Editor's Note: The critical strength of F3EAD is the fusion of operations and intelligence: a step toward more holistic thinking and flatter command and decision-making structures.
The views are the authors' and do not necessarily reflect those of the Army or Department of Defense.
Abstract: Find, Fix, Finish, Exploit, Analyze, and Disseminate (F3EAD), pronounced “F-three-e-a-d” or “feed,” is a version of the targeting methodology utilized by the special operations forces (SOF) responsible for some of the most widely-publicized missions in support of overseas contingency operations. F3EAD is a system that allows SOF to anticipate and predict enemy operations, identify, locate, and target enemy forces, and to perform intelligence exploitation and analysis of captured enemy personnel and materiel. Central to the F3EAD process is the functional fusion of operations and intelligence functions throughout the SOF organization. In F3EAD, commanders establish targeting priorities, the intelligence system provides the direction to the target, and the operations system performs the decisive operations necessary to accomplish the SOF mission. This paper explains the F3EAD process, examines how it is used by SOF and general purpose forces, and provides recommendations for its further implementation and inclusion into formal doctrine.
“Information and Intelligence” is the “Fire and Maneuver” of the 21st Century.
-Major General Michael Flynn, March 2011.
Find, Fix, Finish, Exploit, Analyze, and Disseminate (F3EAD), pronounced “F-three-e-a-d” or “feed,” is a version of the targeting methodology utilized by the special operations forces (SOF) responsible for some of the most highly-publicized missions in support of overseas contingency operations. F3EAD is a system that allows SOF to anticipate and predict enemy operations, identify, locate, and target enemy forces, and to perform intelligence exploitation and analysis of captured enemy personnel and materiel. Central to the F3EAD process is the functional fusion of operations and intelligence functions throughout the SOF organization. In F3EAD, commanders establish targeting priorities, the intelligence system provides the direction to the target, and the operations system performs the decisive operations necessary to accomplish the SOF mission.
The most significant aspect of F3EAD is the establishment of a true symbiotic relationship between the operations and intelligence warfighting functions. In F3EAD, operations constantly directs the overall intelligence effort, and intelligence in turn feeds operations with the information necessary to enable the successful accomplishment of the mission. This kind of synchronization is crucial because on the modern battlefield the two functions are becoming fused; indeed, some may now say that “intelligence is operations.” The goal of the operations/intelligence fusion and rapid pace of the F3EAD process is to enable commanders at all levels to plan and execute operations against the enemy faster than the enemy can react. When utilized successfully, the process allows SOF to get into the enemy’s decision cycle and simultaneously direct operations against several parts of the network. This results in the ability of friendly forces to dictate the operational tempo, and sets the conditions for the friendly operations.
F3EAD is a natural evolution of targeting, combining aspects of the conventional intelligence cycle and doctrinal operational planning with best practices and emerging tactics, techniques, and procedures forged in worldwide overseas contingency operations.
Although SOF is best positioned to utilize F3EAD due to their inherent organizational adaptability, specialized training, and unique resourcing, F3EAD is neither new nor unique to SOF. Indeed, conventional targeting doctrine now supports F3EAD as a part of the targeting process, and F3EAD has become part of the institutional training programs at places such as the Military Intelligence Officers Basic Course.
F3EAD in Conventional and SOF Doctrine
Some SOF units diverge from conventional doctrine in that a version of F3EAD is the exclusive targeting methodology in those units while conventional targeting doctrine as reflected in Field Manual 3-60 shows F3EAD subordinate to the legacy “decide-detect-deliver-assess” (D3A) process. The same manual also describes “Find, Track Target, Engage and Assess” (FT2EA). Looking at the doctrinal overlay of F3EAD into D3A (Figure 1, below), D3A looks almost superfluous because F3EAD can accomplish the exact same thing as D3A, while improving the overall targeting process by increasing the input of intelligence. If that is so, then it may make sense to replace D3A and FT2EA with F3EAD. Additionally, conventional doctrine also seems to focus almost exclusively on the manhunting or “High Payoff Target” (HPT) aspect of F3EAD. While F3EAD is indeed very well suited for manhunting and operations against HPTs, it is equally effective in other types of targeting, including those seeking non-lethal effects. Finally, while doctrine views F3EAD as a hasty decision process, many units utilize F3EAD in deliberate planning as well.
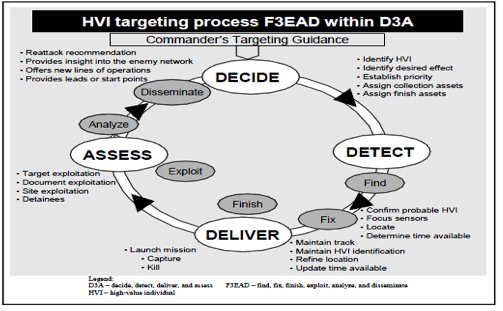
Figure 1: F3EAD as a Function of D3A. Source: FM 3-60.
There are some other important distinctions between the ways SOF and conventional forces implement F3EAD: 1) the degree to which the process is understood and implemented within the SOF community; 2) the emphasis placed on the process by SOF commanders, and 3) the degree success the process achieves for the SOF units who utilize it. In SOF units effectively utilizing F3EAD, operational leaders at all levels took responsibility for the intelligence effort, developing lines of communication and direct contact with the intelligence personnel supporting them at all levels throughout the intelligence community. This interaction allowed intelligence enablers to better understand and anticipate operational needs, and facilitated the development of useful, long-term professional relationships between intelligence and operations personnel. Additionally, units which successfully utilize F3EAD often possess organizational adaptability that facilitates the conscious incorporation of personnel, assets and capabilities that are not always considered as part of the warfighting enterprise. Specifically, the inclusion of law enforcement personnel and their investigative, forensic, and information-sharing capabilities were critical in the process of turning intelligence into evidence, which became more and more important in the non-lethal capabilities of F3EAD as the situations in Iraq and Afghanistan evolved.
The F3EAD Process
 The legacy models of “find-fix-finish” and “decide-detect-deliver-assess” were some of the earliest precursors to F3EAD. These lethal-targeting, operations-centric methodologies, when combined with a culture of adaptability, lessons learned from overseas contingency operations, and best practices from around the world, generated the next evolution in targeting methodology: F3EAD. Unlike other traditional targeting models and processes that focus on the operational or “finish” aspect, the main effort of F3EAD is the intelligence effort, specifically the “exploit-analyze-disseminate” portion. This allows F3EAD to be equally effective in lethal and non-lethal targeting, and is key to understanding the F3EAD process. It is useful to visualize the F3EAD process as a web, with the different elements of the process on the periphery, connected both directly to each other and to the fusion of the operations and intelligence systems, in the manner shown below. The cycle is continuous, but not necessarily congruous; steps can be and often are skipped or shortened in order for the process to keep up with the “speed of war.”
The legacy models of “find-fix-finish” and “decide-detect-deliver-assess” were some of the earliest precursors to F3EAD. These lethal-targeting, operations-centric methodologies, when combined with a culture of adaptability, lessons learned from overseas contingency operations, and best practices from around the world, generated the next evolution in targeting methodology: F3EAD. Unlike other traditional targeting models and processes that focus on the operational or “finish” aspect, the main effort of F3EAD is the intelligence effort, specifically the “exploit-analyze-disseminate” portion. This allows F3EAD to be equally effective in lethal and non-lethal targeting, and is key to understanding the F3EAD process. It is useful to visualize the F3EAD process as a web, with the different elements of the process on the periphery, connected both directly to each other and to the fusion of the operations and intelligence systems, in the manner shown below. The cycle is continuous, but not necessarily congruous; steps can be and often are skipped or shortened in order for the process to keep up with the “speed of war.”
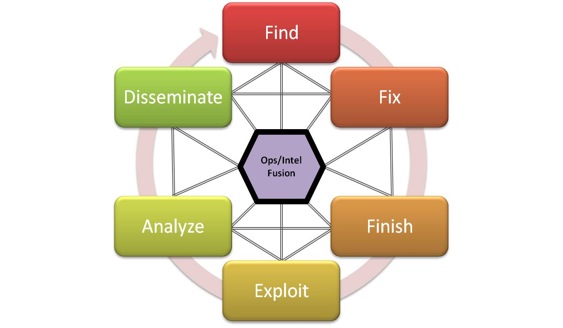
Figure 3: The F3EAD Process. Source: Authors.
Find
The “find” function of the process takes place at all levels of both the intelligence and operations systems, with both operations and intelligence personnel intimately involved in the effort. In simplest terms, the find component of F3EAD is the process of establishing a start point for intelligence collection. These start points often take the form of target nominations, which can be generated internally by individual units or can be directed from external headquarters. After receiving planning guidance from the commander and operations planners, F3EAD practitioners employ the full range of intelligence capabilities from organic, to national, and sometimes even to international assets to get a starting point for the rest of the process. The targeting start point can be deliberate or opportunity-based, and can focus on a known personality, a facility, an organization, or some other type of signature.
Fix
Once a target is identified, the full gamut of intelligence collection capability is applied against the target in order to develop operational triggers to “fix” the target in space and time. Fixing a target simply means that the intelligence effort has progressed enough that the operations function has sufficient information to execute the mission, whether that mission be kinetic or non-kinetic. When possible, SOF utilizes a practice of “federating” or spreading the intelligence effort out amongst multiple agencies in order to maximize effects while minimizing costs, effort, and time. This is often done as far forward as possible in order to increase the speed of the process, but much of the effort can be accomplished via reachback. Federated intelligence processes enable the organization practicing F3EAD to spread the collection effort across the IC, calling on specific organizations and in some cases specific personnel to provide the expertise and capability to bring the process into the “finish” phase. Redundant, persistent, and centralized intelligence, surveillance and reconnaissance (ISR) capability allows commanders to mass ISR against a specific target for the period of time necessary to support F3EAD. The goal of an ISR is to provide an “unblinking eye” squarely focused on the target, to bring the targeting process into the decisive next phase.
Finish
The first two steps of F3EAD lead to decisive operations against the enemy. Lethal combat operations in which SOF or their surrogates close with and destroy or seize enemy facilities, equipment, or personnel are one type of operation associated with the finish phase. However, the finish phase can just as easily be non-kinetic in nature. Neutralization of an enemy communications node, disrupting a courier network, legal prosecution of key terrorist personalities, or achieving a desired psychological, political, or social effect are just as much a part of “finish” as missile strikes or combat assaults. Therefore, in F3EAD, finish refers more to finishing a particular mission, than finishing enemy forces.
Under legacy targeting methodologies, the finish phase was considered the main effort. This made sense in prior wars which were focused more on physical destruction of enemy forces and infrastructure as a means to end his will to resist. However, in an information-age era of protracted conflicts, risk aversion, non-state actors and networked warfare, the main effort cannot be on “finishing” enemy forces in a traditional sense, in large part because the nature of warfare has changed. Therefore, F3EAD does not end in the finish phase; indeed, with “finish,” the main effort of F3EAD is just beginning.
Exploit
The “exploit” phase, as the main effort of F3EAD, is the most critical single step in the process as it leads to the finding, fixing, and finishing of the next target and the perpetuation of the cycle. Exploitation also best fulfills the main purpose of intelligence, which is to enable “decision advantage” for decision-makers at all levels. In the F3EAD model, exploitation is the process of examining, analyzing, interrogating, and processing captured enemy personnel, equipment, and materiel for intelligence purposes.
The overall aim of the exploitation effort is to produce enough actionable intelligence and/or prosecutorial evidence to perpetuate the F3EAD process as rapidly as possible. In support of this aim, exploitation has four broad goals: force protection, targeting, component and material sourcing, and prosecution. (McIntyre, Russell, “Criteria for a Successful Theater Exploitation Effort,” 19 September 2009) Exploiting captured enemy personnel and materiel for force protection purposes allows operations and intelligence to function together in order to prevent enemy attacks on friendly forces, installations, and capabilities. Targeting allows friendly forces to engage enemy forces, installations, and capabilities in order to achieve lethal or non-lethal effects. Component and materiel sourcing allows intelligence personnel to backtrack sources of enemy personnel and materiel, thereby enabling friendly forces to engage the enemy across his network. Finally, exploitation enables prosecution of enemy forces after they and their materiel have been fully exploited for intelligence purposes. This represents another fundamental evolution in warfare, since prior to the current Overseas Contingency Operations, prosecution was most often associated with events that occurred after a conflict was resolved, not during hostilities. By including prosecution as a part of the overall exploitation process, practitioners of the F3EAD process allow friendly forces to then turn intelligence into evidence, enabling successful legal prosecution of enemy forces, and ensuring that both the population and friendly forces are protected. This is particularly useful in the kind of “adaptive, security-conscious networks” frequently encountered in irregular warfare.
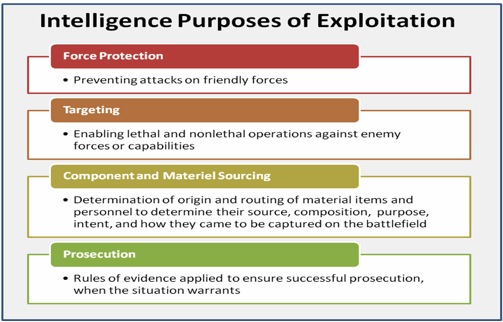
Figure 4: Purposes of Exploitation. Source: Authors.
Exploitation occurs at three levels. Level 1 exploitation is tactical exploitation at the point of capture, Level 2 is unit organic or theater-level exploitation, and Level 3 is national-level exploitation as part of the federated intelligence community effort. Exploitation can be accomplished by operations or intelligence personnel on the objective through a variety of means, such as battlefield interrogation or on-site document and media exploitation (DOMEX). As personnel and materiel are moved up the exploitation chain, the process becomes more deliberate and detailed, culminating at a centralized in-theater facility staffed by military, civilian, and law enforcement professionals. When appropriate, SOF federates analysis of DOMEX and electronic media to outside agencies for faster exploitation and dissemination. This allows SOF to minimize their forward footprint and count on “reachback” to CONUS sanctuary locations.
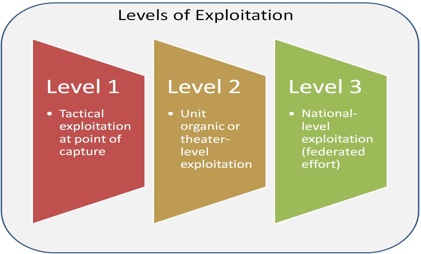
Figure 5: Levels of Exploitation. Source: Authors.
Analyze
The “analyze” phase is where the information gained in the find, fix, finish, and exploit phases turns into intelligence which can be used to drive operations. Analysis can be performed by SOF in theater, or information and materiel can be sent back to CONUS for further in-depth analysis. As in the fix phase of F3EAD, SOF lessons learned reinforce the value of a federated approach to intelligence support to intelligence analysis, since very rarely does SOF have the organic intelligence infrastructure necessary to maximize the value of F3EAD.
Disseminate
The last step in the F3EAD process is the “disseminate” phase. One of the keys to success of F3EAD is the creation of a wider dissemination network than what has traditionally been practiced inside the US intelligence community. Dissemination is a key aspect of the SOF targeting process and warrants inclusion as an independent phase of the SOF targeting cycle. Dissemination of intelligence information gleaned through the SOF targeting process helps to create “a network to defeat a network” throughout the intelligence enterprise and helps eliminate intelligence stovepipes. SOF experience shows that in the risk versus gain analysis more information sharing is better when it comes to defeating our nation’s enemies. Wider dissemination to conventional, Coalition, and even host-nation military forces, interagency partners, and civilian leadership contributes enormously to the success of F3EAD by expanding the intelligence and operations networks in support of SOF missions.
F3EAD vs. F3EA
Some organizations utilize the acronym “F3EA” instead of “F3EAD.” While the processes are essentially the same except for the last letter of the acronym, the difference between the two involves more than mere semantics. The argument for F3EA is that the “D,” dissemination, is an “understood” part of the process and does not need to be specifically designated as an individual component. This thinking is in error. “Exploit” and “analyze” were added to the legacy find-fix-finish (F3) process because those functions required specific emphasis in order for the process to realize its maximum potential. The same holds true with dissemination; without emphasizing it as a specific and essential part of the of the targeting process, SOF runs the risk of creating “stovepipes of excellence” that deliberately or inadvertently compartmentalize information, thereby inhibiting the effective fusion of operation and intelligence functions and bogging down the targeting process. Emphasizing “dissemination” as a formal part of the process ensures that practitioners keep the dissemination element in mind as a continuous part of the process.
The Way Ahead for F3EAD
It might be tempting for some to look at the F3EAD process through the lens of legacy targeting techniques and their own limited experiences and say, “nothing new here.” That view is extraordinarily shortsighted. While it is true that F3EA and F3EAD have been in existence for years, and that F3EAD incorporates familiar components of legacy doctrinal targeting methodology, F3EAD represents nothing less than a revolution in the way SOF conduct lethal and non-lethal targeting. More than a conceptual model, F3EAD reflects a fundamental change in thinking and makes the concept of “operations/intelligence fusion” a reality. Through F3EAD, commanders ensure that “operations/intelligence fusion,” “operations directs intelligence,” and “intelligence drives operations” are more than trite buzzwords. Additionally, F3EAD creates the kind of unity of effort and generates the potential for an operational tempo that has arguably never been seen in modern combat. The success of the SOF units utilizing F3EA/F3EAD serves as validation of the efficacy of the process.
Recognizing the potential of exploitation and analysis phases of F3EAD, institutional training has arisen within the SOF community in order to capitalize the lessons learned from the field in terms of the utility of F3EAD. The 6th Battalion at the John F. Kennedy Special Warfare Center and School (SWCS), for example, now boasts 11 courses which stress ops/intel fusion and the F3EAD process as part of the curriculum. Several of these courses were begun as partnerships between SWCS and the Joint Special Operations Command’s Intelligence Brigade (JIB), ensuring the dissemination of SOF ops/intel best practices throughout the joint and combined SOF communities. 6th Battalion, officially activated on 27 June 2011, already trains both operations and intelligence personnel in a variety of exploitation tactics, techniques, and procedures. For its part, the JIB ensures joint SOF operability and provides joint doctrine for SOF personnel employing F3EAD in Overseas Contingency Operations and other locations throughout the world.
Conclusion
The F3EAD targeting methodology can be successfully utilized by any organizational echelon, with any level of resourcing. As previously mentioned, SOF are not the only forces who are capable of utilizing the F3EAD process. Indeed, F3EAD has been effectively utilized by general purpose forces and U.S. allies, and is incorporated into doctrine. But more still can, and should, be done. F3EAD should become standard practice not only for SOF but for joint and combined doctrine, which is currently characterized in some cases by poor operations/intelligence fusion and joint/interagency cooperation, and encumbered by multiple and often conflicting tactics, terms, and procedures. The utility of the methodology and the efficacy of the process are clear; F3EAD is successful for SOF and with proper execution, it can be successful for the entire force.
About the Author(s)
Comments
F3EAD is a tactical tool which, as others have written,must be part of the larger joint targeting cycle and operational plan. Too often Messianic proponents of F3EAD over-promise on it capabilities, and because of its ability to feed itself, it continues to run and run even as it under-delivers. I explore the efficacy of leadership targeting, 'man-hunting' as this article describes it here: http://www.tandfonline.com/doi/pdf/10.1080/14702436.2013.845383
The article is a well-written and useful summary of how F3EAD developed and what it could become, but I think underpinning it is an assumption that it has delivered rather more than it has.
1. Good synoptic article on a difficult topic, in particular if the discussion on “holism” (military operations-intelligence analysis-etc.) results on a more technical debate about which kind of bodies or entities (maybe totally new political-military ones) should carry on these D3A general and F3EAD particular tasks.
2. Let’s be realistic: this is the future of wars to come. Political in nature, irregular in manifestation, small or low (with peaks) in intensity, mostly multi-national due to the identity (or non-identity of combatants). In the present “Serval” set of ops in Mali, there was the opportunity to establish that the several terror groups include around 11 different nationalities.
3. It was important for the authors to add caveats and clarifications on the meaning of the “finish” phase, this one being seen too quickly in certain military/intelligence quarters of several nations as obliteration of adversary structures, through literal physical lethal action. In November 2010, the Brazilian Armed Forces SF/SOF (including the Army 1st SF battalion and others, also from the Navy) were employed in a total new scenario: to dislodge criminal and drug dealing organized gangs from several shantytowns in the neighborhood of Rio, in particular Morro do Alemão and Vila Cruzeiro. Complex task, due to the dimension of the places (a bit like Mogadisho in the “Black Hawk Down” incident), the fact that gangsters were holding hostage entire population sectors, and the fact that the criminal groups had their own paramilitary structures, intelligence collection networks and even military-like infrastructures (watching towers, bunkers, ammo dumps, etc.). Besides raiding places, dismantling cells, doing difficult hand to hand combat in urbanized terrain, the Brazilian SF’s established information warfare checkpoints and modules, printing pamphlets, giving classes, performing “law and order agitprop” and psyops, etc., as part of the “finishing” phase. Lessons learned during “exploitation” and “dissemination” showed that this IW set of actions was as decisive as heliborne assaults or counter sniping, or physical elimination of drug czars and their foot mercenaries.
4. Another example of non-combat meanings of “finish” can be seen in the effort done by French special forces and intelligence operators, successfully de-linking independence seeking Tuaregs of the MNLA from “Azawad” Jihadists (Ansar Dine, AQMI, Signatories with Blood, e.a.), or forcing non-Jihadist Salafists to create “political” movements, like MIA. This took the support base from the “Arab Cells”, that had no choice but pack and run (to live and fight another day, of course). But “finish” here was essentially a militarily supported political intelligence task.
5. I see as specially sensitive the dissemination phase, as this cannot be seen as a one way street, but an interaction process, through which feedback from entities benefitting from intelligence or other data packages, or judicial files an suits, experiences or related, can not only produce reviews of initial products, but a return to earlier phases of exploration and before, if new elements are discovered or added. When dissemination is done in international coalitions this is more relevant even. Actually, the particular rules of dissemination outside of coalitions, but inside of broad “objective alliances” (for example, dissemination of “Serval” results from the orbit of the French COS and DGSE into concerned but non-allied countries, like Algeria, Libya, Egypt) is a major problem, the need to know factor tempering the anxiety to get feedback from useful but extraneous actors.
6. The growth of new needs is also producing, in all NATO countries and others, an emerging class of professionals, structures, techniques and technologies, methods and scientific tools (CALEB, for example), which will make the subject of irregular warfare and its constraints a fascinating subject for the immediate and not so immediate future.
7. Some comments were spot on adding considerations about time frames and possible add up of phases or sub-phases (for example, development, testing, operational feedback, etc.).
8. At any rate, congratulations and good luck to the authors.
Nuno Rogeiro
Lisbon, Portugal
"Life sucks in Afghanistan, but not as bad as getting shot in face." All the academic models and doctrinal mutations in the world are meaningless if the enemy does not feel that he may be killed at any moment should he continue to serve the Taliban. What is truly missing from this article is that should the ROE continue to hamstring Commanders' ability to apply lethal force no amount of artful targeteering will ever bring about success in war. If your enemy does not fear death, what makes you think he fears you? It's constraint based warfare, and the opportunity to say "no" has made its way into command thought processes' and boldness has been replaced with a reticence to do damage doctrinally. The answer to such a nuanced problem is obscenely simple: find where they are, or at least your best guess and send a squad in there to see what happens.
An off hand observation before a more direct answer to the question. I would argue that "develop" should be added to the F3EAD, making it F3EAD2 in order to greater exploit the information collected weighing the restraint of not acting against the potential value of the intelligence collected; ostensibly replacing the "finish" with "follow".
While the above may not be a total departure from a military application of the F3EAD algorithm, I do believe it shows that using F3EAD as a guide, the path may deviate to serve other purposes.
At its core, F3EAD is a formula used to identify and solve problems. If you understand the problem, or at least have as much information as possible, this formula can be used as an instrument of counter-terrorism for any agency or department. The way the military, Army or more specifically ARSOF consolidate and organize information about a particular problem is in the 1st paragraph, or "Situation" paragraph of an Operations Order. While this format is the most basic and almost parochial way or organizing information in a joint endeavor to solve an identified problem, its simplicity lends itself not only to dynamic problem solving, it allows those from multiple services, agencies departments, countries etc to communicate and participate using a common language. Identifying a simple format for everyone to use reduces superfluous learning and allows all involved to focus more directly on the task at hand.
Whether you are an aid worker attempting to improve quality of life, making a target population less susceptible to an extremist message or a border officer attempting to shunt illicit activities which indirectly support terror, the theory of finding the threat(s), fixing it in a certain location, finishing (or otherwise acting decisively by focusing resources of any kind upon the threat/problem set), exploiting success or failure through a chosen medium and then honest follow-on analysis of what could be improved in subsequent operations and determining whether or not the means justified the ends is way for non-SOF writ large to apply the F3EAD cycle to meet their needs. It cannot be applied in a vacuum and an intimate knowledge of statutes, jurisdictions, foreign and domestic law and its use's impact on US policy should be the focus of some discussion before choosing the cycle as a part of any course of action.
Thanks for the article.
Are there lessons from this framework that can be applied to CT efforts on the homeland and in international zones where terrorism is being planned? Apologies if this is a stupid question, but Im interested in the differences, subtle or otherwise, between SOF mission and operation planning in a military context compared with counter terrorism planning in a non-military arena.
What's broken is that we don't do MDMP at all anymore. We use overcomplicated "CONOP" formats as incomprehensible gibberish to conceal the absence of honest thought. Powerpoint is meant as a presentation tool, not a planning and production tool. More can be accomplished by laminated large sheets of paper, pasting them to the wall and rooting out specified and implied etc. than large groups of people all huddled around computers individually working on "their slides". The second problem is simple: if a Battle Staff is discussing the definition of targeting after deploying, there is an error in sequencing. Deployments are for the conduct of decisive operations designed to achieve a known end-state.
Just a side comment.
Have the entire battle staff in a room---minus the FIREs/Targeting guys.
Ask them to define the term targeting and you will have 20 different answers and or no answers.
That is the reason battle staffs are having major problems with the target planning process.
Ask again the question of nodal analysis or why does the FSO/Targeting CWO do a TSM---and again you will get blank faces.
Targeting as it it today is inherently tied to MDMP--but MDMP is broken big time---try to fit the current concept of targeting into the coming staff process being currently discussed---Design.
Just my opinion.
Before we go into F3EAD and or F2T2EA we have to understand the larger picture of this targeting process and where the D3A fits in to the 6 phases of the Joint Targeting Cycle. During phase 5 of the JTC, Mission Planning and Force Execution, the JFC approval has been gained and the directives in the form of the Target Tasking Frago have been passed to the TF. The TF in turn begins their MDMP process and use D3A as the starting point. In the decide phase of D3A, something completely overlooked in F3EAD and F2T2EA, provides the overall focus and sets priorities for intelligence collection and attack planning. The decide functions draws heavily on a detailed intelligence preparation of the battlefield (IPB) and continuous assessment of the situation (HQ DA, 2010). Why then is this step, being the basis for the beginning of the TF targeting process overlooked in the F2T2EA and F3EAD? It is because these processes mentioned are subordinate to the D3A which is subordinate to the JTC. In the SOF community it has been widely understood that they have their own targets that support their commander’s end state and objectives that are nested with the JFC’s end state and objectives but they are not one in the same. The SOF is not really subordinate to the JFC.
F2T2EA and F3EAD are very effective targeting processes when it comes to executing at the tactical level. D3A is MDMP, during MDMP we may have to execute a target that lends itself to fast decisive action that would have to be engaged outside of the normal planning process and requires dynamic execution. During deliberate targeting this would be categorized as an on-call target. These targets have actions planned against them but not at a specific time so they would fall outside of the normal ATO process and targeting process. This is where the F2T2EA/F3EAD would come into play as well and in-toto to dynamic targeting where both unplanned targets and unanticipated targets may offer an opportunity to have significant battlefield effects when action is taken against something or someone that has not been planned.
F2T2EA/F3EAD has its place in targeting but it is far from holistic and is not solution to the Targeting process but just another step with in it. I recognize many of us have seen successful targeting at many echelons and failed targeting at many echelons. As you consider your recommendations on your experiences I urge that you look at it from a holistic perspective across, and I hate to use this term, the full spectrum of operations. Recognizing the tactical advantage that the SOF offers us as a whole there is more to targeting than this. I will also argue that it would not work well at all echelons. We all know what targeting is and what the “science” of it is. The “art” of it is tying all of the WFF functions into one unified mutually supporting effort and assessing and exploiting the gains associated with those efforts IOT drive follow on targeting cycles. All of which will support the “end state and Commander’s objectives” which have been developed and is phase 1 of the JTC. Where is this done in F2T2EA/F3EAD/D3A?
“Capabilities analysis” is phase 3 of the JTC which is similar to both the Decide and Detect function of D3A. It’s clear, during D3A, that a TF will not “Decide” to engage a target that it cannot, nor would it attempt to “Detect” a target that it cannot, unless assets from other echelons are available and have been allocated to them. So in a way the “decide” and “detect” function at the TF replicate the capabilities analysis function of the JTC. This is vital to the targeting process but it is not included in the shortsighted F2T2EA/F3EAD processes.
What the author is referring to as a legacy targeting process is the targeting process. It is iterative, repeatable, consistent and flexible enough to be used in any fight COIN or otherwise. Staff organized and Commander driven, the inconsistency arises because of the lack of staff understanding. This lack of staff understanding is evident in this article. Targeting is the process of selecting and prioritizing targets and matching the appropriate response to them, considering operational requirements and capabilities. Targeting without the “decide” is FT2TEA/F3EAD.
Just a side comment.
The current F3EAD model is based in current doctrine for BCTs on a 14 day targeting cycle. The reference to FM 3-60 and the HVI diagram is interesting in that it reflects the targeting process for say a BN/TF, BCT and a Div/Corp. FM 3-60 does not go into the targeting process at all for SOF.
SOF or better yet JSOC marches to a totally different drumbeat of a 24 hr targeting cycle and the core targeting methodology is built around F3EA not as the article reflects F3EAD as they do not need to get into a D mode as they are fused with the shooters all in the same room as intel and operations.
NOTE: JSOC initially modified the per doctrine D3A model to actually F3EA while in Iraq and then the regular Army units started to use it in late 2007 early 2008. In the older Targeting/FIREs FM F3EAD was not even doctrine.
Can the SOF targeting model be applied to the BCTs, Division and Corp levels?---will never happen as these organizations are currently struggling just to get the targeting process to work using standard MDMP/B2C2WG.
We have seen repeated problems in BCT targeting process at the various CTCs since 2006 and it is not getting better and a number of BCTs/Divisions and Corps are going actually back to the D3A model.
A more interesting question and direction should have been can the idea of a fused staff element at the BCT/Div/Corp level actually increase overall targeting efficiency and improve the battle staff processes---definitely yes but the regular Army is not there yet.
KEY element absolutely not talked about in this article is the complex issues around sysnchronization and integration of organic, tactical and operational ISR assets that are a central KEY compotent of targeting.
Right now there are rumors that JSOC is taking an ever increasing percentage of ISR assets available in AFG and the BCTs are left with "fair sharing".
I would argue that the SOF targeting model is not based on the success or lack of success in using the F3EA model but rather in their fusion of shooters, intel and ops in a single planning room coupled with their extensive ability to pull ISR assets as needed---something current BCTs/Divisions and Corps do not have available to them.
WORTH IT---to go back into the SWJ articles and call up several SWJ articles written by Jimmy Gomez a leading Targeting CW4 131A (retired) on the same topic especially his article in defining the differences and uses of D3A vs F3EAD.
This article can in fact open a can of worms about the battle staff driven targeting planning process and ISR planning inside BCTs/Divisions, and Corps.
Will be interesting to see where this discussion goes----
Good article on a relevant and important adaptation of the tried and true targeting methodologies we have used for many years. It is important that best practices are shared and inculcated in training and programs designed to build the future force. We began teaching F3EAD as part of the core curriculum at the 131A Warrant Officer Basic Course in 2007--it was important then and it remains so today.
I suppose I am one of the “exceptionally shortsighted,” one of those poor creatures that, according to the authors, am forced to look through the “lens of legacy targeting techniques,” perpetually blinded by my “limited experience” to the Truth and Light of their received revelation. I must concede that casting any potential critics as simpletons before they have a chance to open their mouths is a good debate technique, especially if the debate is televised, but it seems unnecessary and inappropriate here.
The authors actually have some very good points, it was a good and informative article about the merits of F3EAD, they make a solid case about why it might make great sense to better define the targeting process. However, much of what is good is swept away by not properly addressing the underlying issue - that a process is only as good as the people who use it and the way in which they use it. Most of what the authors point to as improvements that F3EAD might bring are really just backhanded commentaries on the improper use of existing target methodology – the same critiques that would probably apply to F3EAD if it were the targeting law of the land…
“In F3EAD, commanders establish targeting priorities, the intelligence system provides the direction to the target, and the operations system performs the decisive operations necessary to accomplish the SOF mission.” This, truly, is not new…it is the entire point of the targeting process. The saw “intelligence drives operations” is not newly derived wisdom, but a reminder to this generation of what has come before.
If that is not happening to the satisfaction of the authors, is that because of the process or the people involved?
“D3A looks almost superfluous because F3EAD can accomplish the exact same thing as D3A, while improving the overall targeting process by increasing the input of intelligence.” Even if we take this generalization at face value, do we really need an entire new process to merely increase the input of intelligence – and back to the point, if the authors are unhappy with the amount of intelligence input into D3A is that the fault of the process or the people involved? I would posit that you could declare “D3A is dead, long live F3EAD” and you would still struggle with proper targeting guidance and intelligence inputs and poor use of intelligence outputs…because of people.
“Unlike other traditional targeting models and processes that focus on the operational or “finish” aspect, the main effort of F3EAD is the intelligence effort.” Of course, this begs the question, why are we even targeting anything if not to achieve a desired effect – whether lethal or non-lethal? But more to the point, only one aspect of D3A addresses delivering or finishing anything – the rest is devoted; to the commander deciding what to target, why to target it, and what effects are necessary; where it is and how to deliver the fires necessary to create the desired effects; assessing the effects of those fires in terms of reattack, future targeting, and yes, utilization of the intelligence generated from that assessment effort.
If that is not happening…is it the process, or the people?
Any process, to include F3EAD, is useless if not understood and utilized appropriately and in good faith. Indeed, the authors’ point that the success of F3EAD relies upon “1) the degree to which the process is understood and implemented within the SOF community; 2) the emphasis placed on the process by SOF commanders, and 3) the degree success the process achieves for the SOF units who utilize it.” Which is to say that, if not understood or implemented properly, if not emphasized and disciplined, or if not modified in the face of repeated failure, F3EAD is just as pointless as any other acronym.
It is not appropriate to maintain the status quo just to maintain the status quo, but nor is it appropriate to make change for the sake of change and declare it progress because change has occurred. I would argue that the key in determining whether F3EAD should supplant any particular targeting methodology is that, given the same groups of people with the same experiences and training, does F3EAD deliver a better effect? If the answer is no, then all involved can save a lot of energy in focusing on executing D3A better, rather than rewriting doctrine.
