Treating Islamic Violent Extremism as a Pandemic Super-Infection: Inverse Darwinist Operations Line of Operation Explained
Thomas Doherty
Authors Note: This is a continuation of the article “Treating Islamic Violent Extremism as a Pandemic Super-infection” (http://smallwarsjournal.com/jrnl/art/treating-islamic-violent-extremism-as-a-pandemic-super-infection). That article outlined a concept for defeating the Global Jihadi Movement (GJM) consisting of three Lines of Effort (LOE) and two Lines of Operation (LOO). Future articles will continue the process of explaining this concept. This particular article will explain the LOO known as Inverse Darwinist Operations. By following the concept for this LOO, the leadership of a Violent Extremist Organization (VEO) within the GJM will be set up for defeat.
The platoon had been laying there waiting for hours in the cold. Their mission was to disrupt enemy operations. Slowly two nervous enemy soldiers enter the kill zone looking left to right; they were the point element for a much larger main force that is was attempting to avoid contact. The noise was defining as the claymores exploded sending hundreds of steel balls into the kill zone. The thunder continues with bursts of small arms fire punctuated by the thud of SMAW-D rounds that could felt as much as heard. Tens of thousands of dollars of ammunition expended in less than a minute. Hearing the ambush the enemy main force melts back into the woods and moves to an alternate route ultimately reaching its destination 2 hours later than planned. Friendly units report successful disruption of enemy movement and death of an HVI Corporal Joe Snuffy leader of a four man 'Direct Action Cell' and one associate. Another overwhelming success achieved the unit goes back to its base.
The above is the conventional equivalent of our counterinsurgency targeting methodology. Technically speaking the enemy force was 'Disrupted'. However, the friendly forces actions prevent its ability to deliver a decisive blow. In short, by constantly, attacking the first available target the enemy force is never ‘Defeated’.
Why Defeat
Clearly defining operational terminology is fundamental and due to the lack of proper terminology usage across the US military, I will take a second to create a common understanding. Of the terms most commonly misused, "Clear" and "Disrupt" are the most applicable to this concept. Both "Clear" and "Disrupt" mean more than showing up in an area for a few hours. They actually mean:
"Clear – A tactical mission task that requires the commander to remove all enemy forces and eliminate organized resistance within an assigned area."[i]
"Disrupt – A tactical mission task in which a commander integrates direct and indirect fires, terrain, and obstacles to upset an enemy’s formation or tempo, interrupt his timetable, or cause his forces to commit prematurely or attack in piecemeal fashion."[ii]
The major point to take away from these definitions is neither of these terms has a long-term effect. If you place your hand in one side of a bucket of water and move it as fast as you can to the other side, you have "Cleared" and "Disrupted" the water. However, the bucket is still full of water.
To win The Global War on Terrorism (GWOT), you must Defeat, Neutralize, or Destroy the enemy. Destroy is not appropriate in this conflict because it is focused on the major end items and personnel of your enemy not the psychological aspects of a ideology.[iii] However, the tasks “Neutralize” and “Defeat” are very appropriate with “Defeat” being the most suitable for the desired endstate.
"Neutralize – (Army) A tactical mission task that results in rendering enemy personnel or materiel incapable of interfering with a particular operation."[iv]
"Defeat – A tactical mission task that occurs when an enemy force has temporarily or permanently lost the physical means or the will to fight. The defeated force’s commander is unwilling or unable to pursue his adopted course of action, thereby yielding to the friendly commander’s will, and can no longer interfere to a significant degree with the actions of friendly forces. Defeat can result from the use of force or the threat of its use."[v]
The concept of treating the GJM as a super infection combines LOO/Es with the desired endstate of defeating the GJM, not just disrupting it. Whereas our current methodology over the last decade plus has been focused on disruption via what is commonly refered to as 'Whack-A-Mol'.[vi] A key component to the defeat methodology is the network focused LOO that uses operational patience to strike only when needed until the conditions are set to defeat the VEO in either its entirety or within a given a theater of operations.
Current Operations
The two prevalent targeting methodologies are D3A and F3EAD. In theory, they are supposed to be applied in a continuous circle that provides for consecutive operations by using the intelligence gathered during a previous operation see Figure 1.
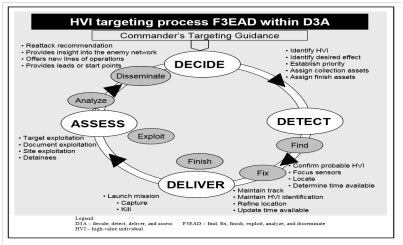
Figure 1. High-Value Individual Targeting Process[vii]
For most units, this is not possible. The highly centralized command and control mechanisms used in the various theaters does not allow for this. For the vast majority of units after a mission is conducted an entirely new mission must be approved. Therefore, there is no ability to conduct strikes in a rapid sequence, and the most immediately exploitable intelligence often passes its latest time of intelligence value. As a result D3A and F3EAD going from being a circle to, at best, a series of contiguous line segments as represented in Figure 2.
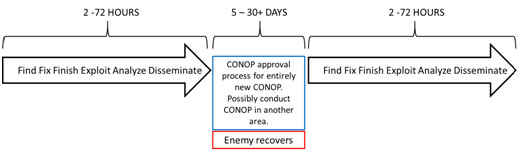
Figure 2. Normal Operations Timeline
Thus even if the operation did disrupt the VEO, it has recovered by the time another operation occurs. Conducting operations in this way allows a VEO to accept disruption as a regular part of doing business and therefore it is not truly disruptive.
Super Infection Targeting Methodology
To review, the overall concept is to treat the GJM as a super infection. The concept consists of three LOEs and two LOOs see Figure 3. The three LOEs are predominantly nonlethal with the purpose of preventing the spread and acceptance of the GJM ideology. This infect inoculates a population within an area isolating the targeted VEO from popular support. Then there are two LOOs, one of which focuses on the cyber domain and the other predominantly on kinetic operations. This kinetic LOO is called the Inverse Darwinist Line of Operations (IDLOO). The purpose of IDLOO is to de-evolve a VEO's resistance to COIN operations by conducting lethal and non-lethal operations in a manner that causes the organization to promote leadership that is less competent, less aggressive, possess less OPSEC, and is less capable at Information Operations.
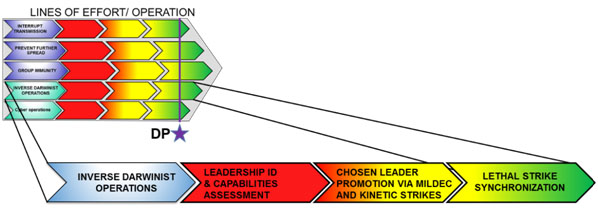
Figure 3. LOEs and LOOs Concept
IDLOO uses known epidemic vaccination percentages as a reference to determine a decisive point. It has been proven that the spread of an epidemic can be arrested if you achieve an effective vaccination ratio of 96%.[viii] The important word is effective; this effect can be achieved by vaccinating 30% of the population.[ix] Due to the different command structures used by various groups, a hard number for all groups is not possible. However, as long as the key association nodes are targeted, and a loss of 30-50% of a VEO's leadership is achieved in rapid succession then the VEO will at least be forced back to the latent incipient phase where the other LOEs designed to reduce the ideological influence and local support will prevent its recovery.
This LOO is accomplished in three phases; leadership capabilities assessment, chosen leader promotion via MILDEC and kinetic strikes, and lethal strike synchronization. To prevent a ‘Whack-A-Mole’ style approach targets will only be struck as a form of immediate lifesaving defense or to assist in degrading the capabilities and capacity of the VEO’s leadership. The flow chart in Figure 4 demonstrates the decision flowchart for performing kinetic strikes.
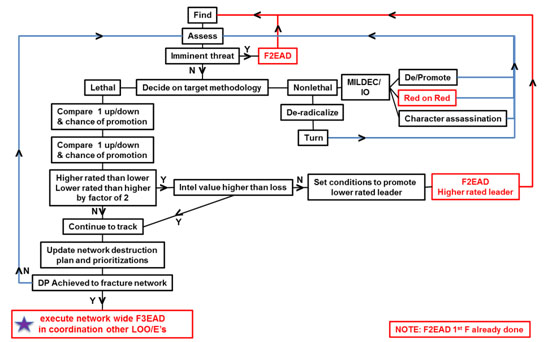
Figure 4. Targeting Flow Chart
Phase I: Leadership Capabilities Assessment
Phase I starts when a VEO is targeted for Defeat and ends after the full assessment of the target(s) and the immediate threat analysis is completed. Leadership capabilities assessments are a key component to this LOO. The steps are laid out in Figure 5. It is important to note that a target competence and position as a key node are more important than actual rank in the command structure. Once friendly forces identify a leader, the leader is rated on a scale of 1-10 with 10 extremely competent and aggressive and 1 being extremely incompetent or passive. After being placed in the link chart the importance of the target is based on its binding strength. If the target is critical to the linkage of various branches of a VEO, then the target is referred to as a key node (KN). Due to the carrying structures of different VEOs, an exact number of branches for a key node may be different.
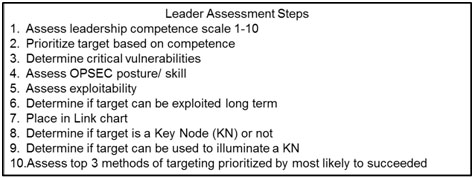
Figure 5. Leadership Assessment Steps
Phase II: Chosen Leader Promotion via MILDEC and Kinetic Strikes
Phase II starts after the immediate threat decision and ends with the decision to execute the network-wide synchronized kinetic operations. It is during this phase that the network analysis is compiled and the leadership of the VEO is degraded. Only limited strikes are conducted and only to facilitate the advancement of incompetent leadership. It is important to note that every strike conducted during this phase may prolong the time needed to achieve the Decisive Point (DP). The KNs are mapped out and a strike plan to take out as many of the KNs as possible as quickly as possible is developed. The targeting flow remains circular in nature with targets and plans being constantly reassesses. Red on Red fighting is promoted during this phase. Additionally, as the DP is approached and synchronized with the other LOO and LOEs, the massing of combat power may begin.
Phase III: Lethal Strike Synchronization
Phase III starts with the decision to execute network-wide synchronized kinetic operations and ends when VEO leadership network is Defeated. Final synchronization with the Cyber LOO and containment LOEs is conducted. Combat power is surged to the theater. A key component of this phase is a shift from current C2 methodologies to a mission command methodology. The Higher command will synchronize target sequence, assign assets. Lower levels of command will finalize tactical plans with the assets assigned. After initiation of the sequence, release authorities are lowered to the GFC and follow-on targeting is approved by GFC’s next higher commander without using the current CONOP process. It is an essential task that operations not be slowed down by our current highly centralized command and control procedures.
The Inverse Darwinist Operations LOO is the kinetic arm of the concept. During most of the campaign, this LOO has a low operational tempo with just enough assets to conduct extremely limited strikes. Once the other LOOs and LOEs have reached the ability to prevent support from the populace and disrupt the communications and messaging of the targeted VEO, forces are surged. With KNs killed or captured, the VEO will be unable to coordinate operations. Continued strikes beyond the KNs will assist in making the VEO infrastructure unviable. At that point, it is up to the LOEs to prevent reconstitution of the VEO from the latent incipient phase.
End Notes
[i] U.S. Army, ADRP 1-02: Terms and Military Symbols, November 2016, 1-16.
[ii] U.S. Army, ADRP 1-02: Terms and Military Symbols, November 2016, 1-31.
[iii] Destroy also implies you will accomplish victory by attrition, something not appropriate for an ideology supported by a civilian population as well as a military force.
[iv] U.S. Army, ADRP 1-02: Terms and Military Symbols, November 2016, 1-67.
[v] U.S. Army, ADRP 1-02: Terms and Military Symbols, November 2016, 1-26.
[vi] Gordon Adams, Richard Sokolsky, “The Pitfalls of a Whack-a-Mole Strategy Against ISIS”, Foreign Policy, May 28, 2015, Accessed March 29, 2017, http://foreignpolicy.com/2015/05/28/the-pitfalls-of-a-whack-a-mole-strategy-against-isis/.; Bill Gertz, “For White House Counterterror Adviser, Media Attacks Are Latest Theater of Battle”, The Washington Free Beacon, February 27, 2017, Accessed March 29, 2017, http://freebeacon.com/national-security/white-house-counterterror-adviser-media-attacks-latest-theater-battle/; This is just two examples there are many more.
[vii] U.S. Army, FM 3-60: The Targeting Process, November 2010, B–2, Accessed March 29, 2017, http://www.globalsecurity.org/military/library/policy/army/fm/3-60/fm3-60.pdf.
[viii] Nicholas Christakis, "Nicholas Christakis: How social networks predict epidemics", Video file, 17:54, TED.com. Posted by TED@cannes, June 2010, Accessed August 29, 2016, http://www.ted.com/talks/nicholas_christakis_how_social_networks_predict....
[ix] Gary Slutkin, "Gary Slutkin: Let's Treat Violence Like a Contagious Disease", Video file, 14:08. TED.Com. Posted by TEDMED, April 2013, Accessed August 29, 2016, http://www.ted.com/talks/gary_slutkin_let_s_treat_violence_like_a_contag....
About the Author(s)
Comments
https://usaman.linkenonline…
https://usaman.linkenonline.nl/
https://forum.contentos.io/user/okcupid
https://chaturbate.com/external_link/?url=https://www.loveawake.com
https://ams.ceu.edu/optimal/optimal.php?url=https://bit.ly/3qAqaeW
https://www.justjaredjr.com/flagcomment.php?cl=10842755&el=https://bit.ly/3HeHhd0
Nope. Just a retired U.S. Army Senior NCO and Old Cold War and Vietnam veteran -- "calling 'em as I see 'em."
Herein to suggest that you consider my thoughts -- those of the U.S. State Department -- and indeed yours and those of your buddies -- more from the standpoint of whether these tend to:
a. Help the U.S./the West achieve its "expansionist" goal -- of transforming the outlying states and societies of the world more along modern western political, economic, social and value lines (many benefits to be derived thereby?) -- or tend to:
b. Hinder the U.S./the West from achieving its such strategic objective.
(It is from this "goal of the U.S./the West" strategic standpoint [containing and rolling back communism back-in-the-day; advancing market-democracy today], would you not agree, that you, I, and/or others must determine whether [a] someone's ideas tend to properly portray -- and thus help -- the U.S./the West achieve its strategic goals or [b] tend to mistakenly portray -- and, thus, potentially thwart/undermine -- the U.S./the West's such efforts. Yes?)
All,
Thank you for the debate I am sorry I did not get back on here sooner, but life is what it is. I sincerely appreciate your discussion points it is one of the reasons I like SWJ. The counter points are quick and sometimes decisive. I would like to take a moment to respond to a few of your points. Some of them I believe come from a misunderstanding of the methodology.
Bill C,
Roger the West is the evil doer and Islam has never had any intention of expanding its culture which may be, but should never be, considered by other "societies [as] more along alien and profane political, economic, social and value lines." However, back in reality, most cultures have attempted to expand their belief structures into new areas. This expansionist tendency is why Islam is not contained to only Western Saudi Arabia. It has also been expansionist in nature since its inception. I told somebody once that thought you might work for the US Dept. State or USAID sine they say almost the same things. The person pointed out you do not seem to like the communists either so probably not.
R. C. J. / Bill M
You are correct CT as a counterinsurgent strategy is a failure. However, that is not what this is. The targeting part is a small part of the overall concept. I attempted to note this with the author's note which included a link to the overall concept, Figure 3, and the summary. In accordance with Sun Tzu's teachings, it is my fault for not being clear enough. To keep with the firefighting metaphor you still have to deal with the smoke and have a plan to deal with it or the firefighter dies before the fire is extinguished. However, the superinfection name is not a simple metaphor. The overall concept follows the same concepts used to eliminate diseases such as Polio. For example, the cyber LOO is based off ideas like web crawling as a way to predict infectious outbreaks such as bird flu. However, this does include fighting the disease itself. This is the wound debridement/antibiotic part of the treatment. By itself, it is not effective in eliminating the disease, however, when tied into prevention of disease spread (the 3 LOEs in Figure 3) I believe it can be. The targeting methodology is modular and could be used in other types of conflicts but for it to be effective in a COIN fight the other parts need to be incorporated. The targeting part is not the foundation of the plan it is a supporting effort within it.
FYI, I like your idea of the categories of insurgencies and intend to look at that deeper in the future. Sounds like a possible article if you would care to expound upon it further.
Bill M
I think it is awesome that you were lucky enough to have seen a chain of command attempt to make a plan. In The Gamble Tom Ricks points out the lack of a campaign plan in Iraq. I have been in the military for the entire conflict, and the closest I have seen to a targeting plan is "Kill [Jihad group name]." Which of course meant that every commander that wanted to do missions played seven degrees of Kevin Bacon so they could target that group in places it had never been. Maybe you could PM me and let me know which unit did that so I can try to get more info on it.
You are correct, insurgents are well inside our OODA Loop, do not need a survey to get rid of bad leadership, and doctrine does need to be updated. I attempt to create a temporary OODA Loop parity during the execution phase by dictating lower approval levels and pointing out we would have to use mission command or even Auftragetaktic. Let them get rid of bad leaders. It saves us the time still creates dissent within their own ranks, makes them focus resources against themselves. Even better it shifts 'insurgent math' in our favor.
Insurgent math being when the US/ COIN force conducts a kinetic operation:
1 EKIA = ≥ 1 new insurgent
It follows then that if for example, the Taliban kill one of their own we should have a new sympathizer in that tribe.
1 Red on Red KIA = ≥ 1 new COIN force sympathizer
Doctrine should be revised. However, the point would be lost if I went on a tangent to recommend changes in doctrine and terminology. Should LOO/Es be branched or even geometric as opposed to (L)iner are Decisive Points useful etc. would be a book in itself. Since this is a hobby of mine, I do not have the time although I do participate when possible in doctrine rewrites and have other articles in SWJ about recommendations on current TTPs being used.
I think you misunderstand the terminology argument. Because the overall mission is defeat does not mean every single unit has only that task. In theory, the DO of the DO of the DO, etc. does but every other unit can have any task including clear. The problem I am attempting to point out is EVERYONE is disrupting and clearing no one is assigned to defeat the enemy. I know of a couple of HQ that believe they are the DO in the GWOT all have some ambiguous you cannot prove I was unsuccessful mission statement. As previously noted all want to do kinetic ops one of them is in existence simply for that purpose.
As for metrics, I have a half finished article about not tracking real metrics, but that will have to wait for a while.
If I missed a point let me know, I will attempt to address it. However, I think that hits the primary concerns.
Bill M...I would argue that actually Robert is very correct in his assumptions.....
If one truly takes the time to analyse the Syrian Sunni revolt against Assad from the very beginning to now 6.6.2017....in the past six years we have seen literally every aspect that Robert talks about...that analysis was not done using the smokescreen "who is moderate and who is radical" because if an analysis had been done senior decision makers would have been forced to accept they were wrong and who wants to admit that at their levels.
FSA had been fighting IS and AQ since they arrived in Syria and the only way to defeat both is via Sunnis themselves not the Kurds...and now we the US, CENTCOM and SOF have to defend why we are supporting, training and fighting together with a US named terrorist group the Communist led Kurdish PKK....that has a reputation for ethnic cleansing of Arabs..ie Sunnis.
And if one looks at how CENTCOM, SOF and WH have basically treated it as just one big CT event...Roberts comments are also valid in that there is nothing but tactical moves being made...nothing at the strategic level that would in the end defeat an IS and or AQ insurgency...and you are correct in that CT has totally failed...
BTW...the reason the UK is failing in their fight against IS is that they are treating it as if it is the IRA all over again...the IRA was never a terrorist org..them viewed themselves as being a political front with an armed wing to achieve their political goals..and we saw their recent strong election results but then a large Semtex bomb in a car was recently found as well so the Provos are still around and want a fight...old habits die hard it seems...
Sad to say what we are seeing now in UK is in fact an IS homeland led insurgency with first generational leadership that will evolve faster than UK security and police can keep up with...couple that with a heavy amount of UK returning IS combatants with combat experience ...the UK is headed for a rough decade....
UK is currently struggling because they are still in a CT mind set and have not shifted yet to a CUW mind set...
COL Jones: You said:
"... the success of communism was borne of the conditions of governance and the cultures of the populations it was directed upon."
So it appears that we agree that the advance of political, economic, social and value communism, in many parts of the world in the 20th Century, was a success. (At least until such time as the Soviets/the communists, under Gorbachev, decided that they needed to "mimic" the West; this, in order for the Soviet Union to continue to survive in the face of the advances being made by the Western world by that time? Bad decision by Gorbachev, as this such "mimicing" of the West would invalidate the very foundations upon which communism -- and the Soviet Union -- were based?)
As to this, apparently agreed upon, dramatic success -- of the advance of political, economic, social and value communism throughout most of the 20th Century and throughout much of the world back then -- you would seem to attribute this, as you note above, to the "conditions of governance and the cultures."
What I am noting is that COL Bjelajac, in his "Unconventional Warfare: American and Soviet Approaches" (provided by, referenced and linked by me above) would appear to suggest that -- all such things being equal -- the reason that the Soviet/communist succeeded, and the U.S./Western failed, was due to other factors; specifically, the very different approaches used by the Soviets/the communists -- very different approaches that COL Bjelajac takes great pains to carefully point out.
Thus, as COL Bjelajac appears to say -- all other things being equal -- the success of the Soviets/the communists, and the failure of the U.S./the West, this can be attributed:
a. Not to such things as the -- generally uniform/often the same -- "conditions of governance and cultures" that both the U.S./the West and the Soviets/the communists faced, but, rather,
b. To the -- decidedly different -- way that the Soviets/the communists (versus the U.S./the West) went about the job of attempting to transform outlying states and societies more along alien and profane political, economic, social and value lines.
Herein to suggest that COL Bjelajac's theory -- and the Soviets'/the communists' success story (and our failures) related to same -- these seem to, thus, call into question your "conditions of governance and cultures" thesis.
Thus, before we can give further consideration to your such "conditions of governance and cultures" theory, must we not -- first and foremost -- give due consideration to, and indeed significantly experiment as per, COL Bjelajac's -- apparently validated by history -- "different means, methods and approaches" thesis?
(This, before we can throw in the towel/honestly say or suggest that the "impose" job, post-WWII, cannot be done by the U.S./the West also?)
Bill C.
Ok, you have me at a loss. Where, pray tell, did the Soviets succeed?? Even Mother Russia herself, is no longer Soviet.
We need to appreciate that just because Lenin was the father of the use of a communist ideology to organize and direct the workers in Russian cities to stand up to the poor governance of the Czar, his efforts would never worked if the conditions of insurgency against the Czars were not high. The narrative of communism as applied by Lenin was carefully tailored to his target audience.
Mao tried to apply the Leninist approach by the book, and failed. The revolutionary energy Mao needed to target was in agricultural, rural communities, so he tailored the message to focus on land reform. Again, but for the high conditions of insurgency in these evolving populations, his message would have fallen on deaf ears. The Maoist approach also worked well with the agricultural rice cultures across South East Asia, where the dual drivers of resistance (warfare) insurgency against Imperial powers of Europe, Japan and the US; coupled with revolutionary (illegal democracy) insurgency against the client regimes those imperial powers put in place; combined to make a ready pool insurgent energy to tap into.
In the Middle East there is no population of oppressed industrial workers or tenant farmers. Communism fell flat as an insurgent ideology when attempted in the Middle East for this reason. Among populations where every aspect of life and governance is shaped by their Islamic religion, what other ideology would a aspiring leader of an insurgent group, or head of a UW campaign possible select? It is the only narrative that could work, and to challenge the status quo one must put a spin on that narrative that is "radical" in that it must take a line that the government is either unwilling or unable to adopt.
So no, the success of communism was borne of the conditions of governance and the cultures of the populations it was directed upon. So too with the success of Islamism in the Middle East. Of note, it is hard to find a "radical" communist country these days. These things tend to moderate with time. Who thinks of Euro Protestants as radicals these days?? We will see moderation in the Middle East as well. But why go there at all? Why ignore the reasonable needs of evolving populations just because we abhor the messages and tactics of those who seek to exploit them?? History tells us Kings do not respond well to rises on popular power. History also tells us that those Kings ultimately more often than not die horrible deaths at the hands of their own people. Governance must get in front of this, or governance will shatter.
There is no "win" in military action, only suppress. The role of the military is primarily to create time and space for civil authorities to understand what the true needs of the people are and to make the necessary, reasonable adjustments of governance; and to disrupt and mitigate the high end of violence.
This is not a revision of the facts of history, this is a refreshment of how we interpret the facts more for what actually occurred, rather than how we perceived it at the time.
Best, Bob
From COL Jones - June 4, 2017 - 8:49am comment/thought below:
BEGIN QUOTE
1. I don't believe that it has been feasible in the post WWII era to impose ones's will onto a weaker nation and force/bribe a population to accept the government you are really building for yourself, but imposing on them, to accept as having the right to govern them. These governments are not possessed of popular legitimacy. So what we set out to do in Vietnam, Afghanistan and Iraq was infeasible by strategic design at the policy level, and that therefore no amount or form of military, diplomacy or development effort could have ever made them work. They were hard broke from the top down, and could/cannot be fixed from the bottom up. I think Bill still believes that the right efforts done well could make this work.
END QUOTE
Reflecting on the (highly successful?) "expansionist" efforts and designs of the Soviets/the communists post-WWII, can we say that COL Jones may have gotten this wrong?
Herein to ask, during the Old Cold War; wherein, the Soviets/the communists, like the U.S./the West today, faced similar state and non-state actor enemies/obstacles,
a. Why were the Soviets/the communists largely successful back then and
b. Why is the U.S./the West largely unsuccessful -- then and now?
The answer to this question might be found in the following analysis of (a) the larger and more entailed commitment of the Soviets/the communists to this "expansionist"/"transformational" enterprise and/or, more importantly, (b) the often "grass roots"/"prepare the ground first" approach to unconventional warfare the Soviets/the communists used in the service of same?
BEGIN QUOTES
The offensive employment of unconventional warfare -- to extend political and strategic positions -- has been almost solely the weapon of the Sino-Soviet bloc in the Cold War. The Communists follow a pattern of active and aggressive promotion of their goals, while the United States and allied countries have used unconventional warfare primarily for the protection and safeguarding of their interests. ...
Among the techniques used to implement revolutionary warfare strategy and to attain their goals, the selection of cadre, organization, deification of the masses and psychological impregnation are the most important. Leaders, speakers, propagandists, activities, organizers, officers, volunteers and others are trained. Revolutionary cells are established to control different circles and organized groups in all sections of society. Parallel communists hierarchies are organized starting with the cell of a local committee to the central communist party. This becomes the party's invisible machine by which unions, sport, and cultural associations, veteran societies and others are controlled. The conflict embraces all segments and groups of society and, in fact, is concerned with every single aspect of social activity. It is and must be a fight for the minds of the people. That side which is victorious in this aspect of the struggle is virtually assured ultimate victory.
END QUOTES
https://www.jstor.org/stable/1034145?seq=1#page_scan_tab_contents
Bottom Line Thought:
Thus, re: our similar goal of outlying state and societal transformations today: If:
a. We wish to become the (highly successful?) "pandemic super-infection" that the Soviets/the communists were back in the Old Cold War, then
b. Must we (a) consider making a similar commitment as the Soviets/the communists did back then and, accordingly, (b) consider employing our WOG assets (think: COL Jones' "military, diplomacy or development efforts") more as the Soviets/the communists did back-in-the-day?
(This, before we can throw in the towel/honestly say or suggest that such an "impose" job [see COL Jones' thought above], post-WWII, cannot be done by the U.S./the West also?)
Seems to me the missing ingredient overall is thinking, especially at Happy Command where group think tends to dominate. We now have SOF politically correct solutions to problems that are not solutions, but few willing to challenge the prevailing beliefs whether it is network theory related to HVIs, or the empty statement of by, with, and through. If you're promoting the same failed HVI focus strategy through partners, you are still embracing a failed strategy.
Specifically your comments,
Quote, "I suspect Bill is more comfortable with the historic perspective captured in doctrine (for now...), but I think we missed the distinctions in the nature of these two forms of population-based political conflict in the past due to the ability to suppress either or both through the application of state power".
If you read my thesis you would realize I'm not at all comfortable relying upon historical perspectives that may or may not be captured in doctrine. The world has changed too much to rely totally upon legacy lessons; however, history is still important. To clarify I believe the new builds upon and layers over the old. The old is still there, so yes a study of history is certainly necessary if one wants to develop a strategy nested in reality. Perhaps the key difference between a strategist and a historian is the strategist must understand how we evolved to this point in time, then project where the trend is going, and then propose ways to shape that trend in a way that benefits our national interests. Change is constant, so we must not fall in love with our strategy and supporting plans.
Regarding your thoughts on internal revolutions and resistance, the reality is that it is increasingly a blend of these types of conflict that confound our efforts. Afghanistan is both internal (numerous actors defying government control) and there are numerous external actors leveraging the various internal actors. Collectively the simplistic approach of winning hearts and minds (at least the way we do it) is a road to nowhere. The competitive control theory is the most apt in this situation and in many other conflicts around the globe, but we don't seem to have the intellectual capacity to grasp what that means.
To your first point about our inability to impose our will on a nation or people you may be right, but that is due to our naïve belief based on the neo-conservative philosophy that got us into Iraq to begin with. If we just "establish" a democracy and free market, then everything else will fall in place. We never attempted to establish control, instead we removed all elements of control leading to a chaos that was beyond our limited means to control. Then we responded with a targeting strategy that missed the larger picture, and only made the situation worse. We still cling to that same strategy.
You may be right about "our" inability to impose control, but it is not because we don't have the means, we simply don't have the ways and the will (yes will is a means, but by the first use of means I meant tangible means). Other states and non-state actors have successfully imposed their will to control their populations, especially after WWII. Mao, Stalin (and his successors), Tito, the Taliban, Assad, etc. In all cases there were tensions that had to be constantly suppressed. Some actors imposed more force and information control than others to maintain control because they system they imposed was not seen as legitimate. I am not making a case we should do this, but simply calling your argument that it can't be done into question. We should have at least established martial law and put in an authoritarian government in place with the long term goal of evolving that government into a more legitimate form of government after control is established. Is this feasible? I'm not sure, but I know our current approach is not working.
Bill and Outlaw, good comments, and as this is an important discussion I will expand a bit.
First, I realize I was a bit pithy in my initial post. I stand by everything I said, but the tone reflects the frustration of being a strategist in a 4-star tactical headquarters. (No, people, level of command, and breadth of operations do not automatically bestow "strategic" on what one does or how one thinks, any more than having some variation of the word "strategy" in ones's title, duty description, or project).
Second, I'd like to highlight the areas where I perceive that I diverge from Bill on this. Perhaps the greatest reason for the divergence is that Bill grew up in the community as a thinking operator. I grew up in the same community as a thinker who has operated. The distinction is an important one, as it colors our perspectives and we both recognize the balancing effect it plays.
1. I don't believe that it has been feasible in the post WWII era to impose ones's will onto a weaker nation and force/bribe a population to accept the government you are really building for yourself, but imposing on them, to accept as having the right to govern them. These governments are not ossessed of popular legitimacy. So what we set out to do in Vietnam, Afghanistan and Iraq was infeasible by strategic design at the policy level, and that therefore no amount or form of military, diplomacy or development effort could have ever made them work. They were hard broke from the top down, and could/cannot be fixed from the bottom up. I think Bill still believes that the right efforts done well could make this work.
2. I have come to believe that there are really only two broad categories of insurgency. Revolutionary (within) and Resistance (between). By nature, the first is any effort by a segment of a population to seek to coerce change on their own government through illegal means. Key words being "internal" and ""illegal." This may be peaceful or very violent, and is best thought of as Illegal Democracy, and not as some irregular form of war. Resistance, on the other hand, is a continuation of warfare between a segment of some population and some external occupying power. Clausewitz applies, and one must defeat a population equally to their government and their military if on is to stay and impose their will upon them. This is the essence of the American Way of War. Both are most accurately thought of as lines of motivation, and often exist in varying degrees within the same space and within the same individuals. Both require very different solutions, so success demands that the distinction be made at the very top and incorporated into the policies and strategies shaping the campaign.
I suspect Bill is more comfortable with the historic perspective captured in doctrine (for now...), but I think we missed the distinctions in the nature of these two forms of population-based political conflict in the past due to the ability to suppress either or both through the application of state power. We call a decade or two of suppression a "win" and repeat as necessary. I believe that the relative shift in power from governments to the governed has rendered this historic approach and perspective obsolete. Britain recognized this (grudgingly) in places like Kenya, Malaya, India, and Northern Ireland. We in the US, however, still believe we are both "exceptional " enough and powerful enough to make it work. We are wrong.
For those interested, I wrote a chapter on this that is embedded in the latest publication by the Strategic Multi-layer Assessment SMA team on Human Geography that explains this in greater detail.
Bob
Bill provides an interesting insight into the simple fact we as a country and military have apparently not "learned from history"....
In Europe during the terror days from the mid 60s to the end of the mid 80s...Europeans would target the leaders of RAF, Red Brigades, 2 June, the Greek ultra leftists and Carlos.....all going after leadership of these groups...
What was the learned lesson and what then did the Europeans as a whole do....
1. with each elimination of a leadership level, more just bubbled up and say with RAF they reached a fourth generation of leaders..which each generation learning what got the previous group killed and or captured thus the structure became very adaptive at surviving and learning from the CUW.
2. then after this realization the CUW forces mainly state security and police went after "structure".....money, safe houses and modes of movement AND most of all the the "verbal and not so verbal secondary supporters....
Referring to Operation Phoenix....while badly beaten up politically by those in the left side of US politics and US MSM....as one who worked that program...yes there were excessive abuses initially but on the SVN side, but US SF/CIA advisors got that under control and in my particular area that consisted of vast rubber plantations and tens of vocal villages that had been the backbone of VC taxation and political cadre system of NVN political control.... within 1.5 years of focused targeting built on an extensive intel network we eliminated that infrastruture...
We on the intel side got to the point we could pinpoint every newly recruited member of the VC down to hut number and village....only when you reach that level can one effectively counter an UW movement.
Yet when even reaching this level in a UW fight it was doomed as the SVN government never made the necessary strategic political and economical moves needed to support the tactical gains being made on the ground...AND the then US government leadership and senior military leadership "never understood UW"....AND the US government reps and senior US military leaders in Saigon never assisted the SVN government in getting that point across....
In SVN at that time US military senior leadership was more interested on the appearance of what SF soldiers looked like while in Saigon in their own compound and were totally distrustful of SF/CIA relations...or whether SF was armed and on the streets of Saigon when US military could not be armed....
"Appearance" over effectiveness....was the senior leadership mantra....
I was excited by the title, but the article itself didn't cover any new ground. It was another attempt to promote targeting as the answer to our woes. Then it artificially attempted to get conventional doctrine terms like defeat to conform to an unconventional war. As for the inverse Darwinism LOE, I have been in many planning groups where we discussed selecting targets with the hope of an incompetent moving into a leadership position. Overtime the impracticality of this approach became apparent for a number of reasons. Beyond our own knowledge limitations and ability to predictably shape adversary behavior our adversaries are also adaptive strategists who arguably have a more effective OODA loop than we do. If they are stuck under an incompetent leader they will either remove him, or form a splinter group. The author in some respects is demonstrating mirror analysis where we look at the adversary as a military organization much like ours where leaders are appointed and subordinates will blindly follow. That isn't how the real world works outside of the military or dictatorial governments.
More to the point, an operational approach or strategy founded on targeting will continue to fail us. One only needs to look at each area of the world where we actively pursue this targeting approach and simply look at the results. In each case the situation has gotten worse, in some cases considerably worse (Afghanistan, Yemen, Libya, etc.). Why educated officers blindly adhere to the empty concept of centers of gravity and then targeting its so called decisive points after this strategy is a proven failure still amazes me. We do assessments, and we identify we're failing, and yet we still pursue the same template approach. Commanders want more forces so they do more of the same, while missing key opportunities to shape the environment strategically to actually make a difference in a way that is not only more effective, but also sustainable.
Bob's comments below are right, our metrics need to change. We probably won't agree on what the metrics should be, but we'll agree that the current approach is self-defeating. Contrary to Thomas' point that the task to clear only achieves temporary effects, in a counterinsurgency it is a critical tactical task that can lead to strategic effects over time (many variables come into play after an area is cleared to include effective governance). Conducting a targeting campaign without effectively clearing areas and then controlling them is exactly what we have been doing for over 15 years to no discernible end. It is similar to the failed operational design Westmoreland used in Vietnam where our forces mostly pursued a seek and destroy strategy (a body count metric, and we do the same thing today, but focus on so called HVIs). In Vietnam, the communist actually retained political control of most areas despite our tactical clearing operations because the military didn't understand what a UW infrastructure looked like. Some of the most important people in UW don't carry weapons, they carry and spread ideas (that is the super-infection, one that can't be treated with traditional targeting). As pointed out by observers who could see past the hype in Vietnam, we would build the schools, then the communists would appoint the teachers. Fortunately, the CIA and SOF understood it, and Operation Phoenix while much maligned was actually one of the more effective programs during the war, since it focused on destroying VC political infrastructure. That should have been the main effort, unfortunately the vast destruction committed by the conventional forces and the failure of the RVN government to reform simply fed the communist narrative.
Until we gain a true understanding of unconventional warfare as a nation, not just in U.S. Special Forces, which managed to dumb down UW to a structural issue (underground, auxiliary, and guerrillas) to coerce in doctrine, we will continue to throw good money after bad. The Russians, the Chinese, and the Islamic VEOs all have simple yet sophisticated strategies to advance their interests based on today's operational environment. We have one model for the whole world, project force, target their military forces, and maybe do some inefficient economic development as a parallel effort. We can do better.
Robert..liked the response...BUT you are starting to write like a late 60s revoluntionary.....but keep on writing this....
Maybe at some point in time people will begin to actually "see and understand" that this is the only way forward in a truly complex 21st century.
If one really does look closely at the areas under control of say the FSA in Syria...a lot of what you are writing about is actually being implemented...local solutions tied to local culture, tribes and what they understand they want their form of "democracy" to look and feel like...and there is absolutely nothing wrong with that....and of all surprises it includes a hefty involvement of women....
BUT in the CT fight against IS WE the US have sided with and actively support a US named Communist Kurdish terrorist group that takes over Arab land using US arms, training and CAS and never gives it back causing more of a conflict in the coming decade....with the US smack in the middle of that conflict as we have "taken sides with a terrorist group"....does this make sense to anyone outside of DC and CENTCOM....???
Many do not fully understand that if your thinking was implemented US standing in the eyes of a lot of the world would rise 5 notches as they would see a US that is not trying to impose its will or values but a nation state that really does want them to succeed for as they succeed the US would succeed long term...and the number of conflicts we are current involved in might actually decrease...
First, CT is a failed strategy. Not because we lack adequate permissions, or ISR, or larger areas of operation, or effective intel or C2, CT is a failed strategy because it is inherently not strategic. It is a simplistic, reactive approach that by design allows one's opponent to control the tempo and location of operations; and that targets symptoms in a manner that makes the underlying problems worse. We bundle actors by how they are superficially similar to facilitate targeting, rather than separating them by how they are strategically unique to facilitate sophisticated, tailored approaches that could be done at the fraction of current costs and optempo, while being far more conducive to our strategic goals.
What's not to like? Well, it demands that we give up the cold comfort of first order thinking, objective, immediate metrics of "success," and admit that the past 15 years have been foolish and counterproductive. It would require us to distinguish between revolutionaries and UW operatives; it would require us to prioritize the advancement of US interests over the preservation of specific regimes; and it would require us to give up our dream of making others a lesser version of ourselves, and instead perhaps help them a bit to become better versions of their own selves. It would require us to stop pushing Western values and Western perspectives on democracy, and to instead advocate for culturally appropriate government that is more inclusive and self-determined that what currently exists. Finally, it demands we understand the world for what it actually is, rather than rail against it in efforts to make it what we want it to be.
CT is first order thinking applied to a higher order problem.
CT is like firemen adopting a strategy designed to defeat smoke, as it is the greatest killer, and to defeat flame, as it does the most damage; rather than following a strategy of separating the fusion of fuel, heat and oxygen necessary for fire to exist, while mitigating those two dangerous symptoms listed above.
Publishing a better way to do CT is like publishing a better way to punch yourself in the balls. Is better really, better?
It is time, past time, to adopt better strategic approaches based on the nature of the challenges we face, rather than designed to react to the symptoms of the challenges we face. AQ for the past 20 years has implemented a UW strategy. ISIS has, for the past 5 years implemented a UW strategy. Isn't it about time the CT crowed got curious about what exactly UW is, and how to effectively counter it? But those who advocate UW are relegated to the corners, while the ball punchers move ahead. Until this changes, we are doomed to reactive approaches that only advance individual careers, and not the interests of the United States of America.
Question:
If certain efforts made by both great nations and small, and by both state and non-state actors, can properly be described as "resistance movements" -- such as in the Old Cold War of yesterday and with the Rest of the World's resistance efforts versus Soviet/communist attempts to "transform" them back then --
Then can an argument be made that, in circumstances such as these, the Rest of the World's such efforts -- given that they are, uniformly it would seem, "resistant" and "defensive" in nature -- that these such efforts cannot be properly identified with, and/or characterized as, a "pandemic super-infection?"
This such characterization/identification/role (to wit: that of a pandemic super-infection) properly applying -- in cases such as that noted above -- to those great nations (the Soviets/the communists in the Old Cold War) who attempt to "transform" the Rest of the World more along alien and profane political, economic, social and value lines?
Bottom Line Question:
If, during the Old Cold War, the Sino-Soviets had -- in spite of the logic offered here -- adopted the author's suggested (a) THEY (the Rest of the World) are the "pandemic super-infection" and (b) WE (in this case, the Sino-Soviets) are the "resistance movements" thesis back-in-the-day -- and had proceeded along our author's suggested approaches accordingly --
Then would this have allowed that the Sino-Soviets, back then, would have, more easily, more quickly and/or more effectively,
a. Overcome the Rest of the World's "resistance to transformation" efforts back-in-the-day. And provided that, in spite of same,
b. The Rest of the World would have been transformed -- against its will -- more along alien and profane communist political, economic, social and value lines anyway?
(If so, then maybe the U.S./the West should [a] take such a tact and [b] attempt such approaches today?)

