographic formations, which emit physical, electronic, cyber and social media signatures, will be possible, on future battlefields. This is an example where a “Singularity” in warfare will occur as virtual war and physical war elements are aligned. Holographic armored formations will be detectable and seen by opposition forces. Once the opposition force identifies and engages the tank holographic formation, friendly forces will be able to direction find and triangulate the opposition force’s electronic and digital signatures and their firing locations. After this is accomplished, friendly forces can destroy the enemy using Physical Battle Space weapon systems. As we have seen, enemy forces and criminal organizations will develop or buy this new technology and co-evolve with U.S. fighting forces and our law enforcement agencies as soon as these “cloaking” capabilities are available.
The Aloha Scenario. This is an excerpt from Wikipedia, concerning the recent false alarm on Oahu, that has serious implications for U.S. leadership as they deal with future tenuous security impasses.
On January 13, 2018, a false ballistic missile alert was issued via the Emergency Alert System and Commercial Mobile Alert System over television, radio, and cellphones in the U.S. state of Hawaii. The alert stated that there was an incoming ballistic missile threat to Hawaii, advised residents to seek shelter, and concluded "This is not a drill". The message was sent at 8:07 a.m. local time. The governor wanted to warn people by Twitter of the error but he couldn't remember his password. A second message, sent 38 minutes later, described the first as a "false alarm". State officials blamed a button pushed in error during an employee shift change at the Hawaii Emergency Management Agency for the first message. Governor David Ige publicly apologized for the erroneous alert, which caused panic and disruptions throughout the state. The Federal Communications Commission and the Hawaii House of Representatives immediately announced investigations into the incident.[ix]
This event occurred with no outside virtual influence on leaders of the government in the State of Hawaii. The technology exists today, for an adversarial nation-state or group of technically capable actors to construct malicious virtual avatar scenarios that are capable of spoofing key political leaders at the state and national-levels to act in an irrational manner. Potential spoofing avatars could be used in a nuclear weapons scenario that is focused on nK, or another country, that causes unintended disastrous reciprocal action by the United States.
A tangential historical case in point, with far less complexity relative to virtual influence, is the July 3rd, 1988, Iranian Air Flight 655, that was shot down by the United States Navy guided missile cruiser USS Vincennes. The USS Vincennes entered Iranian territorial waters after one of its helicopters was fired upon from Iranian speedboats operating within Iranian territorial limits. Moments later, 290 civilians died in a scenario which is benign, compared to the modern day virtual scenarios that can be weaponized and transmitted via opposition cyber, social media, and fake news outlets, from dozens of sources at once, to a single decision-maker in a time compressed in-extremist environment.[x]
The U.S. National Security Imperative. “Whole of Nation Warfare” is now required to sustain the American way of life. The leadership of the United States must communicate the threat accurately to the American people, and mobilize the massive virtual industrial base, which resides in the U.S., to overcome the extraordinary challenge that is before our country. The “Anti-Fragile” attributes that are required to win in both Virtual Battle Space and in Physical Battle Space are not resident in the schemata which are employed by the U.S. DoD and broader governmental leadership today. This needs to change quickly if we intend to regain personal mastery of warfare in our time and maintain our way of life.
U.S. leaders must perpetually reimagine and redesign the way forward, to see the virtual, cognitive, moral and physical domains as evolving interdependent public-private frames of reference for decades and centuries to come. Faced with a growing network of opposition actors, the current reactionary decision-making infrastructure puts the U.S., and our way of life, at a disadvantage versus more agile adversaries who seek Virtual War. Exploiting a retinue of national, and international, thought leaders to design a lasting national technology-based policy, strategy and doctrine for the United States is the imperative of our time. Do we have the foresight to see, and the will to overcome the unprecedented threats that are confronting our republic and way of life?
[i] Vinge, The Coming Technological Singularity Essay, 1993; Kurzweil, The Singularity is Near, 2005.
[ii] Clausewitz: On War. Book 1, Chapter 1.
[iii] Kurzweil, The Singularity is Near, 2005, Chapter 5 & Pages 13-28.
[iv] Banach, From 9/11 to London: The Need for Virtual Battle Space Maneuver Doctrine, Small War Journal, June 2017
[v] https://link.springer.com/chapter/10.1007/978-3-642-36751-9_2, by S Istrail - 2012
[vi] Kurzweil, The Singularity is Near, 2005, Page 23.
[vii] Ibid, Chapter 2.
[viii] Ibid, Chapter 2.
[ix] 2018 Hawaii False Missile Alert – Wikipedia.
