Cyber Resiliency: Bridging a Cyber Capability Gap in 2025
Matthew Hutchison, Frederick Waage and Dan Bennett
The United States Army must develop a holistic solution to Army-wide cyber resiliency and hardening of its electronic systems in order to address our current cyber capability gap. Cyber resiliency goals must be achieved by anticipating vulnerabilities and disruptions before they occur, being trained to withstand the effect or disruption should one occur, understand each echelon’s responsibility for recovering from a cyber attack or event, and continue to evolve our methods, doctrine, and training to address the ever-changing threat landscape. A holistic approach requires an analysis of our human capital, our training and education programs, how we acquire combat systems, and how to change the Army’s culture to prepare for intensive cyber conflict. Imagine in the not-so-distant future, we find ourselves in an extended ground conflict with a cyber peer. Are we prepared from the tactical edge to the strategic core for winning in a complex world?
The 2014 MITRE paper, Cyber Resiliency Engineering Aid – Cyber Resiliency Techniques: Potential Interactions and Effects[i], forwards a Cyber Resiliency Engineering Framework (CREF) based off the premise that regardless of the erudition of one’s existing cybersecurity practices, organizations must accept that they will always be susceptible to ongoing - and largely stealthy - campaigns by sophisticated adversaries. To adapt to an evolving information environment MITRE has produced four Cyber Resiliency Goals or outcomes to govern defenders’ Cyber Resiliency actions. The first goal is anticipate, where one maintains a state of informed preparedness, followed by withstand which requires organizations to continue essential functions despite adversity. The next goal is to recover, where one restores essential functions during and after adversity. Lastly defenders attempt to evolve, which directs the adaptation of functions and supporting capabilities. Employment of the four governing outcomes of the CREF are illustrated in the below tactical 2025 vignette.
By the time the Cyber Resiliency (CR) team arrived, the Recon Strike Group’s (RSG) executive officer had already ensured that half of 16 non-deadlined Multiple Launch Rocket Systems (MLRS) in the unit were lined up across three adjacent motor-pools. The Storm Center had forward staged and aligned the CR Team at the RSG’s forward outpost based off of the robustness of the Atropians’ electronic order of battle. Given the Atropian situation template, the RSG, in coordination with the Storm Center, anticipated that the Atropians would target the RSG’s MLRSs. Therefore, Storm Center mobilized a CR Team to provide CR capability to the RSG.
With the other eight MLRSs covering down on the dead-lined MLRSs’ sectors of fire, the RSG chief mechanic was the first to greet Technical Sergeant (TSgt) Grist upon his arrival, stating that “about two minutes into the first contact two of our MLRSs were ‘bricked’. Luckily, the operators detected the cyber attack and immediately reported their statuses, allowing the commander to quickly adjust our engagement plan. After the cyber attack was detected and withstood, we pulled the dead-lined MLRSs to the rear and my own CR specialist took a look at them. She tried skill level one remediation unsuccessfully, so we called up to the Storm Center for advanced remediation and I guess here you are.
After receiving the situation back-brief from the RSG chief mechanic, the CR Team interviewed the unit’s CR specialist to better understand the MLRSs’ pre-existing baseline configurations. The CR Team, now understanding the MLRSs’ baseline configuration, initiated a recovery plan which included diagnostic checks of the MRLSs’ operating systems. The CR identified evidence of an intrusion in diagnostic logs and determined that it entered the MLRSs through the Global Positioning System (GPS) that Atropian cyber electromagnetic teams on the ground were able to exploit. The CR Team immediately reported the discovery to the Storm Center to alert the joint force of the vulnerability. The Storm Center oversees the containment and destruction of the malicious code and disseminates the appropriate patches to evolve beyond the exploited MLRSs cyber vulnerability.
Bridging the Gap
The cyber gap is growing, increasing the chances that a nation will likely use this gap in an attack against the United States. This gap exists because the United States is the most vulnerable nation to cyber attack based on the nation and Army’s reliance on networked information systems. The gap cannot be bridged by increasing our offensive cyber capabilities; other state and non-state adversaries will be able to maintain pace. We have already passed a point of no return for reducing our dependence on networked systems. The only way to bridge this cyber war gap and maintain cyber dominance is to improve our defenses and harden our systems against enemy disruption and attack. The cyber war gap provides adversaries of lesser military an asymmetric advantage that practically tempts them to attack when faced with increased international tension. Furthermore, the damage that may be prosecuted on United States assets from a cyber attack, may not be readily reciprocated in a counter cyber attack, given the lack of interconnectedness of other nation’s infrastructure and military forces.[ii] We must train and equip the force of the future to readily address critical military system cyber vulnerabilities and mandate cyber resiliency, hardening ourselves to cyber attack at the system and network level, and requiring secure systems from the drawing board to deployed ground combat.
Achieving Resiliency through Anticipation
Anticipating the threat is the proactive step in building cyber resilience. It involves preparing for future conflict, by changing the Army’s Operating Concept (AOC) now. In the near term, we can better prepare ourselves for operating in a cyber-challenged operating environment by changing the basic constructs of operational doctrine and training. As the Cyber branch refines its roles and responsibilities within the Army, we must continually allow doctrine to evolve to place responsibility for cyber resiliency at the lowest echelon possible. We cannot proceed another decade relying on the few cyber warriors and subject matter experts to keep our fighting units safe. A review of older Army doctrine is necessary to determine if being contested in cyberspace should change the way in which we operate and the skillsets that we train our soldiers as they prepare for war.
As electronic systems continue to become more sophisticated, Soldiers must be aware of their inner workings and learn a healthy awareness of the data and indicators being presented to them. It is impossible to stop the technological slide towards systems with greater ease of use and automation. However we can develop skillsets through cyber disruption focused training that can help change our dependence on computer systems and data and provide our operators with better skills to withstand and recover from cyber effects. Training akin to describing the signal flow of major combat systems is required, to inform operators (pilots, tank crews, artillerymen, etc.) as to what systems comprise their combat equipment, which systems rely on what data, and how those systems may be linked and therefore can be disrupted through less than obvious means.
The Army’s generating force includes organizations responsible for the acquisition and fielding of major Army combat systems, as well as their maintenance, contractor support, and supply chain validation. These organization are vital to future cyber resiliency of our fighting systems. While in the near-term, we must focus on finding and remediating vulnerabilities in the systems with which we currently fight. This will require but not limited to extensive penetration testing, software assurance, contractual support to outsource vulnerabilities, and an in-depth analysis of full-spectrum supply chain security of our defense industrial base. Cybersecurity is best achieved when built into systems life-cycle, and not applied as an add-on. As we pursue future combat systems, we should relook at our industrial age acquisitions for computing systems, require a standard for secure software as part of those systems much like the Federal Information Protection Standards (FIPS) outlined by the National Institute for Standards and Technology (NIST).
With the growth in demand for cyber effects and operations, it will be necessary to create a headquarters or “storm center” which can house the expertise and aggregate the data from cyber effects and anomalies across systems “fleets”. The nuclear navy does this for its nuclear reactor fleet, where there is a single point of contact for reporting anomalies and being able to discuss problems with experts ready to aid in system recovery. This storm center will need to be large enough to manage the aggregation of reports and data provided from the operational force, and will grow in house expertise through ongoing testing and evaluation of each combat systems’ level of cybersecurity. A brigade equivalent of Soldiers and contractors may be necessary in order to conduct storm center operations, including ensuring software assurance during product development and providing a deploying force with a forward capability ready to help detect and remediate possible cyber disruptions to combat systems. Aligning detachments by Army Warfighting Function (WfF)[iii] would help to focus cyber security evaluations and mitigation technical skills within the storm center and serve as the reach-back support for deployed units who perceive that their systems may be compromised (See Figure 1).
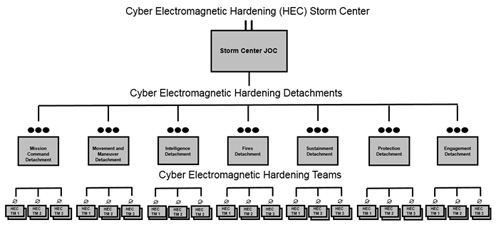
Figure 1
One critical aspect of cyber resilience lies in the education of our Army leaders and Soldiers who must be trained to operate with a degraded system and be educated in methods to detect and recover from system disruption. We have gone to a training model in the generating force that leads Soldiers and Leaders to understand how to operate a system, but not necessarily understand the inner-workings of the system. This creates overreliance on the system itself for anomaly detection and remediation. By changing our generating force education model to include more theoretical electronic and cybersecurity coursework, we can begin to instill in our force of the future, that computers are useful, but that reliance on them become a grave mistake.
The operational force must continue to focus on training and fighting with its current combat systems in order to be capable of winning in a complex world. However, the generating force must rapidly mobilize in order to execute a long-term and holistic approach to cyber resiliency in all our systems over the next decade. Responsibility falls on TRADOC to continue to adjust training and education models at all schoolhouses to address operating without trusted systems and data and possibly with the complete loss in capability of information sharing or position, timing and navigation data (PNT). The Army’s acquisition community and contracting arm must address cybersecurity in all future acquisitions prior to the request for bid, and have a system in place to evaluate the cyber resiliency of system alternatives proposed by our defense industrial base. Cybersecurity requirements for those bidding and subsequently being given the award must also be considered[iv]. The current cyber operational force in conjunction with third party contractor support must prepare to remediate cyber disruption in the near-term and secure fleets of systems Army-wide after they are prioritized and sorted by risk and mitigation cost.
The views expressed in this article are those of the author and do not reflect the official policy or position of the United States Military Academy, Army Cyber Command, the Department of the Army, US Cyber Command, the Department of Defense, or the US Government.
End Notes
[i] http://www.mitre.org/publications/technical-papers/cyber-resiliency-engineering-aid-cyber-resiliency-techniques-potential
[ii] The term “Cyber War Gap” is used and discussed in Richard Clarke’s book Cyber War on pages 148-149,, in which he addresses how less sophisticated weapon systems may have advantages should cyber war breakout. Interestingly he posits that improving offensive cyber skills is not the best way to close the cyber war gap with our adversaries. Harper Collins, NY, 2010.
[iii] See Chapter 3 of http://armypubs.army.mil/doctrine/DR_pubs/dr_a/pdf/adrp3_0.pdf
[iv] Executive Order No. 13636 - https://www.gpo.gov/fdsys/pkg/FR-2013-02-19/pdf/2013-03915.pdf
