Transforming DoD Information Technology Through Coalition Partner Trust
Ron Iammartino, Gary Whelan, Todd Doherty, Grant Hume, John M. Fossaceca and Jeff Forry
“We must continue to pursue technological interoperability with our allies at all levels, from the strategic to the tactical. Just as important, we need to enhance the human dimension of interoperability through combined exercises that test shared doctrine and refine operating concepts so we can fight seamlessly with our allies”
-- General Joseph F. Dunford, Chairman of the Joint Chiefs of Staff, 2017[1]
A proliferation of information technology (IT) advances have disrupted the modern world, which has accelerated the pace of change and expanded the body of knowledge in nearly every human endeavor. Previously isolated events now have near immediate, pervasive effects for militaries, politics, and cultures worldwide. The implications of these changing conditions are perhaps most applicable to how the Chairman has expressed the criticality of global integration for military operations across Combatant Commands (CCMDs) and Areas of Responsibility (AORs). Together with the Secretary of Defense, the Chairman has emphasized the importance of coordinating with and reassuring allies as essential to this effort. Mission partner integration not only serves to enhance alliance power projection, but also acts as an IT stress test for the level of trust necessary to meet the Joint Force’s demand signal for seamless, worldwide operations.
To support the fight against complex trans-regional threats, Department of Defense (DoD) network transformation requires a deliberate shift from hierarchical control to enabling faster IT decision-rules in a way that amplifies the best IT standards across the enterprise. This suggests a fundamental change to how we think about trust in enterprise IT strategy. As it stands, today’s Joint Force’s need for operational convergence is met by disparate efforts to improve upon a legacy IT infrastructure that has previously been characterized by distributing capabilities for unilaterally-focused, isolated CCMD AORs. IT systems, people, and resources had been iteratively developed for clearly defined communities of interest (COIs) in alignment with AOR-specific threats. Taken altogether, these factors have resulted in networks that are dogged by fractured security and policy considerations, thus limiting standardization and operational user community understanding and trust.
CCMDs have reported that top-down enterprise IT solutions do not appropriately balance the confluence between autonomy and enterprise-wide mission support capacity. Policy and security constraints applied independently across multiple Command, Control, Communications, Computers Intelligence, Surveillance, and Reconnaissance (C4ISR) systems and Defense networks, which sometimes lack a commonly understood view of mission risk, intent, and diversity in CCMD or Component mission-sets, has compounded this perceived lack of autonomy and trust.
Defense networks, represented in the DoD as a network of networks, must be able to respond to the Chairman’s call for integration with simple, adaptable standards that ensure real-time information access across networks, CCMDs, and mission partners. The U.S. contribution to the Federated Mission Networking (FMN) construct is one way the Department seeks to achieve greater standardization for interoperability with allies and coalition members. However, this alone will not deliver the systems and C4ISR integration required. The DoD must continue to address enterprise IT scalability and flexibility vulnerabilities that have typically driven CCMDs to internal IT development. The limitations of the extreme alternative to enterprise IT – legacy, stove-piped AOR IT - is now more confining than ever, since there is an exponentially increasing need for globally connected information sharing and data. Varying defense network security controls restrict, segment, and slow IT systems integration; the enemy, on the other hand, has ubiquitous access to information and is comparatively unconstrained by data classification categorization, programmatic lifecycles, cyber-security risk assessments, or logical network isolation.
Here we assert that Five Eyes (FVEYs) interoperability could serve as a context to rigorously test, validate, and challenge how the Joint Force thinks about enterprise IT agility for enabling strategic unity of effort. With a global reach that encompasses every CCMD AOR, the FVEY nations are comprised of the diversity in systems, people, and IT processes needed to provide an adequate representation of the enterprise technical and policy standards needed for worldwide operational interoperability. Through stress testing FVEY systems’ integration, collaboration, and coordination, general enterprise system rules can emerge that might more effectively map information sharing onto intersecting global problem sets, while also paving the way for improved enterprise standardization in the future.
This article applies Complex Adaptive Systems (CAS) theory as a conceptual model for understanding enterprise warfighting IT requirements in today’s uncertain, interdependent threat environment through the context of FVEYs interoperability. CAS theory investigates the complex system relationships of a range of macro rules that influence dynamic change for locally interacting agents where outcomes are complicated and difficult to predict.[2] It examines how universal principles indirectly serve to impact local systems at the micro-level. CAS theory has been applied many times in the past to model how social and technical environmental rules influence self-organizing interactions within and across various types of systems.[3] As depicted in the figure below, CAS similarly implies that local interactions or events, such as in a CCMD AOR or theater, can have effects that change the wider system, thus creating enterprise-wide feedback loops from previously isolated cause-effect environments.
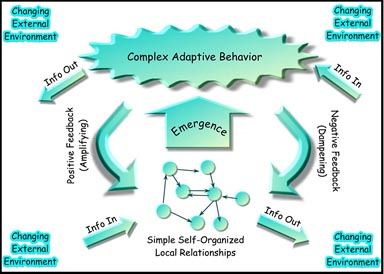
“Complex Adaptive Systems.”
Source: Stephen Johnson, “Emergence: The Connected Lives of Ants, Brains, Cities, and Software” (2001).
More pointedly, CAS theory offers a fresh perspective on the role of enterprise IT strategy in influencing first and second order effects when meeting integrated CCMD and AOR requirements. This construct can help military thinkers develop decision-rules and hypotheses for predicting outcomes based on AOR requirements that indirectly result from enterprise coordination or interactions as determined by mission, risk, historical precedent, and strategic intent.
This method factors into relevant interdisciplinary concepts such as behavioral economics-based theories on risk, decision-making, and tipping points.[4] From this lens, we can use CAS to assess how overlapping IT policy and governance from across the FVEY nations will interact to compel first and second order effects within AORs and CCMDs. Whereas IT operational flexibility requires responsive, tailorable, and coordinated change-management in real-time, this construct lends itself to the dynamic stressors of a rapidly changing world. For the CCMDs, this view might help commanders visualize, understand, and describe how a globally connected network of networks can be exploited for flatter and faster C4ISR systems incorporation with current operations.
To be clear, we do not intend to use CAS to present a prescriptive view on IT policy or to assess exhaustively how the warfighting community prioritizes requirements for command and control (C2) systems. Rather, we intend to demonstrate how a disciplined, principles-based CAS framework through a FVEYs context can help the DoD establish a common awareness of enterprise IT enabling decision-rules when faced with the challenges associated with decentralized, emergent information-sharing needs in multiple network domains. Drawing from the 1999 Federal Enterprise Architecture Framework principles, then intended to bring together legacy federal government networks, we aim to deliberately define relevant principles that account for the intricacies associated with the Joint Force IT power projection in the modern world.[5]
We propose a representative FVEYs stress test to stretch enterprise IT conceptual planning factors beyond the typical limits of national network boundaries. Though this test can be applied to a wide-range of mission partner types, the FVEYs represent a good illustrative use-case since each nation maintains sovereign IT policies and infrastructures yet aspires to an enduring, common approach for unity of effort across nations. We suggest that stress testing IT integration beyond nationally controlled authorities can serve as a model for validating the viability of IT systems across the full spectrum of warfighting - within and between CCMD AORs - while also providing the basis for incorporating broader mission partners. This thinking follows the logic that if enterprise decision-rules are stress tested against diverse FVEYs networks, particularly for enabling technologies, then CCMDs can develop network systems for local IT requirements faster and with greater efficiency since policies and procedures have addressed higher-level complexity multinational use cases.
The proposed CAS model assessment has three phases. First, we begin with a high-level view of the current DoD IT environment and the implications of technological advances in recent years, including cloud computing and commercially driven change. Next, we identify the specific policy and governance gaps associated with coordinating across five separate national IT strategic environments. Thirdly, the model applies hypothetical CAS theory principles to stress test practical use-cases with the intent to visualize the first and second order implications of DoD enabling IT systems across the enterprise. Our CAS assessment concludes with a snapshot of the current and future policy, technology, and operational employment gaps that must be resolved to support an interoperable and globally integrated IT enterprise.
Current IT Environment
The contemporary information environment is marked by rapid change and growth across platforms and technologies. IT has evolved to fuse data, voice, and video into a single protocol, thus enabling integrated information availability to commercial end-users at all times. The supporting software applications and systems march forward at a pace that, at times, overwhelms the DoD’s ability to assess, sort, and categorize data into usable components adequately.[6]
The DoD has a responsibility to propel IT modernization efforts, such as cloud computing, in order to ensure the U.S. maintains a technological advantage over the enemy. As highlighted in the 2018 National Defense Authorization Act, this necessitates a concerted effort with CCMDs and partners to be “less risk averse” while simultaneously slicing through bureaucracy to optimize and deliver faster, more seamless information sharing.[7]
In this vein, commercially developed technological innovations have largely fueled IT system enhancements, which has swelled new and latent user demands. End-users expect data and systems to be available now. Hundreds – if not thousands – of widely accessible applications contribute to the extension of desktop computing to a range of mobile technologies, thus elevating expectations for mission data assimilation at all levels and phases of war. The widespread adoption of modern social media, mobile systems, and data analytics correspondingly proves that the use of cloud-based technologies like Artificial Intelligence (AI) and Big Data will continue to grow as an instrumental advantage in nearly any competitive endeavor, particularly warfare, where information dominance is most vital.
The reality of today’s operational environments requires us to pull together real-time IT solutions that use information to both influence and enact the operational commander’s campaign objectives and end state.[8] For the military-industrial complex, the challenges are two-fold: reliably integrating secure, usable data and technology that is scalable to existing platforms and ensuring flexibility for future iterations of changing user needs. Addressing this necessitates an agility and responsiveness that are not emblematic of large institutions or government-controlled technologies. These tasks are especially difficult when faced with the competitive pressures to maintain the pace of commercial, open-source technologies that enable the adversary to make, share, and exchange information without the boundaries of security, programmatic delivery timelines, or policy.
Policy and Governance
Policy-making effectiveness in the DoD, as with most other large governmental institutions, can be quickly dated by the pace of today’s data-driven operations. Higher-than-ever user expectations compressed decision-making cycles, and unprecedented access to large raw data sets represent significant hurdles to efficiently and effectively conduct relevant department-level policy analysis on the multitude of information sources available.
Hierarchical DoD policy directives, for example, include bureaucratic staffing processes that can inadvertently filter, slow, delay, or misinterpret intents for IT implementation in support operations. This is especially true for the most complicated, and often times most urgent, systems integration requirements at the edges of our networks and policies, such as in accommodating coalition interoperability or account provisioning as part of a Combined Joint Task Force (CJTF). These factors can contribute to resulting IT solutions that inject operational risk at the altar of rigid policy or cybersecurity controls without a fully informed appreciation of the operational problem(s) to be solved.[9]
Information asymmetries can similarly hamper governance through stakeholder board coordination, which can result in compromised IT policies that unintentionally tax a commander’s priorities of speed and mission risk. Boards may not appropriately weigh the AOR operational impact, decision-rule timeliness, and/or data when evaluating complex, distributed systems. Even worse, the shorter decision-making cycle involved in a data-driven, globally connected environment sets the conditions for board conveyances to be too late to provide the policy coverage with a wide enough scope to solve for the variance throughout the enterprise.[10]
Complex Adaptive Systems (CAS) and the FVEY Stress Test
Using the FVEYs as a case study, we explore a different way to interpret how the U.S. DoD, federal mission partners, and respective FVEY Defense departments interact at the network edges. We scrutinize how the edges can influence information sharing norms in that both policy-makers and IT managers must endure the heightened rigors of deciding upon how to integrate and stress national policies, investments, and trust frameworks through which systems enable multinational operations.
CAS theory implies that coordinating macro, rules-based principles for interoperability at the edges flattens the landscape to meet mutually supporting CCMD requirements around the globe more effectively. We further propose the potential for economies of scale in terms of more efficiently bridging gaps and combining lessons learned that might have previously resided solely within CCMD network boundaries. Even more, this construct can be extended to a strategy to influence technology adoption standards and processes for larger COIs that look to the FVEYs for coalition leadership in IT.
We propose five general areas for the application of CAS theory to stress test DoD enterprise IT standards within the context of FVEYs interoperability:
First, the FVEY nations should default to trust. The Chairman has referred to this concept as “cultivating a bias for sharing.”[11] This means the nations should consider a default to the widest possible releasable information sharing as a generally accepted rule for the instrumentation of trust.
Codifying a default position on information exchange to, from, and across the FVEYs could set the conditions for warfighters to have quicker access to information resources at the critical point of decision. Elements such as classification labels, email filter rules, access controls, and foreign disclosure should be evaluated, standardized, agreed upon early and updated often. Once agreed upon, decision-rules must be automated, tested during combined-joint exercises, and normalized where feasible. This can create the basis for generating effects that establish a responsive information availability baseline to make policy and governance hurdles less formidable in the face of urgent needs isolated to specific AOR or CCMDs.
One practical mechanism to generate an enterprise-wide feedback loop for increased trust is to target federated identity and access management (IDAM) controls across nations; a shared identity-based infrastructure can both advance accountability and automate information release decisions in a timeframe that keeps with the pace of operations. It also bolsters operational community trust through pre-committing to standards-based information protection and access assurance levels, such as Public Key Infrastructure token-based authentication. This, in-turn, eliminates delays due to ambiguity for systems and data protection standards when time-sensitive, decentralized accounts and trusted access are most critical.
Digital identity trust, as in other domains, cannot be assumed as intrinsic to the partnership relationship. It should be conditions-based and shaped by the things partners do to help cultivate trust. Sharing a bias to trust through shared strategy and IDAM procedural controls is central to this viewpoint. Past conflicts have proven that we cannot comprehensively forecast our information sharing requirements, but sharing firm identity standards for network data access puts the foundation in place for better responsiveness when unexpected information exchange or release needs arise.
Another important way to cultivate a bias towards trust is through establishing a shared cloud infrastructure at the enterprise level. The FVEYs should specifically move together on a cloud-based approach for sharing the right Command and Control (C2)/Common Operational Picture (COP) data and applications to the right users at the right time. C2/COP datasets often cut across security domains, service providers, and mission types, and the governance for these types of data is uneven. Oftentimes, AOR or CCMD requirements arise for ad-hoc mission purposes, temporary solutions are developed, and robust, enduring fixes are engineered “in-flight” or not-at-all. The FVEYs might address these systemic issues through a cloud-based standard or threshold for C2/COP data that can be institutionalized (and shared by default). This means establishing a baseline for user volume, mission sensitivity, cloud defense-in-depth, operational frequency, and cyber risk. Such benchmarks could help CCMDs detect mutually shared risk and prioritization of links, thereby enhancing enterprise resilience and more fully utilizing mission partner IT capacity for combined-joint operations.
A ‘default to the cloud’ principle can be readily actualized through multiple mediums to include interoperability exercises and IT architecture improvements. Bold Quest or Talisman Sabre, for instance, provide exercise platforms where partners can validate a target cloud architecture in a relatively low-risk environment. The heightened risk tolerance associated with these types of training or exercise networks can even afford the enterprise with derivative stress-test metrics for any number of variables, to include live network design and cybersecurity assessment.
In terms of architecture, Service Oriented Architecture (SOA) is a way to enable modularity for distributed networks and software types. It is not enough to share data. Artillery needs different data than Combat Air, which needs different information than Infantry or Intelligence. Flooding the COP is not the answer. Accordingly, the nations should move toward the development of a SOA for FMN/Joint Information Environment (JIE) and the Mission Partner Environment (MPE) in order to better incorporate shared cloud-based C2 data and applications across national network boundaries.
Third, the IT systems lifecycle must deliberately prioritize rigorous mission and user engagement to ensure networks are designed for how the current, and future, Joint Force fights; this should be underscored by clearly defined rules for mapping network types to mission types across CCMDs. Mission-set diversity should be aligned with commensurately diverse networks and risk tolerance levels. Strategic, Mission, and Intelligence-sharing network interoperability might be implemented more aptly at a local level when the high-level coordinating strategy accommodates quicker governance and decentralized decision-rules. The most prominent among these rules surrounds clarifying and categorizing the DoD’s and CCMD’s intent for information sharing across different types of network domains. Can the FVEYs agree on standing categories for matching networks to mission types and phase? Can the FVEYs establish rules for trust – in terms of both network and data sharing policy? Will specific network types be used for broader COIs while others are limited to more constrained administrative information sharing purposes?
Answering these questions at the enterprise-level could be paired with increased transparency and clarity on authoritative coordinating instructions for Joining, Membership, and Exiting Instructions (JMEI) across all network types and missions. For example, the current FMN strategy calls for continuous JMEI rehearsals, targeted technology deployments, and robust interoperability training. In particular, the DoD should emphasize the Coalition Interoperability Assurance and Validation (CIAV) guiding principles (Assurance and Validation, Trust, Interoperability, Tailorable, Flexible, Unique) for Mission-based Interoperability (MBI) as the generally accepted standard for JMEI rationalization across all types of Defense networks.
Systems development should correspondingly be stimulated and calibrated through an ongoing dialogue with operational users. The enterprise should direct straightforward end-user validation and instructions for employing the varied, and often scattered, mission interoperability enablers across the DoD. In the 2017 Joint Force survey of 500 network users conducted by the Joint Staff J6, for instance, more than 90% reported no knowledge of where to go to access “how-to” guides or help-desk procedures for core enterprise coalition information sharing tools; 80% reported a complete lack of awareness of any coalition information sharing technologies altogether.[12] One of the thorny issues with large enterprise IT is determining the appropriate-level of coordinating instructions and details to the user community. These survey findings underline the importance of translating IT systems development into clearly articulated mission tools as quickly as possible. The onus is on engineers and service providers to include operators in IT development processes early and often. In parallel, operators must also play an active role in clearly communicating user feedback at all phases of the lifecycle to ensure appropriate design. System development theory is insignificant without first validating mission alignment.
Fourth, the FVEYs should arrange for a cybersecurity risk framework to formalize common cybersecurity controls and standards. Akin to the U.S. DoD Cybersecurity Scorecard, for example, the FVEYs should hold each other accountable for reporting on basic cybersecurity hygiene standards, such as strong network authentication, removal of outdated software, implementing Host Based Systems Security (HBSS), network architecture vulnerabilities, and configuration management.[13] Extensive research on decision-making and risk judgment shows that access to validated, objective information is critical to overcoming intuitive risk decision-making bias, including anchoring or information availability preconceptions, when trying to assess the probability of uncertain events like cyber-intrusions effectively.[14] Codifying reporting standards represents a rules-based approach that can foster quicker, more accurate cyber risk decisions not only within the FVEYs but also as a driver for communicating a best-practices model and baseline (or requirement) for opt-in external mission partners in the future.
Within the context of military history, cyber-based effects are in the nascent years of employment in terms of contributing to military and national security aims. Along these lines, common cyber standards can reinforce enterprise systems intended to share information on cybersecurity events more widely. Stronger FVEY trust and IT network ties reflexively yield more accurate and objective information flows for enterprise IT decision-making. This helps prevent attribution error, which is a major factor when evaluating how sometimes opaque cyber risk assessments fit within the scope of overall mission risk.
In the long run, the totality of mission risk and IT system risk should be merged and weighted appropriately. As with other fields, decision-making related to complex systems can be slow, but IT or cyber events oftentimes happen fast. The DoD must continue to consolidate and transform how we deal with these inextricably linked risk factors to provide commanders with suitable decision points. One approach towards this end is to share tactics, techniques, and procedures (TTPs) for balancing traditional IT responsibilities for network defense with newer cyber operations. Those that defend the network should be nested with and cooperatively supporting of those that operate on the network. The interplay between network defense and cyber operations necessitates ongoing discourse across the breadth of warfighting functions, including operations, command, intelligence, Signal/IT, legal, and many more. Designing systems that center on the cross-functional, multinational development of ideas, TTPs, and risk management procedures is imperative for growing cyber as an actionable and relevant mission command enabler.[15][16]
Fifth, the FVEYs can apply CAS theory for flattening decision-making bodies and workforce structure across nations. This calls for aligning IT managers and engineers into operational warfighting forums and organizations more closely. Past research shows that the technical workforce – the types of workers and service-members that can enable IT rules-based principles – operate most effectively in decentralized organizational structures headed by operationally focused leadership.[17] Lesser bureaucracy between the operational community and IT service providers could help mitigate the already discussed Policy and Governance risks that detract from effectively delivered IT. These concepts additionally support the premise that technical workforce turnover is reduced and knowledge management correspondingly improves in environments characterized by decentralization and operationally focused leadership. [18]
Our methodology suggests that flatter organizational structures accommodate operationally focused senior-leader engagement on targeted, high priority efforts. IT project research shows that a project champion (defined here as senior leader endorsement for specific priority projects) results in a quicker, more effective delivery to end-users.[19] As Secretary Robert Gates conveyed in his 2014 memoir, senior leaders can guide accelerated changes through the DoD enterprise only through consistent, purposeful effort and a keen awareness of process complexities.[20] From this perspective, technical workers in flatter organizations have greater access to inform operational leaders who, in turn, can more readily drive top-down influence on projects and programs that have the potential for globally connected impacts.
Finally, we find it worth noting that the challenges associated with this model are real and non-trivial. Those close to the edge must have a deep understanding of the commander’s intent and mission risk while simultaneously being empowered to make well-versed course corrections on DoD networks. It assumes an ability to balance between top-down and bottom-up COIs for communicating and coordinating network activities. Decentralization for IT in the modern world requires that the network infrastructure must have the flexible capacity to disseminate large amounts of information quickly while also leaning hard towards emerging technologies and cybersecurity to deliver the right data at operations speed across networks and C4ISR platforms.
Conclusion
IT integration is difficult and complex. In this article, we have provided a new lens on enterprise IT through the application of a CAS approach, which couples coordinating rules-based interoperability with the emergent properties of a hub-spoke model for change. We showed that the FVEYs could represent a CAS federation construct for understanding how both internal (national) and external (broader mission partners) stakeholders can stress test systems across CCMDs and national network boundaries in an effort to strengthen standing trust.
Globalization and IT advances continue to disrupt military operations in all phases of conflict. Together with unprecedented access to data and technology, the increasingly interconnected world calls for more adaptive and agile IT delivery. Enormous changes in technology, policy, and IT delivery demands are particularly vulnerable to exploitation and competitive pressure from the enemy. IT transformation should include an ongoing dialogue on principles and decision rules for shaping the effects of technological change and trust at our network edges. Applying CAS theory could help in this effort.
End Notes
[1] General Joseph F. Dunford, “Allies and Partners Are Our Strategic Center of Gravity,” Joint Forces Quarterly 4, no. 87 (2017): 5.
[2] Surya D. Pathik, “Complexity and Adaptivity in Supply Networks: Building Supply Network Theory Using a Complex Adaptive Systems Perspective,” Decision Sciences 38, no. 4 (2007): 547-580.
[3] C. Macal & M.J. North, “Tutorial on Agent-based Modelling and Simulation,” Journal of Simulation 4, no. 3 (2010): 152-161.
[4] G. Barmpalias, R. Elwes, & Andy Lewis-Pye, “Tipping Points in 1-Dimensional Schelling Models with Switching Agents,” Journal of Statistical Physics 158 (2015): 806–852.
[5] U.S. Chief Information Officers Council. Federal Enterprise Architecture Framework Version 1.1, August 5th, 1999.
[6] C. Johnson, Elmo Wright, Jessica Bice, J. Almendarez and Linwood Creekmore, “Transforming Defense Analysis,” Joint Forces Quarterly 3, no. 79 (2017).
[7] Derrick B. Johnson, “The DoD Looks to get Aggressive about Cloud Adoption,” FCW, September 20, 2017, https://fcw.com/articles/2017/09/20/dod-cloud-adoption-risks.aspx.
[8] David Kilcullen, The Accidental Guerrilla – Fighting Small Wars in the Midst of a Big One (Oxford: Oxford University Press, 2009).
[9] Robert Gates, Duty: Memoirs of a Secretary at War (New York: Alfred J. Knopf, 2014).
[10] Ibid.
[11] Dunford, “Allies and Partners,” 5.
[12] This 2017 Joint Force Coalition Information sharing Survey was distributed to all Combatant Commands, Services, and Agencies by the Joint Staff J6. Results and details are available upon request to the authors.
[13] Billy Mitchell, “Pentagon Automating its Cyber Scorecard,” Fedscoop, 2017, https://www.fedscoop.com/pentagon-automating-cybersecurity-scorecard/.
[14] Amos Tversky & Daniel Kahneman, “Judgment under uncertainty: Heuristics and biases,” Science, (1974), 185(4157), 1124-1131
[15] U.S. Department of Defense. Department of Defense Cybersecurity Culture and Compliance Initiative (DC3I), October 2015.
[16] Ted Bowlds, John Fossaceca, and Ron Iammartino. Software obsolescence risk assessment approach using multicriteria decision‐making. Systems Engineering 21, (2018): 455–465.
[17] Ron Iammartino, John Bischoff, and Christopher Wiley, “The Relationship between Supervisor Ratio and Organizational Turnover: The Mediating & Moderating Effects of Engineers,” ASEM Engineering Management Journal 28, no. 4 (December 2016): 238-248.
[18] Ron Iammartino, John Bischoff, and Christopher Wiley, “Emergence in the U.S. Science, Technology, Engineering, & Mathematics (STEM) Workforce: An Agent-Based Model of Worker Attrition and Group Size in High-Density STEM Organizations,” Complex and Intelligent Systems Journal (Springer) 2, no. 1, (2016): 23-34.
[19] Markham, Green, & Basu. “Champions and Antagonists: Relationships with R&D Project Characteristics and Management,” Journal of Engineering and Technology Management (1991): 214-242.
