Trusting Smart Cities: Risk Factors and Implications
Margaret L. Loper
This article is the latest addition to the U.S. Army TRADOC G2 Mad Scientist Initiative’s Future of Warfare 2030-2050 project at Small Wars Journal.
In the coming decades, we will live in a world surrounded by tens of billions of devices that will interoperate and collaborate to deliver personalized and autonomic services. This paradigm of objects and things ubiquitously surrounding us is called the Internet of Things (IoT). Cities may be the first to benefit from the IoT, but reliance on these machines to make decisions has profound implications for trust. Trusting smart cities refers to the confidence and belief of smart city installations to be capable of operating securely, reliably, and accountably. To understand how trust applies to smart cities, we introduce formal definitions of trust and risk, and present three risk factors that capture the range of issues that must be considered when deploying smart city technologies. Building on these risk factors, a threat analysis matrix for capturing how well smart cities are addressing these risks is proposed. We close the paper with some thoughts on the future of warfare in smart cities.
Introduction
The urban environment is becoming increasingly more connected and complex. In the coming decades, we will be surrounded by billions of sensors, devices and machines, the Internet of Things (IoT). Cities and urban areas that benefit from the IoT are commonly referred to as Smart Cities (SC) [1]:
"A smart sustainable city is an innovative city that uses information and communication technologies and other means to improve quality of life, efficiency of urban operation and services, and competitiveness, while ensuring that it meets the needs of present and future generations with respect to economic, social and environmental aspects."
The idea of a SC can be applied to other domains as well, such as smart military installations, smart compounds, and smart campuses. [i] Smart city applications are developed with the goal of improving the management of urban flows and allowing for real time responses to challenges. However, there are security risks associated with deploying distributed sensor networks in urban environments. One risk is the ability of adversaries to gain access to civilian infrastructures and use them against us. Therefore, it is critical to understand how these IoT technologies will be used in urban environments, their operational behavior, how citizens will interact with these sensor networks, and security implications of large scale deployment in urban environments.
Cities may be the first to benefit from the IoT, but being surrounded by billions of sensors, devices and machines has profound implications for security, trust and privacy. The more technology a city uses, the more vulnerable to cyber-attacks it is, so the smartest cities face the highest risks. While security, privacy and trust are all critical areas for IoT, our specific interest is focused on Trust.
The need for trust has long been recognized, as stated in [2], the “… pivotal role in … decision making means it is essential that we are able to trust what these devices are saying and control what they do. We need to be sure that we are talking to the right thing, that it is operating correctly, that we can believe the things it tells us, that it will do what we tell it to, and that no-one else can interfere along the way.” This brings us to the idea of whether we can trust smart cities.
This paper is organized as follows. In section II we introduce a formal definition of trust and its inverse relationship to risk. In order to understand how trust applies to smart cities, we introduce three risk factors in Section III. A threat analysis matrix is introduced in Section IV, which represents the next steps in understanding the risk to smart cities. We close the paper with some thoughts on the future of cyber-attacks on smart cities.
Trust and Risk
There are several definitions of trust. Trust is the belief in the competence of an entity to act dependably, securely and reliably within a specified context [3]. Trust is the extent to which one party is willing to depend on somebody, or something, in a given situation with a feeling of relative security, even though negative consequences are possible [4]. In other words, trust is a broader notion than information security; it includes subjective criteria and experience. Trust includes concepts, such as
- Perception – awareness of something through the senses;
- Memory – past history and experience; and
- Context – trust may exist in one situation, but less or not at all in another.
The subjective nature of trust relies on one’s willingness to participate in a transaction, and the relative security of the outcome of the transaction. Thus, there is an aspect of dependence, which includes both uncertainty through possibility and risk through negative consequences [4].
Risk emerges when the value at stake in a transaction is high, or when this transaction has a critical role in the security or the safety of a system. “In most trust systems considering risk, the user must explicitly handle the relationship between risk and trust by acknowledging that the two notions are in an inverse relationship, i.e. low value transactions are associated to high risk and low trust levels and vice versa, or, similarly, risk and trust pull in opposite directions to determine a users’ acceptance of a partner.” [5]
To understand how this inverse relationship applies to smart cities, we define three key risk factors [6]: non-technical, technical and complexity. Non-technical risk includes aspects of a SC where humans are involved, such as management, training and education, governance and security practices.
Technical risk factors focus on the technology aspects of a SC, including both hardware and software systems. This also includes the concept of cyber-physical systems, which is a system of collaborating computational elements controlling physical entities. The last risk factor is complexity. A smart city is not a discrete thing; it is the complex multi-dimensional interconnection of diverse systems (human and technology) that deliver services and promote optimum performance to its users. There is risk in the complexity of these systems, especially as the scale becomes very large. These key risk factors are described in more detail in the following section.
Risk Factors
In this section, we describe examples of risk that fall into each of the three dimensions.
Smart cities represent a fundamental change to the way that services are delivered – it’s not primarily about technology, but about service transformation and improvement [7]. This brings into focus the importance of processes and people, i.e. how to make a city smart and who manages it. This leads us to the non-technical risk areas: management, training and best practices.
Management. Advanced technologies increase complexity and uncertainty. The greater the risk, the more necessary it is to have effective managerial and policy tools to deal with the risk. Performance of smart cities will depend on effective management of the systems and infrastructure, not purely the performance of the systems themselves. Information technology (IT) deployment is a complex endeavor, and failure to manage the high risks associated with a deployment can lead to total failure in technology-driven public sector projects. An example of this is the disastrous roll out of the health information marketplace for the Affordable Care Act. [8] In fact, 85% of all IT projects fail because of the challenges by non-technical aspects of innovation, in large part - policy, organization, and management-related risks [9].
Training and Education. The infrastructure supporting the digital economy is growing more complex. Companies and cities increasingly run their computing systems on virtual machines, and cloud services have become a standard business practice. Yet, despite the influx of technology, there is a significant lack of trained security experts, which will result in a shortfall of as many as 1.5 million workers by 2020 [10]. The security skills shortage tends to be worse in the public sector - the most talented people are attracted to the private sector due to higher salary and compensation. Therefore, as cities become smart, attracting qualified people and offering them competitive pay will be challenging. One option is to train the current workforce, while also working to attract younger generations into technology fields (i.e., increasing the pipeline of potential workers). However, this requires an investment above and beyond normal equipment purchases, and operation and maintenance of those systems. Obtaining a training budget for security and smart city technology requires educating leaders and obtaining buy-in, which can change with every election.
Best Practices. Cities need to enforce security practices to help them combat extreme threats. There are many lists of “best practices” that provide useful guidance to defend against the majority of security threats. One such best practice is rigorously testing devices and systems. Cities may test for functionality, resistance to weather conditions, etc, but they often perform little or no cyber security testing [11]. According to Cerrudo, about 200,000 vulnerable and insecure traffic control sensors were installed in cities such as Washington D.C., New York, Seattle, San Francisco, London, Lyon, and Melbourne. Information from these sensors could be intercepted 1,500 feet away because one company failed to encrypt its traffic. This security hole could have enabled someone to make traffic lights stay red or green, tweak electronic speed limit signs, or mess with ramp meters to send cars onto the freeway all at once. This security gap could have been caught had these cities or the software vendor had performed the appropriate security testing during deployment of the devices and/or through routine security screening. Unfortunately, "most product vendors are releasing hardware, software without any security, and governments are releasing it without any testing." [12]
Technical
Technology is the enabler of a smart city, which includes both hardware and software systems. Examples of technology risks include: information security, software development, and the design of cyber-physical systems.
Software Development. Municipalities taking advantage of sensors and data networks to create cities that are more transparent and more responsive to their communities are the next frontiers of IoT. Key to accomplishing this goal is whether we can get the software right. Vint Cerf was quoted as saying, "We don't know how to write software without bugs. We've been trying for 70 years." [13] If smart cities are going to rely on software to run critical infrastructure and services, how do we trust it knowing it very likely has bugs?
An example of what could happen occurred August 14, 2003. In a city running 100’s of systems for critical services, a software bug had huge impact due to a chain reaction or events. A blackout affected almost 10M people in Ontario, Canada and 45M people in 8 U.S. states. The blackout’s primary cause was a software bug in the alarm system [14].
Cyber Attacks. The number of cyber-attacks on critical infrastructure systems is increasing. In 2012 Chinese military hackers breached a Canadian company that produces software that allows oil and gas pipeline companies and power grid operators to remotely access valves, switches and security systems. The company also kept detailed blueprints on more than half the oil and gas pipelines in North America [15]. In 2014 security researchers at the Black Hat Europe demonstrated how to black out parts of cites by manipulating smart meters and exploiting encryption problems in power line communication technology [11]. Cerrudo also describes another attack involving the Department of Homeland Security (DHS). In 2014 DHS acknowledged that “a sophisticated threat actor” had broken into the control system network at a public utility, simply by guessing a password on an Internet-connected system. Most recently hackers were able to remotely kill a Jeep on the highway [16]
Smart cities will use wireless sensors to control everything from traffic lights to water management; therefore, the attack surface for cities is huge. There isn’t a notion of an “internal network” in smart cities. The smarter the city, the more computer systems, the more integration between the systems, and the more open the access to the data collected by all those systems. This presents a wide number of possible attack vulnerabilities. According to the 2013 Symantec Internet Security Threat Report, 22% of targeted attacks are aimed at governments and energy/utilities companies, while governments and healthcare institutions are the target of 24% of identity breaches [17].
IoT raises a wide range of serious security challenges, since many IoT devices interact closely with the physical world. Devices may have poor or nonexistent security features, or worse, are not able to defend themselves appropriately, due to limited computing and power resources. The problem is exacerbated by the fact that many IoT devices may be built using potentially old operating systems and libraries that are not fully patched. If a device relies on open-source software with vulnerabilities (e.g., the many routers that used the version of OpenSSL that was susceptible to the Heartbleed virus), updating the firmware on such devices can be difficult [18].
Trusting Data and Devices. Another risk lies in that devices may misrepresent themselves. In other words, they are intentionally programmed to cheat. An example is the recent case where Volkswagen was found to have programmed their software to cheat on emissions tests [19]. Cheating is any action that intentionally misrepresents the product’s behavior for the purpose of gaining an unfair advantage, e.g. Volkswagen deceived regulators to pass the emissions tests and deceived consumers to sell more vehicles. Delegating more control and decision making to devices could create more of a temptation to cheat. For large companies with well-established brands, the risk of exposure in cheating may dissuade them. However, the risk is much lower for IoT and Smart City startups, so the temptation to cheat will be greater [18].
Related to trusting the device is trusting the data. One of the biggest concerns about smart buildings and smart cities is that the sensors in the equipment can be hacked and fed fake data - which could be used for all manner of mischief, like causing signal failures that shut down subways or allowing contaminants into the water supply [12]. “When we see that the data that feeds smart city systems is blindly trusted and can be easily manipulated - that the systems can be easily hacked and there are security problems everywhere - that is when smart cities become dumb cities” [15]. There is a growing need to validate, regulate and trust IoT devices.
Complexity
The core systems in a smart city are not discrete; it is the complex multi-dimensional interconnection of diverse systems that promise to deliver unique services and promotes optimum performance. In this light, a smart city can be thought of as a complex system. Complex systems are composed of interconnected parts that as a whole exhibit one or more properties not obvious from the properties of the individual parts [20]. Smart City complexity can lead to two types of risk: cascade effects and normal accidents.
Cascade Effects
A cascade effect is an inevitable and sometimes unforeseen chain of events due to an act affecting a system.[ii] Cascade effects are a real danger for smart cities due to the complexity and operational interdependencies that exist among systems. When cities are running hundreds of systems and devices for critical services, it will be difficult to identify what is exposed and how the system will react. As a result, a simple software bug or a cyber-attack could have a huge impact due to interdependency and chain reactions. For example, what would commuting look like with non-functional traffic control systems, no streetlights, and no public transportation (e.g., subway)? How would citizens respond to an inadequate supply of electricity or water, dark streets, and no cameras? What if waste collection was interrupted during the summertime, and garbage piled up and began to stink in the streets? Attackers know about cascade effects, and that it can be used to their advantage by launching an attack on a small, poorly secured system that doesn't seem very critical, which sets off a chain reaction [12].
Normal Accident Theory
Normal Accident Theory is a framework for characterizing complex technological systems such as air traffic, marine traffic, chemical plants, dams, DNA research and especially nuclear power plants according to their riskiness [21]. According to the theory, accidents in complex systems are presumed to be unavoidable because innocent and seemingly unrelated events accumulate and align to create major malfunctions that produce disastrous results. In his book, Perrow presents a number of detailed examples, including this description of a DC-10 crash cited from a National Transportation Safety Board report:
The loss of control of the aircraft was caused by the combination of three events: the retraction of the left wing’s outboard leading edge slats; the loss of the slat disagreement warning system; and the loss of the stall warning system – all resulting from the separation of the engine pylon assembly. Each by itself would not have caused a qualified flight crew to lose control of the aircraft, but together during a critical portion of the flight, they created a situation, which afforded the flight crew an inadequate opportunity to recognize and prevent the ensuing stall of the aircraft.
Perrow identifies three conditions that make a system likely to be susceptible to Normal Accidents: the system is complex, the system is tightly coupled, and the system has catastrophic potential. Combination, connection and integration of systems and infrastructures are fundamental to a city being smart. The smarter the city, the more computer systems it will have, the more integration between the systems will be needed, which means that there is a greater possibility that things can go wrong. Smart cities could connect millions (or more) of people, machines, sensors and devices. As more machines are connected, they will outnumber people and it will be impossible for humans to monitor and control all these machines. Therefore, some decision-making will be delegated to machines in the system. Add humans into this complex loop, and accidents can happen. The sheer scale and complexity of these systems leads us on a path to normal accidents.
Security Implications
Now that the risks have been defined, the next step is to analyze how well smart cities are doing as compared to existing threats. Threats can be characterized as current (or imminent), sometime (not persistent), tolerable (can recover from) and intolerable (e.g., black swan events).[iii] An analysis should look at threats to smart cities, group them into one of these four categories, and grade how well a SC is able to respond to these threats in the three risk areas. A matrix for this analysis is shown in Figure 1. This analysis would help smart cities understand the security implications they face in the future and take steps to start addressing them.
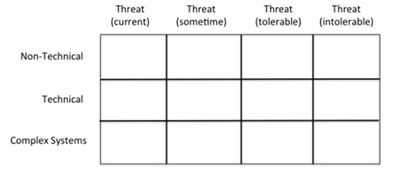
Figure 1. Security Implications of Smart Cities
Conclusions
Public safety and security is becoming increasingly challenging as homegrown and ISIS- inspired terrorism comes to large metropolitan cities. City governments are expected to address all of these challenges and solve them, in some part, with Smart City technologies.
Every new technology and innovation brings challenges and problems. Currently, cities around the world face huge cyber security problems. These problems could have a direct impact on government, residents, and the businesses and organizations that conduct business there. Cyber security in cities is extremely important, but we have yet to fully realize the risk [11].
An obvious question is whether we are overplaying the cyber risk that cities face. After all, it isn’t equivalent to war, or worse nuclear war, is it? We typically think of war as being fought on land by people. However, in 2009 the Secretary of Defense directed the Commander of U.S. Strategic Command to establish United States Cyber Command (USCYBERCOM). "USCYBERCOM plans, coordinates, integrates, synchronizes and conducts activities to: direct the operations and defense of specified Department of Defense information networks and; prepare to, and when directed, conduct full spectrum military cyberspace operations in order to enable actions in all domains, ensure US/Allied freedom of action in cyberspace and deny the same to our adversaries." [22] From the military’s perspective, cyber is a form of warfare.
In 2008 the conservative Hoover Institution claimed a new weapon of mass destruction (WMD) exists in computer malware and botnets, coining the term “electronic Weapons of Mass Destruction” or WMD. The authors state “While one hopes eWMDs will never be able to cause the loss of life that other weapons of mass destruction (nuclear, chemical, biological) can cause, they should still be recognized as having the potential to destroy livelihoods or even entire economies. . ..” [23]. There was not unanimous agreement over their view that cyber-attacks were equivalent to WMDs, but it did generate conversation about passing laws to make it easier to track down botnet owners and spammers as well as force internet registrars to provide factual registration information.
This issue resurfaced when the Deputy Chief of Systems Vulnerability & Assessment at the Defense Threat Reduction Agency, U.S. Army Major Quan Hai T. Lu, wrote a journal article on the new WMD challenge. In his article, he states “the IoT links individuals’ daily lives to that of the internet. This interconnectedness between people and cyberspace gives criminals, extremists, and adversary nation- states a vector to target individuals, private and governmental organizations, and U.S. civil society as a whole, and, in the process, it has inspired a fear of the unknown. In short, cyber is the new weapon of mass destruction threat, and addressing it will require marshalling the resources of the entire interagency” [24]. Lu argues that the methods and means may be different, but a cyber-attack on chemical facilities, biological research labs, nuclear power plants, and the nuclear command and control nodes is effectively equivalent to an adversary using WMD.
Regardless of whether you believe the emerging risks are equivalent to war or WMDs, action must be taken now, at the beginning of this evolution, to make cities more secure and protect against impending risks. Being prepared is key to preventing bigger problems and chaos. Cyber security problems are all around us, and smart cities will be wide open to cyber-attacks. This is a real and immediate danger. It’s only a matter of time before cyber-attacks on city services and infrastructure happen. The more technology a city uses, the more vulnerable to cyber-attacks it is, so the smartest cities face the highest risks. As defined in [9], smart city innovation requires advances in technology, organization, and policy:
- Technology innovation: a mechanism to change and upgrade technological tools to improve services and create conditions where the tools can be better used.
- Organization innovation: a mechanism to create managerial and organizational capabilities for effective use of technological tools and conditions.
- Policy innovation: a mechanism to address institutional and non-technical urban problems and create conditions enabling for a smart city.
- It is not technology solutions alone; all these areas are critical to solving the risks, enabling us to trust smart cities.
I would like to thank the Georgia Tech Research Institute, Information and Communications Laboratory for supporting my participation in the Georgia Tech Sam Nunn Security Fellows program. I would also like to thank Dr. Maggie Kosal, who leads SNSP, for thoughtful discussions on this project.
References
International Telecommunication Union, “Smart sustainable cities: an analysis of definitions,” ITU-T Focus Group on Smart Sustainable Cities (FG-SSC), 2014.
S. Peters, “Smart cities' 4 biggest security challenges,” Information Week, Dark Reading Vulnerabilities and Threats, 1 July 2015. http://www.darkreading.com/vulnerabilities--- threats/smart-cities-4-biggest-security- challenges/d/d-id/1321121
T. Grandison and M. Sloman, “A survey of trust in internet applications,” IEEE Communications Surveys and Tutorials, vol. 3, issue 4, pp. 2-16, 2000.
A. Jøsang and S. Presti. "Analysing the relationship between risk and trust." In Trust Management. Springer Berlin Heidelberg, 2004, pp. 135-145.
A. Patrick, “Building trustworthy software agents”. IEEE Internet Computing, Vol. 6, Issue 6, pp. 46– 53, November-December 2002.
M. Loper, “Trusting Smart Cities.” Technical Report, Sam Nunn Security Fellows program, Georgia Institute of Technology, Atlanta, Georgia, 2015.
City of Edinburgh Council, “Delivering the smart city: a 21st century government action plan,” 2001. Available at http://download.edinburgh.gov.uk/smartcity/.
R. Pear, S. LaFraniere, and I. Austen, "From the start, signs of trouble at health portal," New York Times, 2013. Available at: http://iittala.com/store- locator
T. Nam and T. Pardo, "Smart city as urban innovation: focusing on management, policy, and context." Proceedings of the 5th international conference on theory and practice of electronic governance, ACM, 2011.
M. Suby, "The 2013 (ISC) 2 global information security workforce study," Frost & Sullivan in partnership with Booz Allen Hamilton for ISC2 (2013).
C. Cerrudo, “Cyber security and the rise of smart cities,” Inform Tmforum, October 1, 2015. Available at: http://inform.tmforum.org/strategic- programs-2/open-digital/2015/10/cyber-security- and-the-rise-of-smart-cities/
R. Moulds, “The internet of things and the role of trust in a connected world,” The Guardian, January 23, 2014. Available from: http://www.theguardian.com/media-network/media- network-blog/2014/jan/23/internet-things-trust- connected-world. [retrieved: June 2014]
D. Patterson, “Cities first to benefit from internet of things, if we can write better software,” Tech Republic, November 5, 2015. Available at: http://www.techrepublic.com/article/vint-cerf-cities- first-to-benefit-from-internet-of-things-if-we-can- write-better-software/
Wikipedia, “Northeast blackout of 2003,” Accessed December 2015: https://en.wikipedia.org/wiki/Northeast_blackout_of_2003
N. Perlroth, “Smart city technology may be vulnerable to hackers,” The New York Times, Bits Blog, April 21, 2015. http://bits.blogs.nytimes.com/2015/04/21/smart-city- technology-may-be-vulnerable-to-hackers/?_r=0
A. Greenberg, “Hackers remotely kill a jeep on the highway—with me in it,” Wired magazine, July 21, 2015.
Semantec, “2013 Symantec internet security threat report,” pp.15 and 91 http://www.symantec.com/security_response/publications/threatreport.jsp?inid=us_ghp_thumbnail1_istr- 2013
Computing Community Consortium, “Systems computing challenges in the internet of things,” Computing in the Physical World Task Force, September 22, 2015.
J. Linkov, “Volkswagen emissions cheat exploited 'test mode',” Consumer Reports, 25 September 2015.
C. Joslyn and L. Rocha, “Towards semiotic agent- based models of socio-technical organizations,” Proceedings of the AI, Simulation and Planning in High Autonomy Systems (AIS 2000) Conference, Tucson, Arizona. 2000.
C. Perrow, Normal Accident Theory, Living with High Risk Technology, New York: Basic Books, 1984.
DoD, “U.S. Department of Defense, Cyber Command Fact Sheet,” May 21, 2010. Available at: http://www.stratcom.mil/factsheets/2/Cyber_Command/
K. Zetter, “Computer malware the new ‘weapon of mass destruction’,” Wired Magazine, December 12, 2008.
Q. Lu, “Cyber attacks: the new WMD challenge to the interagency,” InterAgency Journal Vol. 6, Issue 2, Special Edition, Spring 2015.
End Notes
About the Author(s)
Comments
I believe that our life…
I believe that our life should be unconditionally safe and attractive. When the necessary steps are taken towards energy conservation, I welcome this.
Traveling around the world,…
Traveling around the world, I have repeatedly witnessed how people are trying to save natural resources. And it becomes very relevant at the moment. Thanks to https://narrowband.com/applications/smart-lighting which created smart city lighting, I was able to significantly reduce energy consumption in my locality. Everything around is developing and changing every day and this requires us to use natural resources more rationally. I am sure that technology needs to adapt to the changing pace of urban life and look for new ways to save money. Making city life safer and more attractive and glad to be able to contribute to energy conservation.

