Free Wi-Fi & Security: Why It Matters
James Torrence
The internet is an essential part of both personal and professional life. People use the internet to complete tasks ranging from banking to buying groceries. Organizations use the internet to afford their employees access to networks/information whether in the office, working from home, or working on-the-move. In order to accommodate the growing need for internet access, there has been a 4,414 percent increase in the number of Wi-Fi hotspots in the United States since 2013 (Covington, 2016). There are roughly “54 million Wi-Fi hotspots” (Covington, 2016) in 2016, with the number growing daily. The increase in internet availability creates more opportunities to be connected if one is outside the home or office, has limits on cell phone data, or is out of cellphone coverage. Though there are more opportunities to be connected, there are also more risks; public Wi-Fi is inherently insecure. David Maimon, Associate Professor of Criminal Justice at University of Maryland, sums it up as follows:
The major hazard with public Wi-Fi is the fact that all the information you’re transferring between your computer and the computer that you’re accessing is available to everybody on the network (Hill, 2015).
The risks of Wi-Fi hotspots are compounded when users do not understand how Wi-Fi networks work, and thus do not comprehend the risks associated with connecting to a free hotspot. In a 2016 study, it was determined that “the level of ignorance” (Schlesinger, 2016), with regard to the understanding of free Wi-Fi networks, is “somewhat alarming” (Schlesinger, 2016), and that “more than 60% of consumers think their information is safe when using public internet…” (Schlesinger, 2016). This is an important topic not just because of ramifications of personal information that could be exposed, but also for organizations whose employees access organizational information on networks that are not secure. It is evident that a new method of educating and informing employees about the dangers of free Wi-Fi is necessary to help protect both personal and organizational information. The author will put forth a framework that can be integrated into existing employee ecosystems, augment existing policy, and better protect organizational and personal information. Before introducing the framework, it is first necessary to understand why public Wi-Fi is insecure, why the problem will continue to persist, and how organizations can successfully implement a new framework.
Why Public Wi-Fi is Insecure
Public Wi-Fi has a number of risks, with the two most prevalent being: man-in-the-middle attack (MitM), and packet sniffing. MitM attacks (shown in figure 1) occur when attackers put “together their own network” (Hill, 2015) and stand “between your computer and the computer you’re trying to access and all the information is routed through their device” (Hill 2015). The attacker acts as a voyeur into one’s digital transactions and, once they have established their MitM position, they can watch all information that is passed from a person’s computer to the free Wi-Fi router (see figure 1).
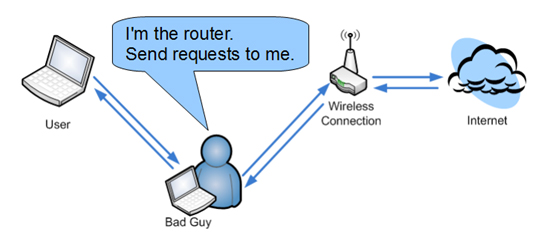
Figure 1. Man-in-the-Middle Attack
An excellent example of an ethical MitM attack occurred in September, 2016, when a British magazine, The Mirror, invited an ethical hacker (Rob Shapland) to reveal the secrets of one of its investigators (Farhoud, 2016). The investigator logged onto a network in a café she thought was legitimate, but Shaplan had created the network with a similar name to the café, and then routed the traffic back through the café Wi-Fi (just like Figure 1 depicts). This meant that he had established a MitM connection, and could begin monitoring all of the investigator’s internet activity. Shapland, after the investigator logged onto the faux Wi-Fi network, said the following:
…by intercepting this page I had a mirror image of what was being inputted in real time including passwords and credit card details which a criminal would save for later use (Farhoud, 2016).
The investigator logged onto banking, social media, and travel websites during her time in the café, and had no idea she was being monitored. It was evident that, had he been a criminal, Shapland could have cleared her bank account, created a running log of all the passwords she used, and done as much damage to her as he desired. MitM attacks are one of the more common forms of intrusion on free Wi-Fi networks and need to be understood by users to ensure they take proper precautions.
Packet sniffing involved the monitoring of information being sent to a Wi-Fi hotspot. When conducting sniffing, “attackers record huge swathes of data as it travels across the network and then analyze it later to uncover useful details” (Hill, 2015). The interesting thing about packet sniffing “is that it’s not even illegal to sniff through packets a lot of the time” (Hill, 2015). Obtaining the tools to conduct Wi-Fi sniffing is easy, and after installing them it is possible to see what anyone connected to the free Wi-Fi network is doing. The author decided to test out the complexity of Wi-Fi sniffing on his home network. The author of this article downloaded packet-sniffing software, Wireshark, and installed it on his home computer. The software download took approximately five minutes, after which the author read the instructions for installation. After five minutes of reading, the author scanned his home wireless network and was able to track all of the data going between his devices and his wireless router. The author was able to go from no background on packet sniffing to sniffing his home network within 15 minutes. The data that is captured by packet-sniffing software needs to be synthesized, but it is alarming how easy it is to obtain that data with a computer and a public internet connection.
The Need for Secure Connections Will Only Grow Stronger
Researchers estimate that “by 2020, the number of active wireless connected devices will exceed 40 billion” (Dickson, 2015). The IoT is in its infancy, and the ability to be connected to anyone and anything will continually increase. Concurrently, BYOD implementation in organizations “has been estimated at anywhere between 67 and 95 percent” (Jarrett, 2016,) and “employees are checking email on the go and accessing CRM software outside the office, all on their own devices” (Jarrett, 2016). There is continual blurring of personal and professional lines when it comes to communication, and having multiple devices (personal and work) can be inefficient and decrease productivity. Companies that embrace BYOD and IoT integration “are seeing a significant increase in productivity, clearer business activity and reduced infrastructure costs” (Jarrett, 2016). BYOD and IoT are not going away, and it is necessary to understand the associated security risks with their integration, and why secure connections will continue to be important for securing organizational information.
In a study conducted by Ovum, “17.7 percent of survey respondents who bring their own devices to work claim their employer’s IT department has no idea about this behavior” (Meyer, 2016), and “28.4 percent of IT departments actively ignore BYOD behavior” (Meyer, 2016). It is evident that “many business owners aren’t aware of their employee’s mobile usage, and don’t understand the security risk a BYOD policy may carry” (Jarrett, 2016). The risks posed by uneducated users (or organizations) that don’t fully understand BYOD implications is very high. This isn’t to say that it’s impossible to implement an effective BYOD policy, but that the switch to BYOD in the workplace is outpacing effective education and policy, and thus creating constant security risks.
Compared to IoT devices, BYOD seems very secure because at least it is recognized that organizations should have a policy or process in place to help secure devices (whether they do it or not is another story). It is much easier to grasp security associated with a phone or computer than the number of IoT devices that could compromise one’s personal or professional information. Wearables (devices that attach to the body augmented by technology) can be a major threat to one’s privacy because:
…hackers can use the motion sensors embedded in smartwatches to steal information when you’re typing, or they can gather health data from smartwatch apps, or health tracker devices you might be using (Dickson, 2015).
Organizations could have the best BYOD policy in the world, and could still potentially be compromised by someone wearing a smartwatch, fitness tracker, or other type of wearable that isn’t covered in a BYOD policy. There is a potential for smart sole inserts which could, in a secure facility, be hacked to show different locations in the facility that would normally not be common knowledge. This information is intimidating but important for organizations and people to understand when they are trying to secure their data. There are a number of benefits to incorporating BYOD policies and integrating IoT devices into the workplace. It is necessary, after implementing such policies and devices, to understand associated risks and develop an adaptable framework that can counter current threats, and react to future threats without being obsolete. The framework needs to take into account IoT devices (not just BYOD) because of the potential risks assumed by the company for ignoring emerging IoT devices that can provide just as much data as a smart phone.
Foundations for Framework Implementation
Policies are only as effective as their implementation. BYOD and IoT policies cannot become another piece of paper that gets added to a mandatory policy binder. A BYOD/IoT policy needs to provide both information for protection, and a framework that is applicable to multiple scenarios. Current operational environments require the ability to work on both complicated and complex problems. Complicated problems are the easiest to manage because they have a finite number of factors and solutions, and can thus be addressed with a checklist or a specific set of rules. An example of a complicated problem would be the execution of a disaster recovery plan in the wake of a power outage; it is a challenging problem, but there is a known place for relocation, and a known amount of equipment moving to that location. An example of a complex problem would be fighting a counterinsurgency: there are multiple known and unknown ever-changing independent variables that cannot be neatly categorized into a set of rules or a checklist.
Organizations need to do three things in order to effectively implement an effective policy: develop a security baseline for BYOD/IoT devices that can be part of a checklist, ensure the new policy is incorporated into existing ecosystems, and create an accessible framework that their employees can use to navigate future threats. Developing a secure baseline should be proposed from the information technology department with approval from the c-suite. A secure baseline can take a number of forms, but it can be defined as the strongest form of blanket security devices must have in order to qualify for BYOD use. This could take the form of VPN installation, software upgrades, mobile encryption, or any other baselines the organization deems necessary for a security baseline.
Organizations need to understand how to implement policies into existing organizational infrastructure without adding more stress to their workers. In order for a policy to be successful, the organization needs to understand the ecosystem in which its employees operate. Once the ecosystem is understood, the employees can find a way to merge their new policy and follow-on framework with existing requirements, and avoid adding another mandatory requirement for employees who are potentially already overworked. An example of understanding the requirements of a worker is shown below in the form of some analysis the author did on a soldier in the United States Army:
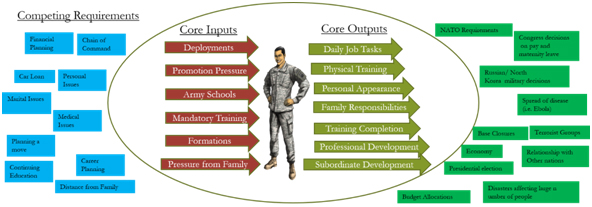
Figure 2. Demands on a Soldier's Time [Soldier Image Courtesy of U.S. Army]
If an organization takes the time to understand its employees’ requirements, and creates something like the diagram above, it will be much more likely to succeed with their implementation of a new policy and/or framework.
There is one more thing that an organization needs to take into account before creating a framework: the accessibility of the content. Accessibility needs to be taken into account for literal physical accessibility, intellectual accessibility, and visual accessibility. A framework needs to be accessible in each of these ways for employees to get the most effect out of its content.
Framework Proposal
The author doesn’t think it is necessary to layout a policy outline, but rather an adaptive framework. Information technology departments within organizations are more than capable of writing out a technical policy that details basic steps like applying a VPN, or installing a secure mobile application (there are many other steps, but information technology experts are adept at understanding those details). The author thinks the real challenge is injecting an applicable framework into the employee work cycle that can be used while accessing the internet for both professional and personal reasons. The framework is then used as a springboard to promote secure behavior, and to reference technical guidelines when the framework does not provide enough specific information. The framework is in place to be a constant reminder of best practices, and to continually reinforce the importance of organizational policies and procedures that the information technology and security departments (depending on the organization) work so hard to put together.
The framework consists of the word “AWARE” with the acronym consisting of the following steps: ask before connecting to free Wi-Fi, watch company videos on new cyber threats, assume everything you do on your device and wearable could be monitored, report any suspicious activity, and ensure you follow organizational policy when accessing company information in and outside of the office. The framework, depicted as a graphic, is below:
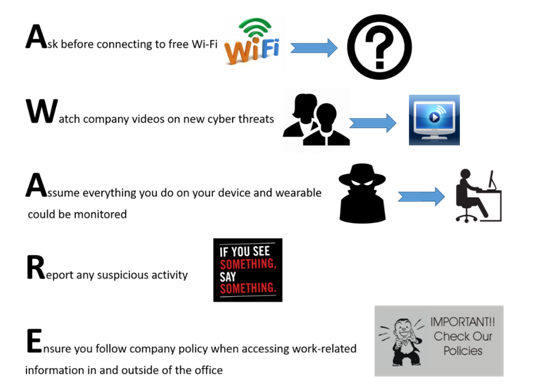
Figure 3. AWARE Framework
The goal of this framework is to provide guidelines that are applicable to multiple situations, and this framework is an excellent primer for uneducated users about cybersecurity. The framework can be presented differently by any company. Companies can implement the information, depending on what their research says about how their employees best receive information, in the following ways (this list is not all inclusive and serves as an example of some ways to display the framework):
- Poster displays
- Monitor backgrounds
- Display that appears when accessing the company’s mobile application
- Display that appears when accessing company information
- Wallet-sized card carried on one’s person
The framework, depending on the method of display, could have QR codes, hyperlinks, or other directions to provide more information each step.
The “AWARE” framework is meant to augment existing policies and create a better, accessible, security posture for employees outside of the office. The organization needs to determine the best existing programs into which they could introduce/inject this framework. In the military there are annual security awareness briefings that could serve as an excellent place to introduce the framework. It would then be the responsibility of leaders to continually reinforce the principles espoused in the framework.
Conclusion
Public Wi-Fi is dangerous, and people have not yet changed their wireless browsing habits to achieve the privacy they desire. BYOD and IoT integration are bringing more technology to the workplace, and the increase of Wi-Fi hotspots is creating more places where people can work outside the office. The current situation is a perfect storm for personal and organizational information to be compromised; the technology is outpacing the security required to keep information private. A new paradigm is needed, and should be one focused on frameworks that can be applied to multiple situations, while still being grounded in organizational policy. The “AWARE” framework was created with employees in mind, and is accessible to them on multiple levels. The “AWARE” framework should be injected into existing employee ecosystems, and continually reinforced by leadership. Employees need to be constantly educated, and they need something simple they can apply to multiple situations. The “AWARE” framework should be prototyped to determine its strengths and weaknesses, and then adapted to address specific organizational needs. It should be constantly challenged, updated, and re-instituted to ensure employees have the best information at their disposal to protect themselves and their information. Organizations should implement the “AWARE” framework, or similar version (assuming it is updated or tweaked for organizationally-specific tasks), to augment their policies, and give their employees the tools they desperately need to keep their personal and organizational information safe.
References
Covington, M. (2016, October 8). Free Wi-Fi and the dangers of mobile man-in-the-middle Attacks. Retrieved from http://betanews.com/2016/10/08/free-wi-fi-mobile-man-in-the-middle-attacks/
Dickson, B. (2015, October 24). Why IoT Security Is So Critical. Retrieved from https://techcrunch.com/2015/10/24/why-iot-security-is-so-critical/
Evans, D. (2015, October 7). What is BYOD and why is it important? Retrieved from http://www.techradar.com/news/computing/what-is-byod-and-why-is-it-important--1175088
Farhoud, N. (2016, September 1). Dangers of using public Wi-Fi revealed as cyber crooks can steal your ID when you use free hotspots. Retrieved from http://www.mirror.co.uk/tech/dangers-using-public-wi-fi-8750973
Hill, S. (2015, August 15). How Dangerous is Public Wi-Fi? We Ask an Expert. Retrieved From http://www.digitaltrends.com/mobile/how-dangerous-is-public-wi-fi/
Jarrett, P. (2016, September 12). Are BYOD policies putting your company at risk.Retrieved from http://www.director.co.uk/blog-byod-putting-your-company-at-risk-director-magazine/
Madden, M. & Rainie, L. (2015, May 20). Americans’ Attitudes about Privacy, Security, and Surveillance. Retrieved from http://www.pewinternet.org/2015/05/20/americans-attitudes-about-privacy-security-and-surveillance/
Meyer, C. (2016, April 1). Bring Your Own Risk with BYOD. Retrieved from http://www.securitymagazine.com/articles/87016-bring-your-own-risk-with-byod
Samson, A. (2015, October 21). Five Reasons Why We Compromise Our Privacy Online. Retrieved from https://www.behavioraleconomics.com/5-reasons-why-we-compromise-our-privacy-online/
Schlesinger, J. (2016, June 28). Most people unaware of the risks of using public Wi-Fi. Retrieved from http://www.cnbc.com/2016/06/28/most-people-unaware-of-the-risks-of-using-public-wi-fi.html
About the Author(s)
Comments
We're all guilty of it -…
We're all guilty of it - falling into the trap of making excuses for why we don't do things. In this life and business, as a creative person you work in a place where your creativity is encouraged but also needs nurturing and care. Let's get PureWL - White Label VPN to learn some tips about the vpns. Being prepared for unexpected things that may happen in our everyday lives is a vital part of being ready for any eventuality.
This really confirms once…
This really confirms once again that awareness is of great importance, and it is necessary to thoroughly study the issue before making a decision. For example, the review resource https://letsgradeit.com/review/gradesfixer/ helps me, so I can get a full description of online help and not make a mistake, this information immediately gives an understanding of the shortcomings and advantages of the service.
