Man, Computer, and Special Warfare
Patrick Duggan
“The confounded telegraph has ruined everything.”[1]
1855 Crimea--General Sir James Simpson
Man-machine teaming is inexorable and Special Warfare[2] needs a blueprint to transform along with it. With every passing day, our hyper-connected landscape spawns a new class of threats more technologically evolved than the last. These ‘hybrid-threats’ confound establishment-thinking seemingly more preoccupied with conflict typology, than the innovation of new organizational concepts to counter them. Success in warfare is not derived by labeling its assembled parts, it is achieved by correctly assembling emerging technology and new capabilities into trusted fields of practice. U.S. military culture must increasingly confront technology’s permutation of conflict, as great powers have contended since the ‘dawn of machines’ during the Crimean War. This paper serves as one step in a larger man-machine journey, and advances a conceptual framework to align technology, tools, and tactics for a new contemporary cyber-enabled Special Warfare practice. If successfully developed, this framework provides a mission-specific blueprint for the convergence of computers and man, and amplifies Special Warfare’s capabilities to counter future hybrid-threats and deny them growing technological advantage.
Hybrid-Hype
Hybrid-warfare has been complicated with umbrella labels ranging everything under the sun. It has been defined as a “combination of conventional, irregular, and asymmetric means, including the persistent manipulation of political and ideological conflict, and can include the combination of special operations and conventional military forces; intelligence agents; political provocateurs; media representatives; economic intimidation; cyber-attacks; and proxies and surrogates, para-militaries, terrorist, and criminal elements.”[3] The examination of hybrid-warfare has fueled spirited debate and spurred numerous papers over its characteristics, purpose, and parts; and no doubt, will continue for some time.
However, the truth is, hybrid-warfare is nothing new. It has, and always will be, a hodgepodge of previously labeled conflicts fused together by technology in unexpected ways. Hybrid-warfare is an asymmetric grab-bag of tricks that converges old and new technology and tactics to open new ‘attack surfaces’ against an adversary. Simply put, “the evolving character of conflict that we currently face is best characterized by convergence.”[4] Hybrid-warfare’s phenomena has only seemed to surge as a result of the tightening interaction between humans, the physical world, and cyberspace, whose connections produce a new class of threats increasingly adept in merging man and machine in a ‘cybered’ world. Powered by the steady proliferation, sophistication, and affordability of technology, hybrid-warfare is a useful means to inflict disproportionate harm against an opponent, relative to the size, resources, or geography of an adversary. Today, every country, non-state actor, or super-empowered individual can increasingly harness hybrid-warfare as a means to pursue their goals.
The most daunting challenge to hybrid-warfare is keeping pace for how fast adaptive adversaries are using the explosion of technology, information proliferation, and network connectivity for warfare. Their blistering speed in merging man and machine threaten US military advantages, and in some cases, outstrip our own innovation.[5] With an almost organic property to it, hybrid-warfare is in a state of perpetual change; and so long as technology continues to constrict the space between humans, the world, and cyber, its velocity will increasingly outpace a man’s ability to process, respond, and counter on his own.
Unfortunately, technology does not lift the fog and friction of war, technology clutters it. Technology does not lead to more antiseptic conflicts, but instead, to messier, more complex, and ambiguous ones. Technology provides adversaries more lethality and precision, and empowers them with new innovative ways to obfuscate, circumvent, and obviate previous limitations for doing it. Simply put, “technology does not make war more clinical; it makes it more deadly.”[6] Furthermore, US cutting-edge technology is used by adaptive adversaries to open new ‘attack surfaces’ against US vulnerabilities and push the limits of warfare norms and accepted conventions. Ironically, America may find itself a double victim of its own advanced technology; first, by failing to innovate sufficient new concepts for technology in conflict, and second, by failing to deny adaptive adversaries new technological advantages.
Human-Machine Teaming
The Department of Defense (DoD) is urgently exploring the future of human-machine teaming to spur new thinking and research on the changing character of warfare and the “types of new systems, organizations, and operational concepts needed to conduct it.”[7] The over-arching goal of DoD’s efforts is to create new paradigms, where machines and humans are “joined at the hip in a symbiotic relationship where each brings what it does best.” [8] Activities range from the experimentation of new technology, to rethinking organizational and operational force structures and tactical application. The “Third Offset Strategy is designed to create new advantages” over evolving-threats and explores promising technology like; advanced computers, big-data, robotics, artificial intelligence, semi/autonomous systems, and other cutting-edge technologies.[9] Ultimately, the Third Offset strategy is all about staying ahead of ‘hybrid-threats’ bent on the frustrating exchange of technology, tools, and tactics.
Each military service is exploring their own options for human-machine teaming and are questioning their own combat methods for fusing human-based strategic-thought with computer based tactical-acuity.[10] Ideally, the services must combine the precision and reliability of computers with the creativity and flexibility of humans.[11] Computer assisted human operations require the development of a common language which ties humans and technology to service specific lexicon, and must be accomplished in a simple way, using clear terms bound to missions and activities that resonate with commanders. Merging man with computers is not a technology thing, but rather cultural and organizational issues, which are vastly more challenging than just implementing things.[12] Excelling in the challenge requires each service to individually tailor organizational concepts that are true to their culture and amplify their specific missions.
Fortunately for the US, although adaptive threats may reverse engineer American technology, they can’t easily copy its greatest strength, its people and creativity. As recently expressed by Deputy Secretary of Defense Robert Work, “The human element is the secret sauce—the element that foreign powers can’t copy as easily as they can our software.”[13] When it comes to the race to merge man and machine, the competition depends upon harnessing the US’s two key advantages, its people and ingenuity, to assemble “the pieces of future military power better and faster than our rivals.”[14] Unfortunately for the US, there is an overall lack of man-machine concepts to merge technology in conflict, and this is a significant barrier for remaining competitive against adaptive adversaries.[15] More mission-specific concepts are needed across DoD, to include specialized missions like, Special Warfare, Irregular warfare, Counterterrorism, and Counterinsurgency, which “must also be updated to account for adversaries armed with advanced weaponry.”[16]
So the question for Special Warfare is, how do we assemble “the pieces of future military power”[17] into a framework that provides a culturally compatible mission-specific blueprint for computers and man? And then, how does Special Warfare use a growing-array of cyber-technologies like; wearable electronics, the Internet, social media, cyber-tools, and digital devices, to create new vulnerabilities and advantages against an adaptive enemy?
Crimean War--Dawn of Machines
Considered the first ‘Modern or Industrial War,’ the Crimean War (1854-1856) was allegedly fought by Britain and France to check Russian expansion into the Ottoman Empire. Less historically debatable, but perhaps more meaningful, the Crimean War also served as the backdrop for numerous wartime ‘firsts’ for machines invented during the Industrial Revolution era. The Industrial Revolution had produced more machines with wartime application than armies of the day “knew what to do with”[18] and included; steam powered trains and iron clad ships, breech loading and rifled canons, ‘minie’ bullets for rifled muskets, cameras, the telegraph, and many more. The new technology, coupled with industrial scale mass-production, impacted great and small Armies alike. Simply put, post-Napoleonic era militaries found themselves awash during the dawn of machines with a deficit of new wartime concepts, not unlike today.
An ancestor to modern-day computers, the telegraph’s first use in combat was during the Crimean War;[19] and today, is remembered more for its war-journalism impacts than any tactical benefit. Bemused by the novelty, commanders had not anticipated or adequately prepared for the telegraph’s military potential. Labor intensive and problematic, the British telegraph’s “gutta-percha insulated lines” had to be laid by plow when ground and weather permitted, and were frequently and easily broken.[20] Lacking telegraphy concepts or specialized military forces prior to the war, the British Army relied on private sector expertise for battlefield training.[21] By the end of the war, the British had still not fully embraced the telegraph’s potential for revolutionizing tactical communications, as they organizationally grew from zero to only one Telegraph Detachment and eight Field Stations,[22]and culturally, Commanders still preferred couriers for a primary means of communication. Even the 300 miles of cable which ran from Varna Bulgaria to Balaclava Crimea to connect the war to European circuits wasn’t submerged until April 1855, only after private industry convinced British and French government and military officials to submerge the telegraph cables.[23] It wouldn’t be until 1863, until the British Army standardized its telegraph equipment and tactics.[24]
Much to military commanders’ dismay, the telegraph’s most auspicious use was to connect the front to European audiences,[25] where bureaucrats and politicians micromanaged their field Armies with incessant questions, suggestions, and orders from afar.[26] “This was a substantial change in military strategy, and many tacticians lamented how the battlefield had become prone to interference by armchair warriors back at home.”[27] Frustrated by the lack of perceived constructive use, other than “constant pestering from London,” the British Commander-in-Chief General Sir James Simpson famously quipped “the confounded telegraph has ruined everything.”[28]
Fueling commanders’ frustrations, newspaper war-correspondents used the Victorian Internet[29] to turn the Crimean War into “the first war in history to be the subject of daily reports from the fighting front.”[30] The telegraph’s rapid affront to military culture was a result of its natural tendency to centralize the conduct of the war, and resulted in a rift between military commanders on one hand and the “politicians, the war correspondent, and public opinion” on the other.[31] This growing divide led to another British Officer, Sir William Simpson, famous for painting the Charge of the Light Brigade, to deride wartime journalists as “the curse of modern armies.”[32] In short, the telegraph was more of a nuisance to the Armies of the day than a benefit.
“The Industrial Revolution was itself an information revolution,” and during the Crimean War, military organizations struggled to conform, adapt, and manipulate this new warfare environment, “just as militaries are striving to do today.”[33] A key lesson as history moves forward, is that “those militaries that took best advantage of the new technologies of the industrial age were not those that acquired the machines or weapons first, but those that recognized the broader informational implications and strove to organize themselves accordingly.”[34] Meaning, the dawn of machines in Crimea still symbolizes the cultural and organizational difficulties nations experience when new technologies are introduced in battle, but also urge the US to vigorously adapt, if it’s to succeed in today’s man-machine competition.
The Cyber-Enabled Special Warfare Pyramid
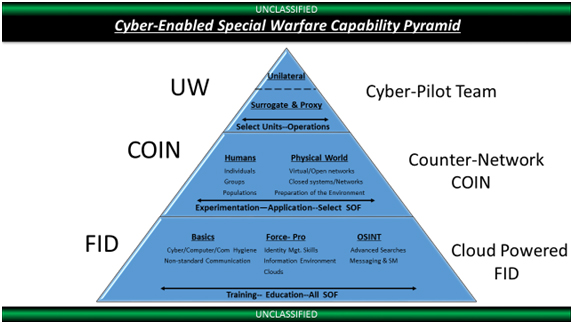
Figure 1. Cyber-Enabled Special Warfare Pyramid
What is it?
The cyber-enabled Special Warfare (CE-SW) pyramid is a conceptual construct that organizes reinforcing blocks of capability into three levels that are aligned to the three core missions of Special Warfare; Unconventional Warfare[35], Counterinsurgency[36], and Foreign Internal Defense.[37] The pyramid integrates technology, tools, and tactics into increasingly more advanced capabilities that support the three concepts of cloud-powered FID, Counter-network COIN, and UW Cyber-Pilot Teams.[38] The CE-SW pyramid aids “in identifying the new core tactical competencies, operational and organizational constructs and combat systems needed to survive and thrive in a cyber-environment”[39]and organizes capabilities in a manner to exploit closed and wireless computer networks with cyber electro-magnetic activities.[40] Analogous to computer programming or ‘chunking,’ the CE-SW pyramid breaks down information (or training) into chunks, then arranges the chunks into blocks of capabilities which enable a specific function (or mission). The CE-SE pyramid begins at the base with cyber-technology skills, education, and training, which are the foundation for building higher levels.
Theory
The fundamental theory underpinning all cyber-enabled Special Operations is about leveraging cyber-technology’s asymmetry to amplify the elemental aspects of what makes a special operation, special. Meaning, if correctly applied, cyber-technology amplifies a Direct Action mission’s lethality, precision, and discreet nature; while in Unconventional Warfare’s case, cyber-technology would amplify its ambiguity, deception, and resiliency. The “human element” is the glue that holds the pyramid’s capabilities together and is the guiding principle for any man-machine arrangements. To be successful, the pyramid must be applied in manner that exemplifies the first SOF truth, “Humans are more important than hardware.”[41]
Form
There are three levels to the pyramid which correspond to the three major missions of CE-SW; cyber-enabled Unconventional Warfare (CE-UW), cyber-enabled Counterinsurgency (CE-COIN), and cyber-enabled Foreign Internal Defense (CE-FID).
The CE-FID level primarily focuses on education and training for all practitioners and serves as the foundation for all CE-SW missions. This level’s capabilities are divided into three major categories; the Basics, Force-Protection, and Open Source Intelligence. Each major category is further subdivided into sub-categories. The Basics has two sub-categories; Cyber, Computer, and Communication Hygiene, and Non-Standard Communications. In the middle, Force Protection is divided into three sub-categories; Identity Management Skills, the Information Environment, and Clouds. On the right, Open Source Intelligence is divided into two sub-categories; Advanced Searches, and Messaging/Social Media Fundamentals. Within each subcategory, there are numerous tools, technology, and skills which are sequenced to build reinforcing blocks of capability to support all other missions.
As an example, CE-FID would train practitioners on cheap, low-visibility, and indigenous devices which could be employed across the globe to help monitor “weak signals of social change” and “provide early indicators of danger or unrest.”[42] CE-FID would educate practitioners on using simple commercial devices, like a Rasberry-Pi, to run a wide-array of communication, command and control, mapping, and meshed devices to network partners ‘off the grid,’ where there’s little or no electricity, services, or power, as well as, the employment of non-standard devices to build mutual trust and interoperability through habitual ‘telepresence’ activities. Finally, CE-FID would train practitioners on methods for reacting to those “early indications of danger or unrest” so that they could enable foreign partners via remote virtual access kits in activities or locations where US involvement is problematic.
CE-COIN is more heavily focused on experimentation and conflict application for select SW practitioners. This level is divided into two major categories; Humans, and the Physical World. On the left, the Humans category is further divided into three sub-categories; Individuals, Groups, and Populations. On the right, the Physical World category is divided into three sub-categories: Virtual Systems and Open Networks, Closed Systems and Networks, and Preparation of the Environment Activities. Within each subcategory, there are tools, technology, and experimentation efforts deliberately sequenced to build reinforcing blocks of capability that support CE-COIN and CE-UW missions.
As an example, CE-COIN would train practitioners on how to employ UAVs to monitor, engage, and disperse crowds as part of cyber-enhanced population control measures. It would also educate practitioners on how to build and leverage crowdsourced, geo-tagged, and non-standard databases for micro-security operations.
Finally, CE-UW is more heavily focused on select units and clandestine operations. This level is the highest level of cyber-enabled capability and is divided into two major categories; Surrogate and Proxy operations, and Unilateral operations. Within each category there are several subcategories which bring together all earlier tools, technology, and training into the penultimate of strategic SW capability.
As an example, CE-UW would train SW practitioners on how to leverage 3-D technology and additive manufacturing to support resistance movements for a whole host of activities. The CE-UW level would educate practitioners on how to utilize 3-D prints like; computers, weapons, munitions, engines, UAVs, and IEDs, as well as, other possibilities being unlocked every day.
New Practice
The CE-SW pyramid borrows under-utilized tactics, capabilities, and tools from previously labeled conflicts, and unexpectedly fuses them together to open new ‘attack surfaces’ against an adversary. The new opportunities target humans, networks, and narratives in decentralized and disaggregated operations and uses a mix of both virtual and physical practice. Some examples follow:
Humans: CE-SW can target the life-blood of an adversary and erode human means for survival by disrupting financial sectors, private enterprises, government-backed corporations, and illicit economies. CE-SW can be used to slowly degrade the adversary’s quality of life through long-term, low-grade, and persistent “financial-insurgency” tactics “rather than quick, high-profile battles with decisive results.”[43] CE-SW can manipulate critical good prices, employ preclusive purchasing, [44] and combine other economic warfare tactics to disrupt an adversary’s every-day life.
Narratives: CE-SW can use information and psychological means as a coercive tactic to change, modify, and punish an adversary’s behavior. Whether coordinating sit-ins, directing “swarm stream attacks,”[45] or spreading social media whisper campaigns, CE-SW can use “cyber-smash mouth tactics”[46] to amplify its physical and virtual activities. CE-SW can vet and leverage sympathetic ‘privateers’, vigilante, crowd-sourced, as well as, employ false flag efforts to “create believable deceptions in cyber-space over a protracted period of time.”[47]
Networks: CE-SW can employ human, informational, physical, and intelligence networks to compromise the confidentiality, integrity, and availability of an adversary’s networks. CE-SW can access open network systems with suites of cyber-tools and penetrate closed network systems, like precision guided military weapons platforms. CE-SW can actively monitor private sector advancements to improve cyber-technology UW concepts, and deny adaptive adversaries technological advantage through counter-UW constructs.
Conclusion
This is a hyper-connected world producing increasingly adaptive and technologically-savvy ‘hybrid-threats.’ To remain competitive, the US must vigorously pursue new concepts which correctly assemble emerging technology and new capabilities into trusted fields of practice. As the telegraph’s use during Crimea signals, the integration of technology into conflict requires forethought about culturally compatible military concepts to organize around. The CE-SW pyramid serves as one step in that larger man-machine journey, and advances a conceptual framework to align technology, tools, and tactics for a new contemporary cyber-enabled Special Warfare practice. If successfully developed, this framework provides a mission-specific blueprint for the convergence of computers and man, and amplifies Special Warfare’s capabilities to counter future hybrid-threats and deny them growing technological advantage.
End Notes
[1] National Army Museum, “Field telegraph wire used during the Crimean War, 1855 (c).” http://www.nam.ac.uk/online-collection/detail.php?acc=1965-10-202-4 (accessed December 25, 2015)
[2] Special Warfare is a broad term that doctrinally covers a range and combination of Unconventional Warfare, Foreign Internal Defense and Counterinsurgency operations. Special Warfare activities involve both lethal and nonlethal actions executed by a specially selected force steeped in regional understanding that is trained to fight alongside indigenous elements in permissive, uncertain, or hostile environments. U.S. Department of the Army, Special Operations, Army Desk Publication 3-05 (Washington, DC: U.S. Department of the Army, August, 2012), 9
[3] Robert A. Newsome, “Why the US Needs a Strategy to Counter Hybrid Warfare,” DefenseOne.com, October 23, 2014, http://www.defenseone.com/ideas/2014/10/why-us-needs-strategy-counter-hybrid-warfare/97259/ (accessed December 25, 2015)
[4] Frank G. Hoffman, “Hybrid Warfare and Challenges,” Joint Forces Quarterly 52, (1st Quarter 2009): 34. http://ndupress.ndu.edu/portals/68/Documents/jfq/jfq-52.pdf (accessed December 25, 2015)
[5] Robert O. Work and Shawn Brimley, 20YY Preparing for War in the Robotic Age (Center for a New American Security: CNAS Publications, January, 2014), 20. http://www.cnas.org/sites/default/files/publications-pdf/CNAS_20YY_WorkBrimley.pdf (accessed December 25, 2015)
[6] Ibid., 9.
[7] Ibid., 9.
[8] Sydney J. Freedberg Jr., “Centaur Army: Bob Work, Robotics, & the Third Offset Strategy,” Breaking Defense, November 9, 2015, http://breakingdefense.com/2015/11/centaur-army-bob-work-robotics-the-third-offset-strategy/ (accessed December 25, 2015)
[9] Sydney J. Freedberg Jr., “Will US Pursue ‘Enhanced Human Ops?’ DepSecDef Wonders,” Breaking Defense, December 14, 2015, http://breakingdefense.com/2015/12/will-us-pursue-enhanced-human-ops-depsecdef-wonders/ (accessed December 25, 2015)
[10] Cheryl Pellerin, “Work: Human-Machine Teaming Represents Defense Technology Future,” DOD News, October 8, 2015, http://www.defense.gov/News-Article-View/Article/628154/work-human-machine-teaming-represents-defense-technology-future (accessed December 25, 2015)
[11] “Centaur Army: Bob Work, Robotics, & the Third Offset Strategy,” 1.
[12] Mark Pomerleau, “For the military, the Internet of Things isn’t about things,” Defense Systems, November 12, 2015, https://defensesystems.com/articles/2015/11/12/internet-of-things-dod-cartwight-csis.aspx?m=1 (accessed December 25, 2015)
[13] “Centaur Army: Bob Work, Robotics, & the Third Offset Strategy,” 1.
[14] Ibid., 1.
[15] Bryan Clark and Mark Gunzinger, Winning the Airwaves, Regaining America’s Dominance in the Electromagnetic Spectrum, (Center for Strategic and Budgetary Assessments: CSBA Publications, 2015), 39. http://csbaonline.org/publications/2015/12/winning-the-airwaves-sustaining-americas-advantage-in-the-electronic-spectrum/ (accessed December 25, 2015)
[16] 20YY Preparing for War in the Robotic Age, 21.
[17] “Centaur Army: Bob Work, Robotics, & the Third Offset Strategy,” 1.
[18] Patrick Murphy, “The Effect of Industrialization and Technology on Warfare: 1854-1878,” MilitaryHistoryOnline.com,1. http://www.militaryhistoryonline.com/general/articles/effectofindustrialization.aspx (accessed December 25, 2015)
[19]Christopher Sterling, Military Communications, From Ancient Times to the 21st Century (Santa Barbara, CA: ABC-CLIO, 2008), 441.
[20] Steven Roberts, “Telegraph at War 1854-1868,” Distant Writing, A History of the Telegraph Companies in Britain between 1838-1868, 2012, http://distantwriting.co.uk/telegraphwar.html (accessed December 25, 2015)
[21] Ibid., 1.
[22] Ibid., 1.
[23] Walter Peterson, “The Queen’s Messenger: An Underwater Telegraph to Balaclava,” History of the Atlantic Cable & Undersea Communications, July 14, 2015, 1. http://atlantic-cable.com/Cables/1855Crimea/ (accessed December 25, 2015)
[24] Ibid., 1.
[25] “Telegraph at War 1854-1868,” 1.
[26] Military Communications, From Ancient Times to the 21st Century, 441.
[27] Dwayne R. Winseck and Robert M. Pike, Communication and Empire, Media, Markets, and Globilazation 1860-1930, (Raleigh, NC: Duke University Press, 2007) 26.
[28] Emily O. Goldman, Information and Revolutions in Military Affairs, (New York, NY: Routledge, 2005), 61.
[29] Tom Standage, The Victorian Internet, (New York, NY: Bloomsbury, 2009), 1.
[30] George F. Botjer, Samuel F.B. Morse and the Dawn of the Age of Electricity, (Lanham, MD: Lexington Books, 2015), 52.
[31] Communication and Empire, Media, Markets, and Globilazation 1860-1930, 26.
[32] Mitchel P. Roth, Historical Dictionary of War Journalism, (Westport, CT: Greenwood Publishing, 1997), 72.
[33] Information and Revolutions in Military Affairs, 72.
[34] Ibid., 73.
[35] Army doctrine defines UW as “activities conducted to enable a resistance movement or insurgency to coerce, disrupt, or overthrow a government or occupying power by operating through or with an underground, auxiliary, and guerrilla force in a denied area.” U.S. Department of the Army, Special Operations, Army Desk Publication 3-05 (Washington, DC: U.S. Department of the Army, August, 2012), 9.
[36] Joint doctrine defines COIN as “comprehensive civilian and military efforts taken to defeat an insurgency and to address any core grievances.” U.S. Joint Chiefs of Staff, Counterinsurgency, Joint Publication 3-24 (Washington, DC: U.S. Joint Chiefs of Staff, November 22, 2013), I-2.
[37] Joint doctrine defines FID as “participation by civilian and military agencies of a government in any of the action programs taken by another government or other designated organization to free and protect its society from subversion, lawlessness, insurgency, terrorism, and other threats to its security.” U.S. Joint Chiefs of Staff, The Department of Defense Dictionary of Military and Associated Terms, Joint Publication 1-02 (Washington, DC: U.S. Joint Chiefs of Staff, June 15, 2014), 103.
[38] Patrick Duggan, “Strategic Development of Special Warfare in Cyperspace,” Joint Forces Quarterly 79, (4th Quarter 2015): 49-52. http://ndupress.ndu.edu/Media/News/NewsArticleView/tabid/7849/Article/621123/jfq-79-strategic-development-of-special-warfare-in-cyberspace.aspx (accessed December 25, 2015)
[39] 20YY Preparing for War in the Robotic Age, 20.
[40] Winning the Airwaves, Regaining America’s Dominance in the Electromagnetic Spectrum, 3.
[41] United States Army Special Operations Command, http://www.soc.mil/USASOCHQ/SOFTruths.html (accessed December 25, 2015)
[42] Patrick Tucker, “These are the Decisions the Pentagon wants to Leave to Robots,”DefenseOne.com, December 14, 2015, http://www.defenseone.com/technology/2015/12/these-are-decisions-pentagon-wants-leave-robots/124480/ (accessed December 25, 2015)
[43] Hudson Institute, Cyber-Enabled Economic Warfare: An Evolving Challenge (Washington, DC: Hudson Institute, 2015), 98. https://s3.amazonaws.com/media.hudson.org/files/publications/2015.08CyberEnabledEconomicWarfareAnEvolvingChallenge.pdf (accessed, December 25, 2015)
[44] Ibid., 52-53.
[45] Patrick Duggan, “Harnessing Cyber-technology’s Human Potential,” Special Warfare 28 , no.4 (October-December 2015), 15. http://www.soc.mil/swcs/SWmag/archive/SW2804/October%202015%20Special%20Warfare.pdf (accessed December 25, 2015)
[46] Ibid., 15.
[47] Robert Schultz, “Countering Extremist Groups in Cyberspace,” Joint Forces Quarterly 79, (4th Quarter 2015): 55. http://ndupress.ndu.edu/Media/News/NewsArticleView/tabid/7849/Article/621124/jfq-79-countering-extremist-groups-in-cyberspace.aspx (accessed December 25, 2015)
About the Author(s)
Comments
The Community-Driven…
The Community-Driven Education is the best to help us and provide great results. The Project Ownership Where it Belongs is amazing and I like that you shared this post for us to know about these ideas. Also from Fortinet NSE6_FAC-6.4 Valid Questions Answers I realize that it is more helpful for us.
I find the framework helpful in developing some initial ideas on integrating cyber to facilitate SOF operations (and vice versa). Hopefully, SOCOM will expand the framework to include the full spectrum of special operations to include SR and DA. Ultimately, the biggest challenge will be overcoming the inertia of our procurement bureaucracy, to ensure we can evolve as fast as technology evolves. I suspect we would not keep up with the Red Queen with our current overly centralized systems. I suspect by the time we purchase and field a capability it will be outdated, or sub competitive compared to what our adversaries are using, and how they are employing it.
