The Dynamic Field of Terrorist Weapons Options
Christopher Flaherty
Introduction
Recent trends in the use of weapons by terrorist, extremist or violent attackers points to a dynamic field of options, representing a spectrum from the highly complex to the simple weaponization of common everyday items. Rather than a linear progression from the simple to the complex, or devolution from the complex to the simple, there is an elastic set of polar options, that attackers range between. Examining this phenomenon in terms of tactics, techniques and procedures (TTPs) analysis reviews the notion of a weapon; its use; and what constitutes one. It can dramatically shift for a variety of reasons and circumstances, even the beliefs, and behaviours among various attackers can affect the decision to use one weapon, over another, or to weaponize (Flaherty, 2012). The choice of attack can oscillate between using simple or complex weapons, or the weaponization of something. The dynamic field of weapons options creates asymmetric possibilities for an attacker that need to be factored into counter-measures.
Dynamic Field of Weapons Options
Figure 1 illustrates how the use of weapons and weaponization sits in a four-quartered field, offering a spectrum of options.
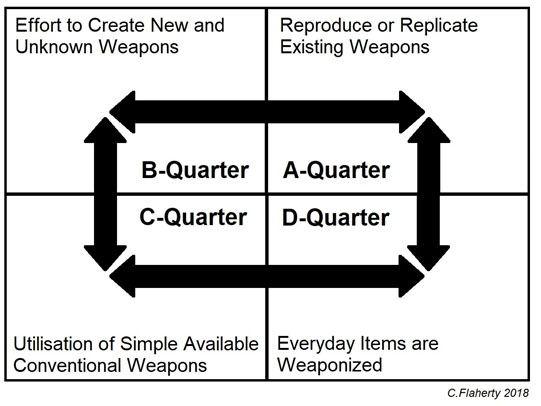
Figure 1: Dynamic Field of Weapons Options
A-QUARTER: Represents the effort to reproduce or replicated existing weapons technology, such as explosive devices. This trend has been a longstanding tactic in terrorism, as the:
“expertise and technology to improvise low-cost mass-casualty explosive devices have proliferated during the past decade.” (Gunaratna, 2001)
There are many examples where attackers have made copies of military styled mines, such as fabricating a pipe bomb, or a pressure-cooker bomb. These are made from commonly available items such as pipe fittings or a cooking pot with lockable top. Filled with an explosive materiel, such as gun-power harvested from fireworks and stuffed with nails and scrap metals, and then fitted to a detonator. Home manufacture has also seen the attempt to mix chemicals and other substances intended to reproduce various well-known explosive materials.
B-QUARTER: Represents the effort to create new and unknown weapons that operate as an asymmetric advantage over conventional counter-measures. In this category, we see attempts to make new explosive mixtures, or the development of the infamous body cavity bombs serve as examples where manufacture becomes highly developed requiring an actual lab, even a manufacturing facility to build the weapon (Bunker, Flaherty, 2013).
The higher-order attempt to produce new kinds of explosives, was the cause of the 2006 U.S. Governments’ additional security measures that implemented changes to airport screening, including the prohibition against liquids and gels of any kind in carry-on baggage (Transportation Security Administration, 2006). The plot itself involved the use of a combination of chemical components, based on peroxides; and while an extensive:
“list of chemicals that could conceivably be used—in either liquid or solid form—is essentially endless, given the proper expertise…Neither of these is easy to work with” (Biello, 2006).
This approach requires the support of a larger network of specialists to design and test the weapons’ feasibility. Use of this approach by attackers is well known. However, it has many drawbacks, such as the expense and resource intensity of these operations; that have proved difficult, and sometimes impossible sustain in the face of concerted international counter-terrorist operations aimed at disrupting supply and communications between individuals and groups.
C-QUARTER: Represents the use of conventional small arms and light weapons, that are, “the main tools of terrorist violence.” (Gunaratna, 2001); and this trend remains unchanged:
“It was noted that conventional arms remained the weapons of choice for terrorists.” (United Nations Headquarters, 2017)
A devolution relationship can be seen linking the A-to-B-to-C quarters. This is where the attempt to use complex weapons becomes counter-productive. The response may be to change tactics, and replace with ever-simpler, and more available conventional weapons. This is because it has become too hard, complex, time, or resource consuming to create new and unknown weapons. Attackers reverting to the use of commonly available firearms and bladed weapons often makes their attacks indistinguishable from other violent crimes. It has been argued that the recent upsurge in these types of attacks is a direct result of the degrading of support networks by sustained operations over the last decade that have forced a radical rethink in tactics. The breaking-up of international terrorism into more loosely aligned groups and lone individuals has forced a situation were attacks have to be orchestrated quickly to avoid detection, allowing only for the use of weapons commonly available to local violent criminals.
D-QUARTER: Represents the continuing process of devolution, where objects are used that conventionally are not weapons at all. Everyday items are weaponized; using any available item as a weapon, as long it as it can cause injury or even kill a person. The use of an item, even if something not conventionally seen as a weapon is not uncommon, as virtually any implement can be used to attack a person offensively as a weapon and cause bodily harm.
On aspects to this phenomenon, is that the problem may in fact have nothing to do with weapons, or the weaponization of a surrounding object, or objects. For instance, the recent U.S. Governments’ electronics ban on international flights was an attempt to stop, “smuggling explosive devices in various consumer items” (Department of Homeland Security, 2017). In that case, an item such as a computer laptop could have foreseeably been used as camouflage, concealing an improvised explosive device (IED) in the battery space. It is interesting to note, that the 2006 transatlantic aircraft plot involved the use of a small amount of high explosive hidden within an AA battery casing intended to detonate the main bomb. A not dissimilar use of camouflaging was seen in the 1990s where a plot to attack multiple U.S.-bound airplanes from Asia involved the use of nitroglycerine filled saline solution bottles typically carried by contact lens wearers (Biello, 2006).
In the case of the laptop ban there was a subsidiary fear that if the battery had been left in (and not removed to make more space for the IED), then it too could have become another component explosion. This secondary effect is often known as weaponization, where the initial blast is intended to begin a process of turning surround objects into weapons themselves causing injury and death (Flaherty, 2005). A more complex example of these phenomena has been the possible use of a powerful battery alone to catastrophically explode casing death or injury (Phelan, 2018).
The use of car ramming where the driver has intentionally used a vehicle as the weapon of attack has been a growing trend; and in this regard has been characterised as worldwide (Yan, 2018). One of the more terrible of these attacks occurring in 2016, which was an act of terrorism, at Nice’s Promenade des Anglais, killing 86 people and wounding more than 430 others. It is generally understood, that ISIS claimed responsibility for the actions of the Tunisian-born Mohamed Lahouaiej-Bouhlel, who drove a 19-ton truck into a crowd celebrating Bastille Day (CEP, 2018). A great many of these attacks are known, and in some instances of vehicle-ramming these have been categorised as attacks, but not actual acts of terrorism or extremism.
Conclusion
An overarching driver in the choice of a weapon, or the decision to weaponize is the resources available to an attacker, and as well may reflect an expression of the beliefs and behaviours held by the attackers themselves. For instance, the use of complex and sophisticated weapons may be a statement of superiority. This is not a new factor in warfare, even as far-back as the late 18th century, the introduction of military ballooning into the French revolutionary army was politically justified, by the:
“committee of public safety, ambitions of boasting that it had enlisted science under the banner of liberty, had sent a company of aerostats to the head-quarters of the army, in consequence of which a balloon was constructed” (Baines, 1817).
The dynamic field of terrorist and extremist weapons options has been used to illustrate the concept that attackers will often move elastically from one pole of extremes to the next, each representing a category of weapons or weaponization options. In some cases, there are clear overlaps. For instance, the conversion of everyday items such as metal pipe and fittings into the housing for a simple bomb; the pipe alone can be a lethal tool used to attack a person.
The true driver is to find asymmetric advantages by creating unknown weapons or using weapons in unanticipated ways. Seeking surprise is core to a successful attack. Surprise can be achieved using immediately accessible weapons, or through an increment in a group, or individuals’ skill and capability; if they continue to make attacks, making each attack more lethal and spectacular than the past. This progression was clearly seen in the two attacks made on the former World Trade Center in New York City, beginning with the conventional use of a vehicle-borne IED in 1993, followed by the shocking use of fuel-laden passenger aircraft to kinetically destroy these buildings in 2001.
Rather than viewed as a continuing lineal progression, or devolution, from the complex to the simple (or in its reverse order), the dynamic field of terrorist weapons options has been described thus far as a perpetual-cycle. However, in the case of small arms use and simple IED production, there is an overarching connection between both approaches, and it could be argued that there is a direct relationship between the C-to-A quarters. Additionally, there appears to be a cross-link between the B-to-D quarters where commonplace items such as commercially available chemicals and products that on their own are intern are combined to make a hither-too unknown explosive.
References
Edward Baines, History of the Wars of the French Revolution, from the Breaking Out of the War in 1792, to the Restoration of a General Peace in 1815: Comprehending the Civil History of Great Britain and France, During that Period. London: Longman, Hurst, Rees, Orme, and Brown, 1817.
David Biello, “Liquid Explosives Linked to Terror Plot.” Scientific American. 10 August 2006, https://www.scientificamerican.com/article/liquid-explosives-linked/.
Robert. J. Bunker and Chris Flaherty, Eds., Body Cavity Bombers: The New Martyrs. A Terrorism Research Center Book. Bloomington: iUniverse, Inc., 2013.
Counter Extremism Project (CEP), Vehicles as Weapons of Terror. 2018, https://www.counterextremism.com/vehicles-as-weapons-of-terror.
Department of Homeland Security, Fact Sheet: Aviation Security Enhancements for Select Last Point of Departure Airports with Commercial Flights to the United States. (Updated). Washington, DC: 21 March 2017, https://www.dhs.gov/news/2017/03/21/fact-sheet-aviation-security-enhancements-select-last-point-departure-airports-06.
Christopher Flaherty, Dangerous Minds: A Monograph on the Relationship Between Beliefs – Behaviours – Tactics. OODA LOOP. 7 September 2012, https://www.oodaloop.com/security/2012/09/07/dangerous-minds-the-relationship-between-beliefs-behaviors-and-tactics/.
Christopher Flaherty et al., “Fragmentation and Weaponisation of Buildings: A Review.” Priyan Mendis, Joseph Lai and Ed Dawson, Eds., Recent Advances in Counter-terrorism Technology and Infrastructure Protection. Proceedings of the 2005 Science, Engineering and Technology Summit, Canberra 2005.
Rohan Gunaratna, “Terrorism and Small Arms and Light Weapons.” Symposium on Terrorism and Disarmament. New York: United Nations, 25 October 2001.
Matthew Phelan, “Battery Catch-22.” Slate. 11 June 2018, https://slate.com/technology/2018/06/were-increasingly-reliant-on-high-tech-batteries-and-completely-unprepared-for-high-tech-battery-bombs.html.
Transportation Security Administration, “Press Conference Regarding 2006 Transatlantic Liquids Explosives Plot.” Washington, DC: 10 August 2006, https://www.tsa.gov/news/speeches/press-conference-regarding-2006-transatlantic-liquids-explosives-plot.
United Nations, “Chair’s Summary: Open Briefing of the Counter-Terrorism Committee on ‘Preventing Terrorists from Acquiring Weapons’.” New York: 17 May 2017, https://www.un.org/sc/ctc/wp-content/uploads/2017/06/20170526-Weapons-briefing-Chair-summary.pdf.
Holly Yan, “Vehicles as Weapons: Muenster Part of a Deadly Trend.” CNN. 7 April 2018, https://edition.cnn.com/2017/03/22/world/vehicles-as-weapons/index.html.
