Understanding the Complexity of the Improvised Threat
Norman T. Lihou and Bret Doyle
Improvisation on the battlefield is not new. However, the improvised threats that are faced today have increased the scope, scale, and degree of battlefield improvisation impact at all levels of warfare. With technology accelerating knowledge proliferation and the expanding access of technological diffusion, non-state actors have been able to create unprecedented risks to US forces and our partners. The current forms of improvised threats, improvised explosive devices (IEDs) and small unmanned aerial systems (sUASs), are low cost; easy to build; allow for indirect tactics; can target joint forces, friendly forces, government officials, and unprotected populations; can be used indiscreetly or as a systems-based approach to targeting[i]; and can challenge conventional military power. Ultimately, while an improvised threat is a combination of weapons, systems or tactics, the definitive distinction is in the inability of tactical commander ability to counter and stop the cascading impacts.
The improvised explosive device has been one of the greatest 21st century improvised threats to U.S. and allied personnel and continues to be responsible for friendly causalities around the globe. While joint forces prepare for conventional force on force maneuvers, the lessons learned over the decades of facing insurgencies, terrorism, piracy, transregional criminals, drug traffickers, and other threat networks must not be lost. The improvised threat has proven to be an effective means by asymmetric forces to engage conventional forces. Never before have the joint forces had to put so much effort into countering, an improvised threat. The improvised explosive device cost many lives, money, and directly impacted the way joint forces deploy and operate. The effort to counter the IED also required unprecedented interagency cooperation and new information-sharing capabilities, which required a whole of government approach that continues to this day.
While most closely associated with violent extremist organization (VEOs), the use of IEDs and sUASs can be expected to be a continuing and growing risk for any future U.S. conflict. Nation-state competitors such as Russia, Iran, North Korea, and even China, have observed and learned from the U.S. challenges caused by improvised threats in Syria, Afghanistan and Iraq. Already, there has been media reporting of a Russian sUAS attacking a Ukrainian ammunition dump with a thermite grenade that destroyed billions of dollars’ worth of material[ii]. Further, the threat from state and non-state adversary overlap, since states like Iran and Russia use non-state proxies to pursue their interests[iii]. Any conflict involving the United States and nation-state adversaries should be anticipated to use improvised threats as an integral part of irregular warfare.
More importantly, technological change is also increasing the likelihood that tomorrow’s threats will be improvised. Potential adversaries now have greater access to emerging commercial technologies than ever before, posing a serious threat to national security[iv]. With online communications and global connectivity, new technologies spread with increasing speed as commercial-off-the-shelf hardware can be purchased and delivered around the globe. Distributed manufacturing capabilities, such as 3-D printing, and increased access to online technical education are allowing for increasingly distributed innovation and manufacture. This can effectively “democratize” potential improvised threat technologies for even the remotest VEOs[v]. Understanding the commonalities between the risks posed by improvised threats, as well as the shared approaches to countering them, can help better prepare the United States and the Joint Force to avoid strategic and battlespace surprise as new improvised threats emerge.
VEOs have demonstrated the ability to develop, train, equip and employ new and effective theater-wide military-like capabilities in a matter of months. Contributing to the surprise factor is the adversary’s ability to produce these improvised threats largely within the operational environment under the control of friendly forces. In prior conflicts, this type of widespread, large scale and significant capability development was the purview of national level research and development programs. Previous developments of new threats weapons and systems took place in a homeland and required a multi-year timescale. These new trends and developments enable this new level of adversary field-based innovation show no signs of abating, this aspect of conflict with irregular forces can be expected to continue into the foreseeable future.
Improvised Threat Characteristics
Essentially, improvised threats begin with an adversary intent to overcome a friendly capability. Adversaries, historically, primarily non-state actors, then develop the idea through a process of devising a weapon, system, tactic, organizational structure, technology, or a combination thereof, to create an adversarial advantage. Although improvised threats are primarily employed by non-state actors, their success can lead to adoption by state actors and/or state sponsorship of research and refinement. Once an attack proves successful, it can be a catalyst for future attacks by other threats. Aided by modern communications, adversaries have been able to propagate successful changes quickly across the battlespace, or beyond to other theaters.
Improvised threats are generally locally fabricated, modified or developed; however the local environment may not provide all of the necessary resources. This has led to global support lines of communication that deliver needed resources, which were then distributed throughout the joint operational area to the local threat networks. The employment of an improvised threat is driven by the availability of resources in the local environment, the impact of the friendly presence and capability, and the effect of improvised threat counter measures. Employment often occurs in a flexible manner, and with rapid innovation, inside the decision cycle of their opponent, giving the adversary a battlespace advantage.
An improvised threat can be described as an adaptively applied tactical capability leveraged to provide a cascading impact against a friendly advantage. The improvised threat has a number of key characteristics derived from how they are developed and employed:
- Adaptively applied – addresses the innovative and/or rapidly evolving nature of improvised threats. This also includes adversary employment of improvised threats being informed by their understanding of the environment and friendly advantages, and their ‘adaptation’ to them.
- Tactical – improvised threats are employed and conducted at a tactical level.
- Cascading impact – an improvised threat elicits a succession of actions, processes or operations, each of which triggers or initiates the next impact. The improvised threat can cross the operational levels of war (tactical, operational, and strategic) as well as spread across geographical areas (transnational and transregional).
- Friendly advantage – this addresses the role of improvised threats in overcoming, neutralizing or otherwise countering friendly advantages such as freedom of movement or force protection. Friendly advantage encompasses more than just US forces alone as an I-T can impact military or non-military partners.
Not every improvised action or attack would rise to the level of an ‘improvised threat’. As noted, improvisation itself has been a feature of warfare and conflict from the earliest points in human history. Although improvised threats are employed at a tactical level; key to understanding an improvised threat is that the collective tactical impacts aggregate to impact the operational and strategic levels. This is referred to as improvised threat cascading impacts. An example is given in Figure 1, for the IED case.
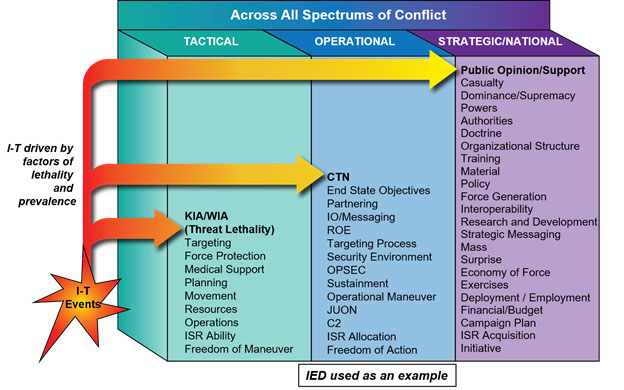
Figure 1: Improvised threat (I-T) Cascading Impact Chart
Improvised Threat Framework
Although current improvised threat is seen in the forms of IEDs and sUASs these are not the only types of improvised threats that a Commander can expect to face in the future. Modified systems, such as sUAS have provided new intelligence, reconnaissance, surveillance and command and control capabilities to our adversaries, even if they have not directly caused many casualties on the battlefield, yet. However, while the IED is categorized as an improvised weapon the sUAS does not easily fit into that category. Further, improvised threats could also fall into the category of ad hoc tactics, techniques and procedures (TTPs) that have been replicated or encountered throughout the battlespace. As modifications to technologies emerge and the adversary collects on friendly counter-measures, TTPs, and the improvised threat event success, that knowledge will be used to further develop capabilities. Therefore, the potential risk from modified systems or ad hoc TTPs cannot be discounted and must be identified as early as possible for Joint Forces to be proactive for the tactical commander.
Therefore, the improvised threat becomes a parent category of improvised weapons as well as two other sub-categories, modified systems and ad hoc TTPs. These categories have been designed as a framework which allows for expansion of additional types as the adversary continues to develop other improvised threats. The following are the first three sub-headers under the improvised threat (See Figure 2):
- Improvised Weapons – such as improvised explosive devices or other types of weapons.
- Modified Systems – such as small UAS’s. Modified systems are not always a lethal threat, however these systems are modified from the original intent. In the sUAS example, this involved using hobbyist and commercial UASs and both applying them for military purposes, as well as “do-it-yourself” modifications to them.
- Ad Hoc TTPs – such as a localized new TTP being fielded at the tactical level for a specific purpose. An Ad Hoc TTP is about the way and new goal that an improvised threat is being employed. To date, these have been applied to overcome a specific friendly security measure, countermeasure, collection, or identification capability. Once successful, the Ad Hoc TTP will be shared throughout the entire threat network and to other geographical areas.
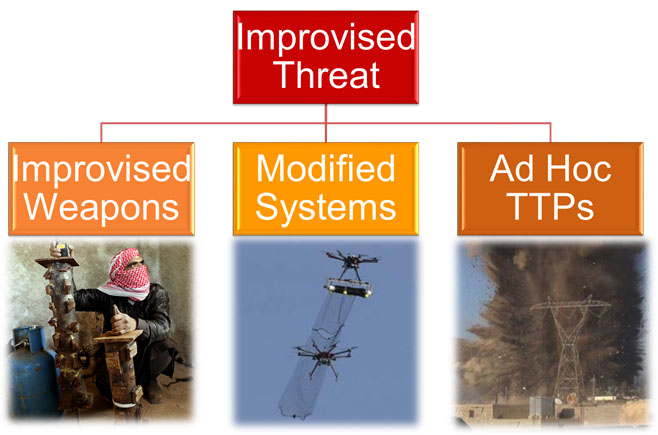
Figure 2. Improvised threat Framework
Though the improvised threat may originate as an individual or small group of incidents, once known to be successful it is replicated by adversary forces to become a standard way of operations. The spread and frequency of improvised threats can quickly affect an entire theater or more. Due to their widespread use they can have cascading impacts that counter, deny or disrupt friendly force advantages. These emergent higher-order impacts arise from the interaction of numerous improvised threat events from across the operational environment, rather than as a result of individual improvised threat attacks. Due to this complexity, the operational and strategic impacts of numerous tactical uses of improvised threats have been difficult to identify and anticipate.
The friendly advantage that is impacted can vary depending on the nature of the improvised threat. Although examples of improvised threats such as IEDs have impacted freedom of movement and force protection, different improvised threats could impact across a range of friendly capabilities. The adversary sUAS now challenges the previous conception of air superiority that was one of the strengths of joint forces while providing real-time command and control to direct attacks. Further, improvised threats can have transnational and transregional effect as the impact spreads. As with the use of IEDs during the 2004 Madrid train bombings, a single improvised threat event can generate a global level impact. This occurrence had strategic geopolitical impact where an effect was almost felt immediately as the Spanish voters brought in a new government that then removed Spain from the Iraq Coalition.
Approaches to Countering the Improvised Threat
While improvised threats have proven to be an endurance challenge to joint forces methods have emerged to begin to successfully counter them. With their quick development and propagation, local commanders are often unable to successfully counter improvised threats with the available resources or capabilities. Likewise, normal national acquisition and force development processes cannot respond quickly enough to counter or anticipate the evolution of improvised threats. As a result, rapid procurement processes, such as joint urgent operational needs statements (JUONS) and force adaptation methods, have proven necessary for us to accelerate our OODA loop (observe-orient-decide-act) and regain the advantage.
Further, improvised threats are often connected to or supported by a wide range of threat network groups which can be targeted and countered. Both improvised weapons and modified systems have been employed heavily by insurgent and terrorist networks. Criminal networks have also been known to use both, at least occasionally and have been adept at applying Ad Hoc TTPs to enable smuggling. VEOs have attempted to employ toxic chemicals in IED attacks and are known to be interested in other ways to use improvised weapons or systems to deliver WMD payloads. Countering these threat networks involves applying network engagement approaches to interacting with friendly, neutral, and threat networks, conducted continuously and simultaneously at the tactical, operational, and strategic levels, to help achieve the commander’s objectives within an operational environment. Network engagement provides a framework for the JFC to create friendly networks with far-reaching capabilities to engage neutral networks and counter threat networks.
Concluding Thoughts
Commanders have had to respond to and counter battlefield surprise throughout history. Yet, there has never been the imperative need to be prepared for innovative and adaptive weapons, systems and tactics on the scale of the improvised threat. If the threat can be stopped at the tactical level, then the impact will not be felt at the operational and strategic levels. The United States, and the Joint Force, must not just learn how to counter specific or niche improvised threats as they arise on the battlefield. It is imperative to learn how to anticipate emerging improvised threats in such a way that the problem continues to stay at the tactical level. Beginning to think about improvised threats holistically is the first step on the path to meeting this challenge.
Establishing a unified approach to addressing improvised threats would enable the joint force to both better anticipate new threats as they emerge and better apply existing knowledge and experience with improvised threats such as IEDs and sUASs toward countering them. By thinking systematically about improvised threats, it would effectively help U.S. commanders begin to ‘expect the unexpected’ and mitigate surprise. Countering an improvised threat is a complex issue that deserves operational and strategic attention by providing tactical commanders with the resources to rapidly deter and neutralize emerging improvised threats[vi].
The opinions and characterizations in this article are those of the authors and do not necessarily represent official positions of any agency, organization, employer or company.
End Notes
[i] Rassler, D. (2018). The Islamic State and Drones: Supply, Scale, and Future Threats West Point Combatting Terrorism Center. Retrieved from https://ctc.usma.edu/islamic-state-drones-supply-scale-future-threats/
[ii] Mizokami, K. (2017, July 27). Popular Mechanics - How Your World Works. Kaboom! Russian Drone With Thermite Grenade Blows Up a Billion Dollars of Ukranian Ammo. Retrieved August 5, 2108, from http://www.popularmechanics.com/military/weapons/news/a27511/russia-drone-thermite-grenade-ukraine-ammo/
[iii] Jones, S. (2018) “America’s Counterterrorism Gamble” Center for Strategic and International Studies. https://www.csis.org/analysis/americas-counterterrorism-gamble
[iv] Greef, T. (2018) “The Pentagon can’t develop technology quickly enough to thwart enemies. Here’s one way to help.” Defense News. https://www.defensenews.com/opinion/commentary/2018/08/01/the-pentagon-cant-develop-technology-quickly-enough-to-thwart-enemies-heres-one-way-to-help/
[v] Ackerman, G. and Jacome, M. (2018) WMD Terrorism: The Once and Future Threat, PRISM vol. 7, no. 3.
http://cco.ndu.edu/News/Article/1507339/wmd-terrorism-the-once-and-future-threat/
[vi] Pico, S. (2017). “U.S. Policies and Actions Aim To Counter Improvised Explosive Device Threats” U.S. Department of State. Retrieved from:
https://blogs.state.gov/stories/2017/07/17/en/us-policies-and-actions-aim-counter-improvised-explosive-device-threats
