Understanding and Countering Nation-State Use of Protracted Unconventional Warfare
Jason Rivera
Introduction
The United States’ national adversaries are engaged in protracted unconventional warfare strategies designed to counter-balance U.S. military might and enhance their own strategic security postures. Nations such as China, Iran, and Russia, while avoiding direct conflict with the U.S., are deploying unique and effective strategies across multiple domains within the spectrum of wartime operations. Though the U.S. remains dominant in the land, sea, air, and space domains, the nation’s adversaries are levying unconventional strategies designed to contest U.S. power within highly disputed and less understood domains to include cyberspace, the international information operations environment, and the human terrain environment. These unconventional warfare strategies, over a protracted period of time, have the effect of subtlety attritting the United States’ worldwide military presence, bleeding the American economy, sowing confusion, chaos, and distrust amongst U.S. policy makers, and wearing down the will of the American people.
This paper, at its core, is designed to identify, enumerate, and provide recommendations to counter protracted unconventional warfare strategies and will fulfill its design by accomplishing two things:
- Demonstrating how the nation’s adversaries operate in such a manner as to aggressively achieve their national security objectives while simultaneously remaining below the threshold of what would be considered an act of war, let alone a universally understood and condemned act of aggression. It is below this threshold that the United States must engage its adversaries if the U.S. is to counter its adversaries unconventional wartime strategies.
- It will deliver strategies designed to directly engage the United States’ adversaries below the threshold of war as well as the means to strategically posture the United States to levy flexible deterrent options.
By accomplishing the above two objectives, it is the intent of the author to demonstrate how the U.S. may effectively contain its strategic adversaries before the U.S. security posture is irreversibly eroded.
War by Other Means
Upon recognition that nuclear weapons had rendered unrestricted conventional war all but obsolete, China’s Communist Party Central Committee and the Central Military Commission endorsed in 2003 a military strategy known as “Three Warfares”.[1] This method of warfare is a dynamic, flexible doctrine that promotes war by other means to include psychological operations directed at the adversary, media warfare designed to exert influence over public perceptions, and legal warfare designed to exploit legal asymmetries to achieve political and commercial objectives.[2] This strategy – indirect, asymmetric, and protracted – is cunningly designed, over time, to combat a superior adversary that cannot be defeated through conventional means.
Over a thousand miles to the west in Southwest Asia, the Iranian leadership – specifically from the early 1990s onward – has begun to implement a strategy that leverages religious loyalism to enhance its strategic influence over the region and preserve the future of Shia Islam against the perceived threat of the Sunni majority. In Yemen, Iran is allegedly providing military support to the Houthi rebellion, a minority Shi’ite movement that stirs unrest and conflict in the war-torn nation.[3] During the height of the Arab Spring, Bahrain’s military leadership unrelentingly swore that Iran was providing both moral and material support to Shi’ite agitators;[4] all this while improvised explosive devices continue to be employed ever more frequently throughout the island nation as the Shi’ite majority becomes increasingly frustrated with the ruling Sunni minority. Most recently, it has been reported that Iran has deployed two or more battalions of its Iranian Revolutionary Guard Corps (IRGC) forces to assist Iraqi troops in combating the recent surge of insurgent activity from the Islamic State in Iraq and the Levant (ISIL), an offshoot of al-Qaeda.[5]
Another one-thousand miles to the north in the transcontinental nation of Russia, President Vladimir Putin is likely directing unconventional warfare operations in Eastern Europe. In 2008, at the commencement of the Russo-Georgian war, Russia inspired insurrection within Georgia by handing out Russian passports in the Abkhazia and South Ossetia regions as well as installing their own officials in key government posts.[6] This action was immediately followed by government sponsored cyber operations designed to disrupt and degrade the Georgian government’s capacity to communicate with its military and civilian population. Russia’s current strategy in Crimea and Eastern Ukraine bears remarkable similarities; in the early March 2014 timeframe, it was alleged that Russian operatives were distributing passports to ethnic Russians in the Crimean capital of Simferopol.[7] Shortly after, there appeared to be evidence of cyber operations targeted at Ukrainian telecom providers to include denial of service operations against websites and the physical severing of critical fiber optic cable trunks.[8] Still today, it appears that Russia continues to operate in Eastern Ukraine through the use of similar tactics.
Geographically, strategically, culturally, and politically distinct, all three China, Iran, and Russia appear to be engaging in war by other means through use of protracted unconventional warfare strategies in order to achieve their national security objectives as well as compete for global and regional influence amongst key populations. While not allied with each other in the same manner that the U.S. is allied with the NATO countries, there seems to be a tacit level of cooperation amongst these three nations that has the effect of eroding the United States’ worldwide diplomatic, information, military, and economic (DIME) advantages. Though the nation’s adversaries are varied in their method of strategy execution, these strategies share similarities as follows:
- The nation’s adversaries are strategically interpreting, intentionally distorting, and exploiting international laws and norms to achieve their objectives – this is the most important function of their protracted unconventional warfare strategies. They are aggressively testing the limits of laws and norms by asserting pressure upon the United States’ military posture while simultaneously remaining below the threshold of what would unequivocally be considered an act of war.
- As a secondary – yet almost equally important – effort, the United States’ adversaries are decisively engaged in full-spectrum psychological warfare. The term “full-spectrum” is specifically used to characterize a form of psychological warfare that has evolved far beyond military usage and into the realms of politics, culture, society, and commercial business. This full-spectrum psychological warfare is amorphous in nature and is beyond what most Americans and leaders are capable of comprehending or detecting. Some examples include but are not limited to English language foreign news, foreign political lobbyists, the establishment of Islamic cultural centers, or the exposure of sensitive U.S. intelligence programs by foreign entities with the intent of causing an adverse reaction amongst the American populous through the exploitation and manipulation of defectors.
- Because the U.S. remains the dominant worldwide force in all aspects of the DIME spectrum, the nation’s adversaries, at the time being, are avoiding direct confrontation with the U.S. in favor of strategies that use indirect approaches to erode the nation’s secondary or tertiary national security interests.
- Quick, technologically-centric conflicts favor the United States’ military warfighting posture. Therefore, the nation’s adversaries both now and in the future will engage in protracted, asymmetric conflicts with the United States over an indefinite period of time.
The Strategy of Protracted Unconventional Warfare
The United States’ adversaries are currently not capable of defeating the U.S. in conventional conflict and as such will avoid actions that are universally and unequivocally understood to be acts of war. Following this logic, the nation’s adversaries will avoid direct conflict with the United States’ military, yet will engage indirectly in conflict against the U.S. security posture so long as they can sustain this conflict over a protracted period of time and so long as they can levy asymmetric advantages against a technologically superior American nation. This should not be interpreted to mean that the nation’s adversaries will not engage in warfare against the United States, rather, that they will engage in unconventional warfare by interpreting, distorting, and exploiting the consensus formed by Westernized democracies in regards to international laws and norms. The most internationally accepted and well understood agreement on what constitutes an act of war is contained within article 2(4) of the United Nations Charter, which states that, “All Members shall refrain in their international relations from the threat or use of force against the territorial integrity or political independence of any state.”[9] Legal scholars have gone on to illustrate specific examples of what constitutes use of force, however, the threshold of “force” in terms of what the international community can agree upon is overwhelmingly vague. In the realm of kinetic conflict, it is generally accepted as true that a nuclear strike, state-sponsored terrorist attack, or conventional invasion would constitute use of force. There are other examples, but these three represent the most basic threats that national militaries train and equip for on a regular basis. The increasing prominence of cyber capabilities implies that use of force may also apply to information warfare. According to the Tallinn Manual[10][11], state-sponsored actions that result in death, injury, or destruction to persons or property would constitute use of force in cyberspace.[12]
As a secondary effort to the distortion and exploitation of international law, the United States’ adversaries are engaged in full-spectrum psychological warfare against the American population. Some of these psychological efforts are subtle and designed to influence the populous over time. Such strategic thinking is characterized by the writings of Li Bingyan[13], who proposed the following:
“How can you make a cat eat a hot pepper? You can stuff a pepper down a cat’s throat (the most difficult), you can put the pepper in cheese and make the cat swallow it, or you can grind the pepper up and spread it on his back. The latter method makes the cat lick itself and receive the satisfaction of cleaning up the hot pepper.”[14]
Other efforts of full-spectrum psychological warfare are more overt and direct. Consider Vladimir Putin’s September 2013 article in the New York Times calling for restraint in Syria. In this article, Putin appeals directly to the American people and political leaders, establishes a foothold with the American psyche by referencing the joint U.S. – Russian efforts of defeating the Nazis and establishment of the United Nations, and then follows on by sowing doubt in the United States’ justification for an attack on Syria.[15] Another example – though unconfirmed – is Russia’s harboring of Edward Snowden[16] for reasons that are possibly not humanitarian, but rather to leverage Snowden’s background and knowledge of U.S. intelligence practices to harm the image of the United States Government.
In the manner that the United States’ adversaries exploit international law and conduct full-spectrum psychological warfare, this paper contends that the strategist or the policy maker must be conscious of three categories of actions concerning the use of force. At the highest level of severity, there are those actions that are unequivocally and universally considered acts of war (nuclear strike, conventional invasion, societally destructive cyberattack, etc.). These actions, however, are few and far in between. In the conduct of warfare in the modern age, most actions fall below the universally agreed upon threshold of war and are legally ambiguous in respect to international laws and norms. The nation’s adversaries are keenly aware of this legal ambiguity; consequently, this is where they predominantly apply their efforts in order to avoid direct engagement with the United States. Per the various interpretations of Article 2(4) of the UN Charter, these legally ambiguous actions are considered by some nations to constitute use of force and are considered by others to fall below the threshold of force. These interpretations are almost always subjective and depend primarily on the interests of the involved nation-state(s). The following graphic is this paper’s proposal for the spectrum of nation-state warfare operations and the three categories considering use of force that must be understood by strategists and policy makers in order to counter unconventional warfare.
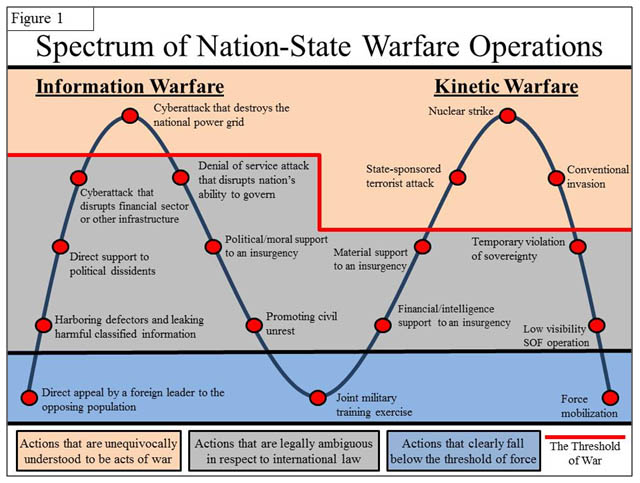
Figure 1 divides actions of warfare into two categories: information and kinetic. Note that these categories are not mutually exclusive of each other, rather, all actions fall somewhere along the spectrum between being purely kinetic or purely informational in nature. The higher up the action is along the spectrum, the more severe it is; the highest severity of actions being a nuclear strike or cyberattack that destroys the national power grid. Actions above the red line are, on the most part, universally accepted to meet the threshold of declaring war; actions below the red line are either legally ambiguous or clearly fall below the threshold of declaring war. Note that actions tend to be more legally ambiguous in the realm of information warfare due to a less robust understanding as a result of the shorter historical context of information warfare’s usage. Though a cyberattack that critically disrupts the financial sector may potentially be as damaging as or even more damaging than a state-sponsored terrorist attack or a conventional invasion, the realm of information warfare (especially cyberwarfare) tends to be more ambiguous due to issues of blame attribution and the interpretation of sovereignty as it relates to the physical and logical boundaries of computer networks and servers.
Of paramount importance, this paper’s graphic illustrates that most actions of warfare fall within the realm of legal ambiguity. This is not to say that actions within the gray area are legal according to international law, rather, there is a lack of consensus in terms of how nations choose to interpret their legality. In fact, most of these actions under a strict interpretation of international legal code are considered to be illegal. Consider the act of providing material support to an insurgency. In 1986, the International Court of Justice ruled against the U.S. for breaching its obligation under international law to not intervene in the affairs of another state by providing training and weapons to the Contras in Nicaragua.[17] This serves to demonstrate that many, if not most, actions within the gray area, could be considered a violation of article 2(4) of the UN Charter’s prohibition against the use of force. However, often times as is the case with international law, such rules and norms are subject to the interpretation of the nation-state in question. Consider the case of Russia’s use of “Patriotic Hackers” in 2007 to conduct distributed denial of service attacks against Estonian state websites, thereby crippling Estonia’s ability to perform governance.[18] According to the Estonian Minister of Defence, this cyberattack constituted a “national security situation”[19] which was followed on by a request for NATO support and the subsequent foundation of the NATO Cooperative Cyber Defence Centre of Excellence (CCD COE) in Tallinn, Estonia. Clearly the Estonians considered this attack to constitute a use of force. Clearly the Russians, while most certainly intending to use force, managed to distort the international perception of this use of national power in order to avoid a larger, disadvantageous conflict.
Given the lack of international consensus regarding the legality of many, if not most, actions of warfare, it is likely that United States’ adversaries’ use of protracted unconventional warfare strategies will continue to exploit this lack of consensus. Such a strategy is best characterized by early-twentieth-century Chinese strategic culture as well as their adoption of “Unrestricted Warfare”. In terms of the basis of Chinese strategy, Sangkuk Lee[20] states that:
China’s revolutionary leadership, such as Mao Zedong, emphasized that in order to defeat militarily and economically stronger enemies, political work to strengthen one’s own forces as well as to weaken enemies was one of the most decisive factors and needed to be systematically organized and pursued assertively.[21]
This philosophy would eventually lead to the writing of Unrestricted Warfare by two People’s Liberation Army (PLA) Air Force colonels, Qiao Liang and Wang Xiangsui. Unrestricted Warfare asserts that an adaptive and cunning warfighting force will:
… no longer use armed forces to compel the enemy to submit to one’s will, but instead will use all means, including armed force or non-armed force, military and non-military, and lethal and non-lethal means to compel the enemy to accept one’s interests… [this] means that all weapons and technology can be superimposed at will; it means that all boundaries lying between the two worlds of war and non-war, of military and non-military, will be totally removed.[22]
The above exerts concerning unconventional warfare strategies, though Chinese in origin, are not exclusive to Chinese strategic culture. As illustrated in earlier portions of this paper, both Russia and Iran also appear to be engaged in indirect strategies designed to achieve their national security objectives. With this assertion in mind, the next portion of this paper will discuss strategies designed to counter the unconventional warfare tactics used by the United States’ adversaries.
Countering Protracted Unconventional Warfare
Despite the asymmetric advantages gained through China, Iran, and Russia’s use of protracted unconventional warfare strategies, these nations are characterized by deeply seeded and fundamentally destructive strategic vulnerabilities. If exploited, the nature of these vulnerabilities presents strategic posturing opportunities to the United States and its allies; a brief description of these vulnerabilities is as follows:
- International Isolation: China, Iran, and Russia’s tactics of distorting international law and conducting nefarious operations have left them relatively isolated amongst the international community. This enables opportunities for the United States to leverage its diplomatic and military partnerships to the disadvantage of its adversaries.
- Societal Instability: China, Iran, and Russia suffer from socio-political instability and internal popular insurrection. According to a study conducted by Freedom House,[23] all three nations ranked amongst the worst nations in the world in terms of political rights and civil liberties.[24] Furthermore, ongoing incidents of political insurrection suggest that these nations remain vulnerable to internal upheaval, which implies opportunities to redirect the attention of the United States’ adversaries inward in order to quell unrest amongst their own populations.
- Damaged or Externally Dependent Defense Industrial Bases: China, Iran, and Russia’s defense industrial bases (DIB) are vulnerable to outside influence due to external dependencies and internal complications and therefore have the potential to be crippled through continued competition with the U.S. DIB.
The nature of the above vulnerabilities creates opportunities for the United States to levy two types of counter UW strategies. The first of these strategies is Counter UW through Direct Engagement. Direct engagement strategies encompass those counter UW capabilities/activities that the United States should develop and deploy immediately in order to directly counter its adversaries’ asymmetric, indirect, and international law distortive advantages. These strategies do not have a triggering point and are well-characterized by their immediacy and the direct targeting of an adversary’s vulnerabilities within the gray realm of legal ambiguity. The second strategy that can be leveraged is Counter UW through Flexible Deterrent Options. Flexible deterrent options are those counter UW capabilities/activities that the United States should develop, but not necessarily deploy, in order to coerce the adversary into ceasing their use of UW activities. These strategies are premised upon the credibility of the deterrent capability, the development of key decision points, and selective communication of those capabilities and decision points to the adversary. Using these two strategies, direct engagement and flexible deterrent options, the following portions of this paper will illustrate how the United States can counter unconventional warfare via the exploitation of its adversaries’ critical vulnerabilities.
Counter UW through the Exploitation of International Isolation
China, Iran, and Russia’s international relations are characterized by relative isolation due to their tendencies to cause regional disturbances through their exploitation, violation, and distortion of international law. China, for example, is not a member of any formal military alliance. Iran possesses only an unofficial alliance with Russia and possesses sectarian ties with the incumbent ruling parties of Syria and Iraq (both of which are currently under siege by external forces). Russia, the only one of the three nations to be part of a formal military alliance, is a member of the Collective Security Treaty Organization (CSTO)[25][26]. Of note, the CSTO’s membership has shrunk since its initial formation in 1992, having lost three of its former members to include Azerbaijan, Georgia, and Uzbekistan.[27]
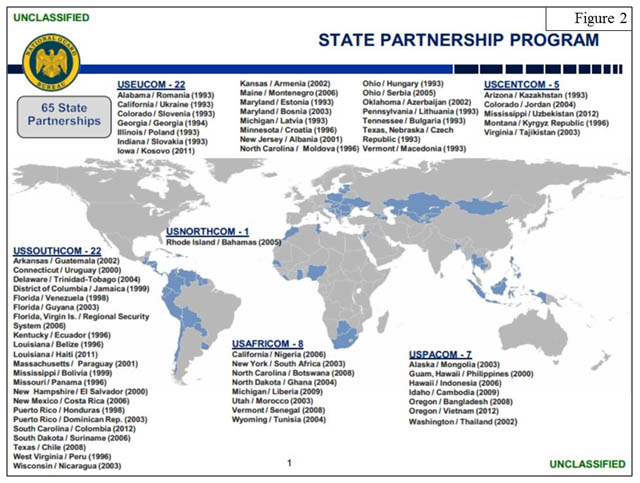
The United States, on the other hand, is party to seven collective defense agreements[28][29] and has 65 State Partners through the National Guard Bureau’s State Partnership Program.[30] Figure 2[31] illustrates the United States military’s global depth and is indicative of the magnitude of international cooperation the U.S. is capable of leveraging throughout the world; the same can be said for the United States’ strongest allies who, like the United States, are also able to leverage deeply rooted and advantageous alliances.
Given the United States’ strategic advantage in terms of its relations with the international community, the U.S. should exploit its adversaries’ relative isolation as follows:
- Counter UW Direct Engagement Isolation Strategy vs. Iran: The U.S. should adopt a sunk cost[32] mentality in Iraq and should acknowledge that Iraq will likely not become a fully-functioning democracy free from sectarian partisanship. The current successes of ISIL against Iraq’s conventional military force are indicative of the Iraqi military’s inability to competently defend itself. Moreover, there is little reason to believe that the United States’ provision of 300 special operations military advisers in Iraq[33] will change this dynamic. Instead, the U.S. should seek to exploit the present opportunities to be gained via ISIL’s presence. As stated earlier in this paper, Iran has deployed two or more battalions of IRGC into Iraq and may increase its commitment if the situation worsens. As of 25 Jun. 2014, it was reported that the Syrian government had carried out aircraft bombings against ISIL targets within Iraq.[34] Instead of viewing ISIL as a terrorist organization, the U.S. should instead view ISIL as an insurgency vying for power within Iraq. The United States should facilitate the conditions necessary to allow ISIL forces to directly engage Iranian IRGC and Syria’s Baathist led military troops while straying away from overt military operations in Iraq. Iran’s relative isolation from other regional powers such as Saudi Arabia and the rest of the Gulf States imply that, if successfully executed, the United States could foment the conditions necessary for Iran to fight an insurgency in its own backyard without any help from other regional stakeholders.
- Counter UW Direct Engagement Isolation Strategy vs. China: Specifically within East, South, and Southeast Asia, white paper reporting suggests that China actively conducts computer network operations (CNO) against South Korea, Taiwan, Japan, Indonesia, Vietnam, Singapore, and India,[35] Australia,[36] and New Zealand.[37] The United States should attempt to form a coalition of regional cyberspace stakeholders within the region in order to exploit China’s position of isolation that they have put themselves in via their nefarious activities in cyberspace. This coalition should be modeled on NATO CCD COE, which is headquartered in Tallinn, Estonia and was founded after Russia’s cyberattacks against the Estonian government in 2007. This organization should specifically exclude China and should be designed to increase China’s isolation in terms of their activities in cyberspace.
- Counter UW Flexible Deterrent Isolation Option vs. Russia: Of the five countries Russia is allied with via the CSTO to include Armenia, Belarus, Kazakhstan, Kyrgyzstan, and Tajikistan, the United States currently enjoys National Guard State Partnerships with all except Belarus. The United States should leverage these partnerships and attempt to form a partnership with Belarus in order to deter Russia’s behavior. Specifically, the United States should threaten to provide increased military training and funding efforts to current partners within the CSTO alliance and to form a partnership with Belarus if Russia does not cease its UW operations in Eastern Europe.
Counter UW through the Exploitation of Societal Instability
The United States’ adversaries are plagued by issues with societal instability and consequently engage in censorship and popular unrest suppression operations. While China’s issues in Taiwan are well understood amongst the national security community, less overtly and more recently, China appears to be struggling with Hong Kong as illustrated by the 100,000 demonstrators were present at a 4 June 2014 candlelight vigil marking the 25th anniversary of the Tiananmen Square massacre.[38] Of note, this event was followed up on 11 June 2014 by a 14,500 word Chinese government white paper stressing that Hong Kong does not have full autonomy and falls strictly under Beijing’s oversight, thus bringing the “one country, two systems” concept into question.[39] Iran, in 2009, experienced massive unrest and violence as a result of alleged corruption and fraudulent practices during that year’s presidential election. Also of note, along with Iraq and Turkey, Iran continues to periodically struggle with its ethnic Kurd population along its western borders. Lastly, Russia has historically struggled along its border regions with former members of the Soviet Union; today, Russia continues to struggle with Islamic and nationalist extremism in the Northern Caucuses. Additionally, Russia’s large country size and history of conquest makes it one of the most ethnically diverse nations in the world, to include more than 170 different ethnic groups and 27 official languages within its various regions.[40] This implies an opportunity to inspire ethnic fracture within the vast Russian state.
Conversely, the United States’ population enjoys robust political rights and civil liberties and is therefore unlikely to be held at risk if its adversaries were to attempt to inspire insurrection within the U.S. mainland. Given the nation’s hardened societal posture, the U.S. should exploit its adversaries’ problems with societal instability as follows:
- Counter UW Direct Engagement Social Destabilization Strategy vs. China: China faces problems with societal instability, most specifically within Hong Kong, Taiwan, and other major cities. To combat this instability in terms of stopping the flow of information that could cause unrest, China engages in strict Internet censorship practices. In an effort to cause instability within China and force them to divert resources from regional UW strategies that hamper the U.S. national security posture, the United States should develop and deploy a cyber capability that can open up externally hosted search engines to the Chinese population that are outside of the jurisdiction of Chinese Internet service providers thereby hampering the government’s censorship capabilities. The effect of such a capability would enable the Chinese population to have unrestricted access to information and contentious historical events such as the Tiananmen Square Massacre. Such an operation would ideally have the effect of forcing the Chinese government to focus resources internally to pacify its population.
- Counter UW Direct Engagement Social Destabilization Strategy vs. Russia: Russia, known for its heavy concentration of corrupt bureaucrats in its largest cities,[41] is responsible for one of the largest crime syndicates in the world. The United States should strategically leak or intentionally expose information gained through its intelligence disciplines that provides proof of corrupt relations between Russian officials and criminals; specifically, the U.S. should seek to deploy this strategy in regions within Russia that are newly acquired, prone to insurgent uprising, or where ethnic Russians comprise the population minority.
- Counter UW Flexible Deterrent Social Destabilization Option vs. Iran: The United States should issue a demarche to Iran announcing a policy of funding Iran-based dissident groups such as the Mjahideen-e-Khalq or Kurdish separatists in direct proportion to Iran’s funding and training of its own dissident groups throughout the region. I.e., for every dollar of direct funding, material, or training support provided by the Iranians, the United States should provide a higher yet directly proportionate amount funding to Iranian dissident groups, thereby making it increasingly difficult for Iran to sustain its foreign support efforts.
Counter UW through the Exploitation of the Defense Industrial Base
The United States’ adversaries’ defense industrial bases (DIB) are hampered by external dependencies and internal macroeconomic and procedural problems. China, for example, is incredibly dependent upon espionage efforts in order to remain abreast of the latest military innovations[42] and is therefore subject to misinformation and deception. Iran’s theater ballistic missile (TBM) program, its principal military deterrent, is reliant on external suppliers for key missile components and materials[43] and is therefore vulnerable to supply chain interdiction. Russia faces problems in terms of defense procurement and R&D planning to include a general inability to retain its top talent due to macroeconomic and internal policy.[44] Furthermore, Russia’s DIB has experienced substantial problems over the last decade in terms of financial solvency, with one-third of its arms manufacturers on the verge of bankruptcy.[45]
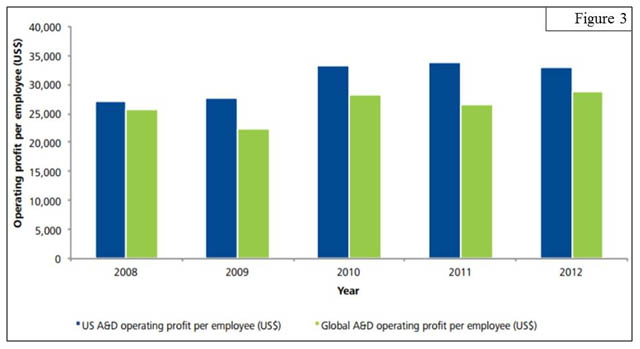
The U.S. DIB, on the other hand, is a world leader in the production of advanced military weapons systems and C4ISR[46] systems. Compared to the rest of the world, the U.S. DIB has financially outperformed the global market in terms of operating profit per employee (see figure 3)[47], implying that the U.S. can produce a higher quantity of higher quality weapons at a lower cost margin than other world competitors.
The U.S. should leverage the strength of its DIB in order to exploit its adversaries’ defense industry external dependencies and internal vulnerabilities as follows:
- Counter UW Direct Engagement DIB Exploitation Strategy vs. China: Given the emphasis on China’s CNO espionage programs, the United States should endeavor to develop custom designed honeynets[48] containing counter-data in order to defend the schematics and plans contained within the most sensitive DIB networks.[49] Such counter-data could include custom designed malware that, if exfiltrated in an unauthorized manner, would directly harm the adversary, activate a callback module, or notify the local police authorities and the media (thereby naming and shaming Chinese personnel engaged in CNO espionage); another option would be to seed intentionally flawed data within the honeynet in order to indirectly harm the adversary by sowing misdirection, confusion, and false intent.[50]
- Counter UW Direct Engagement DIB Exploitation Strategy vs. Iran: Iran’s perceives their TBM inventory as an important deterrent capability[51] which provides them the strategic latitude to promote substate conflict abroad through state proxies and insurgent groups such as Hezbollah, Hamas, and the Yemeni Houthi Rebels. So long as the current U.S. Central Command air defense posture remains evenly matched against Iran’s TBM force and so long as Iran believes in the integrity of its TBM key technology and materials acquisition program, Iran will continue to maintain confidence in deterrent. Given Iran’s perception, the U.S. should engage in a three-part counter UW strategy comprised of the following:
- U.S. policy makers and military leaders should publically state that they are seeking to degrade and/or disrupt Iran’s TBM program, thereby raising the Iranian alert posture.
- The U.S. should engage nation-state and non-state actors who facilitate the Iranian TBM acquisition process and should financially compete with the Iranian acquisition program. This will serve to drive up the price of TBM components and materials as well as cause distrust in the acquisition process due to U.S. competitive involvement.
- U.S. intelligence and special operations forces (SOF) should engage in TBM supply chain interdiction in order to replace functioning missile components with faulty missile components. Occasionally, the U.S. intelligence community (IC) should intentionally leak information (true or false) to the Iranians regarding the success of its supply chain interdiction operations.
- Counter UW Flexible Deterrent DIB Exploitation Option vs. Russia: The U.S. DIB should directly compete with the Russian arms sales industry in order to apply downward pressure on Russian sales quotas and sales revenues. Given this strategy, the U.S. must not allow Russia to gain market footholds in newly formed conflict zones. Iraq’s recent acquisition of fighter jets from the Russian defense industry as a result the United States’ inability to deliver F-16 jets to the Iraqi military is a mistake that cannot be repeated.[52] Upon applying sufficient pressure on the Russian DIB and further exacerbating Russia’s internal macroeconomic challenges, the United States should issue an ultimatum to the Russian leadership stating that if they do not cease their UW activities in Eastern Europe, the U.S. will increase its DIB sales to nations within the CSTO alliance, thereby striking at the heart of the Russian arms sales industry.
Conclusion
Though the United States adversaries’ currently enjoy the advantages gained through their asymmetric activities, these advantages are in a perpetual state of flux and are vulnerable to U.S. sponsored counter unconventional warfare (UW) strategies. This paper has demonstrated that China, Iran, and Russia can be directly engaged and flexibly deterred through exploitation of their international isolation, societal instability, and vulnerable defense industrial bases. By levying counter UW strategies that play to the United States’ principle strengths and exploit its adversaries’ principle weaknesses, the United States can, over time, attrit and eventually defeat the UW strategies employed by China, Iran, and Russia.
The United States’ struggle versus its primary nation-state adversaries is likely to be a protracted and borderless conflict fought within the realm of legal ambiguity. In many ways, this conflict resembles the Cold War between the United States and the former Soviet Union. Battles will be fought indirectly and success will have to be measured in terms of long-run gains and losses. The key difference, however, is that today’s conflict is likely to be fought within unconventional warfighting domains to include cyberspace, the international information operations environment, and the human terrain environment. Nonetheless, like the battles fought throughout the Cold War and the Soviet Union’s subsequent collapse in 1991, it stands to reason that the more legally just, socially cohesive, economically sustainable, and politically sound society will prevail; all of which the U.S. is characterized by in abundance and conversely is lacking within the societal constructs of United States’ primary nation-state adversaries.
End Notes
[1] Stefan Halper, (2013) “China: The Three Warfares,” University of Cambridge, 11.
[2] Ibid., p. 12-13
[3] Anthony Cordesman, et al., (2013) “The Gulf Military Balance Volume III: The Gulf and the Arabian Peninsula,” Center for Strategic & International Studies, v.
[4] Bahraini Royal Air Force Officer in discussion with the author, February 2011.
[5] Amir Abdallah, “Iran deploys military to fight Sunni ISIL insurgents in Iraq,” www.iraqinews.com, http://www.iraqinews.com/iraq-war/iran-deploys-military-fight-sunni-isil-insurgents-iraq/ (accessed 17 Jun. 2014).
[6] Uri Friedman, “Putin’s Playbook: The Strategy Behind Russia’s Takeover of Crimea,” The Atlantic, http://www.theatlantic.com/international/archive/2014/03/putins-playbook-the-strategy-behind-russias-takeover-of-crimea/284154/ (accessed 18 Jun. 2014).
[7] Ibid.
[8] Jason Rivera, “Has Russia Begun Offensive Cyberspace Operations in Crimea?” The Georgetown Security Studies Review Forum, http://georgetownsecuritystudiesreview.org/2014/03/02/has-russia-begun-offensive-cyberspace-operations-in-crimea/ (accessed 18 Jun. 2014).
[9] U.N. Charter, art. 2, para. 4.
[10] NATO CCD COE, (2014) “The Tallinn Manual,” NATO Cooperative Cyber Defence Centre of Excellence, http://ccdcoe.org/249.html (accessed 20 Jun. 2014).
[11] According to NATO, the Tallinn Manual is “an independent ‘International Group of Experts’ [and] is the result of a three-year effort to examine how extant international law norms apply to this ‘new’ form of warfare.”
[12] Michael Schmitt, et al., (2013) Tallinn Manual on the International Law Applicable to Cyber Warfare, (Cambridge, UK: Cambridge University Press), 45.
[13] Famous contemporary Chinese strategist.
[14] Li Bingyan, (2004) “Applying Military Strategy in the Age of the New Revolution in Military Affairs,” The Chinese Revolution in Military Affairs, (China: New China Press), 2-31.
[15] Vladimir Putin, (2013) “A Plea for Caution From Russia: What Putin Has to Say to Americans About Syria,” The New York Times, http://www.nytimes.com/2013/09/12/opinion/putin-plea-for-caution-from-russia-on-syria.html?pagewanted=all (accessed 6 Jul. 2014).
[16] Former National Security Agency (NSA) contractor responsible for the single largest classified intelligence disclosure in U.S. history.
[17] International Court of Justice (1986), “Military and Paramilitary Activities in and against Nicaragua (Nicaragua v. United States of America),” www.icj-cij.org, http://www.icj-cij.org/docket/index.php?sum=367&p1=3&p2=3&case=70&p3=5 (accessed 21 Jun. 2014).
[18] The Economist, (2007) “A cyber-riot: Estonia has faced down Russian rioters. But its websites are still under attack,” The Economist, http://www.economist.com/node/9163598 (accessed 22 Feb. 2014).
[19] Andreas Schmidt, (2013) “The Estonian Cyberattacks,” in A Fierce Domain: Conflict in Cyberspace, 1986 to 2012, (Vienna, VA: Cyber Conflict Studies Association), 192.
[20] Member of the Korea Institute for Defense Analyses.
[21] Sangkuk Lee, (2014) “China’s ‘Three Warfares’: Origins, Applications, and Organizations,” The Journal of Strategic Studies, Vol. 37, No. 2, 200
[22] Qiao Liang and Wang Xiangsui, (2011) Unrestricted Warfare, 2nd ed., (Wuhan, China: Chongwen), 41, 46-47.
[23] A nonprofit, nonpartisan organization that supports democratic change, monitors freedom, and advocates for democracy and human rights.
[24] Freedom House, (2014) “Freedom in the World 2014,” Freedom House, (Washington, DC: Freedom House), 18-23.
[25] Alexander Lukin, (2014) “What the Kremlin is Thinking: Putin’s Vision for Eurasia,” Foreign Affairs, Vol. 93, No. 4, 91.
[26] A military alliance comprised of Armenia, Belarus, Kazakhstan, Kyrgyzstan, Russia, and Tajikistan.
[27] Miles Yu, (2012) “Uzbekistan exits Russia-controlled pact, joining Georgia, Azerbaijan,” World Tribune, http://www.worldtribune.com/2012/07/10/uzbekistan-exits-russia-controlled-pact-joining-georgia-azerbaijan/ (accessed 24 Jun. 2014).
[28] U.S. Department of State, (2014) “U.S. Collective Defense Arrangements,” www.state.gov, http://www.state.gov/s/l/treaty/collectivedefense/ (accessed 245 Jun. 2014).
[29] Current U.S. Collective Defense Arrangements include the North Atlantic Treaty, the Agreement between the United States and Australia and New Zealand, the Philippine Treaty, the Southeast Asia Treaty, the Japanese Treaty, the Republic of Korea Treaty, and the Rio Treaty.
[30] Division of International Affairs, J53, (2014) “The National Guard State Partnership Program: Annual Report Fiscal Year 2013,” The National Guard Bureau, (Arlington, VA: The National Guard Bureau), 3.
[31] Ibid.
[32] A previous cost that has already been incurred and therefore cannot be recovered.
[33] Mark Landler & Michael Gordon, (2014) “U.S. to send Up to 300 Military Advisers to Iraq,” The New York Times, http://www.nytimes.com/2014/06/20/us/obama-to-address-nation-on-iraq-crisis.html?_r=0 (accessed 26 Jun. 2014).
[34] Karen DeYoung, (2014) “Syrian aircraft bomb Sunni militant targets inside Iraq,” The Sydney Morning Herald, http://www.smh.com.au/world/syrian-aircraft-bomb-sunni-militant-targets-inside-iraq-20140625-zsl1a.html (accessed 26 Jun. 2014).
[35] Dmitri Alperovitch, (2011) “Revealed: Operation Shady RAT,” McAfee, (Santa Clara, CA: McAfee), 5.
[36] The Guardian, (2014) “Chinese cyber-attack on Australia ‘wider than previously thought’,” The Guardian, http://www.theguardian.com/world/2014/apr/28/chinese-cyber-attack-australia-emails (accessed 29 Jun. 2014).
[37] Eduard Kovacs, (2014) “Cyberattack on New Zealand Supercomputer Traced to Chinese IP,” Security Week, http://www.securityweek.com/cyberattack-new-zealand-supercomputer-traced-chinese-ip (accessed 29 Jun. 2014).
[38] Tim Hume, (2014) “Alarm in Hong Kong at Chinese white paper affirming Beijing control,” CNN World, http://www.cnn.com/2014/06/11/world/asia/hong-kong-beijing-two-systems-paper/ (accessed 24 Jun. 2014).
[39] Ibid.
[40] World Population Review, (2014) “Russia Population 2014,” www.worldpopulationreview.com, http://worldpopulationreview.com/countries/russia-population/ (accessed 24 Jun. 2014).
[41] Robert Orttun, (2006) “Causes and Consequences of Corruption in Putin’s Russia,” Center for Strategic and International Studies, (Washington, DC: CSIS), 2.
[42] Robert Farley, (2014) “Can China’s Defense Industry Catch Up?” The Diplomat, http://thediplomat.com/2014/05/can-chinas-defense-industry-catch-up/ (accessed 25 Jun. 2014).
[43] Steven Hildreth, (2012) “Iran’s Ballistic Missile and Space Launch Programs,” Congressional Research Service, (Washington, DC: GPO) 38.
[44] Vasily Kashin, (2014) “The State of Defense Innovation in Russia: Prospects for Revival?” Center for Analysis on Science and Technology, (California: University of California Institute on Global Conflict and Cooperation), 1.
[45] Guy Anderson, (2009) “The Russian Defence Industrial Base,” www.rusi.org, https://www.rusi.org/downloads/assets/Russian_Defence_Industrial_Base_RDS_Summer_09.pdf (accessed 25 Jun. 2014).
[46] Command, control, communications, computers, intelligence, surveillance, and reconnaissance.
[47] Deloitte, (2014) “2014 Global Aerospace and Defense Industry outlook,” Deloitte Global Services Limited, (United Kingdom: Deloitte), 14.
[48] An artificially emplaced network designed to be compromised for the purposes of studying and preparing against adversarial CNO tactics and capabilities.
[49] Jason Rivera & Forrest Hare, (2014) “The Deployment of Attribution Agnostic Cyberdefense Constructs and Internally Based Cyberthreat Countermeasures,” in The 6th International Conference on Cyber Conflict Proceedings, (Tallinn, Estonia: NATO Cooperative Cyber Defence Centre of Excellence), 111.
[50] Ibid., p. 112.
[51] Ibid. 34, p. 3.
[52] BBC.com, (2014) “Iraqi PM Nouri Maliki: Russian jets will turn tide,” BBC News Middle East, http://www.bbc.com/news/world-middle-east-28042302 (accessed 28 Jun. 2014).
About the Author(s)
Comments
Can anyone at SWJ explain the role of OSCE who has been tasked to monitor the mercenary areas and the Russian border crossing points into eastern Ukraine, BUT cannot seem to state exactly what they are seeing.
First they were caught by video and photos actually giving Russian mercenaries rides in their monitoring vehicles which forced them to “apologize to the Ukraine” and were then accused twice of passing actual locations of Ukrainian troops who where shelled shortly after the OSCE visited them.
Now the following and yet they never “seem” to be able to see the same convoys that journalists and the locals are seeing nor are they observing actual modern Russian heavy equipment even setup in the Donbas main towns.
Let’s see---1600 more “not boots on the ground” SOF to Iraq and more air strikes, Clapper is off to North Korea and what does the US do about the Ukraine and Russia---utter silence---does it not strike one that the US leadership on the Ukraine is totally aimless?
Locals report #OSCE was next to a #Russian army column in #Ukraine on Nov 8 heading for #Donetsk, full #RUS flags
https://twitter.com/don_banderovka/status/531121094892462080 …
#Snizhne, 80 km from #Donetksk. #Russian invading army in #Ukraine. Nov 8 2014. Any comment @OSCE ?
pic.twitter.com/UZoP7D4bD4
#Makeevka. 25 km fr #Donetsk. Nov 8 2014. #Russian invading army in #Ukraine. Any comment by @OSCE?
pic.twitter.com/9gGwmNbaP0
Endless columns of annexing #Russian army in #Donetsk, #Ukraine on Nov 8. Each truck tows a MSTA-B 152mm howitzer.
pic.twitter.com/iQ30uYetAH
VIDEO: #Russian tanks drive through the streets of #Donetsk. #Ukraine
https://www.youtube.com/watch?v=m0MAvjg7qzk … pic.twitter.com/7HGeuqZlIW
Currently there have been three failures inside the Russian UW strategy;
1. the overall general Donbas population was 56% Ukrainian and 44% Russian with a large number of both ethnic groups not wanting to be annexed into Russia and nor did they trust the mercenaries and or the Ukrainian government
2. the over all Russian economy has suffered badly due to the sectorial sanctions, falling Rubel and oil prices which were unforeseen
3. and now Russia cannot supply food and other supplies urgently needed in the Crimea so this was announced yesterday by Russia:
#Russia lifted ban on imports from #Ukraine to #Crimea, recognizing that it cannot effectively feed the region using ferries
Reference the MH17 shot down--from today:
Brown Moses @Brown_Moses
We plan to publish the @Bellingcat #MH17 report (currently 30+ pages) tonight at midnight GMT.
If all goes to plan one will see a strong uptick in Russian hacking and trolling against the site as per the past when he released MH17 information.
Always a good indicator that the Russian government dislikes what is being released.
Why is it that right now it "appears" that it is only the US senior military leaders via DoD that is calling a Russian spade a spade--meaning calling out the continuing Russian aggression and movement of Russian troops.
Today NATO/US openly stated there are combat ready Russian BNs moving ever closer if not sitting already exactly on the border.
Notice a total lack of US civilian leadership comments anywhere in the media---total silence---what is so difficult for the civilian leaders of the US to state "Russia is in fact at war with the Ukraine"? AND that the massive convoys of troops and heavy equipment GO way past an "incursion".
No Russians then ;)
“@NatVasilyevaAP: I’d like to stress that the Kamazes that our crew has spotted had no number plates or any insignia.”
Another one “@HarrietSalem: Saturday morning convoy #Donetsk: 21 covered trucks, 17 howitzers, & 2 anti-aircraft missiles. #Ukraine”
@NatVasilyevaAP just spotted at least 40 armored Kamaz trucks, some carrying mortar systems on a highway in Makiivka on the way to Donetsk
For many the shot down of MH17 is now back page news but for the blogging community dealing with the Russian info war side of this they have never given up in ascertaining the "truth" from the "lies".
Latest Russian "myth" was that there were two Ukrainian fighters--but the open source side got ahold of the radar tapes and presto released a simple statement---must have been a "Ukrainian stealth fighter" since absolutely no fighter tracks were to be seen even on the Russian controllers side of the tapes.
Then the German CIA attempted to slide the shot down onto the Russian mercenary side and openly stated in the last weeks that it "might have been a captured Ukrainian BUK"---BUT then the open source side went out and proved beyond a doubt that the exact captured BUK was in fact fully damaged and unable to fight as was stated by the Ukrainians.
THEN the open side even stated exactly what the onboard fire control radars would have seen ie the Ukrainian side would have "seen the fighters as friendly and not fired" the Russian BUKs do not register Russian fighters as "friendly" thus would have fired on it.
Presto the German CIA pulled back their comments and statements.
The following twitter site has been doing some of the massively good OSINT work on the shot down with assistance from two other sites. They have now set a standard for true open source work that even the entire western media with their hundreds of reporters and tons of money have been unable to do and or have wanted to do.
Bellingcat was even able to pinpoint the exact Russian Air Defense unit responsible for the shot down---again largely ignored by western media.
https://twitter.com/bellingcat
WATCH in the coming week or so there will be an intensive redo and additional info will be forth coming from the three sites concerning the Russian involvement in the shot down of MH17 as they will debunking all the various Russian "myths".
ALL the time the US has been sitting on their classified intel which could have put this whole thing to bed once and for all---wonder why they did/have not?
Part of a coherent national level strategic UW strategy is in fact information warfare---and we lost that one badly--we are not even in the game---we are not even close to being somewhere in the game that is how badly we have been at it.
Over 300 plus photos have been recently taken at the MH17 crash site and are now being analyzed by the Dutch and the bellingcat group further reinforcing the BUK shot down theory.
Brown Moses @Brown_Moses
Interesting fragments from the MH17 flight deck crash site, from this photo set
https://www.flickr.com/photos/128537380@N08/ …
pic.twitter.com/VEFkuHuY66
Marcel van den Berg☁ @marcelvandenber
@Brown_Moses See this photo for some sort of shrapnel in headrest of pilot seat
http://bit.ly/1zC8ssB
MF---more on the Russian jamming of the OSCE UAVs being used by the OSCE to monitor the fighting.
The use of the OSCE drones to monitor the fighting and the Russian border were demands by the West AND Russia also demanded them and now they attempt to shot them down.
ALSO if one looks at the Russian UW strategy they also plan on using large numbers of them and still do over the Ukraine. Drones flying over the Ukrainian positions are precursors for MLRS rocket and artillery strikes.
ANOTHER Minsk 1 and 2 agreement failure which Russia still states they support and back but somehow still shot at the drones.
#BREAKINGNEWS @OSCE STOPS USE OF DRONES AFTER ONLY 2 WEEKS, CITING "RISK ASSESSMENT" (Russian army AA and jamming attacks).
The news of #OSCE UAV got radio comms damped is so huge that it has to be reported. This is 1st solid evidence of 1РЛ257 "Красуха-4" in work
Unfortunately on that day #OSCE reported only abt the incident when their UAV got under AA gun fire by border crossing #Russian army forces.
On Oct 29 #OSCE reported their UAV got under attack getting damped all comms when #Russian forces attacked #Ukraine positions @
Newsreel on #Russian news channel on brand new #Russian army radio reconn unit 1РЛ257 "Красуха-4". BRAND NEW!
https://www.youtube.com/watch?v=-WB7yftftqU …
#Russian army the latest radio reconnaissance- dumping unit 1РЛ257 "Красуха-4" technical spec.
http://militaryrussia.ru/blog/topic-742.html …
pic.twitter.com/EzqzXXswKx
KEY MISSION of this system is:
1РЛ257 "Красуха-4" radio recconnaissance / damping unit sole purpose is to kill any in & out comms singal from planes, UAV, rocket in air.
You mention the media carries virtually nothing---WELL here is another great example of western media at work with your tax dollars.
For over now two full months the blogging side composed of Europeans, Ukrainians, and a few Americans has been carrying a massive open source intelligence war on the information side against the Russian info war---with little to actually no support from the entire West.
If one tracked their reporting there has been an average of between 5-50 armored vehicles, artillery pieces, SAMs and armored Kamaz trucks along with troops and ammunition entering into the eastern Ukraine DAILY---
AND by the way---they constantly attempted to verify via photos, videos, and personal observations--most of the photos and videos were even geo tagged for extra verification. Amazing what dash cams give one these days.
AND then yesterday AFP as a major western media news agency carries the reported 32 tanks entering the Ukraine from Russia AND holy heck everything hits the fan on the western media side.
MY question---where have they been for the last two months?
Astonishingly quick response - 10 days of breaking developments & suddenly 32 tanks spotted!
http://www.dailymail.co.uk/news/article-2825222/Dozens-Russian-tanks-sp… …
PERFECT example for their great open source work was the rocket fire that killed two Ukrainian school kids killed this week just playing soccer at their school.
MASSIVESLY used by the Russian as agitate prop for the global press---then the open source guys show up, analyzed the available photos and videos and openly even challenge the OSCE findings and presto the Russian info war takes a hit because they were actually lying. Their work was even used by the Ukrainian Foreign Ministry to push back on the Russian info war efforts.
DID they get any support from western media in ascertaining the "truth" from Russian lying?
MF--it appears that the current Russian top leadership seems to be on an "historical" trip and it seems they want to rewrite European and Russia history along the way.
This from Putin today:
Putin suggests Britain and France were responsible for the Nazi march into Europe
Medvedev says 1917 revolution was a "tragedy" for Russia. http://goo.gl/8wkcFP
Sorry it is in Russian
"Putin has opted for confrontation w/ West as the basis for Russian development & the consolidation of his own power" http://www.nytimes.com/2014/11/07/opinion/roger-cohen-russia-pivoting-t… …
MF--a couple of interesting comments of yours 1) there have been a number of reports from various sources concerning alleged cancer, but today he states life is about love who many seem to think it means his new girlfriend since his divorce so he seems to not have cancer.
Secondly, there have been sightings and confirmation of three Russian Army jamming units that have moved into the eastern Ukraine.
By the way you are correct the Russians are indeed testing their ability to block in the future US drones and that is a certain problem DoD needs to look seriously at--heck even jihadi's have blocked say Shadow signals.
Thirdly, it seems that US senior military leaders both here and in the US are starting to say---they might have to redeploy forces that were taken out of Germany back to Europe---and at what cost--- since they argued that bringing them home was saving money.
What do you think about this rumor that Putin has cancer and only 3 years to live? The Australian article claims that Putin wants to leave a legacy like Peter the Great or Stalin.
http://au.ibtimes.com/articles/570841/20141027/russia-putin-ukraine-eu-…
After being unable to get to the Financial Times article where Putin supposedly defended the Nazi/USSR WWII initial partnership, I found other articles where Putin supposedly asked a Poland minister about dividing Ukraine between them since Ukraine "was not really a country."
It sounds more and more like Putin is the loose cannon behind current Russian problems that only will get worse if he continues his aggression. You are correct in noting that we nearly never hear anything about Ukraine in the mainstream news these days. I'm not sure that ISIS is any less of a problem but the totality of world unrest with serious potential implications is why a drawdown of active Army force structure and a withdrawal of forward deployed credible ground forces makes little sense.
Also, I meant to respond to your earlier comment noting Russian jamming of UAS over Ukraine:
<blockquote>Russia has never implemented--- in fact yesterday again jammed OSCE UAVs again using military grade jammers ---never implemented a single paragraph of the agreements.</blockquote>
Near peer abilities to jam Remotely Piloted Aircraft (RPA) cast further doubt on the recent CSBA study that calls for reducing the F-35 buy and instead starting development of an all new MQ-X and Naval unmanned combat aircraft systems (N-UCAS). How do you fly over near peer territory when we know anti-satellite capabilities mean satellite data links and GPS signals may be unavailable. AWACS systems can vector manned aircraft to air targets without GPS. How do we expand to multiple squadrons of air and sea-based combat UAS sharing limited satellite data link access with many other data links stepping on one another in close proximity?
Then USNI had an article revealing pictures of the J-31 implying that UAS "missile trucks" could take them on. The problem of course is if the Chinese have signatures and appearances similar to our aircraft, it casts doubt on ability to launch salvos from beyond visual range. It further requires visual identification and air combat maneuvering within visual range which an unmanned system seems questionable at accomplishing particularly if it needs to maintain a data link during high g maneuvers. Make it completely autonomous and there are ethical questions and loss of a man-in-the-loop to make final decisions on engagement.
When studies say we should reduce the F-35 buy thinking that monies can be funneled instead to UAS/RPAs, there is an errant perception involved. The money perceived as freed up would be on the tail end of F-35 production. Meanwhile, development of new start exquisite stealthy and software intensive MQ-X and N-UCAS would require extensive funding now and concurrent with F-35 production. When we see the F-35C landing and taking off from carriers, elimination of that capability seems a mistaken notion when contrasted with notional unproven capabilities that would require decades to develop.
In addition, rather than focus on fielding squadrons of N-UCAS and MQ-X due to the perceived dangers to aerial refueling aircraft getting too close to enemy fighter long-range missiles, why not develop fewer stealth unmanned aircraft refuelers instead based on the LRS-B? In addition, we could modify later block-buy F-35s to include an optionally-manned capability. I've always been a big proponent of UAS/RPA, but this push to replace manned aircraft/ground capabilities prematurely with unmanned ones is reminiscent of Comanche and FCS fiascos. A manned-unmanned team capability makes sense and localizes stronger, directional data links that can overcome jamming. Over reliance on autonomy and preprogramming or satellite data links is asking for trouble from a cyber, jamming, and combat ID perspective.
In the face of possible new sanctions for supporting the recent mercenary elections DID Russia just blink?
One has to enjoy their word hair splitting games in order to appear to not be "losing".
Have they explained the difference to their own mercenaries as it appears to them Russia is fully recognizing them based on their statements right after the elections that they are now longer part of the Ukraine.
Updated 3:22 p.m. Moscow Time
MOSCOW, November 7 (RIA Novosti) – Russia's position toward the recent elections in the self-proclaimed Donetsk and Luhansk people's republics (DRP, LPR) in eastern Ukraine expressed by the country's Foreign Ministry as "respecting" them does not mean Moscow "recognizes" them, Russian presidential aide Yury Ushakov said Friday.
"Russia's official position on the results of the elections is expressed compactly, but liberally. The word "respect" was used," Ushakov said.
When asked if the terms "respect" and "recognize" could be used equally with regard to the recent elections in eastern Ukraine, Ushakov said that "these are different words."
"The word "respect" was chosen on purpose," Ushakov stressed.
The new Russian strategic/tactical UW strategy never foresaw the question of "guns and or butter".
Putin is now at that a decision crossroads as the Russian economy is tanking fast--Russian Central Bank is currently holding an emergency meeting---will it be for "guns" or for "butter".
#Russia's ruble drops off a cliff, as #Ukraine's war deepens:
$1 = 47.023
€1 = 58.305
£1 = 74.409
"Full-blown panic, key pressure on the ruble now primarily from households, which is a self-fulfilling process." http://www.themoscowtimes.com/business/article/russian-ruble-opens-more… …
But on the other hand this indicates Putin is still "all in for a victory".
AFP: #BREAKING Column of 32 tanks enters Ukraine from Russia: Kiev
32 Russian tanks, 16 howitzers and 30 KAMAZ trucks with ammunition and men (Russian soldiers) entered #Izvaryne and went to #Krasnyi_Luch
BUT from Russia this morning the following via RIA:
Updated 11:43 a.m. Moscow time
MOSCOW, November 7 (RIA Novosti) - Allegations voiced by Canadian Foreign Minister John Baird and a number of representatives from the United States and NATO about Russian troops supposedly moving toward the country's border with Ukraine have no grounds and are based on rumors, a Russian Defense Ministry spokesman said Friday.
"These announcements were made citing some 'reports' without any solid proof," the spokesman said.
In order for the Russian UW strategy to work and as Putin views Russia as a "superpower" he forgot along the way that in order to be a "superpower" a country must as well be an "economic power".
He now stands in front of a serious question that I am not so sure he even knows the answer--1) continue on the UW path in order to "achieve" a victory and or 2) take what he has and declares it a victory and then fights to get his economy going again.
Seriously think he has chosen "achieving" a victory over the Ukraine as far more important than his own population.
439th Guards Rocket Artillery Brigade deployed as part of #Russian invasion forces #Ukraine
https://burkonews.info/confirmation-439th-guards-rocket-artillery-briga… …
Right now IMO Putin is swimming all over the place and even he is no longer really sure what he is doing and that is dangerous for someone who has threatened the use of tactical nuclear weapons.
Yday #Putin dismissed combating nuke terrorism-Today he defends Nazi-Sov Pact
http://on.ft.com/1Gu5h8b
Today's Nezavis.Gazeta on the sliding rouble: "The authorities are finding it increasingly difficult to convince Russians to stay calm"
If the Russian population starts to question him on his economic polices as the Rubel hit total new lows today THEN he has his own "Maidan" exactly what he has been attempting to side step.
Ruble opens weaker against the dollar. A lot weaker actually. 47.6050 is the new low
pic.twitter.com/tfO6alTu46
Russia's economy: No access to credit, no investments, no manufacturing, brain drain, sinking oil price, lower oil production expected.
Interesting side point----Gorbachev supporting Putin's actions---maybe never as "liberal" as many assumed he was?
It seems Gorbachev is going to defend Putin’s actions while he is here in Berlin for the 25th year of the Wall coming down celebrations---BUT at the same time he forgets his role is suppressing Russian satellite states during the same period of time---strange that he is shifting to support Putin—maybe all along he was never as supportive of the Wall coming down as many seem to think.
http://news.yahoo.com/gorbachev-berlin-wall-festivities-defend-putin-16…
Flashback of legacy Gorbachev left in former republics. Baku Black Monday January 19-20th 1989 http://www.studiolum.com/wang/azerbaijan/santiago/blackjan-map.jpg …
http://youtu.be/lDr7lEKhxPg
Flashback of legacy Gorbachev left in former republics. Vilnius TV tower massacre Jan 13 1991 http://youtu.be/44JOrv6t_Nw
http://fototapeta.art.pl/IMG/lt3/litwa-
Flashback of legacy Gorbachev left in former republics. Tbilisi massacre April 9th 1989. http://youtu.be/EInKmH7RNcQ
Flashback of legacy Gorbachev left in former republics. January 1991, Riga, Soviet spetsnaz OMON busy several weeks
http://youtu.be/1y4wLPgTxwk
Seems the ACoS is now moving to the JCoS views concerning Russia---notice the use of the word aggression--maybe the national level is finally ditching the word so badly used "incursion".
And the Army training still is pushing COIN and Attack the Network methodology as if the next "aggressor" is going to be using IEDs instead of four different calibers of multiple rocket launching systems and high precision artillery shells with an extremely heavy dose of SF/GRU intel sabotage teams, and an irregular army of 12,000.
Gen. Odierno; 'We Continue to See Russian Aggression' http://nbcnews.to/1Glg1FR
This today from two major ranking US Generals- is the White House even "listening" as it asks for "new war powers" for Iraq and Syria? OR does it not really care what goes on in central Europe?;
US Mission to NATO
#Russia is "pushing on the limits of international order"--@thejointstaff General Dempsey
http://goo.gl/CJ7BiE
pic.twitter.com/eaJX2Lw4C2
MAYBE this is why the JCoS made his statement:
Here are 8000 balloons tracing the path of the Berlin Wall on the 25th anniversary of its fall. Wow.
pic.twitter.com/sdKPkXmQ38 #de25
25 years later and war in central Europe is a serious possibility.
SACEUR asked today for more troops based on the massive Russia buildup and tactical nuclear weapons on the Ukrainian border.
US & Germany have refused Ukraine's "requests for military assistance... that might deter a new Russian offensive"
http://www.atlanticcouncil.org/blogs/natosource/mr-putin-resumes-his-ch… …
So does the US leadership truly want the Ukraine to fail or is
"aimlessness" the newest strategy out of the White House?
First Putin complains yesterday of the constant shelling by the Ukraine of civilians and uses the term "civil war", then the killing of two school children today in order to "prove" Ukrainians are killing civilians--immediate open source analysis refutes the accusation that the round came from the Ukrainians--not mentioned though by the Russians and NOW this this evening. Open source analysis work was then quoted by the Ukrainian Foreign Ministry that is how accurate it was.
BREAKING: Rus sec.council. discusses "deterioration of the situation in the Donbass due to repeated violations of the ceasefire by Ukraine.
Notice full blame is being placed on the Ukrainians and not a single mention of the constant shelling all day long of Ukrainian positions by Russian troops and her mercenaries in over 30 locations.
Appears Putin is getting his "approvals" for sending in his "peacekeeping forces" just as he has done in Moldavia and Georgia.
WHAT then will be the White House response?
After the rather aimless US leadership on the Ukrainian events we are now heading towards a full blown war between the Ukrainians and the Russian "vacationing" troops with their irregulars and yet still no comment by the EU/NATO and especially the US.
Heads up this is going to get very ugly in the coming days as the Ukrainians had wisely used their volunteer BNs and their draftee National guard to hold key locations and take the Russian and mercenary artillery and ground attacks and held their own regular Army in reserve which has moved/raced up to the entire front line of contact to relieve those units and have gone over to massive artillery and rocket return fire when the mercenaries and or Russian troops fire on them and have started retaking small towns lost weeks ago.
Ukraine Now Fighting Not for Donbas but for Its Survival as a State and Nation, Babchenko Says
We discuss here often the idea that populations should have the right to select on their own without outside influence their own form of good governance and the rule of law and yet when a population does stand up and makes that decision and decides to fight for it---where is US support and or leadership?
We seem to be more interested in protecting Putin's "NATO humiliation myths" than reigning him in.
Well worth checking the daily sit maps from the Ukrainian NSDC from the last week and then compare it to todays front line activities.
Latest @NSDC_ua combat zone map of E #Ukraine shows a massive resumption of fighting along the DNR/LNR contact line.
pic.twitter.com/ivpthXNW1r
While the US Army cannot seem to turn loose of the COIN concept of Attack the Network (AtN) which never was successful even though the defense contractors that sold the program claim otherwise---but as always concrete results have never been shown.
It appears and seems that the Russian military paid close attention to all of our doctrinal discussions after Desert Storm and incorporated "Effects Based Network operations" into their new strategic/tactical UW doctrine called "New Generation Warfare"---while we on the other simply fluffed it off as a crazy idea sort of thing and just buzz words.
"Effects based network operations"---never though I would see that term again but we seem to be seeing it daily in eastern Ukraine.
A Ukrainian article well worth the read and much of it can be seen daily in eastern Ukraine and in fact negates the current US Army DATE training exercises scenarios and the concept of Attack the Network or "AtN".
And it drives a wooden stake into the heart of COIN as COIN cannot do anything against the new Russian UW strategy.
Currently no DATE scenario being exercised currently and literally anywhere by the Army comes even close to what is being seen in reality in eastern Ukraine and that area of the world was to be the five core scenario exercise concepts.
http://euromaidanpress.com/2014/11/05/russian-hybrid-warfare-what-are-e…
Besides USSR experience and practical concepts Russia has watched closely the development of military doctrines in the West in the late 1990s to early 2000s, especially after 9/11. Some concepts are in further development or reconsideration now: Effect-Based Operations, Network-Centric Warfare, Chaos Theory in the Social Sciences, Preparing for Conflict in the Information Age, Network-Enabled Operations, Effects-Based Information Operations.
Western approaches on effects-based operations and network-centric warfare were in active development in mid-1990s . One of them is “Five Rings for Strategic Warfare concept” of John A.Warden,. III, published in his work “The Enemy as a System” in 1995.
Some elements the new DATE scenarios do not handle and nor does the AtN:
#Ukraine SBU arrested #Russia trained sabotage squad "Kuznetsov" near #Lviv
http://www.youtube.com/watch?v=30gp7MdXvB0 …
pic.twitter.com/SBM4rhOzk4
#Report Russian invasion forces move the rare MSTA-K through Molodogvardiis'k towards the frontline.
(file pic) pic.twitter.com/v6JeURavlO
#Russia-backed rebel have restarted the military offence along the most parts of the demarcation line in East #Ukraine
Russian troops and military equipment continue to arrive in East Ukraine, @NSDC_ua says
Confirmation of the 439th Guards Rocket Artillery Brigade deployed as part of the #Russian invasion forces...
http://fb.me/35gfpKJdR
It is impossible to keep track.
Russian attacked some 30 towns since the morning
Also Donetsk airport,Hirske and Krymske to call only a few
So again to those defenders of the AtN concept and to those that think DATE is the way forward in the coming years for the US Army--think seriously again--AtN cannot answer any of the above events that are in fact reality on the ground.
Another problem with the article that we have not looked at is "what is the role of the aggressor in the UW"---right now part of the failure in dealing with Russia and especially Putin is the simple fact Putin resides in an "altered state of reality"--meaning his press comments, his actions, his international speeches, his own internal comments to the Russian population all go counter to the "reality of Russia actions" on the ground in Crimea and eastern Ukraine.
How does one then plan a strategy where the aggressor "refuses" to be seen as the aggressor and "denies" they are even involved in the internal affairs of a neighbor?
This RIA press releases is in fact a great example of the "altered state of reality" exhibited by the leader of an aggressor state.
Secondly, if one looks closely at the statement it is the precursor for flipping Russian overt support with soldiers, advisors/Russian SF, and heavy weapons into the role of a "peacekeeping force" in order to "protect the civilian population".
It is interesting that in fact the Ukraine and the OSCE were the only parties to the Minsk 1 and 2 agreements forced by Russia and signed by Russia and her mercenaries that attempted to strictly adhere to the agreements.
Russia has never implemented--- in fact yesterday again jammed OSCE UAVs again using military grade jammers ---never implemented a single paragraph of the agreements.
Today the Russian Central Bank virtually gave up in supporting the falling Ruble and it is now in a "free floating fall" and the economy will go truly south now---will Putin in his drive to "victory" over the Ukraine speed up his drive and throttle back?
What if he flips and goes to a straight "peacekeeping operation" effectively annexing all of the Donbas he calls "New Russia" and cuts the Ukraine off from it's tow ports of Odessa and Mariupol?
Another example today from Interfax that he is leaning to total annexation of the "New Russia".
16:50 History cannot be re-written for someone's geopolitical interests - Putin
So in his mind annexation is nothing more than the stopping of the rewriting of "history"--an interesting statement from someone who has threatened nuclear war three times in the last six months.
Will this newly elected Republican Congress be willing to call a spade a spade and go to full military aid support and advisor support for the Ukraine---for all their past words and complaints I seriously doubt it.
From RIA today:
MOSCOW, November 15 (RIA Novosti) – The civil war rages in eastern Ukraine despite reconciliation agreements reached this fall with the participation of Russia and the Organization for Security and Cooperation in Europe, the Russian president said Wednesday.
"A civil conflict, which in fact is a civil war, rages in Ukraine, near Russian borders. Despite Minsk agreements, peaceful cities are being shelled and civilians get killed,” Vladimir Putin said.
For those that track the Russian news agencies RIA and Interfax---it seems the Russian government has lost both it's voice and it's writing abilities.
Both news agencies are normally as active as 500 mice on tread mills can be every minute of the day---- seems to have "lost something"?
Interfax has virtually been silent and the number of released press releases all fit on a single page not the normal 8 or 9 pages.
RIA has virtually ceased releasing articles---all are bland and non critical.
Totally strange--anyone have any ideas?
I know the Russian leadership is struggling with their verbal support of the mercenary elections flashing back into their faces with calls for more sanctions and they are struggling with Merkels statement that the Russian leaders cannot any time soon expect sanctions to come off the table.
Then the Ukrainians appear to be taking the peace gloves off and are talking now for open war after calling the Russian hand on their support of the elections which were a clear violation of Minsk 1 and 2.
Coupled with the nuclear reactor breakdown in Rostov and a major fire that some are calling sabotage on a Russian sub chasing cruiser in Crimea.
Then the KSA announcement today on their oil price reductions caused WTI to hit 78 USD and the Ruble went to 43
BUT seriously-- this quiet I have never seen them in the last eight months.
Did the world miss something going on inside Russia or with Putin today?
In addition to my other longer comments below about another new CSBA study, a more promising one also just released is "Beyond Coastal Artillery: Cross-Domain Denial and the Army." A key quote from that study is as follows:
<blockquote>Meanwhile, by presenting adversaries with new, land-based threats to their air and naval forces and targets deep within their territory and long their coastline, Army forces would add complexity and uncertainty to adversaries’ calculations. By confronting them with a larger set of targets that could be dispersed, hardened, and concealed on land, they would impose upon adversaries the higher cost of finding and striking these challenging targets while reducing the susceptibility of U.S. forces to a first strike and thereby enhancing crisis stability. <strong>Since attacks on forward deployed cross-domain denial forces would have to occur on the sovereign territory of another state-as opposed to at sea or mid-air-they would entail greater diplomatic repercussions and risk of horizontal escalation, creating additional dilemmas for would be aggressors.</strong> In doing all of the above, the Army could make essential contributions to joint efforts to deter and win conflicts in several theaters, including the crucial Asia-Pacific region.</blockquote>
The bold part of the quote that I added illustrates both a key strength in forward deployment of Army forces and a weakness in A2/AD "offset" strategies that seek to limit forward U.S. exposure. The nations we have treaties with have no choice but to defend themselves with ground, air, and sea forces that may be susceptible to varying degrees to Chinese, Russian, or Iranian missiles. These defenses automatically impose numerous targets for a limited number of adversary long-range missiles. Add prepositioned U.S. Army equipment and rotating/visiting smaller Army forces and we demonstrate resolve to honor treaties and share common risks in partner defenses.
It is illogical to suppose that during the Cold War, U.S. forces in Germany were not vulnerable to missiles and air attacks. Why is Asia or East Europe today unique?
The more friendly countries willing to host small Army prepositioned equipment and rotating forces, the more targets for threat long-range missiles and the more coalition partners created in the event of a surprise missile attack. The fact that both Army armor, air defenses, and MLRS capabilities would be on hand to help thwart surprise attacks and expand points of entry into theater would further deter any option to attempt to overwhelm allied and U.S. defense with surprise attacks.
Bill---your bring up a topic that is little discussed here.
Many of the Arab Springs and the Oranges' were population driven and their expression against the existing poor quality of the rule of law and or poor governance and or poor economic development chances---but say for the Tunisia none of the population driven changes made it due to the existing elites pushing back---ie military and or Islamists. All they wanted was a simple chance at having jobs, raising their children in a relative better position than what they had etc.
But if you look at the only truly successful population driven regime change it came from the Germans as we are having here in Berlin the 25th year after the Wall---if you look at how the local population drove their own changes in the face of the Stasi and the Army and the Communist Party one is astounded at how peaceful it went.
The population will always win in the end if they reach a point that they no longer have fear of the existing regime-even if it costs their the life's-the question as you rightly indicate is we the West basically abandoned them after they made their reach for their new values.
Why the German events did not fail--there was a deep drive to reunify something that is not apparent in any of the newer population driven events AND they financed it out of their own tax streams and was not dependent on any other country.
A big difference.
Outlaw:
Regarding, generally, the western-sponsored and western-friendly revolutions that we have seen in recent years and, specifically, the western-oriented Ukrainian revolution that you describe via the "Maidan," you make an excellent point, I believe, in comparing:
a. "Their" (example: Russian) bold and exceptional support for "their" (example: Russian-friendly) populations and fighters.
b. And "our" (U.S./E.U.) comparatively wimpy and insignificant support for "our" western-friendly populations and fighters.
I believe that the reason for this phenomenon is that, when we began this process in the 1990s and 2000s -- of aggressively suggesting/sponsoring/supporting western-friendly revolutions and regime changes -- we did not understand, anticipate or appreciate that there would be both significant resistance and, therefore, significant cost, associated with these such activities. Our heads, back in those days, were in the "End of History" clouds.
Today we are under no such illusion and, due to the financial crisis, have no money, anyway, to either (1) adjust or (2) up our game -- even if we wanted to.
Thus, "our" revolutionaries are left mostly to shift for/fend for themselves, and against the massive forces that we have set against them (exs: great nation forces from Russia; great civilization forces from the Middle East).
Thus your point, I believe, that we should not blame the populations -- and/or the lack of appeal of our values and way of life -- as reasons:
a. Why we/they might fail,
b. Why we have been forced to move back to the regimes and
c. Why we must embrace/re-embrace counter-unconventional warfare.
These such matters having more to do with (1) our 1990s-early 2000s hubris and corresponding expansionist activities (which set in motion revolutions that we cannot adequately support) and (2) the recent financial crisis (which forced us to pull back, leave folks hanging and which gives us little or no room to adjust or up our game)?
Bill---as a counter balance to your comments---the Maidann sprang up out of the unfinished Orange revolution in which actually many Ukrainians of many political colors had placed great hope it---but by Maidan it was now an uprising of the population again across the political spectrum against the corrupted rule of law, really poor governance and massive Soviet style oligarch corruption.
By 2014, it was a general and widely held view by the general population in western Ukraine that their then President was ripping off the country and the economy was stagnating and the general appeal of the EU had been growing as even larger numbers of Ukrainians had been travelling there over the last seven years. By the way--he and his gang made off with an estimated 70B USD.
They physically saw the differences between the EU legal/economic/political/social system vs the old line Soviet style state directed economy and government all based on oligarchs and corruption--the Ukrainian population was not blind.
Then when the Maidan occurred no one even the EU anticipated it would hold on during a very old winter but it did and grew even larger.
So now when a population on it's own decides that it has had enough of poor governance and a lack of the rule of law steps up and makes a decision--Russia makes their move---why because the Maidan threatens Putin and his ruling elites and oligarchs.
Shortly after the Crimea--Putin called a meeting of his national security council and all they discussed was how Russia could avoid a "Maidan"--that was and is still the core threat to Putin. Recently Russian passed an extensive set of internal security laws all aimed and prohibiting "a Maidan".
Now this is the problem---a large majority of Ukrainians do look towards the EU even those in the Donbas did as well---so fighting starts--the Ukrainian Army is a rag tag group but somehow manages to push the mercenaries to an almost defeat on their on by the way and then the Russian Army takes a "vacation" in the Donbas and what does the West do to support the Ukrainian Army blankets, MREs, and sanctions.
In Syria and Iraq what was the Western response and how many troop trainers did they send---did the Ukrainians ask for boots on the ground--no they asked for weapons and moral support and stated they would carry the fight as it was their country.
AND what was the western response---BY the way a little unknown fact ---the EU and the US placed great pressure on the Ukrainians to hold to the ceasefire/Minsk 1 and 2 which they have at great cost in manpower and equipment. Over 300 killed just in the last two weeks.
At one checkpoint which was given up the National Guard unit--it had been fully surrounded over the last three weeks, and was constantly shelled from Russian troops and mercenaries which the NG unit knew where the firing locations were---BUT they never fired a single shot in retaliation ---actually they were forbidden to ask for artillery support.
That has been repeated multiple times in since 5 Sept---how long can an army take being shelled and attacked and not return the violence without suffering humiliation?
Context:
a. The recent failure of "western values" and "western examples," to adequately inspire native populations to successfully effect the political, economic and social changes that we desire; this would seem to have caused the West to now shift gears and determine to work more "by, with and through" the regimes (rather than via the populations) to advance our power, influence and control in various regions of the world.
b. Noting these recent failures, and the corresponding change in Western strategy noted above, this seems to have caused such nations as Russia, China and Iran to "double down" on (1) the ceded local populations and (2) the use of local identities and local values to inspire same; these to be employed as a/the principle means/method to contain and roll-back western power, influence and control in the world.
Question:
Is it against the backdrop that I have described above that "Understanding and Countering Nation-State Use of Protracted Unconventional Warfare" becomes the "order of the day?"
(As "we" now work more "by, with and through" the regimes, to achieve our desired ends, "they" will work now more with the ceded populations, to undermine, compromise and overthrow such regimes and to, thereby, contain and/or roll-back western power, influence and control in their regions. Thus, the [1] new need for [2] counter-unconventional warfare capabilities and expertise.)
What is more concerning than current slow-motion UW in the Pacific and Putin's bolder and more conventional Ukrainian conflict is the potential errant influence of CSBA's newest studies on Democratic administration defense thinking. The just released “Toward a New Offset Strategy” proposes a whole array of new Air-Sea Battle systems that would require decades to develop, procure, and field in adequate numbers while requiring the following bold topic cuts:
<strong>Reduction in manned tactical aviation force structure across the Air Force, Navy, and Marine Corps to include scaled back procurement of all F-35 variants-including possible cancellation of the F-35C (replaced with Advanced Super Hornets and eventually N-UCAS).</strong>
The new CSBA study ignores asymmetric advantages of our already-plentiful tanker force that could stand-off supporting currently produced Joint F-35s. Their proposed alternative of unmanned stealth penetration capabilities would delay threatened theater airstrike capabilities by well over a decade while offering little air-to-air protection for our sea, air and land forces. At least 10-20 years would be required to develop and procure substantial numbers of costly stealth MQ-X and N-UCAS and expensive LRS-B. Unlike a F-22 and F-35, there is little evidence that proposed stealthy unmanned systems could protect themselves over enemy territory or defend against enemy air attacks. Those are decades of risk we may not have if we eliminate the F-35C and reduce the F-35A buy.
Also, Outlaw mentions Putin’s repeated threats to use tactical nuclear weapons. The escalatory risk of flying any LRS-B that could be carrying nuclear weapons undetected deep into adversary territory is particularly troubling. Putin or an asymmetric Chinese threat strategic thinker might consider infiltrating SOF-employed G-RAMM mortar and small missile capabilities to engage LRS-B on U.S. ground. After all, all our B-2s are in one spot and logistics/maintenance would drive similar thinking for LRS-B which is unlikely to be as numerous as presently conceived given past trends in stealth bomber and fighter cost overruns.
The more realistic near term risk is a China facing a depletion of young workers/troops that must support an aging population. Add a depleting labor cost advantage as China reaches closer pay parity with U.S. and other Western/Asian workers that will reduce manufacturing jobs. In Russia the near term risk is the youngish Vladimir Putin who shows no sign of disappearing from Russian power. Add Russia’s reduced relevance in the energy sector, a weak Ruble, and imposed sanctions due to Putin’s aggressive actions. Disgruntled youth in both near peer countries are likely to rebel against aggressive foreign policies that affect economic growth and kill/maim their military loved ones with far less regard for life and CIVCAS than their Western counterparts.
Near term adversary leaders may respond with further aggression masked as Nationalism to distract youth and retirees from economic and social problems. Both near peers likely will perceive opportunities for further aggression if U.S. leaders of both parties display aversion to deterring “foreign” wars that they perceive as being “not our problem.” Until we begin fielding F-35s in substantial numbers, our ability to penetrate adversary air defenses will be limited in scale as evidenced by our fewer long-range flights from the Persian Gulf to attack north Syria targets instead of direct attacks from land and sea basing in the closer Mediterranean and Italy. A curtailment of ongoing F-35 production would expand the window of vulnerability for Russian and Chinese aggression until less capable unmanned MQ-X and N-UCAS could be developed and fielded.
The study seems oblivious to the air-to-air threats to an MQ-X or N-UCAS flying persistently over near peer territory yet would substitute such unmanned systems for the F/A-18, F-35C, and F/A-XX. The study addresses deeply buried and tunneled threats calling them hardened and deeply buried targets yet does not address how an unmanned aircraft would find such underground systems looking through smog and intermingled within urban areas creating radar clutter while not getting shot down visually by enemy fighter guns. Also, enemy armor intermingled with civilians would be a difficult target for any airborne system. Yet such intermingling is the likely asymmetric response to an all-air strategy. A strategy based excessively on autonomous or preprogrammed unmanned aircraft and long range Vertical Launch Cell missiles lacks instant human judgment in response to unexpected events.
<strong>Elimination of at least one aircraft carrier</strong>
This isn't a bad idea given our asymmetric advantage in carrier numbers if money must be saved. It also seems you could park a decommissioned carrier grounded in shallow Persian Gulf waters of an ally to support both U.S. helicopter and F-35B capabilities against a less capable Iran to augment single mobile carrier operations. Such positioning surrounded by a concrete base would safeguard the grounded carrier from terror threats and provide a smaller contractor-operated footprint compared to shore-based facilities that are just as vulnerable to missile attack.
<strong>Scaled-back procurement of large surface combatants (DDG-51)</strong>
Presumably this reflects that despite the numerous Vertical Launch System (VLS) cells on each destroyer that CSBA thinks them vulnerable compared to subs and their proposed undersea towed missile payload modules that sit on the bottom until needed. The study mentions the four lost SSGNs and Los Angeles class subs that will lead to a 60% drop in VLS cells but elimination of DDG-51s and their 94 cells hardly seems the solution.
If near peer A2/AD posits that a surprise attack would kick off any aggression (although long-term UW seems the newer trend) it is hard to fathom in either a surprise or UW scenario that time would exist to tow underwater missiles into position to counter already inbound missiles. True they could retaliate against fixed targets, but an air and missile defense option seems less likely. Likewise, permanent underwater placement 4-6 kms deep “for years until remotely signaled to activate and ‘fall upward’ to the surface” seems implausible. Likewise, given the unlikely nature of open conflicts with Russia or China due to nuclear MAD, the recurring difficulty in maintaining or replacing deep underwater systems every few years over multiple decades of non-conflict seems problematic.
Also, such a trade-off removes destroyer heliborne capabilities to find subs, move SEALs and SOF, and take-on swarming boats. DDG-51 is a potential Future Vertical Lift hopping platform as well to get Army and Marine aircraft from distant islands to threatened shores.
<strong>Reduction in Army BCT force structure and planned modernization</strong>
Oddly the study talks about cutting Army force structure yet armor is most capable of withstanding attacks by half-ton to ton sized conventional missile munitions be they submunitions or unitary explosives. The ability to disperse and conceal such armor and dug-in dismounts renders A2/AD missiles less or non-capable. In addition, another study CSBA is pushing advocates new shore-based capabilities against ships and Army shore-based air defenses. Obviously such systems would need Army forces to protect them from infiltrated SOF and indirect fire G-RAMM attack.
In addition, if the Joint force desires to overcome missile treaty constraints prohibiting U.S. long-range strike then MLRS/HIMARS/ATACMS systems modified with new penetrating unmanned aircraft rounds and capabilities to attack launched inbound threat missiles are a less costly alternative to new start MQ-X and N-UCAS. Both Army armor and MLRS-based systems and air defenses could protect F-35s/F-22s and ground fuel and ammunition storage dispersed underground and in protected fuel/ammo trucks per the Rapid Raptor concept.
<strong>Procurement of a mix of Afloat Forward State Bases and JHSVs in lieu of more expensive amphibious warfare ships (e.g. LX-R and LHAs)</strong>
This seems a reasonable proposition augmented by LCS and Small Surface Combatant capabilities to facilitate Army attack and assault Future Vertical Lift (FVL) and current helicopter ship-hopping to reach distant shores. Army aircraft need not be permanently based on any ship. Rather having the capability to island and ship hop would allow early reinforcement of prepositioned Army and Marine armor at multiple country points of entry. In places like Germany, reinforcement of Baltic and other NATO states would be simplified with faster and longer range FVL capabilities that do not require fixed basing or runways once forward-deployed.
<strong>Cancellation of the Amphibious Combat Vehicle</strong>
This makes sense if you concede that any ship probably will require location at least 100nm from adversary shores. Capabilities to air deploy to shore via Army and Marine aircraft air assault will be able to seize airheads, shallow ports, and shorelines for C-130/C-17 airland/airdrop and air-cushioned LCAC and JHSV capabilities. A Joint Access Vehicle that splits the weight of armored vehicles into two major components is another possibility with rear dismountable modules being tailored to either an amphibious capability for sea-thrust or a pusher prop to support powered parasails to safeguard airdrop aircraft from air defenses through standoff. Once ashore the two major components are joined to create a mobile infantry capability under armor to support both light and armored infantry.
<strong>Conclusion</strong>
The entire A2/AD concept ignores the need for adversaries to actually exploit missile and G-RAMM attacks with seizure of terrain. If China seeks a foothold on Taiwan, parts of disputed Japan or the South Seas, or a disintegrating North Korea, stealthy unmanned aircraft and LRS-B won’t suffice. Dispersed Russian Armor hugging NATO country civilians would also be a difficult target to strike. Army and Marine armor and dismounts will be required to weed adversaries out from allied cities and towns. Manned aircraft cannot attack easily from well above let alone autonomous and preprogrammed unmanned aircraft.
Manned aircraft teaming with non-stealthy unmanned aircraft can overcome that challenge once air defenses are suppressed by stealth fighters, VLS cells, and fewer LRS-B. In many cases, prepositioned company-sized armor in both the Pacific and East Europe could be essential to prevent near peer adversaries from consolidating gains of initial air and missile attacks by protecting points of entry and defending them against SOF attacks.
CSBA's proposed high-low mix of current and stealth remotely piloted aircraft would make sense if only limited numbers of stealthy unmanned systems were proposed. Instead, their proposed eliminations listed above create an extraordinary window of vulnerability, particularly with elimination/curtailment of F-35s, while we wait for both stealth new-start unmanned systems and the LRS-B that will cost $700 million each. We know there would be cost overruns and delays on both.
Sometimes a bird in the hand is worth two in the bush. Their study claims the F-35 is only semi-stealthy yet attributes near perfect stealth to the J-20, J-31, and T-50 which are not even in production and provide hints that they provide less than all-aspect stealth. They assume in error that J-20s and ancient Chinese H-6 bombers will get close enough to our tankers and Guam to launch long range missiles.
A more likely scenario is that allied fighters launched from multiple stand-off airfields, roads, and carriers coupled with effective allies also flying F-35s will take out the few enemy "stealth" fighters very quickly. Simultaneously, PLA/Russian short-to-long range missile quantities will deplete damaging very little of prepositioned Army assets and leaving ample time to deploy light/medium/heavy Army armor, and Army Future Vertical Lift carrying dismounts to join prepositioned Army armor assets and MLRS to defend Pacific and European allies. Once the intertheater deployment challenge is overcome to secured points of entry, the intratheater push to get ground and Joint forces to affected areas from multiple locations won’t be as difficult with enemy ships mostly sunk, missiles largely depleted, and their few capable aircraft shot down. So much for A2/AD.
Exact same Crimea game being played out in the eastern Ukraine. "Legitimate elections equal legitimate government/country"-- annexation is a given under the new Russian UW strategy being played out.
Exactly the Crimea game play.
See the not so subtle Russian threat of annexation in this press release.
BRUSSELS, November 3 (RIA Novosti) - The European Union should recognize the recently held elections in the self-proclaimed Donetsk and Luhansk people's republics if it is interested in a political settlement of the Ukrainian conflict, Vladimir Chizhov, Russia's Permanent Representative to the EU, said Monday.
"I believe that if the EU is genuinely interested in the speedy political settlement of the crisis in the east of Ukraine, it should welcome these elections," Chizhov said.
"I am not calling for automatically recognizing the self-proclaimed republics, nobody expects that from the EU. But the fact that the residents of these regions have expressed their will should be recognized based on the democratic values advocated by the EU," he added.
For those that want to hear and see the current ongoing fighting at the Donetsk Airport --this is a live feed link compliments of the Russian TV and news agency Rupty which is based here in Berlin
http://www.youtube.com/watch?v=-NVJSWtQXRk
Side note for historical buffs--- the fighting in Stalingrad lasted 155 days---the fighting at the Donetsk Airport has broken that record by a bunch of days.
Smoke in the background is the airport.
Reports coming in via Ukrainian social media about Russian activities on the ground there today and still no response from the US national command authority and or the US mass media.
#BREAKINGNEWS A #RUSSIAN_ARMY HIGHTECH JAMMING DEVICE TOOK DOWN AN @OSCE_SMM DRONE ON OCTOBER 29TH.
It crashed near #Sartana, #Mariupol
#BRK_Report:"Agents in Novoazovsk announce the arrival of a large number of enemy armored vehicles. Russian troops are in full readiness."
#Luhansk rebel source: Tanks,apc,Grad,Russian paratroopers,motorized infantry,radio,special forces,+military doctors.
http://informator.lg.ua/?p=44762
#BreakingReport The entire road between #Rovenky and #Debaltseve is full of #Russian_Army troops.
Around 2000 w/tanks
#BreakingNews DNR/LC declare #independence from #Ukraine.
#Quote: "Donbass is no longer part of Ukraine."
While an interesting article today in The Daily Beast it totally reflects the lack of DoD and the WH in "seeing and understanding" the new Russian strategic/tactical UW and how it supports Russian driven neo imperialism as their new form of political warfare.
For going on six months the DoD/WH has seen Putin/Russia military implementing their new doctrine using heavy integrated SOF/intel units, conduct countless nuclear strike exercises both ground and air strikes, equip and man an 15,000 irregular army and send in their troops on "vacation"-an additional 12,000 and use some of their most modern heavy fighting equipment not seen outside the RF to create "New Russia".
Russian T-90s on the move, reportedly, in the Luhansk Oblast. pic.twitter.com/QR1W8GKqGp
Again not a single mention in the article of central Europe, nor the Ukrainians, nor Russia's UW strategy in the entire article---how seriously odd is that?
http://www.thedailybeast.com/articles/2014/11/03/the-pentagon-may-final…
So again just what was that DoD/WH plan for the new Russian strategic UW?
Outside of the German governments response this morning to the Russian backed/supported mercenary elections NOT a single peep out of the other US/NATO/EU capitals--strange is it not.
The only American diplomat currently using twitter and making some rather strong statements is the US rep to the OSCE.
Otherwise silence from the White House.
After the following below--can one really "trust anything Putin and or his FM state? They themselves pushed Minsk 1 and 2 and yet are not holding themselves to their own signature and the signatures of their mercenaries and virtually nothing outside of the Ukrainians not returning fire BECAUSE the EU/US wants it that way has been implemented as agreed to.
1. no completed civilian and military POW exchange--blocked by mercenaries
2. no withdrawal of heavy weapons and mercenaries into Russia
3. no OSCE monitoring o the Russia border outside of three CPs
4. no ceasefire
5. continuous land grapping by mercenaries
6. continuous Russian troops, heavy weapons and munitions are sill flowing into the Ukraine
So what is actually our US position as I have heard nothing about one nor seen VP Biden lately in the Ukraine or heard any direct supporting statement from the White House in literally?
Russian Foreign Ministry statement to the mercenary elections:
The European Union, the United States and the United Nations have spoken out against the elections, claiming they undermine the agreements reached in Minsk. Meanwhile, Russia has expressed its intention to recognize the elections and has emphasized that not recognizing them will run counter to the Minsk agreements.
Russia's Recognition of Ukrainian Separatist Election Is 'Incomprehensible,' Germany Says: http://www.themoscowtimes.com/news/article/russias-recognition-of-ukrai…
DNR/LC leaders: "After elections, we have a legitimate govt. Donbass is no longer part of Ukraine,like it or not"
pic.twitter.com/OLkE7MYWeM
Breaking: @OSCE_SMM head Amb Apakan announces @OSCE UAVs hit by jammers as Russia-backed fighters attacked Ukrainian ckpt on Oct 29.
@OSCE_SMM drones being targeted by Russian proxy fighters is yet another example of undermining Minsk framework & escalating conflict.
Amb Apakan stresses importance of monitoring of Ukraine-Russia stateborder by @OSCE_SMM in accordance w Minsk protocol
Robert--just a side comment---there is right now a Russian "invasion" in full progress just based on the sheer number of Russian military vehicles that have been on the move into the Donetsk from Russia since the last 72 hours. Even the Ukrainian National Security Council has confirmed an unusually high volume of military movements by the Russians.
https://en-maktoob.news.yahoo.com/kiev-claims-intensive-movements-troop…
#Footage claims to show major Russian army tank force, that did not make it with the rest of the convoy to #Donetsk.
https://www.youtube.com/watch?v=Geq5JF6W718
VIDEO #Russia electronic warfare convoy arrived #Donetsk today some w Camo netting
http://www.youtube.com/watch?v=DnM1Hmfd6eg&list=UUAZg55_KAkaKdJxqDd4JksA … #Ukraine pic.twitter.com/0zbIwe71M7
Heck even one of their "humanitarian aid trucks" that arrived yesterday flipped over yesterday in downtown Donetsk--the Russians were claiming it carried food BUT behold there were crates of ammunition scattered all over the roadway.
Russian ‘food convoy’ truck overturns in #Donetsk revealing ammunition http://zik.ua/en/news/2014/11/02/russian_food_convoy_truck_overturns_in…
AND Russian SOF is deep in the fight as well complete with new weapons not seen outside of mother Russia.
The monkeys from #Donetsk show off #Russian army Pecheng MG & AS Val SOF assault rifle. https://twitter.com/forest_brother/status/528969625577328640 …
BREAKING #SBU intercepted phone call of #Donetsk terrorists @ 17:00 on Nov 2 telling what the result must be. SHAM!
pic.twitter.com/gCmJcwgb3j
I would argue the entire EU/NATO/US leadership has "blinked through" a large number of verbal "redlines" they have all stated in the last six months concerning both the Crimea and eastern Ukraine to the point they are now a tad "colorblind".
RC--intelligence is the critical key to a national UW/CUW strategy.
But higher than that is the ability for the NCA to speak truth to power and inform the public to exactly what is ongoing.
This was reported in a number of ways yesterday out of the eastern Ukraine and not a single US/EU/NATO media comment, White House press release and or twitter comment---absolutely nothing---but check the amount of reporting and WH comments on a bunch of crazies waving a "black flag" who definitely do not have a nuclear trigger finger and the weapons to push the button with.
Practice nuclear airborne strikes against NATO members, threat of tactical nuclear weapons being used and SS21s moved into the Ukraine, complete nuclear triad from Russia has been test fired in less than 72 hours,subs in Sweden and an invasion force on the Ukrainian border than has now moved physically into the Ukraine-----
AND yet nothing from the NCA--just how strange is that?
A central European country has basically been invaded and yet from the US---we call it an "incursion" and that is what "truth to power"?
We as a country might as well just pull back into the physical USA and forget about the rest of the world---is an old US tradition but our intelligence commun9ty has failed badly in the Ukraine and with Russia--and we wonder why the IS is as strong as it is---having moved the intel to contractors has been the biggest mistake in the last 13 years.
Tymchuk: Also 110-115 tanks, 250-280 AFV's, 80-100 artillery guns and MLRS units are inside #Ukraine
Tymchuk: 14-15 thousand mercenaries & soldiers of the Russian Federation, as well as 10-12 thousand fighters from local gangs r in #Ukraine
Tymchuk: Also 500 units of vehicles (from #Russian army armored Kamaz and tankers to improvised Gun truck)
Tymchuk: Russian forces have 4 strike groups in #Ukraine with at least 24000 men, 110 tanks, 250 APCs, 500 trucks, and 80 artillery pieces
AND that is not an "invasion" using any English dictionary?
Outlaw,
I'm getting the dreadful impression our Intel people have started lying again. Back in the day I had assumed the KGB had penetrated our Intel agencies but an old pro from the Beltway was always of the opinion the lying was in response to a combination of inter-agency rivalry, fear at admitting mistakes, petty jealousies and similar Kafkaesque realities rather than something Machiavellian. Which he was a pains to point out posed more of a threat to National Security than the KGB.
RC
Robert---the last sentence is to a large degree correct---although I am not sure the argument that Russian "humiliation" by the US and NATO as being harped by Putin during the Crimean event and in his Duma speech is anything more than a "Russian perceived myth".
I would counter argue that it is largely driven by a Russian form of ultra nationalism that we would normally call in the west "fascism" that is both ethno driven and neo imperialistic in nature and it goes back to it being there even when it was the former Soviet Union. If one looks closely at all former Warsaw Pact countries there was already by 1998 a strong neo Nazi movement afoot even in the GDR and their "famous" Stasi who could not keep up with it and we now see it cropping up again in the form of right leaning anti European parties ie Hungary as a good example.
I had often thought it was just an outgrowth of just a common resistance to the then ruling communist system but when one pays even closer attention in the last couple of years to the overall European neo right developments it matches that of Russia like a glove. They both serve and support each other and that is largely being overlooked by our general media and our political leadership--ie when Russia "needs" election observers to establish "legitimacy" who shows up--check the rooster of the eastern Ukrainian observers that were there today--the who's who of the far left and far right.
I had a great professor of RAF terrorism here in Berlin in 1972 who stated---if terrorism is seen as a circle--the extreme left and right will always meet on that terror circle as they share common enemy/driver "myths" much as what we hear today from Russia and their alleged NATO "humiliations".
With the redline---I am no so sure that we currently can even think about a military redline as we have no noticeable military projection power left in Europe and jet aircraft really does not get the attention a large number of say Bradley's and Abrams would get.
Not even the press release of the First Cav on exercise here in Germany is going to impress Putin-- he knows it is just a show---now the entire First Cav Division on exercise in Poland and the Baltics--that get's his attention.
Germany -- Re-arm, re-supply and re-fuel operations at Hohenfels Training Area, Oct 26 with @1BCT1CD
pic.twitter.com/qFAbqbTcdN
And just how far is Hoehnfels from the Ukraine by rail as that is what it takes to move them--heck even to Poland takes time as they must move by German rail flat cars as the US military rail flat cars were mothballed years ago.
Putin knows this as well as the reluctance by Obama to use force--in some aspects he has read Obama extremely well.
Again non lethal supplies to the Ukraine does not send as clear and concise a message as does a large number of TOWs publicly delivered which was taken off the table by this administration at the beginning of Crimea.
A large number of well trained TOW teams are a great balancer of power on the battlefield as we are seeing in Syria especially where there are is an unusually large number of Russian tanks and APCs on the battlefield--that was the old NATO strategy in the 80s and it still works today.
Therein lies the core US problem--"soft power" at times needs a "hard power" element to lend credence and this administration is unwilling for some strange reason to lend credence to what it says.
The second strange thing is the "hang up" with the black flag waving guys who are not currently armed with tactical nuclear weapons the last time I checked the web.
In the ME it is destined that borders will change as it was all forced line drawing by the colonial powers anyway--but the redrawing of European borders after the Wall--that is a total different game.
While irritating and of reasonable concern to the West and those who see stability and interests served best by sustaining the status quo of current borders, governments and limitations on the sovereignty of the entities involved - one has to also recognize that Russia is acting reasonably (and therefore predictably) to secure their interests and best future as they perceive them.
Russia is being a hell of a lot smarter, realistic and effective than the West. That stings our pride, but there it is. Point Russia.
Two primary conditions opened the door to Russia to make this move.
1. Provocation. The unnecessary and unwise expansion of NATO into Russia's sphere of influence has been incredibly provocative by the West. Yes Russia needs a "red line;" and yes, the nations clamoring to join NATO see being a member of NATO as being on the correct side of said red line; and yes, we were desperate for partners to join and validate our operations in Afghanistan. But we played this poorly with little empathy for how it would be reasonably perceived by others, or thought about the likely reaction.
2. Failed deterrence. The excessive pursuit and poorly framed response to the events of 9/11 have left the United States over-extended, over-spent, and overly weary of committing our military yet again to some adventure overseas that many cannot see the value of. Russia has waited their moment, tested the water, and then acted in a manner that would be least likely to trip a "we gotta do something" response among the American public.
So, the primary "counter-UW" the US must conduct in this case is to address these two factors. Reduce unnecessary provocation and give Russia a clear, reasonable and enforceable redline; and restore effective deterrence.
While the author of this article spent a lot of time on it--he basically fails--Russian has been implementing phase for phase of their eight phase UW strategy in the eastern Ukraine and nothing that the author writes here is designed to currently stop that because we the US have no strategy whatsoever for the Ukraine.
1. Russian has held the important "elections" similar to the Crimea and now have legitimacy in eastern Ukraine from the Russian speaking population
2. There was an "invasion" force sized Russian military buildup along the border to the Ukraine and the West never said a single word about it
3. On all Russian TV stations broadcasting the weather news inside Russia they are fully including eastern Ukraine now in their weather maps as part of the Russia land mass map
4. There has been really large Russian military convoy movements over the last 72 hrs into eastern Ukraine---again not a single comment from the US/NATO/EU--some might even say they have now fully crossed into the eastern Ukraine or what some might in fact call an "invasion", but we cannot get past the term "incursion".
Then this today from the Ukrainian government:
FRANCE 24
Kiev claims 'intensive' movements of troops crossing from Russia http://f24.my/1vzbkjo
pic.twitter.com/Z1wqf5dgRX
The core question now is has the author not fully understood that the Russian eight step process has been in full swing for the last six months and all we in the West do is discuss the "problem" and send "blankets" to the Ukraine and MREs.
Russia made an interesting move from phase four of their strategy to phase six several months ago when their mercenaries were losing--it now appears they are jumping straight to phase eight after a one month in phase seven to total military annexation (using phase eight) of the "full New Russia" taking the Odessa land corridor and cutting the Ukraine off from her two natural seaports thus rendering the Ukraine a full vassal of Russia.
AND what was the response from the West "bombing" a bunch of black flag waving Salafists who do not have any tactical nuclear weapons---strange world the US is in.
For those that might not understand the Russian UW strategy phases six through eight.
Sixth Phase: commencement of military action, immediately preceded by large-scale reconnaissance and subversive missions. All types, forms, methods, and forces, including special operations forces, space, radio, radio engineering, electronic, diplomatic, and secret service
intelligence, and industrial espionage.
Seventh Phase: combination of targeted information operation, electronic warfare operation, aerospace operation, continuous airforce harassment, combined with the use of highprecision weapons launched from various platforms (long-range artillery, and weapons based on new physical principles, including microwaves, radiation, non-lethal biological weapons).
Eighth Phase: roll over the remaining points of resistance and destroy surviving enemy units by special operations conducted by reconnaissance units to spot which enemy units have survived and transmit their coordinates to the attacker's missile and artillery units; fire
barrages to annihilate the defender's resisting army units by effective advanced weapons; airdrop operations to surround points of resistance; and territory mopping-up operations by ground troops.
Another key element in the new Russian military doctrine of strategic/tactical UW is the heavy use of informational warfare.
For those that read Russian---great article on the poor working conditions of a "Russsian troll" ie someone who blogs for the FSB.
Great report in Russian on a troll factory in St. Pete. 250 ppl working 12 hour shifts, 24 hours a day. Poor things.
There seems to be no way the US can compete with the Russian info war as we would not work under those conditions and nor the low salary of 700-800 Euros that was being recently advertised on the net.
Not even our own mass media is even getting the stories right in the Ukraine nor are they really interested in carrying any Ukrainian stories as "crazed Islamists" waving "black flags" carry the news cycles these days.
In understanding the new Russian UW strategy one must fully understand the thinking of those around Putin who have contributed to the development of that doctrine.
This is an interesting initially secret speech given by the then Putin senior advisor Surkov from 2005.
http://www.network54.com/Forum/155335/thread/1164815166/last-1164815166…
One of the major tenets of the new Russian military doctrine is the integrated use of SOF, irregular forces, and active military in their strategic/tactical form of UW.
This below shows just how far along Russia is in their development of their version of strategic and tactical modern UW warfare.
#BREAKINGNEWS UKRAINIAN FORCES CAPTURE #RUSSIAN_ARMY NORTHERN FLEET SPETSNAZ OFFICER FROM MURMANSK AT DONETSK AIRPORT
pic.twitter.com/q8h8wwPPLG
What is apparent is that our intelligence has totally failed in the Ukraine and our current military seems still determined to continue training to the DATE scenarios when the Russian military is giving them for free a "virtual lesson in UW strategic/tactical deployments" in support to political warfare that is so far advanced no DATE scenario can come close it.
The Army still is training in their simulations and exercises COIN based experiences tied to Attack the Network (AtN)--does anyone else see a total disconnect to the current reality of the world by DoD and the US Army?
Referencing our current intelligence failures in the Ukraine---there have been a massive series of large military convoys of new armored Kamaz trucks, heavy artillery, fueling trucks, and MRLSs moving towards the Donetsk over the last three days.
No one can tell me we did not see this via all of the NATO/US ISR assets over the Ukraine and yet out of the various NATO capitals--silence.
Even the social blogging world in Europe is slowly believing that the US/NATO are in another world.
HOW COULD @OSCE_SMM, @NATO AND @NSDC_UA BE SO WRONG?!?!...
THE 'ENTIRE' F....... RUSSIAN ARMY SEEMS TO BE IN DONBAS NOW
For those that have not been following daily the Donbas events-- three months ago the mercenaries were crying that only about 1000 locals were fighting with them---and now we are at the rough range of 30,000 Russian fighters inside eastern Ukraine---WHERE did they are come from if only 1000 were "locals"?
Another form of Russian UW strategy---using little known and or not even known organizations to "lend legality".
"Association for Security and Cooperation in Europe" to monitor DNR "elections." Google has never heard of them:
http://bit.ly/1s2mwUg
Donetsk separatist really thought up an "Аssociation for Security and Co-operation in Europe" (ASCE, АБСЕ in Russian) http://dnr.today/news/mezhdunar'
DNR election com. member Kubayev: "Technically this election is the same as any other election that takes place in democratic countries."'
The ability to scale and or morph the Russian UW gives it strategic strength and durability---something our DoD designed UW doctrine does not do.
Two examples from today: The second example is the most interesting as Russia is now taking a chapter out of Maidan and protesting physically in Kyiv for Russians--kind of an in your face thing.
From Interfax today:
Example 1:
11/01 14:42 Crimean leadership declares moral support for elections in self-proclaimed Donetsk republics
Example 2:
11/01 14:08 Pro-Russian association in Ukraine preparing Slavic March in Kyiv on Nov 4 - Russian nationalist leader
The current speed of the Russian UW strategy morphing changes that occur daily should be intensively watched.
The following has happened over the last five weeks.
1. Russian conducted in their eastern regions a truly well organized combined arms and air assault exercise on the invasion of a middle sized country.
2. Prior to that exercise---the western region exercise tested the firing of tactical nuclear weapons in the direction of both Poland and the Baltics.
3. Both Putin, his FM and numerous ultra nationalists have openly threatened the use of tactical nuclear weapons at NATO and the US.
4. Russian has mobilized a massive sized and it can be called an "invasion" force again on the borders to the Ukraine ALL the while more Russian GRU/SF recon and sabotage teams move into the Donbas region in BN size.
5. The latest "aid convoy" brought in no food and humanitarian supplies for the population but rather winter uniforms, and ammo for the mercenaries.
6. Russia multiple times in the last four days basically is abandoning their own signed Minsk 1 and 2 agreements.
7. The crashing oil price and the truly collapsing Rubel and the sectorial sanctions are not having an effect on Putin---in fact they maybe speeding up his timeline in order to complete his "victory" before the economy does in fact crash back to 1998.
8. Russian ran in the last three days multiple simulated nuclear air strikes in the NATO regions coupled with similar "simulated" strike attacks against the US/Canada last month.
9. That has been a literal "rash" of ICBM test firings in the last three months.
10. Russia has deployed totally new weapons systems into the Ukraine that have never been seen outside of the RF.
So after all of the above---again the question should be "is it to late for a national UW strategy"?
Maybe it is time to pull out all of the old Cold War NATO planning documents as it does appear that Putin is using the not so subtle threat of a nuclear war and using extensively now his military in an effort to "cower" NATO/EU and the US into submitting to his plans for the Ukraine.
Better yet after all of the above can even Russia and that is basically Putin even be "trusted" as everything he has stated he would be doing never quite seems to occur.
Or did I miss something over the last six months?
An example from just yesterday on the web here in Europe---interesting how the rules of Twitter and Facebook are being abused to shut down Ukrainian and English sites that track Russian activities.
Seems that American business executives do not mind being used by the Russians as well.
There is some serious online trolling/hacking/attacking going on tonight
Just as critical in having a national UW and C-UW strategy is having an equally effective info war capability.
Perfect example of what is being feed to the Russian population as a whole and to a lesser degree the global world population on a daily basis.
Russian TV station broadcasts to the Russian population that over 99% of the eastern Ukraine and under mercenary control participated in the recent elections.
#Russia RT NEWS Propaganda on #Ukraine elections FAKE http://bit.ly/1wN5Q6N REAL http://bit.ly/1yMgfAN
This goes back to my number of the same comments---just why are we the US somehow so hung up on "black flag" waving radical Islamists rather than a somewhat living in "an altered state of reality Putin" who has threatened nuclear strikes against the US/NATO three times in the last six months.
IF the IS had threatened the use of a nuclear weapon would we have remained so quiet---so why is it we are so quiet with Russia?
Per some ex-¤t US Air Force SIGINT specialists in DailyBeast say #Russia has carried out nuke assault exercises
pic.twitter.com/pplI0GuUzj
Russian bombers conduct nuclear drill off #Ireland and anti-nuclear #Irish stay silent because it's anti-NATO?
Explains just why we will never have a truly national UW or C-UW strategy.
This generation talks way to much.
I remember an America where people went into world of spooks & SOF understanding there'd be no best-selling memoirs
http://www.nytimes.com/2014/10/31/us/former-navy-seal-matt-bissonnette-… …
Consider this from John Lewis Gaddis:
" ... it follows that ideas, ideologies, and moral frameworks become very significant. We have gone too far looking at the Cold War within a materialist framework devoid of moral content. This was, from the outset, a struggle for people's minds as well as for their bodies and their possessions. We are sure to understand it (the Cold War) badly if we fail to take that fact into account."
https://www.mtholyoke.edu/acad/intrel/gaddis.htm
Likewise today, does the author (and numerous others) make this same mistake -- by seeing the conflict more in materialistic (example: "development") rather than in moral terms? Herein, consider this from the author's concluding paragraph:
"... like the battles fought throughout the Cold War and the Soviet Union’s subsequent collapse in 1991, it stands to reason that the more legally just, socially cohesive, economically sustainable, and politically sound society will prevail; all of which the U.S. is characterized by in abundance and conversely is lacking within the societal constructs of United States’ primary nation-state adversaries.
In this regard, consider this thought:
a. If the U.S. fought on the side of -- and significantly relied on -- conservative elements and conservative causes during the Cold War, and, thereby, "won,"
b. Is it likely that the United States today, acting as the champion of liberal causes and relying on liberal elements, will meet the same fate as the Soviets?
Thus, in the "struggle for people's minds as well as for their bodies and their possessions" (described by Gaddis above), does:
a. The role-reversal, "us" v. "them," that I have outlined above and elsewhere,
b. And the difficulties presented by same (associated with championing liberal rather than conservative causes and elements),
c. Become the matters that we must concentrate on most,
d. Re: our endeavor to counter nation-state (and other) use of protracted unconventional warfare against us?
This might explain just why there is no US strategy towards the Russian UW strategy in the Ukraine or for that matter any strategy at all out of this WH.
Obama's NSC has now surpassed Johnson's for incompetent micromangement in warfighting, which is quite an achievement.
http://www.thedailybeast.com/articles/2014/10/31/military-upset-with-wh… …
My greatest worry is how Obama's terrible NSC will handle Putin's next aggression when - not if - it comes. Huge stakes. I'm not confident.
WH is in the middle of a full-fledged civ-mil crisis over #ISIS & ME, combined with meltdown of NSC & Depts. This is a very bad combination
“Not farfetched that...within 2 years Putin makes a...move in E Europe & uses nuclear threat to deter NATO response.”
http://www.thedailybeast.com/articles/2014/10/30/are-russian-bombers-fl… …
I heard endless screams from CENTCOM during W's tenure. What I'm hearing from Tampa now about Obama's people is even worse. Really.
