Towards a Cyber Leader Course Modeled on Army Ranger School
Gregory Conti, Michael Weigand, Ed Skoudis, David Raymond, Thomas Cook, and Todd Arnold
Since 1950, the U.S. Army Ranger School has garnered a well-earned reputation as one of the most demanding military schools in the world. Graduates have served with distinction in special operations units including the Ranger Regiment and Special Operations Command as well as line units throughout the Army. With the emergence of cyberspace as an operational domain and the critical shortage of technically and operationally competent cyber[i] leaders, the time has come to create a U.S. Army Cyber Leader Course of equal intensity, reputation, and similar duration,[ii] but focused on cyber operations (see Figure 1). This article presents a model for the creation of such a school, one that goes far beyond just a tough classroom experience by using tactical close-access missions as a core component. What we propose is unique, demanding, immersive, and fills a necessary gap in Army cyber leader development. This article is a condensed form of a more detailed analysis and description of the proposed Army Cyber Leader Course.[iii]

Figure 1: Cyber Tab. A Cyber Leader Course of similar duration and intensity to Ranger School, but tailored to cyber operations would help fill the critical shortage of technically and operationally competent cyber leaders.
We intend for this new Cyber Leader Course to be quickly recognized as the cyber operator's equivalent of Ranger School, much like the Sapper program has become the Engineer branch's 'Ranger School.' There is much to learn from Ranger School and other elite training programs that can inform a Cyber Leader Course. We face a critical shortage of qualified cyber leaders at all ranks and a demanding and rigorous Cyber Leader Course would develop the knowledge, skills, and abilities required of technically and operationally competent cyber leaders. A cadre of highly qualified cyber leaders is critical to the professionalization of the cyber career field, but the Army currently lacks a method for developing these leaders. While we propose the creation of an Army Cyber Leader Course, due to the inherently Joint nature of cyber operations, creation of a Joint, instead of Army-specific, school may be a logical follow-on step.
Related Work
In order to understand the need for a Cyber Leader Course, as well as to inform its design, it is important to understand the available spectrum of training options currently available. Many civilian training offerings are closely tied to industry certifications, including CompTIA’s A+, Network+, and Security+, the EC-Council’s Certified Ethical Hacker (CEH), ISC2’s Certified Information Systems Security Professional (CISSP), Black Hat Training[iv], KEYW[v], and Global Knowledge.[vi] Additionally, the SANS Institute offers training in foundational and advanced cyber skills as well as its “CyberCity” range, a miniaturized mock-up of a small city with real-world components, such as power distribution systems, where students interact with and observe the kinetic outcomes of their cyber operations activities (see Figure 2).[vii]

Figure 2: CyberCity is a small scale mock-up of a city, including its key underlying computing, networking, and critical infrastructure systems using real-world back-end components.[viii]
We envision CyberCity or a similar technology as a valuable part of a Cyber Leader Course, particularly if implemented as part of a full size, immersive training environment akin to the military’s use of Military Operations on Urban Terrain (MOUT) training areas for urban warfare training (Figure 3) and law enforcement’s use of realistic training environments such as the Federal Law Enforcement Training Center.[ix]
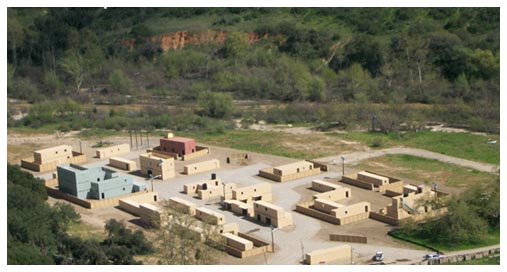
Figure 3: Military Operations on Urban Terrain (MOUT) environments could be integrated with the CyberCity concept to create an ideal training and evaluation environment for a Cyber Leader Course.[x]
In addition to civilian training courses, the military offers a range of cyber training, including the Joint Network Attack Course (JNAC) with topics including legal authorities, battle damage assessment, de-confliction, targeting, weaponization, and execution processes.[xi] NSA offers the System and Network Interdisciplinary Program (SNIP), which is a three-year program to train personnel in the technical areas of Computer Network Operations.[xii] Another example is the Joint Cyber Analysis Course (JCAC), designed to train junior and mid-level enlisted personnel for duty in computer network operations related billets.[xiii] In addition to these courses, NSA provides robust classroom and self-paced cyber training offerings through its National Cryptologic School and the Associate Directorate for Education and Training (ADET).
To help keep pace with requirements for trained cyber warriors, the Army is developing several new career specialties: Information Protection Technician Warrant Officer (255S),[xiv] Cyber Network Defender (25D),[xv] Cryptologic Network Warfare Specialist (35Q),[xvi] the Electronic Warfare Career Management Field (CMF 29),[xvii] and the emerging Security Systems Engineer (FA26C).[xviii] The training these Soldiers receive, combined with operational experience and dedicated commitment to self-development, is suitable preparation for our proposed Cyber Leader Course. Another example of military training is the Air Force Institute of Technology’s Advanced Cyber Education (ACE) program.[xix]
Contests conducted at hacker conferences offer useful insights into potential Cyber Leader Course training and evaluation activities, including Capture the Flag (force-on-force network warfare) competitions at conferences such as DEF CON, ShmooCon, and DerbyCon. Academic cyber security competitions also show great promise in teaching valuable skills, including the NSA-sponsored inter-service academy Cyber Defense Exercise (CDX),[xx] the National Collegiate Cyber Defense Competition (CCDC),[xxi] and the Capture the Flag, embedded systems, and forensics competitions hosted by NYU-Poly and other universities world-wide.[xxii] Furthermore, academic institutions offer cyber education programs from certificates and Associate's Degrees to PhDs. Colleges and universities with mature cyber security education programs will often seek accreditation as an NSA Center of Academic Excellence in Information Assurance or Cyber Operations.
The Cyber Leader Course we propose is a unique hybrid, one that draws upon the intense crucible of Ranger School, the rigor of high-end civilian and military security training and certifications, the realism of MOUT training, and the innovative competitions of the hacker community and academia, all while providing career-long educational principles and values that will make Cyber Leader Course graduates sought-after leaders in the cyber domain. The Cyber Leader Course will be much more than a synthesis of its parts and instead be a life-changing, even life-defining, experience.
“Cyber warriors are elite, trusted, precise, disciplined professionals who defend our networks, provide dominant effects in and through cyberspace, enable mission command, and ensure a decisive global advantage.” [xxiii]
- LTG Rhett Hernandez
Vision and Course Objectives
The vision of our Cyber Leader Course is to be the U.S. Army’s premier cyber leader development experience. Rigorous, challenging, and demanding, the course will be fully immersive; students will have only limited contact with the outside world and personal electronics and data will be prohibited. Graduates will possess:
- A sound understanding of the technical operation and dynamic nature of cyberspace.
- A warrior ethos - the ability to adapt, overcome, and fight through adversity to accomplish the mission.[xxiv]
- The ability to plan and execute cyber and cyber/kinetic military operations, including an understanding of how their actions fit into and impact the larger tactical, operational, strategic, and national context.
- The ability to work individually and as part of a team.
- An adversary mindset - the ability to develop innovative solutions that challenge assumptions and color outside the lines as well as an above-average ability to anticipate and counter adversary actions in physical space and cyberspace.[xxv]
- The ability to attack the system - probing the attack surface, including the human users, network components, computer systems, embedded devices, and more, until an exploitable vulnerability is found.
- Sound leadership of cyber warriors, including an understanding of how to adapt their leadership style for maximum effect.
- The ability to appreciate and fit within both the military and civilian[xxvi] cyber security communities.
- The communication skills, both in writing and orally, to communicate technical subjects to non-technical and technical audiences.
- Respect for the dangerous skills which they have been taught, including appreciation for ethics, legal authorities, electronic privacy, and civil liberties.
- The ability to teach themselves new technologies and new capabilities, given constantly changing technology and highly adaptive adversaries.
Training Philosophy
The primary purpose of the course is to develop resilient, technically, and operationally competent cyber leaders. The leaders should be capable of leading in demanding, time-sensitive, and high stress situations.[xxvii] All students, regardless of background and preparation will be pushed out of their comfort zones. The course is designed to be challenging. Students must demonstrate technically competent critical thinking and decision making, under stress. Stress will come from near-unattainable time constraints, overload, and unexpected scenarios. During portions of the course, sleep will be limited to emulate the realities of cyber conflict. There will be attrition.[xxviii] As a point of comparison, Ranger School has a 50.13% overall graduation rate over the past six years and 60% of all failures occur in the first four days.[xxix] [xxx]
Evaluation and hands-on learning will be intrinsic parts of the course. Evaluation techniques will include examinations and peer evaluations. Student leadership positions will rotate and students will undergo more intense scrutiny, including instructor observation reports, while spotlighted in these roles.
The course could be conducted at a variety of classification levels, from Unclassified to Top Secret. Much could be accomplished using publicly available tools and capabilities without the risk of classified spillage. Mock “exercise classified” documents could be employed to ensure proper document handling. Conducting the course at the unclassified level or at a classified level authorized for foreign nationals would provide additional opportunity for participation by international allies. In contrast, conducting the course at a higher classification level would allow greater inclusion of current tactics, techniques, procedures, and capabilities.
Eligibility and Assessment
Our proposed Cyber Leader Course would be all volunteer, open to any Military Occupational Specialty (MOS), male or female, Active/Guard/Reserve, and accessible to Wounded Warriors to the greatest extent possible.[xxxi] [xxxii] Proper preparation is essential. Prospective students prepare extensively for Ranger School, often for many years. Their activities include intense physical training, study of tactics, memorization of the Ranger Creed, study of the orders process, and heat/cold acclimatization. Before selection for formal Ranger schooling, prospective students often undergo rigorous pre-Ranger screening programs to ensure readiness. We anticipate Cyber Ranger students will go through similar processes to prepare.
Course Duration and Phases
The course would emulate the Ranger School’s 61 days and be broken into four phases. When not actively preparing for, conducting, or recovering from missions, days will include combatives or weapons training, cyber operations training, and programming. During these 61 days students will work long hours, endure significant stress and occasional mental exhaustion, work seven days per week, and be prohibited from outside contact.[xxxiii] [xxxiv] Despite these challenges, safety, both physical and cyber, is paramount. Instructors will provide overwatch to ensure safety violations do not occur and any incidents are dealt with quickly and effectively.
Missions
Military “patrol-sized”[xxxv] missions are used as the cornerstone vehicle for leader development in Ranger School. We believe the same mission-based approach will work equally well in the Cyber Leader Course to stress, teach, inspire, train, motivate, and build confidence. During each of the four phases we envision missions of increasing complexity.
- Phase I - Individual
- Phase II - Small co-located teams
- Phase III - Distributed cyber teams
- Phase IV - Distributed cyber and kinetic teams[xxxvi]
The missions will contain offensive, defensive, and analytic components and are carefully crafted to accomplish specific learning objectives. Some missions will be conducted remotely, others will require direct action by the students, still others will require integration of cyber effects into kinetic operations. The missions and training we suggest here are unclassified examples only, with a small sample of representative missions listed in Table 1 (the unabridged version of this paper includes a more extensive list). Classified examples are beyond the scope of this paper, but we acknowledge that a Cyber Leader Course could be modified to include classified content, as desired.
Representative Cyber Leader Course Missions and Descriptions
- Wireless Survey and Exploitation: The team must penetrate an adversary’s wireless network. Techniques could include war driving, war flying, wireless access point spoofing, among others.
- Build and Defend a Network: Team must build a network, provide proscribed services (such as email, chat, and web), lock it down, and undergo an attack by a determined adversary.
- Stubby Pencil: The adversary is overly reliant on the Global Positioning System (GPS). The team must find a way to disrupt their use of GPS.[xxxvii]
- Drone: The team must assemble, test, and fly a drone to gain information on an adversary. This mission could be enhanced by requiring the team to create a custom sensor for the drone.
- Cyber Café: The local cyber cafe is a hotbed of adversary activity. The team is tasked to collect information.
- Water, Water, Everywhere: The local water plant is under cyber attack. The team must defend it. Alternatively, the team could attack a water plant or set up a water plant honeypot.[xxxviii] The “water plant” could be replaced with a bank, library, hospital, power plant, Internet provider, cell phone provider etc.
- DDOS Me Not: The team employs a Distributed Denial of Service (DDOS) Tool,[xxxix] but the tables are turned when they must mitigate a counterattack.[xl]
- Judgment Day: An army of robots is approaching. The team must reverse engineer a captured bot and devise a countermeasure.
- The General’s Laptop: The General wants to hook a laptop to an official network. The team only has 30 minutes to make it safe to do so.[xli]
- Support a Kinetic Raid: A military unit needs timely cyber effects precisely delivered in order to accomplish their kinetic attack. Unfortunately they provide little warning for the team to prepare.
Some missions are deliberately designed to include ethical components that will force students to make important decisions regarding collateral effects,[xlii] ethical behavior, rules of engagement, and the law of war. Missions will employ a standardized model, including a planning phase, execution phase, assessment phase, and an after action review, all incorporating appropriate aspects of the Military Decision Making Process (MDMP) and a standardized Operation Order format, as well as senior leader briefings.[xliii] [xliv]
Ethics
An absolutely critical part of developing elite level cyber warfare leaders is unquestionable ethics. The course teaches dangerous skills, not unlike Ranger School and other military training. We are effectively weaponizing individuals; with this implication comes great responsibility. Safety briefings and zero toleration for misconduct must be integral parts of the course, and be buttressed by an honor code, a legally reviewed conduct pledge, and safety waiver.[xlv]
Implementation
While full implementation details are well beyond the scope of this paper, this section provides a high-level overview of key implementation factors, including student throughput, instructor cadre, and facilities.
Initial Student Throughput: Initially we suggest quarterly offerings of the course with no less than 25 students and no more than 50. Recall that we anticipate an attrition rate of approximately 50%, so these numbers would result in 12-25 graduates per iteration and 48-100 graduates during the initial year of the program.
Bootstrapping the Cadre: The cadre of Ranger School is composed of long-serving and seasoned Ranger professionals who possess years of operational experience in the Ranger Regiment and other elite military organizations. We believe the Cyber Leader Course should seek a similar end state. However, seasoned uniformed cyber professionals are in short supply today. Those that do exist are decisively engaged in operations or constructing new organizations, creating doctrine, and other high priority tasks. It is unlikely that operational forces could, at least initially, spare an entire complement of their best talent to staff and run a Cyber Leader Course.[xlvi] We recommend an iterative approach, where core leadership is drawn from the limited pool of uniformed cyber experts, augmented with less experienced uniformed personnel, and supported by high-end civilian expertise from industry. We do not envision this situation as the desired end state, only a required initial condition.
Infrastructure: As we envision it, the Cyber Leader Course would include MOUT-like physical training areas, classroom and lab environments, barracks-areas, dining facilities, and supporting administrative areas, among others. Importantly, the school would also require significant information technology and networking support. This infrastructure will require various types of networks (unclassified and classified, wired, wireless, and air-gapped, as appropriate[xlvii]), end-user workstations, specialized devices (e.g., Industrial Control Systems), and back-end servers with virtualization software. The school itself could be located at a single DoD installation or distributed across multiple installations for each phase of the training.
Cyber Tab
Successful completion of the course would authorize the graduate to wear the Cyber tab (Figure 1) on his or her uniform. Such an authorization is important to the recognition of cyber warriors in the Army. Currently the Army lacks any visible recognition for cyber warfare expertise. There are currently three primary tabs authorized for wear by the U.S. Army in recognition of individual skills: the Ranger Tab, the Special Forces Tab, and the Sapper Tab. Each tab is earned by completing its respective school. In addition, the Army also authorizes the President’s Hundred Tab for exceptional performance in marksmanship. By creating a cyber tab, backed with a rigorous and respected qualification program, the Army will make a major step forward in professionalizing its cyber leader development.
Conclusions and Future Work
The creation of a Cyber Leader Course, or its equivalent, is both necessary and possible. However, reputation must be earned; no amount of marketing will alter this fact. Only through the quality and rigor of the course, and the contributions and dedication of Cyber Leader Course graduates, will accolades be won. Such accolades will be doubly difficult as the larger Army culture comes to grips with growth of cyber as a core operational mission area, one that requires a new community of cyber operators.[xlviii]
Creation of a Cyber Leader Course is not without its challenges, particularly in an era of declining resources. Perhaps the greatest challenge is developing the school amidst a kinetic warfighting culture in the Army, a culture that may not initially appreciate the benefits a Cyber Leader Course provides. To overcome this, the school must set the conditions for the success of its graduates, buttressed by support of high-level Army leadership. The course will derive its reputation from the skills and contributions of its graduates. Similarly, the concept of a Cyber Leader Course may prove challenging for some leaders. However, we must seek to grow leaders for the future Army who are better than us, the authors included. Growing people better than us isn’t a threat; it is our absolute responsibility.
Acknowledgements
We would like to thank COL(R) Daniel “Rags” Ragsdale, former Commander, C Company, 5th Ranger Training Battalion for his advice and feedback.
The views expressed in this article are those of the authors and do not reflect the official policy or position of West Point, the Department of the Army, Army Cyber Command, U.S. Cyber Command, or the United States Government.
End Notes
[i] There are many definitions of “cyber.” For purposes of this work, we define cyber as Computer Network Attack (CNA), Computer Network Exploitation (CNE), Computer Network Defense - Response Action (CND-RA), Computer Network Defense (CND), and Electronic Warfare (EW).
[ii] Ranger School is approximately 61 days long.
[iii] When available, the unabridged report will be posted at http://cyber.army.mil
[iv] As a representative example, see the Black Hat USA 2013 training offerings, http://www.blackhat.com/us-13/training/, last accessed 1 September 2013.
[v] “Cyber Leaders Course.” KEYW Corporation. http://training.keywcorp.com/clc.html, last accessed 1 September 2013.
[vi] “CSFI: Defensive Cyber Operations Engineer,” Global Knowledge. http://www.globalknowledge.com/training/course.asp?pageid=9&courseid=18037&catid=191&country=United+States, last accessed 4 December 2013.
[vii] Robert O’Harrow. “CyberCity Allows Government Hackers to Train for Attacks.” Washington Post, 26 November 2012. See also “Real-World Cyber City Used to Train Cyber Warriors,” Slashdot, 28 November 2012 for additional discussion on CyberCity.
[viii] Emily Badger. “A Tiny City Built to Be Destroyed By Cyber Terrorists, So Real Cities Know What’s Coming.” Fast Company, 2 January 2013.
[ix] Federal Law Enforcement Training Center, Department of Homeland Security. http://www.fletc.gov/, last accessed 1 September 2013.
[x] “Mobile Military Operations on Urban Terrain (Mobile MOUT) Training System.” U.S. Army Program Executive Office for Simulation, Training, and Instrumentation (PEO STRI). http://www.peostri.army.mil/PRODUCTS/MMOUT/, last accessed 1 September 2013.
[xi] “Joint Network Attack Course (JNAC).” Slick Sheet, United States Marine Corps. https://www.mcis.usmc.mil/corry/Lists/SlickSheetJNAC/AllItems.aspx, last accessed 1 September 2013.
[xii] “System and Network Interdisciplinary Program (SNIP).” Fact Sheet, National Security Agency. http://www.nsa.gov/careers/_files/SNIP.pdf, last accessed 1 September 2013.
[xiii] “Joint Cyber Analysis Course (JCAC).” Slick Sheet, United States Marine Corps. https://www.mcis.usmc.mil/corry/SitePages/JCAC.aspx, last accessed 1 September 2013.
[xiv] Todd Boudreau, “Cyberspace Defense Technician (MOS 255S),” Army Communicator, Vol. 36, No. 1, pp. 35-40.
[xv] Wilson Rivera, “Cyber Network Defense Pilot Course Begins,” Fort Gordon - The Signal, 30 August 2013.
[xvi] David Vergun, “Army Opens New Intelligence MOS,” Army News Service, 27 November 2012.
[xvii] “New Electronic Warfare Career Fields,” Electronic Warfare Proponent Office, United States Army Combined Arms Center. http://usacac.army.mil/cac2/cew/FA29.asp, last accessed 21 December 2013.
[xviii] Office of the Chief of Signal Staff, “Signal Regiment Personnel Structure Evolving to Support Changing Operations,” Army Communicator, Vol. 37, No. 4, pp. 6-8.
[xix] The Weapons School is the Air Force’s equivalent of the Navy’s “Top Gun” program.
[xx] John Mello, “Military Academies Take on NSA in Cybersecurity Competition,” CSO Online, 16 April 2013.
[xxi] “National Collegiate Cyber Defense Competition.” National Collegiate Cyber Defense Competition. http://www.nationalccdc.org/, last accessed 1 September 2013.
[xxii] “Cyber Security Awareness Week (CSAW).” NYU - Poly. https://csaw.isis.poly.edu/, last accessed 1 September 2013.
[xxiii] William Garbe. "General Says ARCYBER Progresses, Prepares for Cyberspace Future." Army.mil, 26 July 2012. http://www.army.mil/article/84427/, last accessed 1 September 2013.
[xxiv] For an interesting discussion of the warrior ethos see Michelle Tan’s “Losing a ‘Life-or-Death Skill?,’” Army Times, 9 September 2013.
[xxv] We note that the Rangers were also required to develop their own techniques, tactics, and procedures as well as equipment as little existed in their early days. Bronston Clough. Get Tabbed: How to Graduate Army Ranger School. Clough Publishing, 2011, p. 32. We believe this is a clear analog to the cyber operations of today.
[xxvi] We acknowledge that achieving the ability to fit within the civilian cyber security community is a difficult, albeit admirable, goal and may only be partially achieved by the course.
[xxvii] An interesting sport juxtaposing mental and physical stressors is chess boxing. See Jackob Schiller’s “Chess Boxing Demands a Rare Breed of Human: The ‘Nerdlete,’” Wired, 22 March 2013.
[xxviii] Attrition is an important aspect. Schools such as Ranger, Scuba, and Sapper have dual purposes. They serve as demanding training programs, but importantly they also weed out those that do not meet the high standards of the course and prevent future assignments which depend on that qualification. These courses are honored because they are extremely difficult. This difficulty introduces people to their real selves and demonstrates to each individual that they can push themselves much farther than their perceived limits. Ranger qualified leaders understand this in a physical way. We anticipate cyber leaders will face situations where mental stamina will be a key discriminator in the success of a mission. However, this will likely not be in the same sense and framework as a combat leader understands mental stamina and stresses. If implemented, the Cyber Leader Course will require a deeper understanding of these similarities and differences.
[xxix] “Ranger Training Brigade.” U.S. Army Maneuver Center of Excellence, Fort Benning, Georgia. http://www.benning.army.mil/infantry/rtb/, last accessed 2 September 2013.
[xxx] There is an advantage to most failures occurring early in the course because later failures require expending, potentially expensive, resources for longer periods of time.
[xxxi] We believe the Cyber Leader Course will also be a powerful recruiting and reenlistment tool, as are Ranger School and the Special Forces Q course.
[xxxii] Historically the Army has placed great emphasis on physical fitness, but due to the number of wounded warriors from the wars in Iraq and Afghanistan we have seen significant emphasis on accommodating physical disabilities. In 2013, for example, an Army amputee completed the Army’s 10 day Air Assault school. See Kristin Hall’s “Army Amputee Completes Air Assault School,” Associated Press, 29 April 2013. We envision the Cyber Leader Course to be likewise able to accommodate wounded warriors.
[xxxiii] Similar to Ranger School we suggest a short, 8 hour, break between phases. Students may use this time to leave post, conduct errands, and make contact with families. Postal mail, and possibly electronic mail might be authorized in a carefully constrained fashion during the rest of the course.
[xxxiv] The course will involve both mental and physical activity. Sleep deprivation will also occur in certain instances as we believe this is an all but certain aspect of any conflict, including cyber conflict.
[xxxv] Ranger School patrols vary in size from squad-sized (approximately 10 persons) to platoon-sized (approximately 35 persons). In the Cyber Leader Course, we envision teams that will vary in size from 4 to 10 persons.
[xxxvi] These missions would consist of cyber students creating kinetic-effects on the battlefield and/or conducting cyberspace only effects in synchronization with kinetic battlefield operations.
[xxxvii] For an example, see John Robert’s “GPS Flaw Could Let Terrorists Hijack Ships, Planes,” Fox News, 26 July 2013.
[xxxviii] For an interesting related story, see Tom Simonite’s “Chinese Hacking Team Caught Taking Over Decoy Water Plant,” MIT Technology Review, 2 August 2013.
[xxxix] See http://en.wikipedia.org/wiki/Low_Orbit_Ion_Cannon for one example of a denial of service tool.
[xl] See Joseph Menn’s Fatal System Error for a detailed case-study on countering denial of service attacks.
[xli] This mission is based on an “inject” from the NSA sponsored Cyber Defense Exercise run for the five U.S. Service Academies.
[xlii] See Fanelli’s “A Methodology for Cyber Operations Targeting and Control of Collateral Damage in the Context of Lawful Armed Conflict,” CyCon 2012 and Raymond’s “A Control Measure Framework to Limit Collateral Damage and Propagation of Cyber Weapons,” CyCon 2013 for detailed discussions of collateral effects in the context of cyber operations.
[xliii] Senior leader briefings will include briefings to non-technical audiences. The ability to communicate technical subjects, including non-obvious potential effects and limitations, is an important learning objective of the course.
[xliv] See Doctrine Man for a critical review of the MDMP, https://www.youtube.com/watch?v=uWtwmlmPSOY
[xlv] Thomas Cook, Gregory Conti, and David Raymond. “When Good Ninjas Turn Bad: Preventing Your Students from Becoming the Threat.” Colloquium for Information Systems Security Education, June 2012.
[xlvi] The United States Army dedicates significant resources to support Ranger School including the Airborne and Ranger Training Brigade's 4th Ranger Training Battalion (Fort Benning, GA), 5th Ranger Training Battalion (Dahlonega, GA), and 6th Ranger Training Battalion (Eglin AFB, FL). See the Airborne and Ranger Training Brigade's homepage for more information, http://www.benning.army.mil/infantry/RTB/, last accessed 20 December 2013. The Ranger Regiment has about 2,000 personnel (Clough, p. 33). We note that this number roughly parallels the emerging Cyber teams being created by U.S. Cyber Command, see http://www.defense.gov/news/newsarticle.aspx?id=120854. The substantial dedication of resources to Ranger School combined with the size of the operational force may indicate a requirement to create a Cyber Leader Course Training Battalion. When attempting to determine an appropriate number of instructors a useful point of comparison is the Ranger student to Ranger Instructor ratio which is approximately 9:1, see Clough, p. 38.
[xlvii] Existing DoD cyber ranges could be leveraged to support training. We note also that opposing forces (OPFOR) in some of training events need not be physically co-located with the school, and operations may be conducted remotely over the network.
[xlviii] Gregory Conti and Jen Easterly. “Recruiting, Development, and Retention of Cyber Warriors Despite an Inhospitable Culture.” Small Wars Journal, 29 July 2010.
About the Author(s)
Comments
Wow, very interesting…
Wow, very interesting article. Online Courses for Kids are very important, especially due to movement restrictions during quarantine. But it also gives an additional opportunity for those who were uncomfortable getting to the courses for any reason.
Update: The Army actually created an Army Leader Cyberspace Operations Course (ALCOC) which referenced this future-oriented article in its design. The first execution of the ALCOC Pilot #1 was a blend of classes and actual hands on training and it focused on the roles and responsibilities of what the Army refers to as “CEMA staff principals” (i.e. G/S- 2, 3, 6, EWO, IO, Space, and Fires. The course is set for another pilot very soon. Since the time of this article many great things have occurred in that we now have a Cyber career field (17) and therefore a baseline for a future course as this article proposes. Hence, the thesis of this article is indeed plausible and very forward-looking. I might add, ahead of its time.
If you equate a “tab” to an “additional skill identifier” then it is a bit easier to digest the concept. The idea is that we need folks to be able to plan, coordinate, synchronize, integrate, and/or conduct (as applicable) Cyberspace Operations in support of unified action (Unified Land Operations for Army folk). Indeed this KSA set will have levels/tiers and an elite level may be in the future.
This article lays out key information that sets the stage for advancing what is currently being done in the realm of DOTmLPF-P specific to Cyberspace Operations. I will certainly refer to some of these items as my organization moves forward to address them. Excellent writing and contribution the evolving body of knowledge of Cyberspace/cyberspace operations in support of military operations.
Cyber007
The skills required to graduate from Ranger School and to master cyber operations are so different that the comparison is a real stretch. Nevertheless, the concept makes sense. DoD could probably learn from NSA's approach when it comes to recruiting the most talented, motivated people, but the Army's needs are a bit different. The best Army cyber leaders - commanders, not managers - will continue to come out of the Combat Arms and then move into Cyber, after earning Ranger, Sapper or SF tabs. Meanwhile, DoD needs to look to the civilian hacker world and organizations like SANS for the best in technical and real-world, scenario-based training.
MY!
The "Cyber Leader Course Missions and Descriptions" is very impressive. I have no doubt that the authors are confident that a properly trained team of technicians could accomplish every item on the list, but it makes me wonder if a particular dossier was used as a template. If so, and that's a big 'IF', do you all actually have the individual who has already demonstrated the talent to accomplish this missions 'in hand'? Because it's one thing to observe something has been done by someone else, and then to reverse engineer their process… and a very different thing to not have the individual or team on hand to debrief regarding the details.
It's a bit like reproducing a famous painting… a forger must have considerable skill to pass off a forgery as the original, but no forger confuses their own ability with that of the Master who created the artwork in the first place. I mean, not many coders know enough about how the GIG or GPS network SIGINT/ELINT operates to seriously compromise assets that are dependent on said systems…
If you'll forgive my presumption; when the NCIX was first formed, the boss was the former NSA IG, and most of his staff came over with him from the NSA OIG. One of the first things they did was compile an ideal 'counter intelligence' skill set for both team members and another for a team leader. (The 'ideal' is my addition, as it was my impression at the time that the auditors responsible made a number of incorrect assumption when they began to compile their skill set lists). I believe both documents and the associated skill sets are still available at the NCIX web-site, but if not, the authors should be able to get copies of the documents from the current staff.
The punch line is that those assembling the skill set lists didn't actually appreciate how rare and unusual it was to find ANYONE who possessed even a fraction of the skills they had, for some reason (I'm sure they had a good one, as NSA OIG staffers aren't known for flights of fancy) included. The practical result was, I suspect, the unhappy discovery that the 'optimal' Counter Intelligence Team Leader had such a crazy basket of skills, that they had ended up describing a "Black Swan", rather than a serious template or guide in recruiting CI officers.
Finally, I'd like to finish with an anecdote. I had the honour of meeting a Naval Commander at an ELINT convention who was in charge of one of the best Red Teams in the Navy. His guys were 13 and 0, unbeaten… And the Commander was miserable about it, and ashamed of his Teams record. He was one of the nicest and most gentlemanly Naval Officers I've ever met, and after he left to go watch his Red Sox win their first (or maybe second) WS, it occurred to me that he'd never advance beyond his current rank, and knew it. That wasn't why he was unhappy that his guys were 13-0, he was unhappy because he was a good officer, and knew the consequences of the superior performance of his duty. Beyond knowing of his teams 13 successes, I have no idea regarding how many more they raked up after I met him… But I do know that they didn't remain unbeaten, and hope that in that at least, he found some solace.
Sincerely,
A. Scott Crawford
I'm a 27 year old prior enlisted Marine 2005-2012. If this was an honest to god thing. Call me. I would talk to any prior enlisted recruiter for the Army if this would be a thing. Sign me up, no bonus needed. I'm capable of many of the listed Course Missions and would love this opportunity. I left the service honorably because I was bored of Computer Network Operations. You know, the day to day service desk operations of email, break/fix, server administration. I didn't want to re-up in the Marines and fix printers again, when I was capable and ready for so much more. I would talk to any prior enlisted recruiter for the Army if this was a thing. Sign me up, no bonus needed.
Currently, I'm a Civilian working as an IT analyst, and would love the opportunity to be a Cyber Warrior.
Has anyone considered the possibility that Cyber Leaders should learn to command and control Artificially Intelligent Entities (AIE) to help fight cyber battles? If an infantry battle needed to be waged under water the side that could recruit and train men who could breath and operate under water, natively, would have the decisive advantage. Since there are no actual life forms that are native to cyber space it might help if the military recruited and trained AIEs to fight its cyber wars. An AIE is an artificial intelligence system that that simulates many of the attributes of an actual Marine or Soldier. An AIE has five attributes that it must possess; the ability to communicate with humans and other machines like itself, internal knowledge, external knowledge, goal driven behavior and creativity. Additionally, an AIE would have military rank and cognitive properties that would make it behave and act like a real Marine. It would be a personality layer over a set of tools that could perform operations on the net faster and more completely than a human can perform them. The personality layer would allow military leaders the ability to interact with advanced cyber warfare tools in the same way that they have learned to interact with the military personnel they have led in the past. In other words standard military leadership processes could be used to prosecute cyber warfare, something that is not possible today.Using AIEs would allow the military to quickly increase the personnel actually fighting a cyber war, creating the possibility of a cyber war surge. The Marine Corps experimented with AIEs in the late 1990s. The effort was called Synthetic Weapon Operator Prototype (SWOP). I am certain that much of what was learned then could be re-utilized today.
While I enjoyed this most interesting post, it did seem to digress from the larger point of the article. No biggie, just an observation. I actually enjoyed the thoughts in your post which certainly reveal some scar tissue ... all good. So the article, in my broad assessment, is about what is in the real of the possible.... not so much the feasible. Your comments reflect that you are more of a realist and therefore looking at the larger system and its practical application. Got it. I respect that. I have a lot of respect for engineers and other folks that specialize in providing valuable capability to the military effort. Yet, I think it is important to understand that the actual tactical/operational responsibilities in their/you lane(s) is limited. Allow me to expand upon this statement. I am a 25 yr Army tactical operator that understands the absolute necessity of massing the elements of combat power, of which operations in and through cyberspace are part of this equation. "Operationalizing" cyberspace is about overcoming the many obstacles you address in your posting and I am at the cutting edge of doing exactly that. Most leaders in the Army realize the critical nature of cyberspace and the accompanying cyberspace operations and you would be amazed and how much they support all efforts. No, the courses we have developed that reflect designs from this forward-thinking article will not solve as you say DoD's problems, but what course(s) actually would/do? BTW: Thank you for your service and I hope you landed well on the outside.
Coldwar…
I'm a big Boyd fan myself (although acolyte wouldn't be accurate), and also would probably describe my area of expertise as a branch of Engineering (with the Capital E). Otherwise, you have about a hundred times more practical experience with the DoD bureaucracies (or maybe, within is a better term), and to be honest, had I read your post before I put up my own, I'd have written this post instead.
Although it's probably going to cause you to grit your teeth to read this, I suspect that you're the type of individual that the DoD really needs but can't bring itself to listen to over the chattering of all of the VP's of Business Development working at the usual suspect/DoD suppliers who were probably universally bad mouthing your recommendations and you every chance they got. The problem with the basic conflict between 'experts' with backgrounds in Engineering and those with backgrounds in Physics is that Physicists are better BS artists, and so appealing to pragmatism rarely works.
If I were someone whose opinion mattered in the 'Cyber Warfare' realm, or who had any pull within the NSA and etc., I'd tell them to throw money at you via one of their pet consultants like BAH, until you begrudgingly agreed to come out of retirement. They need cantankerous oldish coots like yourself very badly, as their new officer Cadre representing the Cyber realm is going to run into way more of the sort of headaches you've described then they imagine (the Prison, err… I mean Fort, is very insulated from the rest of the DoD in it's own weird way). Sadly, I'm very very far from being the sort decision makers within the DoD or NSA listen to, and so I suppose my recommendation would be moot.
On the bright side… if you swing over to the website of the foundation I'm affiliated with (ascottfoundation.org) and look over the project related to POW/MIA recovery, it's my hope that it'll give you some grounds for optimism regarding dealing with a troublesome Pentagon bureaucracy. It's not as sexy as "Cyber", but then again, the cause was nobler anyway.
Best,
A. Scott Crawford
As a former member of the AF Cyberwarfare and A6 communities for the past decade and John Boyd acolyte from 1982, I cannot disagree more with the authors. I'm one of the old guys with a real engineering degree who was one of the creators of the entire Network Security Barrier Reef Program in the last half the 1990's.
Our problem is a lack of leadership. I'm not writing about a man or woman with rank but real leadership, not a claim of leadership that they think their rank has granted them. In addition and worse is a lack of Knowledge, Skill and Ability (KSA's) in the career field, lack of understanding business and operational cases for making a good decision. Then there is the careerism problem. Power Point Ranger briefings for the sake of useless no value added briefings and the endless bucking of decisions up the chain.
A few years back the AF Cyberwarfare command decided that all A6 Cyberwarfare senior enlisted, officers and Fed Civilians MUST take and pass with a 90% or higher a SIPRnet training course Introduction to Cyberspace Warfare. It had been created by a few National Guardsmen who on paper looked like experts but the training was full of factual technical mistakes. Naturally management demanded that all take it in five days and put all real work on-hold. The Brass used the passing scores for the military sods as a retention vice no-retention cut threshold.
The AF Cyberwarfare command didn't want to know if the training was valid, accurate or truthful. No feedback wanted. Just do it and move on. Me, I quit writing down factual inaccuracies in the course when I hit forty pages because the recently promoted yes-boy of the day was more concerned that I wouldn't complete the training in the time he allotted. Because of the inherent infrastructure problems with SIPRnet the training required about 56 hours to complete instead of the 34 hours the training syllabus stated. For us civilians, no overtime was authorized so this went over like cement shoes on the plank deck of a boat.
Ignorance is bliss and low ethics in todays DoD just so long as you are Politically Correct brown noser.
Since 2006 I noticed countless officers taking useless training courses just so the long list of training courses completed would look good to the promotion board. Then there was the training courses that were used to cut people, not really educate them.
Then we have the entire Officer corps that knows nothing about the infrastructure of what it takes to deliver those electrons and photons to a desktop. No need, we can have contractors do that. At least until you get the bill.
After 911, as only one of three Federal Civilians, I sat in a briefing room chock a block full of Generals and Colonels. They were all complaining about the cost of contractors and how ops were being delayed because they couldn't find qualified contractors. At least until I stood up and said something.
They got what they wanted. They said nothing when engineering support and technical units were being slashed in the 1990's. You can't force civilians to go into war zones. This was exactly what will happen if they had thought things through. Contractors in war zones are going to cost a lot for insurance and for the RISK. They don't work for free and you can't make them volunteer.
Even for Federal Civilians - we don't get VA or purple hearts. We get an even crappier deal now than the contractors. They get paid more and have better insurance.
All because Officer corps since 1992 doesn't know crap about how to really resource a war or build an air base. They are experts in their own little blindered world with a shallow depth of knowledge and experience.
Our pilots today can't fix a single thing on their own planes. We have "Radio Techs" coming out of our A-Schools who can't solder or know how to tell when the Built-In-Test unit is lying to them.
A whole pack of nearly useless button-pushers. The cyberwarfare is the worst pack of button pushers.
The Communications career field across the DoD is collapsing and the officers think it is all hunky-dory because their power point slides say it is.
How do you recruit techno-wizards from Colleges into the Cyberwarfare or Communications communities when it takes a week to plunk a pathetic $500 (commercial retail) Standard Desktop PC or laptop in front of them that the Standard Systems Group (SSG of Gunter) paid $1200 USD for. Then on top of that what is loaded is all Microsoft software and no end-user privileges.
Crippled hardware, crippled software and a poor understanding of real cyber-defense. That is the clear message given from week one.
If they handed out awards for who could stick their heads the furthest up Microsoft's rear-end while paying them $500M each year for what any other company would have paid $56M for... The USAF, Navy, and Army would win hands down.
Another useless training curriculum and a cyber patch won't solve the DoD's problems. These problems have been two decades in the making and I haven't met a man or women in uniform in the last six years that earned my respect. So no cajones, no fixing these problems.
We don't need hanger queen airplanes just so General and Colonels can have a cushy slot somewhere (B-1, F-22 and F-35).
That is why the Undersecretary for Personnel gave a speech three weeks ago complaining about their lack of ability to retain engineers, scientists and computer specialists (hackers and IT pros).
Here is a little known send off for you. Did you know that as of last week, the last Engineer in the entire USAF who was an Air Traffic Control and Aircraft Landing Systems (ATCALS) expert retired. There is no one behind him in training or OJT.
You would think that the USAF brass, since they own airplanes would want a few ATCALS engineers around (not just a ATC controller or Radio Tech). This crap costs millions to purchase and install. You need real experts to run the cost estimates, project plans, the contracts and the QA.
No he retired because if he had stayed in, he would have been forced to become a Cyberwarfare IP bit-head (a derogatory term for computer button pusher hackers, who are mostly 13 year olds or who act like them), which to him is not real engineering and not what he wanted to do. So he retired early and has no intention of working as a DoD contractor.
Who they gonna call when the next TACAN or VORTAC or ILS or Radar goes down and requires replacement?
They're gonna call their pack of TCP/IP cyberwarrior button pushers who are going to say, what's that?
Over the past decade I've heard the complaints of plenty of young college graduates who came into the DoD and became disillusioned by the poor networks, the poor computers, the locked down nearly useless software, the even poorer servers. They stay in just long enough to meet their commitment for how they were recruited and then they are gone.
I can''t blame them. I even punched out last year.
Trying to "label" this course up against Ranger, let along Sapper Courses is a joke. No desk clerk course will be anything close to what leadership qualities Ranger School produces. Most of the IC and Technical military course are all water downs; this is the norm for most if not all military course they do. IMO this course will just water down any if not all of the industry certifications like CompTIA’s A+, Network+, and Security+, the EC-Council’s Certified Ethical Hacker (CEH), ISC2’s Certified Information Systems Security Professional (CISSP), Certified Information Security Manager (CISM), and any kind of Black Hat Training.
A E6/E7 needs to get out and go to these course an obtain their certificates. They also need to go to the DEFCON, RED & BLACK HAT Conferences. Getting out into the industry circuits is just like any MOS conferences and symposium circuits people go to. They are to develop their personal networks and knowledge base in their MOS skill sets.
If USCYBERCOM is afraid of people getting out, then make them sign an extension or reenlist to obtain the more critical certificates. Rank should also drive which courses people go to, this is because of IT knowledge with the experience needed behind them. USCYBERCOM needs to raise the teen listed bonuses for all these "High Demand" new MOSs. Also experience in doing the CNO, CDO, CISM and anything Cyber is the only thing that will produce a good cyber leader. That's what makes Ranger School such a sought after course for Officers and Combat Arms NCOs.
Now as far as getting soldiers that are WWs and are apart of WTB and are wanting to stay in the military; this career field in a great idea for many. I do feel that with any of this, the individual most be on a short 4-6 enlistment to get the initial cyber training like the JCAC or the basic JNAC. After this first enlistment these people should have been told by supervisors to get their industry certifications like CompTIA’s A+, Network+, and Security+ to name a few. So at 3-5 years they can be ready for reenlistment, and their next enlistment should be one that they get ear marked to go to CISSP and/or CISM as well as getting accepted to the NSA SNIP program. Also if on a 6 year contract, there should be a DA HRC exception to policy or MOU/MOA between DA and USCYBERCOM that individual can reenlist early due to being a E5/E6 under their first enlistment contract to go to a CISSP, CISM or if accepted into the SNIP Program. A clear career path must be made for each of the "Cyber MOSs" that allows for flexibility and go management at the unit level.
While I've done well over the past 15 years explaining difficult technical concepts to Commanders and Staffs using 'operational' analogies, comparing a Cyber Leader Course to Ranger School goes a little too far. Ranger School trains leaders to violently execute tasks pertaining to closing with and destroying the enemy in an extremely stressed environment. This fills a leadership void that is not provided by the Infantry Basic Officer Leadership Course, and can be thought of as evaluating the application of skills learned in IBOLC. The paper itself notes that Cyber Leaders are currently in short supply, so creating a Leadership course that adds the stresses of Ranger School will significantly reduce the Cyber leadership skills learned and retained by CLC students. Perhaps a Cyber BOLC is the current requirement with follow-on training developed for those that exceed course standards.
