The Role of the Dark Web in Future Cyber Wars to Come
Jason Rivera and Wanda Archy
Introduction
Warfare is an ever-changing discipline that has evolved alongside human civilization for nearly all of recorded history. From the moment that early hunters crafted the first spear, from the first war to occur between two tribes, to the modern warfare dynamics of today’s world – war has evolved in parallel with mankind. As warfare expands, so do the domains in which it is fought. We fought each other first over land, then the sea, and then the air. We launched satellites into space, and then we created anti-satellite weapons to destroy those same satellites that we had put into space. Most recently, humanity engineered a capability to share information almost instantaneously throughout the globe via the Internet; we then subsequently found ways to use that same global connectivity to hold each other’s critical infrastructure at risk.
The primary takeaway of the above is that warfare has always and will always continue to evolve. A recent evolution that this paper will focus on is the “Dark Web”, to include how this aspect of the Internet has affected national security over the last decade as well as how it may affect national security in the years to come. We use quotations in our initial introduction of Dark Web because it is known by many names and is often conflated with similar terms that characterize other related concepts (such as the Deep Web). Accordingly, this paper will seek to establish a conceptual framework of the Dark Web as a sort of landscape characterized by a series of threat issues and threat actors that national security professionals should be aware of. We will then build upon this framework of viewing the Dark Web as a landscape so that we may illustrate its applications to both the kinetic and digital aspects of human warfare.
This paper will narrow its scope by focusing solely on the national security considerations of the Dark Web, and not those issues that delve into the realm of domestic law enforcement. Drug trafficking, financial fraud, counterfeit goods, illegal pornography, etc. – these are issues that this paper defines as falling into the realm of law enforcement. Weapons proliferation, terrorism, intelligence gathering & extortion, malicious services-for-hire, etc. – these are issues that this paper defines as falling into the realm of national security. We are aware that there is not necessarily a clean split between issues of law enforcement and national security concern; again, our intent here is to narrow our focus onto those threats that have unique national security implications.
Understanding the Dark Web’s application to the future of cyberwarfare requires us to view the problem from multiple perspectives. There is, of course, the underlying national security perspective that should drive our foundational understanding – however, of equal importance are both the economic and intelligence operations perspectives. From an economic perspective, we should consider that the primary application of the Dark Web, thus far, has been as a marketplace used by those wishing to engage in illicit trade. The ability to understand illicit trade on the Dark Web as it applies to national security requires us to consider concepts such as supply, demand, vendor reputation, etc. Whereas from an intelligence operations perspective, the Dark Web can also be viewed as neutral grounds for two parties who wish to anonymously engage in the exchange of information, weapons, and national security secrets. Much like the Cold War era depiction of a clandestine agent meeting his/her source at a “safe spot” or communicating with agents via dead drops, the Dark Web in many ways can be thought of as the cyber means through which two intelligence professionals can safely meet and exchange information in neutral grounds.
In the next section of this paper, we will expand on the above concepts by putting forth a working definition of the Dark Web, which we will subsequently build upon by demonstrating how this anonymous meeting grounds may potentially affect nation-state national security in the future.
Viewing the Dark Web as a Landscape
One of the primary challenges for national security professionals in analyzing the Dark Web is the difficulty around reaching a common understanding of what the term entails. The term “Dark Web” is already ambiguous and is often conflated with other terms such as the “Deep Web” or the “Criminal Underground” or one of many other terms used to characterize its place within the Internet1. Though the purpose of this paper is not to define the Dark Web, a working definition is necessary in order to understand how the Dark Web may affect the national security interests of nation-states throughout the globe. Given this necessity, we propose the following framework:
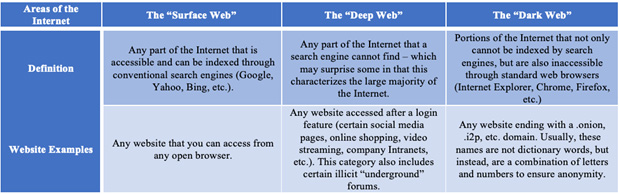
Table 12
Now that we have divided the Internet up into three parts, let’s contextualize these parts so that we may continue to narrow our focus. To be clear, both the Surface Web and the Deep Web do hold national security relevance in their own respects. Intelligence agencies throughout the globe regularly exploit open source intelligence (OSINT) found on the Surface Web; whereas the Deep Web is the location of choice for those cyber criminals who wish to engage in the purchase and sale of stolen identity data, such as social security numbers and other personally identifiable information (PII). Yet for the purpose of this paper, we will focus solely on the Dark Web as defined by the characteristic of being accessible only through special Internet browsing protocol, such as The Onion Router (TOR). That being said, let us quickly review the means through which the Dark Web is accessed.
Access
As described in Table 1, the Dark Web is only accessible through non-conventional browsers, notably TOR and I2P (of which the more popular means is TOR).3 TOR provides anonymity by guiding Internet traffic through other “TOR nodes”, or computers using the browser.4 This traffic bounces through TOR nodes until ultimately it leaves through an “exit node”.5 This essentially creates an “onion” or multi-layered anonymity. According to TOR’s website, “Tor protects you by bouncing your communications around a distributed network of relays run by volunteers all around the world: it prevents somebody watching your Internet connection from learning what sites you visit, and it prevents the sites you visit from learning your physical location.”6
In addition to leveraging the TOR browser, many users will also use a Virtual Private Network (VPN)7 and/or a virtual machine (VM)8 in order to facilitate additional layers of protective anonymity. These additional measures are not necessary to access the Dark Web, but are considered best practice by cybersecurity professionals who regularly engage in research activity on the Dark Web. Once the TOR browser (or its I2P equivalent) is installed on the user’s computer and network anonymity is enabled, the user then needs to determine which Dark Web location they wish to access.
Locations of Interest & Issue Types
To understand the Dark Web from a national security context, we should focus primarily on two things: commerce and communication. From a commerce perspective, national security professionals will want to understand how various actors will use the Dark Web to engage in illicit and/or clandestine trade. From a communications perspective, national security professionals will want to understand how these actors will leverage the Dark Web to conduct planning, recruiting, intelligence gathering, and other activities of interest. Given our focus, there are two general location types on the Dark Web that this paper delves into:
- Marketplaces: Locations on the Dark Web where individuals can go to engage in illicit/clandestine trade.
- Forums: Locations on the Dark Web where individuals go to engage in “secure” discussions pertaining to a variety of different issues.
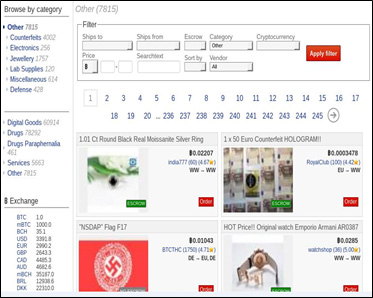
Image 1: Dark Web Marketplace & Categories Listings
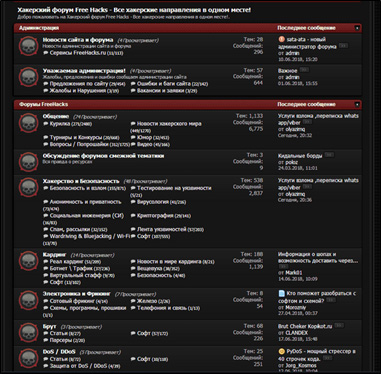
Image 2: Russian Language Dark Web Forum
One of the primary challenges posed by the Dark Web to national security professionals is segregating out the “noise” from issues of legitimate national security concern. With annual cybercrime revenue estimated at approximately $1.5 trillion9 and considering the existence of 7,000-30,000 TOR sites,10 knowing where to look requires us to bound our focus to specific subject areas. In terms of marketplaces, national security professionals should seek awareness pertaining to illicit Dark Web goods and services that could harm national security interests. When it comes to forums, these same professionals should seek awareness regarding conversations, planning activities, and coordination efforts that could potentially affect national security. Given this understanding, the following table is our attempt to distill out issues of national security from issues that do not pertain to national security:
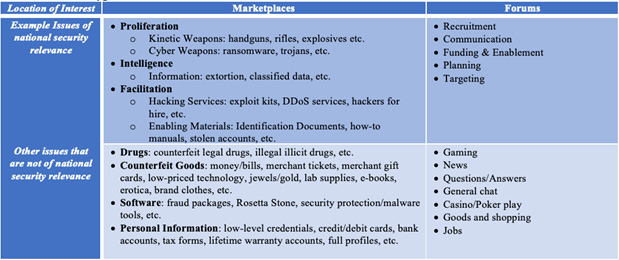
Table 2 – Issue Types
Types of Actors
Once we understand locations of interest and issue types on the Dark Web, national security professionals should then consider the types of actors they are likely to encounter. The following table outlines the types of actors that national security professionals should be most concerned with:
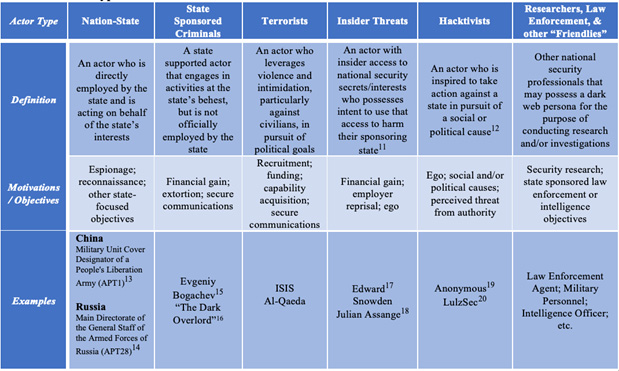
Table 3 – Actor Type
Observations So Far
In an effort to characterize the Dark Web from a national security perspective, below are a series of Dark Web case studies that detail issues of national security relevance. Using the frameworks provided by Tables 2 and 3 of the previous section, these historical observations will be categorized by both issue type and threat actor type in order to provide additional contextualization around how the observation had an effect on national security.
Sale of Unmanned Aerial Vehicle (UAV) Sensitive Documents
Issue Types: Proliferation & Intelligence
Actor Type: Insider Threat
In 2018, security researchers at Recorded Future discovered a sales listing within a Dark Web marketplace for information on an MQ-9 Reaper drone used by the United States Air Force.21 The seller stated that “I expect $150 or $200 for being classified information.”22 The Reaper drone is a widely used US military capability that is deployed throughout the world in support of historical and ongoing contingency operations. In addition to sensitive documents on the Reaper drone, the seller had also listed several other documents, to include an M1 Abrams tank manual and tactics to defeat improvised explosive devices (IEDs).23
United States Office of Personnel Management (OPM)
Issue Type: Intelligence
Actor Types: Nation-State & State-Sponsored Criminals
In 2015, OPM announced that it had been a victim of a data breach resulting in the theft of approximately 21.5 million records of persons who applied for a U.S. security clearance.24 Information contained within those 21.5 million records included full names, birthdates, home addresses, Social Security Numbers, and “also security-clearance files containing extensive details about friends, family, relationships and finances for a range of highly sensitive government jobs”.25 This implies that whoever stole the data effectively possesses not only a roster of U.S. persons possessing a security clearance and the organization they work or worked for, but also the location where each of these individuals live combined with data that could potentially be used to facilitate future blackmail (close family and personal contacts, criminal and financial records, etc.). To make matters worse, this data was then passed to cyber criminals who attempted to monetize the stolen data on a Dark Web forum called “Hell”, where the seller(s) listed personal details for sale, including the social security numbers and personal relationships of the OPM data breach victims.26
Terrorist Use of Dark Web to Engage in Financing & Weapons Acquisition
Issue Type: Facilitation
Actor Type: Terrorist
In December 2018, Israeli authorities levied criminal charges against an individual named Ahmed Sarsur for his attempt to use the Dark Web to acquire weapons for and provide financial support to terrorists in Syria.27 According to the court documents, Sarsur’s actions included an attempt to purchase explosives, hire snipers, and provide financial support.28 Additional reporting by CNN demonstrates that this is not just an isolated incident, but rather an emerging phenomenon. In September 2018, CNN reported that a TOR website called “SadaqaCoins” had been opened on the Dark Web, with the site’s stated goal being to “support the Jihad by providing a secure platform between the funders and the project organizers.”29 The following is an image of the landing page of this Tor website:
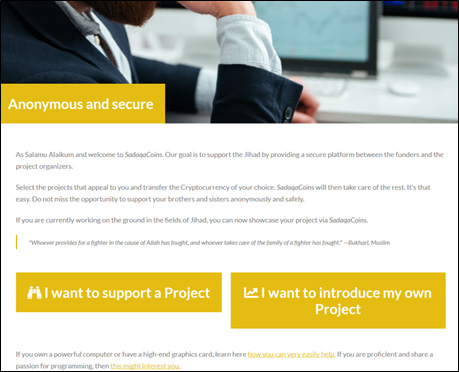
Image 3: SadaqaCoins Landing Page
Zero-Day Exploits
Issue Type: Proliferation
Actor Type: All
From a national security perspective, the uncontrolled proliferation of zero-day exploits raises many concerns, as these capabilities have historically demonstrated a capacity to significantly affect the national security arena. Stuxnet, an alleged US-Israeli malware capability designed to disrupt Iranian uranium enriching centrifuges at Natanz,30 is perhaps the most well-known exemplar of how zero-days can significantly affect the national security interests of nation-states. By most estimates from the national security research community, Stuxnet had potentially delayed the Iranian nuclear program by several years,31 demonstrating the national security potential of zero-day exploits.
Since the discovery of Stuxnet, cyber criminals with the desire to monetize their ability to develop information technology exploits, particularly zero-day exploits,32 have heavily leveraged Dark Web marketplaces to find prospective buyers for their capabilities. The anonymity facilitated by the Dark Web makes it an accessible and secure outlet for finding zero-day exploits prior to their public announcement, allowing attackers to purchase these exploits and launch attacks prior to vulnerability patches being released.33 The following image is an illustration of how US government zero-day exploits have been repurposed by those with malicious intent and monetized on the Dark Web:
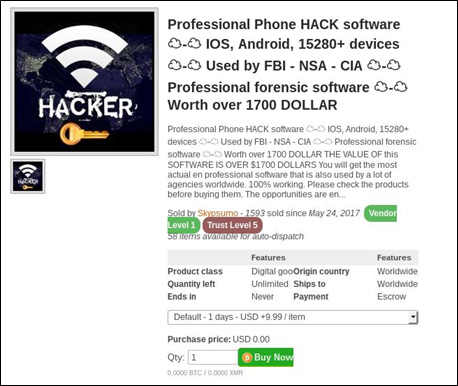
Image 4: Repurposed US Government Zero-Day Capabilities for Sale on Dark Web Marketplace
Emerging Trends Pertaining to National Security
Whereas the last section of this paper discussed observations so far, this section of the paper will delve into the possibilities of how the Dark Web may evolve to affect national security in years to come. Rather than listing a series of discrete possibilities (as the possibilities are literally endless), we will instead put forth a categorical framework that covers the types of Dark Web national security threats that defense professionals are likely to encounter. Before diving in, we want to make it very clear that no framework is infallible. It is very likely that there are categories of Dark Web threats and possible trends that we did not cover in this framework. We are aware that the threat landscape could change in the blink of an eye as emerging technologies such as quantum computing, digital currency, and 3-D printing continue to evolve. Given these caveats, our understanding of the historical threat landscape, and our research into emerging Dark Web trends, the following is our proposed framework:

Image 5: National Security Threats Posed by the Dark Web
Proliferation - Kinetic Weapons
The anonymity facilitated through the Dark Web fosters an ideal trading ground for would-be buyers and sellers of dangerous weapons. This is more than just theoretical – it is a fact that has been proven through observation time and time again. Uranium, dangerous chemical compounds, military grade firearms à these are sample subset of the types of weapons that have been listed on the Dark Web. In response to these listings, the global law enforcement community has been aggressively pursuing would be buyers and sellers of weapons on the Dark Web – and in many cases they have been successful in thwarting potential attacks. In 2016, the U.S. Federal Bureau of Investigation (FBI) collaborated with Irish law enforcement authorities to stop an Irish Republic Army (IRA) militant from procuring handguns, grenades, and plastic explosives from a Dark Web marketplace.34 And while the national security community can claim minor victories with these types of preventative operations, those interested in anonymously buying and selling kinetic weapons have begun to shift their methodology.
Over the coming years, we assess that there will be two major evolutions to the ways that kinetic weapons are traded on the Dark Web. The first is that buyers and sellers of Dark Web weapons will likely move their business away from some of the more popular open-access marketplaces (such as Dream Market) and over to other marketplaces that require a higher degree of vetting to enter (such as Demon Forum and OG-Users Forums). This is likely to happen for two primary reasons. The first is that the individuals who engage in the weapons trade are becoming more wary of undercover law enforcement presence and the possibility that they are being lured into a trap. The second is that the major marketplaces are likely becoming less tolerant of the risk they incur by allowing weapons listings on their marketplaces. Weapons listings have historically attracted the attention of the global law enforcement community, which has resulted in undercover officers perusing markets looking for leads. Beyond the increased risk, the marketplace profit margin for the weapons trade is relatively low when compared to the profit margins of other high-volume illicit goods such as drugs and fraud. According to two studies conducted by RAND, global drug sales on the Dark Web were estimated to be between $12-$21.1 million per month in 2016,35 while the global arms trade was $80k per month in 2017.36 Below is an image from the Dark Web listing some of the locations where threat actors can still purchase weapons:
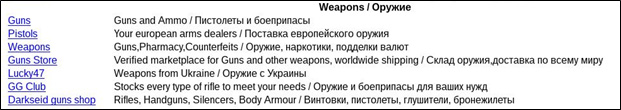
Image 5: Examples of Limited Access Dark Web Marketplaces
The second major evolution we are likely to observe is the transition away from trading and mailing tangible physical weapons towards the digital trade and exchange of information on weapons. The last section of this paper discussed an incident where an insider threat within the US military sought to sell sensitive documents pertaining to a US military drone, but that was only the tip of the iceberg. Emerging technologies such as 3-D printing make it possible to sell the schematics and assembly instructions online, allowing both the buyer and the seller to avoid the risk of physically mailing weapons components via freight mail. Up until recently, it had been illegal in the United States for developers of 3-D printing weapon schematics to distribute their product online due to violations of the International Traffic in Arms Regulations (ITAR). However, in June 2018 the U.S. Supreme Court ruled in favor of a company called Wilson and Defense Distributed, allowing them to “publish plans, files, and 3-D drawings in any form and exempts them from export restrictions.”37 This ruling will not only empower 3-D weapons entrepreneurs to spread their business globally, but will also make it much easier for weapons buyers and sellers to trade weapons capabilities while reducing the risk of detection by global law enforcement. And like other illicit markets, the Dark Web is likely to be a primary outlet for the trading of 3-D weapons schematics.
Proliferation – Cyber Exploits
Before the advent of the Dark Web, highly effective cyber exploits were only available to advanced nation-state governments, organized criminal groups, and close-knit research communities. This is no longer the case, as effective cyber exploits are now being heavily monetized and distributed across dozens of Dark Web marketplaces and forums. This raises issues from a national security standpoint, as it allows threat actors who previously did not possess the technical prowess to simply buy their desired capabilities. The following represents some of the ongoing and future implications of widespread proliferation of exploits on the Dark Web:
Repackaging of Nation-State Exploits: Dark Web malware developers and distributors will continue to repackage and repurpose exploits used by nation-states. There are a couple of reasons that these exploits will continue to rise in popularity – the first is that they are tried and true capabilities that have been successfully leveraged by the world’s most advanced nation-states. The second is that there is a psychological appeal to attaching a “used by nation-state” branding statement as part of the marketing ploy used by the sellers of these exploits.
Increased nation-state and non-state group access: Less well-developed aggressor nation-states, such as North Korea or Iran, that historically did not have the access to powerful cyber exploits now have a greater degree of access to advanced capabilities. Similarly, threat actor groups that typically did not have access to advanced technologies, such as terrorist organizations, can now simply purchase a desired capability.
- Exponential knowledge proliferation: Whereas threat actors used to operate in closed off silos, the widespread proliferation of capabilities via the Dark Web allows exploit developers to leverage their own technical understanding of exploits to make cyber exploits that are stealthier and more dangerous than previous iterations.
- Increased profit margins equals increased incentive to develop exploits: In 2014, it was determined that the cyber black market is more profitable than the global drug trade.38,39 Global total cost of cybercrime in 2017 was up to $600 billion.40 This increase will continue to incentivize developers to create exploits for sale on the Dark Web.
Intelligence – Source Operations, Insider Threat, & Extortion
In the coming years, the Dark Web will be increasingly leveraged for intelligence source operations, insider threat activities, and extortion. There are two primary reasons for this – the first is the inherent design of the Dark Web and its ability to facilitate bidirectional anonymity. The second reason is the increasing amount of data available on the Dark Web that can be used by intelligence officers for extortion or to coerce sources.
In terms of increased anonymity, meeting virtually under the guise of an anonymous persona facilitates a higher degree of safety for both intelligence officers and their sources. The execution of a source meet-up between both the intelligence officer and the clandestine source is a substantial risk for both parties – particularly for the source. In 2017, The New York Times reported that the Chinese government either killed or imprisoned between 18 – 20 CIA sources between the years of 2010 and 2012.41 That is an average of nearly 10 people per year – and that is just for CIA operations in China. Now consider how large this number is likely to be when considering not just the CIA, but all clandestine intelligence services operating throughout all countries, throughout most of the world’s nations. For this reason, intelligence services are likely to increasingly pursue leads and meet up opportunities leveraging the Dark Web in order to attain a higher degree of safety.
The second reason that the Dark Web will likely rise in popularity amongst intelligence officers is the increasing amount of available data that intelligence officers can use to extort potential sources for information. By combining information obtained from the cybersecurity breaches that are occurring on a regular basis, and by merging that with other information that can be used to extort an individual, national security professional may witness a wave of upcoming extortion attempts. Consider the following scenario – what if an intelligence-collecting organization were to possess two datasets: one dataset that contains the information stolen from the US Government OPM breach and another dataset includes identities of individuals who were compromised during the Ashley Madison breach.42 By cross-referencing these two datasets, the intelligence collecting organization could derive a list of individuals who are in positions of national security, determine the types of information they may have access to by virtue of their employment history, and then blackmail selected individuals into relinquishing information over the Dark Web.
Facilitation – Terrorism
As the global conflict between free society and terrorism endures into the 21st century, terrorists and terrorist sympathizers throughout the world are continuing to adapt their methodologies in response to changes in national security tactics and the evolution of technology. It is common knowledge at this point that NATO and its allies possess the technological advantage of being able to monitor what would be considered “open” communications (e.g. telephonic communications, radio, the surface web, etc.). Terrorist organizations have also begun to realize this and are shifting their communication techniques to technological means that provide higher degrees of anonymity, such as using TOR.43 In addition to the shifting of communication techniques to anonymous means, national security professionals should also seek to understand how terrorist organizations will use the Dark Web in order to achieve their violent and political objectives.
In the previous section we illustrated an example of how terrorist organizations are seeking to facilitate funding and weapon acquisition activities via the Dark Web. In the future, it is plausible that terrorists will leverage Dark Web marketplaces to purchase enabling materials in order to assist the execution of their objectives. In addition to weapons and funding, enabling materials such as counterfeit identifications, non-attributable communications devices, and forged documents can serve to facilitate a terrorist organization’s goals by fostering the ability to travel, conduct secure communications, establish proof of residency, etc. This is particular concerning when we think of the implications of how a potential terrorist could use these enabling materials to adopt a pseudo-persona in order to evade detection from the authorities.
Within the counterfeit document listings space of most marketplaces, a variety of counterfeit documents can be found to include counterfeits of: passports, drivers licenses, utilities bills, tax forms, green cards, etc. In some cases, vendors on the Dark Web have demonstrated the capability to sell legitimate identification documents as opposed to counterfeit ones. In 2017, an individual who may be on a terrorist watch list attempted to acquire a legitimate passport from the Dark Web from a counterfeit identification vendor. This vendor claims to sell real passports from European countries that he is able to acquire via his purported connection to “corrupt individuals” within the passport issuing agencies of these European countries. In an online conversation between the vendor and the would-be purchaser, the vendor strongly declined the purchase request, citing that he believed that the would-be purchaser was on a watch list.44 Below is a screenshot of the vendor’s presence on the Dark Web:
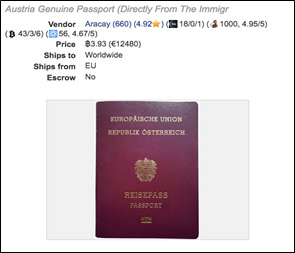
Image 6: Dark Web Listing of Genuine EU Passport45
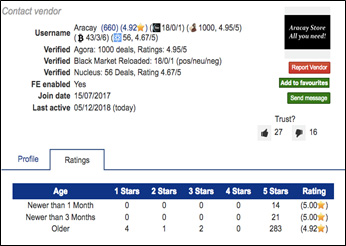
Image 7: Vendor Ratings Page46
Facilitation – Malicious Services for Hire
The Dark Web is home to a variety of different malicious services that could be leveraged by potential threat actors seeking to cause harm. Like other aspects of the Dark Web, separating out the noise and narrowing our focus is critical to understanding the nature of the threat. The following table illustrates a sample list of malicious services found on the Dark Web, and separates those services into national security and non-national security buckets:
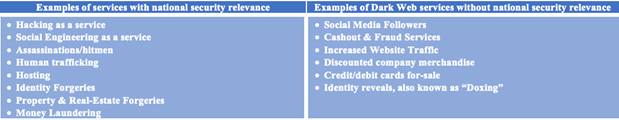
Table 4 – Malicious Services on the Dark Web
As stated in previous sections of this paper, organically developing and executing advanced cyber capabilities is no longer required for threat actors to pull off sophisticated attacks. Like the zero-day malware that has been re-purposed and sold on the Dark Web for profit, threat actors can now purchase malicious services for hire via Dark Web outlets. These outlets can be accessed through TOR and are scattered in various locations throughout the criminal underground. The following image is a screenshot from a “Rent-A-Hacker TOR website”:

Image 8: Rent-A-Hacker Landing Page47
Malicious services for hire allow threat actor groups with relatively low-level cyber capabilities to essentially pay their way towards the accomplishment of their objectives. This possibility could potentially explain how North Korea was able to rapidly accelerate the maturity of its cyberwarfare program over the last few years. Prior to the attack on Sony Pictures in 2014, North Korea was not considered a major cyber super power. Since then, a series of highly sophisticated attacks have been attributed to the North Korean government, to include the Wannacry Ransomware Attack, the SWIFT Network Bank Heist, high-profile cryptocurrency attacks, and a variety of other complex attacks.48 From very little capability pre-2014, to becoming one of the world’s most prominent cyber threats, there is a strong possibility that malicious services-for-hire played a significant role in the uptick in North Korea’s cyber capabilities. In the future, we assess that other state and non-state threat actor groups seeking to accelerate their cyber warfare capabilities may eventually turn to the Dark Web in order to acquire desired services.
Conclusion
This paper has conducted a review of how the Dark Web has affected national security to date and has discussed the potential means through which it may shape the evolution of national security threats in the years to come. Whereas the Dark Web is most well-known for hosting illicit economic trade, it has become clear that the Dark Web also holds some very serious national security implications that will affect most nations throughout the globe. The proliferation of cyber and kinetic weapons, the facilitation of terrorism, intelligence gathering, extortion, malicious services-for-hire à all of these illicit activities are occurring on the Dark Web, and the evidence put forth in this paper suggests that these activities may occur at increasing rates in the coming future.
Warfare has always and will always continue to evolve – it is therefore prudent for national security professionals to be aware of this evolution and familiarize themselves with the various technological intricacies that will continue to shape the evolution of warfare. The Dark Web, like other emerging technologies, is one of those technological intricacies. National security professionals reading this paper should consider how the discussed Dark Web threats could potentially affect their respective areas of responsibility. Moreover, it would be prudent to consider potential countermeasures and monitoring capabilities, such as Dark Web focused threat intelligence, that could be put in place to gain a better understanding of Dark Web related threats.
Whatever the means used to better understand this emerging threat, the overarching goal should be to produce an increased collective awareness amongst the national security community. We want to use this awareness to both reduce the possibility of strategic surprise, as well as to facilitate a predictive understanding of how our adversaries are likely to use the Dark Web in the course of their own malicious operations. And while though this awareness may not necessarily stop national security threats from the Dark Web, it can certainly shine a spotlight on the issue and facilitate a larger conversation on how the global community can address these emerging threats.
End Notes
[a] "What Is The Dark Web?", How-To Geek, 2016, https://www.howtogeek.com/275875/what-is-the-dark-web/.
[a] "Clearing Up Confusion - Deep Web Vs. Dark Web - Brightplanet", Brightplanet, 2014, https://brightplanet.com/2014/03/clearing-confusion-deep-web-vs-dark-web/.
[a] "I2P Vs. Tor Vs. VPN: Which Is More Secure?", Makeuseof, 2017, https://www.makeuseof.com/tag/i2p-vs-tor-vs-vpn-secure/.
[a] "What The Heck Is A TOR Exit Node?", Skeptical Science, 2017, https://www.skeptical-science.com/science/technology/heck-tor-exit-node/.
[a] The Tor Project, Inc, Torproject.Org, https://www.torproject.org/.
[a] Ibid.
[a] A virtual private network “is a technology that creates a safe and encrypted connection over a less secure network, such as the internet.” ("What Is VPN (Virtual Private Network)? - Definition From Whatis.Com". Searchnetworking. https://searchnetworking.techtarget.com/definition/virtual-private-network.)
[a] A virtual machine “is a software program or operating system that not only exhibits the behavior of a separate computer, but is also capable of performing tasks such as running applications and programs like a separate computer.” ("What Is A Virtual Machine (VM)? - Definition From Techopedia", Techopedia.Com, https://www.techopedia.com/definition/4805/virtual-machine-vm).
[a]Jona, Sam, "Cybercrime Revenue Estimated To Be $1.5 Trillion", Deep Dot Web, 2018, .ttps://www.deepdotweb.com/2018/05/05/cybercrime-revenue-estimated-to-be-1-5-trillion/.
[a] Cox, Joseph. "The Dark Web As You Know It Is A Myth", WIRED, 2015, https://www.wired.com/2015/06/dark-web-know-myth/.
[a] "What Is An Insider Threat? An Insider Threat Definition", Digital Guardian, 2018, https://digitalguardian.com/blog/what-insider-threat-insider-threat-definition.
[a] "Hacktivist | Definition Of Hacktivist In English By Oxford Dictionaries", Oxford Dictionaries, https://en.oxforddictionaries.com/definition/hacktivist.
[a] "Advanced Persistent Threat Groups | Fireeye", Fireeye, https://www.fireeye.com/current-threats/apt-groups.html.
[a]Ibid.
[a]Bogachev is the alleged Zeus Trojan author and is currently wanted by the FBI ("EVGENIY MIKHAILOVICH BOGACHEV", Federal Bureau Of Investigation, https://www.fbi.gov/wanted/cyber/evgeniy-mikhailovich-bogachev.)
[a]The Dark Overlord is a financially-driven individual that has extorted the healthcare sector and Netflix. (Cox, Joseph, "After Arrest In Serbia, Netflix Hackers ‘The Dark Overlord’ Say They’re Still Going", Motherboard, 2018, https://motherboard.vice.com/en_us/article/mbkex8/dark-overlord-arrest-serbia-netflix-hackers.)
[a]Edward Snowden was a US contractor that leaked classified information from the National Security Agency (NSA) in 2013. ("Edward Snowden", Biography, https://www.biography.com/people/edward-snowden-21262897.)
[a]Julian Assange is the creator of whistle-blowing website, WikiLeaks ("Julian Assange", Biography, https://www.biography.com/people/julian-assange-20688499.)
[a]Anonymous is a hacktivist group with global operations targeting governments and corporations through DDoS attacks (Geneva Sands, "What To Know About The Worldwide Hacker Group ‘Anonymous’", ABC News, 2016, https://abcnews.go.com/US/worldwide-hacker-group-anonymous/story?id=37761302.)
[a]LulzSec is a hacktivist group seeking to “gain attention” and “embarrass website owners”. (Charles Arthur, "Lulzsec: What They Did, Who They Were And How They Were Caught", The Guardian, 2013, https://www.theguardian.com/technology/2013/may/16/lulzsec-hacking-fbi-jail.)
[a]Barysevich, Andrei. "Military Reaper Drone Documents Leaked On The Dark Web", Recorded Future, 2018, https://www.recordedfuture.com/reaper-drone-documents-leaked/.
[a]Ng, Alfred. "Researchers Find Stolen Military Drone Secrets For Sale On The Dark Web", CNET, 2018, https://www.cnet.com/news/researchers-found-stolen-military-secrets-for-sale-on-the-dark-web/.
[a]"Stolen Drone Files Sold On Dark Web", BBC News, 2018, https://www.bbc.com/news/technology-44807091.
[a]"Cybersecurity Incidents", U.S. Office Of Personnel Management, https://www.opm.gov/cybersecurity/cybersecurity-incidents/.
[a]Hawkins, Derek. “The Cybersecurity 202: 'A wake up call.' OPM data stolen years ago surfacing now in financial fraud case”, The Washington Post, 2018, https://www.washingtonpost.com/news/powerpost/paloma/the-cybersecurity-202/2018/06/20/the-cybersecurity-202-a-wake-up-call-opm-data-stolen-years-ago-surfacing-now-in-financial-fraud-case/5b2924ca1b326b3967989b66/?utm_term=.68353aad1aba.
[a] Stone, Jeff. "The Dark Net Is Selling Hacked OPM Information, And It Could Be Worth $140M: Report", International Business Times, 2015, https://www.ibtimes.com/dark-net-selling-hacked-opm-information-it-could-be-worth-140m-report-1989911.
[a] "Kafr Qasem Resident Indicted For Financing And Purchasing Weapons For Terrorist On Dark Web", Deep Dot Web, 2018, https://www.deepdotweb.com/2018/12/01/kafr-qasem-resident-indicted-for-financing-and-purchasing-weapons-for-terrorist-on-dark-web/.
[a] Ibid.
[a] "Crypto Crowdfunding Terrorists: Marketplace For Jihadist Crowdfunding Found On Dark Web", CCN, 2018, https://www.ccn.com/crypto-crowdfunding-terrorists-marketplace-for-jihadist-crowdfunding-found-on-dark-web/.
[a] Zetter, Kim. "An Unprecedented Look At Stuxnet, The World's First Digital Weapon", WIRED, 2014, https://www.wired.com/2014/11/countdown-to-zero-day-stuxnet/.
[a] Warrick, Joby. “Iran's Natanz nuclear facility recovered quickly from Stuxnet cyberattack”, Washington Post, 2011, http://www.washingtonpost.com/wp-dyn/content/article/2011/02/15/AR2011021505395.html?noredirect=on.
[a] An exploit that exposes a vulnerability within an application, operating system, or information technology process that the cybersecurity community at large is unaware of.
[a] Osborne, Charlie. "The Dark Web Is The Place To Go To Find Bugs Before Public Disclosure | Zdnet", Zdnet, 2017, https://www.zdnet.com/article/the-dark-web-is-now-a-hotbed-of-zero-day-vulnerabilities/.
[a] C. Aliens. "More Details Revealed In The Dublin Explosives Case", Deep Dot Web, 2018, https://www.deepdotweb.com/2018/08/05/more-details-revealed-in-the-dublin-explosives-case/.
[a] “Taking Stock of the Online Drugs Trade”, RAND Corporation, 2016, https://www.rand.org/randeurope/research/projects/online-drugs-trade-trafficking.html.
[a] “International arms trade on the dark web”, RAND Corporation, 2017, https://www.rand.org/randeurope/research/projects/international-arms-trade-on-the-hidden-web.html.
[a] Williams, David. "Americans Will Soon Be Able To Legally Download 3-D Printed Guns", CNN, 2018, https://www.cnn.com/2018/07/19/us/3d-printed-gun-settlement-trnd/index.html.
[a] Note that sources as early as 2009 claimed that the cyber black market had surpassed the global drug trade.
[a] Callahan, Michael. “Hackonomics: A First-of-Its-Kind Economic Analysis of the Cyber Black Markets,” Juniper Networks, 2014, https://forums.juniper.net/t5/Security/Hackonomics-A-First-of-Its-Kind-Economic-Analysis-of-the-Cyber/ba-p/234262.
[a] Lau, Lynette. “Cybercrime 'pandemic' may have cost the world $600 billion last year”, CNBC, 2018, https://www.cnbc.com/2018/02/22/cybercrime-pandemic-may-have-cost-the-world-600-billion-last-year.html.
[a] Mazzetti, Mark; et al. "Killing C.I.A. Informants, China Crippled U.S. Spying Operations", The New York Times, 2017, https://www.nytimes.com/2017/05/20/world/asia/china-cia-spies-espionage.html.
[a] Ashley Madison is a popular extramarital dating site. ("Lessons To Be Learned From The Ashley Madison Data Breach", Panda Security Mediacenter, 2017, https://www.pandasecurity.com/mediacenter/security/lessons-ashley-madison-data-breach/.)
[a] Weise, Elizabeth. “Terrorists use the Dark Web to hide,” USA Today, 2017, https://www.usatoday.com/story/tech/news/2017/03/27/terrorists-use-dark-web-hide-london-whatsapp-encryption/99698672/.
[a]"Conversation between Dark Web vendor and an individual potentially affiliated with terrorism", Complaints Board, 2018, https://www.complaintsboard.com/complaints/fake-id-passports-fake-id-passports-c735014.html?page=2#comments/.
[a]Obtained from Dark Web market called “Dream Market”, where the vendor claims to sell a variety of document forgery services.
[a]Obtained from the vendor rating page in Dream Market which (judging by the number of ratings) indicates the successful sale of hundreds of forgery services.
[a] "Rent-A-Hacker Landing Page", InfoSec Institute, 2018, https://resources.infosecinstitute.com/hacking-communities-in-the-deep-web/#gref.
[a] "North Korea’s APT 38 hacking group behind bank heists of over $100 million", ZD-Net, 2018, https://www.zdnet.com/article/north-korea-s-apt38-hacking-group-behind-bank-heists-of-over-100-million/.
About the Author(s)
Comments
Here is my post, you have a…
Here is my post, you have a great way to watch movies on Kodi. That you enjoy all your favorite movies in your home comfort. With this simple step-by-step guide, you https://veepn.com/blog/how-to-watch-movies-on-kodi/ can start in no time. This guide will run through the basics of establishing and using Kodi to watch your movies. First, you have to download the Kodi app on your device
