Commanding in Multi-Domain Formations: Vision 2050 Warfighter Cyber-Security, Command and Control Architecture
Radhika R. Roy and Brian M. Dempsey
Introduction
Over 63 million new unique pieces of malware [1] were detected in 2015 alone. All predations show that cyber-threats will be omnipresence with the unprecedented advancement in innovative technologies coupled with artificial intelligence (AI) along with billions/trillions of interconnected internet-of-things (IOTs) where each human body will also be connected using nano-biosensors including augmented humans. The net impact is the surprising rise of super-intelligent information technologies fueled with robotics, smart munitions, ubiquitous sensing, and extreme networking, along with the potentially massive impact of cyber warfare [2]. Cyber-threats can be launched even by a couple of hackers or rough-individuals equipped with low-cost powerful technologies powered with artificial intelligence capabilities, not to speak of dedicated terror groups, enemy nation-states, and powerful adversaries.
All these vast technological changes are taking place in the background of dislocation of population with the rise of sea water level coupled with doubling of human population numbers with depleted earth’s natural resources amid economic uncertainties, not even considering the impact of spreading of epidemics.
Altogether it will be creating a huge human cultural change shifting from human and cyber-network as two distinct entities to a single human cyber-network, that is, human’s life itself becoming a cyber-network connected with each human body of the entire whole world. The complete impact of human cultural change that is being caused at the advent of these revolutionary technologies is yet to be imagined. It is also a possibility that a single cyber-attack could cause unpredicted damages across a huge chunk of the connected cyber-network that might also include connected humans’ lives.
The leaders from the U.S. Department of Defense (DoD), US Army Research Lab (ARL), Institute for Defense Analysis, and national security thinkers across academia have expressed opinion that the future battlefield will be increasingly populated with AI-based autonomous robots with much fewer human soldiers [2]. The technological progress in far-off information technology (IT) capabilities is not linear but exponential, and autonomous AI-entities like robots will play off one another, competing and evolving at hyper-speed. As a result, the faster “battle rhythm” will increasingly push human beings out of the decision-making loop, although these humans will exert positive control “but they’ll play umpire, rather than pitcher” shattering the basic tenet of command and control system of “human-in-the-loop.”
The human soldiers would be “super-humans” that “would be physically and mentally augmented with enhanced capabilities that improve their ability to sense their environment, make sense of their environment, use cognitive powers and interact with one another, as well as with “unenhanced humans,” automated processes, and machines of various kind in the 2050 timeframe. The various components needed to enable this development already exist and are undergoing rapid evolution. Even enemies could monitor troops’ biophysical signals and possibly including their brain states or decision-making abilities using cognitive modelling.
However, the advent of super-smart faster technologies also create more and more newer attack surfaces - the colossal effects of those newer future cyber-attacks are yet to be fully imagined. In this paper, we are providing the vision of the Warfighter Cyber-Security, Command and Control by the year 2050 in multi-domain formations. We have articulated great risks and opportunities keeping the perspective of the background of sea of changes that are occurring in technologies, humans, cultures, social, geographies, natural resources, and economics during this period.
Technological Changes by the Year 2050
Rise of Human-Life’s Connected Network
The most fundament change in happening that each individual body will be cyber-connected using a body area network (BAN) equipped with nano-technology-based ultra-thin sensors [3] powered by ultra-small iPhone-like devices. As if, the cyber-network is becoming synonymous with connected people’s life itself. This phenomenon is creating a set of fundamentally new challenges in the basic approaches not only in cyber-security, but also in all aspects of designing the cyber-network architecture. Figure 1 shows a view of a BAN that will connect a human using biosensors.
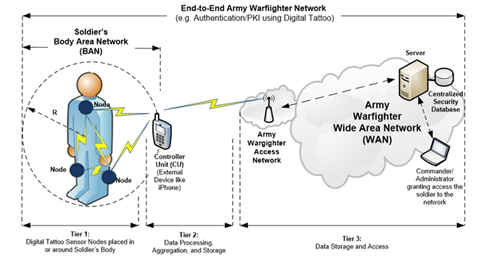
Figure 1: Conceptual View of Connecting a Human Using Biosensors
By the year 2050, a BAN will become an essential part to keep a human connected to the cyber-network. In the case of soldiers, the BAN will be an essential part for each warfighter communicating with the cyber-system autonomously without human intervention.
Nano-Technology-based Biosensors
Nano-technology-based smart biosensors (e.g. patch, digital-tattoo) of a BAN, harvest energy from near-field communication (NFC) signals such as tiny iPhones, sunlight, or by other means. These biosensors are waterproof and breathable, and can be worn for a week or so, before the normal shedding of skin cells begins to force the thin substrate to peel from the skin.
Password-less Physiological Signal-based Continuous Authentication
The physiological signals like Electrocardiogram (ECG) that is generated by biosensors of a BAN is used to authenticate a user continuously (Figure 1) where no password is needed to enter [4] as is the case in today’s networks. It is a revolution in security for authentication especially for warfighters where the dynamic movements of soldiers in constant combat environments do not warrant the use of passwords. Although a soldier performs authentication using password, the continuous authentication is never possible in today’s networks. A unique cryptographic key can be designed from a user's ECG signal allowing the encryption of information. By the year 2050, the password-less continuous authentication will fundamentally change for secured communications.
Rise of Interconnected Billions/Trillions of Internet-of-Things
The Internet-of-Things (IoT) are tiny small devices that can be physical or logical, but those devices can usually be connected over the Internet [5-6]. Physical things exist in the physical world and are capable of being sensed, actuated and connected. Examples of physical things include the biosensors, smart sensors, surrounding environment, industrial robots, goods and electrical equipment, and wearable technology. Virtual things exist in the information world and are capable of being stored, processed and accessed. Examples of virtual things include multimedia content and application software. The key is that the advancement of nano-technologies has created very tiny small devices such as biosensors that have so much intelligence can enable communications over the Internet. By the year 2050, billions/trillions of IoT devices will be interconnected over the Internet and warfighter networks. The security will be nightmare for these devices unless intelligent automotive robotics are used to protecting either individually or as a group depending on mission objectives.
Rise of Machine/Device-to-Machine/Device Communications
Devices like IoT and others will usher a new era of machine/device-to-machine/device communications. The detail of this communication scenario is beyond the scope of this paper. The key aspect of machine-to-machine (M2M) or device-to-device (D2D) communication implies that the information of communications architecture will primarily be peer-to-peer (P2P), a fundamental deviation of the classical client-server (C/S) communications between devices as happen today. Of course, there will be some selective mix of P2P and C/S communications, but in the age of IoT, P2P communications will be predominant. In the subsequent section, we have described the details of the P2P architecture.
Rise of Artificial Intelligent
The goal of artificial intelligence (AI) has been to mimic human intelligence as far as it can. In practice AI employs reasoning, knowledge, planning, learning, communications using natural language processing, perception, and ability to move and manipulate objects. The scope of the AI is huge in complexity and sophistication and is beyond the scope of this paper. In short, we can describe, neural network and machine learning are the two major areas that have played the important role for AI development. Ultimately, AI has driven the development of autonomous robotic technologies. Neural networks are trained, for example, to run the control system of robotics based on command. Machine learning provides the ability of a program to learn automatically when exposed to new environments and can adjust itself accordingly, for example, a robot needs to have this kind of learning capability.
Robotic Technologies
Experts in a recent DoD seminar have predicted that AI-based intelligent autonomous robotics will be ubiquitous [2] in the battlespace including applications in warfighter communications networks by the year 2050. Robotics will mostly be networked, however, they will be in different categories depending on the applications in meeting the mission objectives. For example some robots will be autonomous robotic soldiers, ground MANET nodes, air MANET nodes in unmanned air vehicles (UAVs), Intelligence, Surveillance, Target Acquisition, and Reconnaissance (ISR) robotics sensors, battlefield robots, robotic vehicles, bio-inspired robots, cognitive robots, cyber-defense robots, and other categories. An important observation is that the cyber-defense robots are essential for automate the process of cyber-attacks prevention, detection, and repair the cyber-systems. We envision that the AI-based smart autonomous robotics functionalities shall be embedded for each cyber-entity including in each kind of robotics technologies.
Cognitive Technologies
Computer vision, machine learning, natural language processing, speech recognition, and other functions are usually performed by humans. Like humans, the artificial intelligence-based autonomous robots can be used to understand the human behavior and can predict the actions that a human take. These sorts of technologies are termed as cognitive technologies. It will be one of the potential disruptive technologies [2] that will be available by the year 2050.
Smart Sensors
ISR and other kinds of sensors that are equipped with an AI-based autonomous robotics capability are termed as the smart sensor in the context of the 2050 timeframe. The smart sensors can also be built using smart IoT devices equipped with some kind of robotics capability. These sensors will be widespread in the battlefield in all tiers by the year 2050. The traffic payload generated by each smart sensor can be anywhere from a few bytes to large, high bandwidth intensive real-time continuous videos. The important point is when hundreds/thousands/millions of smart sensors start sending data, intensive processing power is needed for fusion of this huge amount of traffic load to produce the actionable information either for humans or for intelligent functional entities requires powerful autonomous robot(s). Again autonomous robotic technologies are needed for fusion of the sensor information.
Swarms in Battlespace
The swarm capability in battlespace is an important aspect in modern warfare for dealing with new emerging threats like asymmetrical warfare. In the future, autonomous robots, like that of team or group works by human soldiers, will be used for swarming. Swarms will be self-organized and/or collaborative actions of robots with varying degree of freedom that requires a P2P communications architecture without fixed infrastructures as special formations of MANETs. In other words, swarming can only be organized with a P2P MANET networking architecture. Like joining, leaving, and rejoining, swarms in battlespace will be widely used in MANETs as another new capability by the year 2050.
Augmented/Super Humans
A new surprising phenomenon is the use of a combination of mixed human-robot teams in the battlespace. In fact, the mixed human-robot teams will be the principal Army unit operating in the year 2050 timeframe [2]. The human team members collaborating with robots will be enhanced in a variety of ways by implanting cognitive technologies in human bodies and converting them as if they are augmented/super humans and will have access to sensing and cognitive powers with enhanced physical capabilities as well. These high-value super humans will also be the targets of adversaries. However, special protective measures like robot clouds will be created to protect those super humans.
Advent of Predominant Peer-to-Peer Communications Architecture
By 2050, the amount of computing power that a tiny-device can have will enable acting like a small robot. We have explained earlier that autonomous robotics will be the center for cyber-communications in each tier and will be able to move, joint, rejoin, and swarm autonomously as independent peers. This implies that only the peer-to-peer (P2P) communication architecture will be able satisfy the requirements of realizing the full potential instead of traditional centralized client-server (C/S). Although it is expected that a hybrid architecture consisting of both C/S and P2P will coexist in certain situations, the role of C/S will be highly limited acting as some back-up servers for doing some off-line high computation-intensive processing while ceding the actual real-time communications for super-intelligent P2P entities even for fixed networks and mobile cellular wireless networks, not to mention mobile ad-hoc wireless networks (MANETs) where communications are fundamentally P2P [7] in absence of any fixed infrastructures and each node is an independent peer and moves from one-place to another independently. Some example MANETs are the vehicle-to-vehicle (V2V), unmanned aerial vehicle (UAV), and robot-to-robot (R2R) network. Eventually, nano/micro-satellite-to-satellite (Nano/Micro-S2S), low-earth-orbit/medium-earth-orbit satellite-to-satellite (LEO/MEO-S2S), and geostationary orbit satellite-to-satellite (GEO-S2S) networks are also expected to be forming intelligent P2P networks at different tier levels, not even ruling out inter-tier P2P communications, by the year 2050.
Vision 2050 Warfighter Cyber-Security, Command, and Control Architecture
We have briefly articulated how the emerging technologies will fuel radical changes in the future warfighter communications architecture. BANs consisting of biosensors, large numbers of smart IoT devices, M2M/D2V communications, artificial intelligence, robotics, cognitive technologies, smart sensors, swarms in battlespace, augmented humans, and finally P2P communications architecture are among the emerging technologies that will dominate the cyber-warfighter networks. In this context, we have put forward our proposed warfighter cyber-security, command, and communications architecture with multi-domain formations for the year 2050 in the subsequent sections.
Future Threat-Surfaces
The new man-machine interfaces (MMIs) will be a part of the future cyber networks especially for command and control (C2). MMIs will be one of the most important cyber-interfaces and will be the target for cyber-attacks in addition to other interfaces. The numerous newer cyber-applications will be used by a massive number of cyber-entities constituting with robotics, smart munitions, ubiquitous sensing, and extreme networking. Each one of these cyber-entities will have their own zero-day-vulnerabilities (ZDVs) that are left unknown by developers and implementers. Each one of those ZDVs is adding to new holes that are subject to exploit by cyber-attackers. The smarter cyber-attacks will be highly complex because human cyber-attackers will take advantage of emerging smarter, smaller, and even cheaper AI-driven robotics for exploiting ZDVs of newer applications. Whether we call these newer attacks such as Botnets, Denial-of-service (DoS), Distributed DoS (DDoS), Control-flow Hijacking, Code Injection, Industrial Control System (ICS), Man-in-the-Middle (MITM), Phishing, Ransomware/Crypto-Ransomware, Spam, Spear Phishing, Structured query language (SQL) Injection, Stuxnet , Trojan Horse/Virus, Virus, Watering Hole, or Worm [1], each of those cyber-attacks can be launched using more sophisticated means. The combined impact of human- and machine-attackers will have terrifying implications on cyber-attacks in terms of magnitude of complexities, extremely short time-windows, and frequencies of newer attack generations.
Future Cyber-Security
We have yet to fully comprehend the future cyber-attacks with unknown signatures based on the uncertain possibility of emerging newer cyber-attacks. However, it is quite certain that those cyber-attacks will overwhelm human users to prevent, detect, and repair the cyber-systems. Judging the time and speed needed by existing available cyber-tools for helping the human users, the future cyber-tools are extremely insufficient because they keep human-in-the-loop for attack analysis. First of all, these tools are not dynamic enough for performing cyber-attack-analysis even for those known attacks described above because all of them need humans’ help for static analysis. Second, the cyber-defense tools create an overwhelming amount of traffic across the network (e.g. cyber-attacks of polymorphic nature or of using algorithms for generation of large number of domains). Third, present cyber-defense tools cannot detect hardware-based cyber-attacks of advanced persistent threats (APT) nature in which an unauthorized person gains access to a network and stays there undetected for a long period of time, and the attacks resurface again and again creating havoc. Finally, the processing speed for cyber-attack detection/prevention is not only time-intensive, but is also slow because they use a combination dynamic computation and human-static analysis process.
The trends in future cyber-defense tools not only build defenses both in software/hardware, but also need to make their computing processes automatic by removing the human-in-the-loop in the analysis process. Smart richer human-machine interfaces need to play interpreting the results to human users. Although newer cyber-defense tools developed for both software and hardware protection incorporate powerful algorithms, we are in full agreement that the race against cyber-attacks will be lost without artificial intelligence [8] for making them fully autonomous. Artificial intelligence algorithms including machine learning and natural language processing can prevent, detect, and repair the cyber-systems against newer unknown sophisticated cyber-attacks (e.g. polymorphic malware and persistent threats) using an automated process even without human interventions. It will also require powerful human-man cyber-interfaces and even create a new human cyber-culture augmented with artificially cognitive technologies.
First, the most important aspect of the future cyber-defense from a networking point of view is that each node (i.e. terminal, server, and network-switch/router) of the interconnected network shall also be autonomous, acting as the independent entity or equal peer for cyber-defense. As a consequence, the communication architecture between each cyber-entity will be peer-to-peer without creating any additional traffic for cyber-defense over the network. The P2P architecture will enable each entity to execute its processes for cyber-defense autonomously with super-speed without waiting for any information from any other entities. Without this P2P communications architecture, future cyber-defense will become almost ineffective for many future cyber-attacks. Of course, there can be some communications between different network entities for cooperative actions against cyber-attacks informing one another, however, this communication shall be independent of each individual entity’s cyber-defense computing for defending itself. Second, the cyber-defense communications protocol design shall conform to the P2P architecture. Third, the command and control communications architecture for the cyber-defense shall also be P2P. Finally, in this context, we will describe the future overall P2P communications warfighter network architecture in multi-domain formations where the P2P cyber-security communications protocol architecture will be a sub-set of it.
Future Security, Command, and Control
The above analysis shows that the future trends for communications will be primarily P2P to meet the future security needs from a cyber-attack point of view. Each node needs to defend itself as an independent peer. Given the present trends in advancement of computing technologies, the autonomous AI-based robotics will be employed for cyber-defense to meet the future cyber-attacks by the year 2050. As a result, the P2P security protocols will also be deployed given the fact that the early P2P-Vocie-over-IP (VoIP) uses P2P-Session Initiation Protocol (P2P-SIP) standardized in the Internet Engineering Task Force (IETF) standard organization where security protocols align with the P2P communications architecture.
The fundamental new capabilities that the 21st century Army warfighter communications networks are known as mobile ad-hoc network (MANET) communications capabilities in pursuing of random enemies across cross-country, mountains, hills, jungles, and other obstacles as well as join, split, and formation of swarms dynamically in battlespace with sustained operations. It implies that the MANET communications architecture needs to have the following capabilities [7]:
- Every mobile node must act as an independent peer with no functional or operational dependency with any other peers. That is, the MANET network must behave truly as a peer-to-peer (P2P) network.
- The churns of the mobile nodes can be very high which demands that the look-up of the neighboring nodes and re-establishment of the communication network topology, and routing schemes must be very fast. Otherwise, the network topology can be portioned/ fragmented/ disconnected.
An interesting observation of the MANET networking environments can be as follows [7]:
- Each MANET node needs to manage its own security for cyber-attack prevention, detection, and repair the system without depending to any other peers.
- A MANET cannot have any fixed hierarchy that is tied to the physical network topology that is prevalent to the present warfighter command and control architecture either in the ground tier or in the air/space tier.
- In MANETs, there is no need for any centralized network management centers as it is seen in the centralized C/S architecture because each node will do its own management.
- A MANET can be set up just on-the-fly as there is no need for any elaborate test as seen in the classical C/S networking.
- Any node failures can be replaced by any other peer nodes as each peer node has the same capability and thereby enhancing reliability.
- The network itself will not have any fixed infrastructures and only wireless network with P2P communications architecture is able to meet the MANET requirements stated above.
- In some situations, for example – if a network is partitioned, there may not be any end-to-end connection between the source and the destination path for a period of time causing intermittent connectivity.
- The guaranteed quality-of-service (QOS) for audio, video, and data that has been the hall mark of the traditional networks is no longer applicable for MANETs.
- All MANET networking technologies from physical, link/MAC, network, transport, middleware, and application layer must be suitable for working in P2P networking environments.
- There may be longer varying queuing and propagation delays in different nodes of the source-destination path due to the intermittent connectivity.
- Asymmetrical bandwidths requirements may be in MANETs because of different speeds and information transfer (audio, video, and/or data) rates of different mobile nodes.
- Variable high error rates in wireless links with different information transfer rates under different geographical conditions of mobile nodes may also need to be handled by MANET links.
We have also described earlier about P2P networks in the ground and air/space such as the V2V, UAV, R2R, Nano/Micro-S2S, LEO/MEO-S2S and GEO-S2S. In addition, we envision that the classical six tiers (Company, Regiment, Platoon, Squad, Team Leader, and Rifleman) of terrestrial warfighter networks will be “logical” consisting of MANETs instead of rigidly tied to the physical locations. Based on the detail explanations provided earlier with all future technologies, we are now envisioning a new warfighter security, command, and control communication architecture as depicted in Figure 2 by the year 2050. In one instance, we envision that the robotic soldiers are in the forefront fighting the war while augmented human soldiers equipped with cognitive technologies are guiding them from behind, as if “not so much of pitching, but plying umpires” as shown in the rifleman tier of Figure 2. In the same token, in any tier, MANETs consisting of humans and robotics can join, leave, rejoin, and/or swarms, even reducing or increasing hierarchy of logical communication tiers as will to meet the mission objectives dynamically.
We have shown the “logical” view of the hierarchical P2P communication architecture (Figure 2) where the locations of the network nodes can be located physically anywhere in meeting the mission objectives, but only the communications flows will be logically hierarchical. It will also be possible to reduce the logical hierarchy of communications as needed basis dynamically. Figure 2 shows only an example of the future “logical” hierarchy of command and control communications mimicking the present inflexible hierarchy that is tied to the physical hierarchy as well. The use of the P2P communications powered with infrastructure-less wireless networking has freed the nodes to meet the new capabilities for dynamic P2P communications like join, split, rejoin, and/or swarms in the battlespace whether these are humans and/or robotics, and even they can reduce or increase the hierarchy of logical communications flows forming topologies in-the-fly dynamically for security, command, and control to specific meet mission objectives.
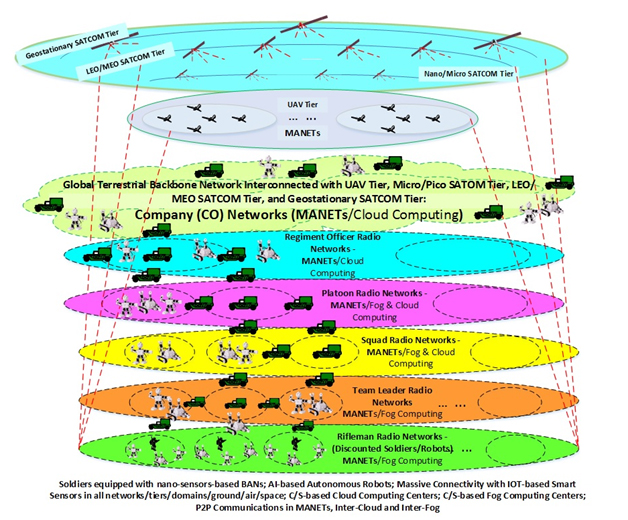
Figure 2: Vision 2050 - High-Level “Logical” View of Future Army Warfighter Network for Security, Command & Control Architecture with Multi-Domain Formations
By the way, there will also be many fixed and/or mobile communication infrastructures like cloud commuting (CC)/fog computing (FC) in the company (CO)/regiment/platoon/squad/ team/rifleman level for example. Coexisting with P2P architecture, these CO and FC centers will use the classical client/server communications architecture serving as the high-end backend processing centers for the P2P architecture-based mobile nodes on-demand. It should be noted that the inter-cloud, inter-fog or inter-cloud-fog communications should also be P2P for reliability purpose.
Conclusion
We have analyzed how the emerging new innovative nano-technologies fueled with new successes of embedding unprecedented processing power into tiny nano-chip level is reshaping the future information communications architecture. The new technologies are not only causing widespread use of AI-based intelligent autonomous robotics in the forefront of communications, they have also been capable to connect each human body connected over the cyber network as if communications mean human’s life. All basic building blocks of these smarter technologies are already emerging right now. By the year 2050, these envisioned technologies such as AI-based intelligence autonomous robotics powered with neural networks and machine learning, super humans augmented with implanted cognitive technologies, smart sensors for providing required ISR and battlefield awareness, smart UAVs tier, smart nano/micro-satellites tier, smart LEO/MEO satellite tier, smart GEO satellites tier, and six logical tiers for terrestrial warfighter networks.
On the other hand, we have shown how new attack surfaces are also emerging for these newer technologies. Cyber-criminals augmented with robotics will have enough power to launch cyber-attacks with unprecedented complexity, frequency, and speed. We envision that a human user will be completely overwhelmed performing cyber tasks unless autonomous robotics especially built for prevention, detection, and repair the cyber-systems automatically without any human intervention are used in multi-domain formations. In addition, we have explained that the security communications architecture needs to be P2P where each cyber-node will act as an independent peer.
Furthermore, we have described with a high-level analysis why all command and control needs to have P2P communication architecture to meet the battlefields’ mission objectives that each peer node of MANETs shall be able to join, leave, rejoin, and/or swarms as will. The cloud computing and fog computing using client-server-based centralized communications architecture will co-exist with P2P architecture severing as backend servers complementing the needs of the peer nodes of the MANETs. All hierarchical levels of command and control architecture such as company, regiment, platoon, squad, team, and rifleman will be logical without being tied to the physical locations completely.
References
- ISTR: Internet Security Threat Report, vol. 21, April 2016.
- Army Research Laboratory (ARL), “Visualizing the Tactical Ground Battlefield in the Year 2050: Workshop Report,” ARL-SR-0327, June 2015.
- T. S. Perry, “A Temporary Tattoo that Senses Through Your Skin,” IEEE Spectrum, May 2015.
- Wael Louis, Majid Komeili, and Dimitrios Hatzinakos, “Continuous Authentication Using One-Dimensional Multi-Resolution Local Binary Patterns (1DMRLBP) in ECG Biometrics,” Journal IEEE Transactions on Information Forensics and Security archive Volume 11 Issue 12, December 2016.
- N. Park and N. Kang, Mutual Authentication Scheme in Secure Internet of Things Technology for Comfortable Lifestyle,” Sensors, December 2015.
- ITU-T Recommendation Y.2060: Next Generation Networks – Frameworks and Functional Architecture Models, June 2012.
- Radhika R. Roy, “Basic Research (Area 6.1) Opportunities in Peer-to-Peer Networking for Army Warfighter Networks,” Technical Note, S&TCD, CERDEC, May 19, 2012.
- Keith More, “The Race against Cyber Crime is Lost without Artificial Intelligence,” ISSA Journal, November 2016.
