Click here to skip to comments.
Editor's Note: While I strive to keep our papers concise, sometimes worthy contributions do not fit neatly into our conventions. This paper is a very professional contribution. While it will be of casual interest to many readers, its real value is in the rigor of the scholarship which can inform both further academic efforts and intelligence analysis. Therefore, we are publishing it at its full length here. Please note that you can click the Adobe Acrobat symbol above to convert this into a PDF for printing or e-reading.
Abstract: This discussion presents a formulation for a computational model that integrates socio-cultural dynamics with kinetic activities in a counterinsurgency environment. We focus on the local population, the key to resolving any insurgency. We describe its structural relationships, which we express as networks based on social roles, values, and power differentials, and as emergent groups of different types. We describe social dynamics which are conditioned by a member of the local population’s relative deprivation, stance, and risk attitude. The expression of the structural relationships through the social dynamics allows us to account for ambiguities in the counterinsurgency environment such as the accidental guerrilla, and groups which go dormant but remain in the corporate memory. We introduce patron-client relationships to account for the importance of selecting an initial point of distribution of resources to a local population, and emergence of alternative structures of legitimacy.
Introduction
The U.S. Department of Defense has long used computational models to support military planning at all echelons – strategic, operational and tactical. Since Cold War planning scenarios assumed the likelihood of attack on the U.S. to be one (a certainty), those scenarios were focused on either the promulgation of an attack or on the response to or the mitigation of one. Analysis of the environment thus focused on kinetic aspects of an engagement. Developments in the analysis of social environments occurred separately from such military planning. In fact, until recently, the problem focus for the development of social simulations has been on private or civil sector problems such as the exercise of social capital through social networks, the modeling of crowds, and the modeling of the behavior of firms or other organizations.
This paper presents an effort to integrate analyses of social and kinetic aspects of a particular type of military engagement through a description of our formulation for a counterinsurgency (COIN) model. We will first introduce briefly the concepts we feel are most salient to COIN warfare in this modeling context. We then outline our specific challenge problem, which focuses on the interaction of kinetic and sociocultural environments. The discussion then moves to the formulation itself. We describe our actors, and their connections through sets of structural relationships. These relationships are expressed as networks based on social roles, values, and power differentials, and as emergent groups of different types. We also describe key social dynamics, conditioned by three primary factors: how much a particular member of the local population cares about his particular situation, which we parse as an expression of his sense of relative deprivation; whom he blames for his situation, which we treat as his stance; and what types of actions he is willing to take, which we express as his risk attitude.
The actors, relationships, and social dynamics we describe are able to express key dimensions of a COIN environment. We can see the emergence of, among others, the opportunistic insurgent (or counter-insurgent) who fights without commitment to an ideological cause, characterized recently as the ‘accidental guerrilla.’[1] This, in turn, leads to a ‘good guy by day, bad guy by night’ phenomenon which we can also accommodate. The dynamics of our emergent groups allow us to handle an ideological or other group which goes dormant but remains in the corporate memory, possibly to be revitalized at some later time. Finally, we introduce a dimension we believe to be novel in COIN computational analyses: that of the patron-client network. This network maps the flow of resources from groups exogenous to the local population into that population, with the accompanying emergence of power differentials and new power structures. We illustrate the inherent (and perhaps necessary) tension between these vertical networks and the horizontal networks that arise from homophily (connections based on similarity or ‘like-ness’). Most importantly, patron-client networks can take on aspects of legitimacy similar to those of a more classic governmental regime, as patrons can generate solidarity based on trust that gives historical depth to the relationship. This solidarity is based on the same type of trust and expectation of fairness that underlies legitimacy.
This work builds on a body of previous work. This stream of research started with collaborative research undertaken with the 1st Marine Expeditionary Force (I MEF) focusing on stability and support operations (SASO). It attempted to create a population of civilians and link their “feelings” about the US with activities that affected their standard of living and social ties.[2] This research continued with a MITRE internal research and development project that attempted to implement Field Manual 3-24 as an entity-level discrete event simulation and link the dynamics expressed within it to the use of improvised explosive devices (IEDs). This research was continued in collaboration with Joint Improvised Explosive Device Defeat Organization (JIEDDO) and also included the University of Vermont, the University of Miami, and the Santa Fe Institute among others, and generated or contributed to a great breath of research.[3] The research team included, among others, an anthropologist, computer scientists, a computational social scientist, an agent-based modeler, and a former Marine with activity duty experience in the Middle East. The basic focus of this latter research is to understand the “ground truth” situation as well as possible through careful data analysis so that we can create the minimally sufficient model formulation to capture the real world dynamics and create an operational level sandbox for option analysis. In what follows we describe the current formulation for this proposed minimum specification[4].
A focus on irregular warfare
The U.S. involvement in COIN in the Middle East has changed the military planning focus. The U.S. no longer assumes a cohesive and well-understood motivation to attack on the part of relatively clearly identified adversaries. In fact, in many cases, it is the multiple and ever-changing motivations of a fragmented adversary to attack or participate in some kinetic activity against the U.S. that are of primary military interest. The U.S. is interested in addressing the ambiguities of a COIN environment. To successfully operate in a COIN environment, the U.S. must understand our adversaries’ full spectrum of motivations and intent.
COIN is a type of irregular warfare (IW). IW is defined by doctrine in the Irregular Warfare Joint Operating Concept (IW JOC) as “a violent struggle among state and non-state actors for legitimacy and influence over the relevant populations.”[5] COIN doctrine states that “[t]he primary objective of any COIN operation is to foster development of effective governance by a legitimate government.”[6] It is this struggle for legitimacy that is the defining characteristic of IW – and therefore of COIN. Since legitimacy depends upon a voluntary (i.e. un-coerced or unrewarded) act of submission to a regime[7] based on the population’s recognition of the regime’s moral authority, the focus of IW is not on control of territory or assets or the exercise of power, but for the ‘minds’ of the population. For this reason, the IW JOC version 2.0 argues that a rich understanding of the sociocultural environment is a key ingredient for success in COIN and other IW activities: “In order to maximize the prospect of success, the joint force must understand the population and operating environment, including the complex historical, political, socio-cultural, religious, economic and other causes of violent conflict.”[8]
Kinetics still play an important role in a counterinsurgency fight, of course. Of perhaps greatest impact to U.S. forces in the current conflict in the Middle East has been the adversary’s use of improvised explosive devices (IEDs). The U.S.’s initial responses to IEDs focused on finding and disabling the devices. Military planners and others soon realized that this was a game of catch-up which would be difficult to win. While not abandoning efforts in this area, U.S. attention has broadened to include efforts to understand and disrupt the socio-technical processes that lead to the manufacture and emplacement of IEDs – i.e., to include upstream activities in counter-IED analyses. Hence, an interest has developed in computational social modeling to address not only the kinetic but also the non-kinetic aspects of the IED problem.[9]
The Challenge Problem
The complex COIN operating environment described by the IW JOC as referenced above is an enormous system with many interdependencies, externalities, and adaptive entities involving both sociocultural and kinetic dynamics. Current analytical tools and techniques fail to reflect the interdependence between the kinetic and social dynamics[10]. Furthermore, interconnectivity and feedback among all the elements of socio-cultural systems creates path dependent dynamics where the order of events impacts future states of the system.[11] This being the case, the most efficient way to understand the dynamics of a system this complex is to simulate it.[12] The most natural way to represent systems of this nature in a simulation is as an agent-based simulation where all entities and their interrelationships can be explicitly represented.[13] We developed such a simulation of the kinetics of Samarra, a city in Iraq. The model was reported to have retrodictively represented changes in the impact of military strategy on the kinetic activity in the area.[14] However, as American interest shifted to Afghanistan and we were asked to move the application target of the simulation and its underlying model, we found that although the model addressed certain aspects of kinetic activities very well, the sociocultural dynamics were incomplete and could not account for the location change. [15] We have thus developed and will describe here a formulation of an agent-based system that addresses the intersection of the social and kinetic spaces in a generic COIN scenario, shaped by a focus on (counter-) IED activity. We phrase the challenge for this project as the development of a computational representation of the interdependence between kinetic and non-kinetic aspects in the COIN environment. As such, our model will need to include representations not only of adversarial and friendly forces, but also the civilian population, and also of the interactions among these three sets of actors.
While the practical relevance for this work certainly will initially be venues in Iraq and Afghanistan as these are of immediate concern for the U.S., our purpose is not to specifically replicate a particular environment or to be able to predict the behavior of individuals in some particular space and time. This model is a strategic tool, not a tactical one. If we are successful, the model will help planners reason about the problem at large and generate scenarios that will broaden the possibility space with which they may engage.
The Model Formulation
This project initially evolved from research by Epstein[16] as well Findley and Young[17]. We also drew upon a broad variety of work in the area of complex conflict dynamics and the dynamics of rebellions and political uprisings.[18]
The U.S. defense modeling and simulation community has a great deal of expertise in kinetics. We drew heavily on this expertise for the parts of our model dealing with kinetics.[19] Although there is within the defense community only a nascent capability in computational modeling of the sociocultural domain,[20] there is even less activity in the integration of the sociocultural with the kinetic domain. Therefore, our discussion here focuses primarily on the sociocultural aspects of our model, with a description of the integration of this dimension with the kinetic.
What follows is a description of the structure of a model. The actors and relationships that we describe here will form the basis of executable code that will allow decision makers to perform certain types of analysis.
An Overview
This section provides a high-level overview of the actors, their relationships and associated social dynamics in our model. Later in the discussion, we shall elaborate on all the terms introduced here.
In any COIN environment, there are three sets of actors. They are the established regime (which includes the host nation and those supporting the regime), insurgents (in a generic COIN sense, those fighting the established regime, which could include members of the local population as well as international supporters), and the local population. These three sets are collections of independently acting individuals. However, the established regime and the insurgents can also act as independent actors (hereafter referred to as collectivities), although the local population cannot. We devote most of this paper to an elaboration of the local population since COIN doctrine states that it is the center of gravity in a counterinsurgency effort.[21]
The dynamics start with a member of the local population assessing how well off he[22] is in relation to others in his social space (i.e., his relative deprivation). He acquires a belief about who is responsible for his perceived condition and who caused people he cares about to come to harm. This is expressed as his stance. He has some inherent risk attitude which will constrain the types of action he is willing to take to improve his condition.[23] Such actions may include both social actions (such as joining groups of various types) and kinetic actions (such as making and detonating IEDs). His relative deprivation, combined with his stance, creates his grievance, which is a surrogate for who he blames for his condition, while his risk attitude conditions what he is willing to do about it. We elaborate upon all these terms later.
Members of the local population create homophilitic connections, i.e. connections based on like-ness, with other members of the local population. (We define homophily in much greater detail later.) Each member considers his homophilitic relationship with other members of the population in terms of both status and values. Connections based on homophily in status and values form horizontal networks which, in turn, lead to the emergence of dynamic, informal groups.
Each emergent dynamic group develops a persona which is a function of the relative deprivation, stance and risk attitude of all the group’s members. The persona thus changes over time as group membership changes – and, in turn, conditions who would be likely to join.
Certain emergent group types require seed resources in order to coalesce. These seed resources can be either endogenous to the local population, or provided to its members from exogenous sources, i.e. the established regime and insurgents. Exogenous provision of these resources could be used to establish patron-client networks.[24]
Patron-client networks are vertical networks which create a tension with the horizontal networks created by connections based on homophily. Furthermore, exchanges between patrons and clients are asynchronous, so the relationships exist over time, unlike the horizontal connections created through homophilitic connections which are synchronous and degrade quickly.
The asynchronosity and other aspects of patron-client networks (which we delineate later) allow those networks to compete for certain aspects of legitimacy with the more formal institutional structures of which regimes consist. Therefore, exogenous resource provision can have an impact on who the local population supports and the channels through which that support is given, in ways that may be rather unexpected (and perhaps unwelcome) to the donor.
As these various types of connection within the local population are formed and dissolved, the insurgents and the established regime are imposing harm on the local population in the form of arrests, kidnappings, killings and the like. They are also providing benefits to that same population in the form of cash or other benefits, as described by the U.S. in various discussions of stability operations.[25] (These form the basis of the patron-client relationships described above.) Additionally, insurgents and the established regime engage in combat operations against each other. In our model, that combat includes use of IEDs and direct fire engagements.
For simplicity, births, immigration, emigration or other endogenous mechanisms of change in the local population are not included in our formulation. However, certain members of the insurgent group and the established regime are replaced at an exogenously determined rate to allow for replacements for combat losses.
The following sections set out an elaboration upon the terms and dynamics introduced above.
Actors
We start with the three sets of actors in the COIN environment. We define them as mutually exclusive high-level actors who exist in both social and geo-physical space. These actors (as introduced earlier) are the established regime, the insurgents, and the local population. The established regime’s goal is to reduce overall violence and to reduce the number of members of the local population who join insurgent-affiliated groups. The insurgents’ goal is to inflict as much damage as possible on the established regime and to increase the number of members of the local population who join insurgent-affiliated groups. The local population is the ‘prize’ in any insurgency environment and is the target of actions by the established regime and the insurgents.[26] The local population presents a shifting landscape of informal groups that form and reform based on social connections established by members as the latter try to achieve various goals. The established regime and insurgents compete for the allegiance of the local population, allegiance expressed in our model by certain actions taken by the local population.
Insurgents and the established regime are two sets of actors, and are groups of a different kind than the local population. As stated previously, insurgents and the established regime, as collectivities, can act as independent actors, although (as we shall see later) their scope of action is relatively limited. That is, the established regime qua established regime can ‘do something’; it can function as a collectivity. The local population, on the other hand, does not act as a collectivity, although groups composed of members with the same job, such as ‘army,’ ‘police,’ ‘farmer,’ and ‘insurgent,’ may function as collectivities.
Individual insurgents and members of the established regime each hold mutually exclusive jobs such as bomb maker or patrol. Mutual exclusivity means that, so long as a given individual holds one job, he cannot hold another. Members of the local population, on the other hand, can hold several jobs and belong to several groups simultaneously, which may allow us to represent, for example, the ‘good guy by day, bad guy by night’ phenomenon. We thus lay the foundation for a rich social environment for the local population, the target of IW/COIN campaigns, and we describe the insurgents and the established regime in relatively simple functional terms.
Members of the local population can simultaneously operate in up to four different social domains: employment, religious, civic, and political. We believe these four domains provide a sufficiently diverse social environment for this model. The religious, civil and political domains correspond to sets of emergent groups (discussed later) which are defined by purpose. The employment domain is further subdivided into varied job functions (hereafter, referred to for simplicity as ‘jobs’) ranging from ‘merchant’ to ‘insurgent’. Each of these functions, in turn, has particular actions associated with it. Each job can act as a collectivity (that is, as a social actor in its own right), but the individuals within the collectivity can also take actions independently of each other and of the collectivity. Of particular interest to us is the insurgent job, as one of the actions that a member of the local population can take in this job is to become an IED emplacer and support those counter to the established regime. Actions for the other jobs are treated abstractly as ‘provide costs/benefits.’ Finally, groups will emerge and recede as a consequence of interactions among members of the local population.
These actors are illustrated in Figure 1 and described in more detail below.
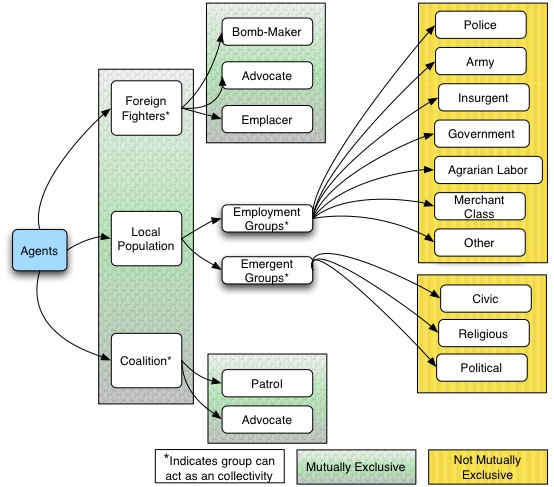
Figure 1: Actors
Insurgents
Members of the insurgent group can have one of three different jobs. First, they can be IED emplacers, in which case their possible actions are to find a cache, acquire an IED, emplace an IED, arm an IED, trigger an IED, and perform battle damage assessment (BDA). Secondly, they can be bomb-makers, in which case their possible actions are to locate a cache, make an IED and to relocate to a new cache if necessary. And finally, there is an ‘advocate’ job. Advocates provide benefits to other actors, and impose costs on actors in terms of killing, injuring, or kidnapping them. (Note that actors may make ‘mistakes’ and impose costs on members of their own side or give benefits to those opposed to them.) We have left benefits abstract in the model, but examples of benefits might be food and medical care for members of the local population. We do not specify cost or benefit types because the type is not relevant to model dynamics. As a collectivity, insurgents can also provide resources to other groups or individuals. Therefore, from the perspective of the local population, insurgents may be viewed positively, negatively, or both.
If IED emplacers and bomb-makers are discovered by the established regime, the established regime will attempt to engage. If insurgents are removed from the battlefield as a result of kinetic engagement with the established regime, they will be replaced at an exogenously determined rate.
The established regime
As mentioned earlier, the established regime can act as a collectivity and have both a positive and negative aspect as perceived by each individual member of the local population. Similar to the insurgents, the established regime as a group can provide resources to groups or to individual members of the local population. Members of the established regime can have one of two jobs: (1) patrol and (2) advocate. The patrol job includes not just patrolling but also executing a convoy mission by moving in concert with other patrols, executing a named operations mission which involves moving to and destroying a cache, or performing BDA after being attacked with an IED. An established regime advocate will provide benefits to and impose costs upon individual members of the local population. As with the insurgents, costs may include arrest, injury or death, and benefits are unspecified. Additionally, if actors in a patrol job are killed by insurgents, they are replaced at an exogenously determined rate, since, as with the insurgents, we assume that the established regime would sustain its force levels with reinforcements.
Local population
The local population is the most complex set of actors in our model, although it does not act as a collectivity per se. (The local population qua local population cannot ‘do’ anything.) This section defines several terms which help us delineate the local population. These terms individuate members of the local population, and establish principles for the dynamics by which they will interact.
We will first discuss how members of the local population define their social identity (defined later in this section) through combinations of attributes which are assigned various weights. We then will describe the social dynamic of homophily. Homophily explains how individuals form social connections by assessing their similarity (likeness) according to various attributes. Once these connections are established, individuals then compare themselves to those with whom they are connected to determine their relative deprivation. They also develop an assignment of blame for their relative deprivation, an assignment we call a stance. Their relative deprivation combined with their stance (how badly off they believe they are relative to others and who they think is to blame for that) yields their grievance. Members of the local population are further individuated by their risk attitude. (We will define risk attitude later in this section.) An individual’s grievance combined with his risk attitude will tell us what types of activities he would be willing to engage in – whether he would be pro- or anti-established regime, for example, and if he would be likely to engage in kinetic activities (e.g. detonating an IED) or less violent (and therefore presumably less risky) activities, such as providing information.
Defining social identity
Recall that in our model, the local population cannot act as a collectivity, unlike the insurgents and the established regime. Also, unlike members of the insurgents and the established regime which, except with respect to their jobs, represent homogeneous groups, each local population member has attributes. The values assigned to those attributes contribute to the individuation of the member’s actions. Each member is also assigned a skill or capability. Planting on a farm, making a bomb, or purchasing food are examples of skills. We will discuss attributes here, and return to skills in a later section on emergent groups.
We have identified eight attributes associated with local population members: ethnicity, tribal affiliation, religion, nationality, gender, marital status, age cohort, and wealth. We believe these attributes provide us the flexibility to represent a rich social environment across time and space. Values for these eight attributes are specified for each member of the local population. Values and weights for each attribute are determined based on the area of interest. (For example, in one area in Afghanistan, the ‘ethnicity’ attribute may have six or seven different values and be weighted less than the tribe attribute in other areas.) Permitting different combinations of weighted attributes allows for creation of a culturally appropriate and relevant population. Setting specific values for attributes and weightings mean that our culture-general concepts are instantiated as a model specific to a culture located in time and space.[27]
Exercising Homophily
Within any social landscape, people tend to connect with others who are like them, although ‘like’ can be defined in a variety of time-, space- and culturally-dependent ways. Analytically, this ‘likeness’ construct is termed homophily. Local population members use their attributes to determine their degree of homophily. We use a more nuanced definition of homophily than is usually found in the computational social modeling literature,[28] as we return to the seminal definition of homophily.[29]
Lazarsfeld and Merton defined two different types of homophily. Status homophily refers to “observed tendencies for similarity between the group-affiliation of friends or between their positions within a group”[30] or similarity in structural position.[31] We use wealth, marital status, age cohort and gender attributes as markers of an actor’s social structural position. Individuals with whom one has high status homophily may become part of one’s status network. Value homophily refers to “observed tendencies towards correspondence in the values [of others]”[32] or similarity in values. We use the ethnicity, tribal affiliation, religion and nationality attributes as indicators of clusters of values. Individuals with whom one has high value homophily may become part of one’s value network. Therefore, our members of the local population have four status-defining and four value-defining attributes, where each attribute has some set of locally determined definitions from which assignments to actors are made. Members of the local population can be like one another in that they occupy similar positions in the social structure, or they can be like one another because of a correspondence in values. This distinction is critical because the social consequences of status homophily differ significantly from those of value homophily.
The social consequences of status and value homophily are explained by reference to two theoretical traditions. Status homophily draws on identity theory, while value homophily pulls from social identity theory.
Identity theory[33] argues that an individual defines his ‘self’ in terms of how well he fulfills expectations of the various social roles from which he may choose.[34] A social role is a set of expectations prescribing behavior that is considered appropriate by others. This approach thus posits a definition of self in terms of others’ (or society’s) behavioral expectations. The complete set of these expectations in a given time and place is a description of social structure.
Social identity theory, on the other hand, focuses on the way in which social categories provide definitions of self and so influence values and attitudes.[35] It focuses on intergroup interaction, suggesting that individuals act as, and are perceived as, representatives of a particular group rather than as unique selves.[36]
Social identity theory also addresses the process of identification with groups, including the formation of stereotypes, the positive valuation of in-group behavior and the negative valuation of out-group behavior. Social identity theory thus has a normative dimension. Identity theory, however, is structural and descriptive. It focuses on descriptions of the roles themselves and their manifestation through behavior and does not assign positive or negative value to those roles. For this reason, the type of self-identification described by social identity theory (self-identification as a member of a group) is more likely to lead to inter-group conflict than is the type of identification developed through role behaviors. In social identity theory, in-group and out-group behaviors become prototyped, stereotyped, and valued. In identity theory, in contrast, the primary dissonance is between individuals who do not agree on role expectations. This could lead to intra-group conflict as we see with (for example) the expression of different expectations for female behavior in some Muslim cultures. This differentiation of status and value homophily allows us to represent more accurately the ways in which members of the local population interact, and the impact of those interactions on individuals’ feeling of relative deprivation (derived from status-homophilitic interactions) or stance (acquired through value-homophilitic interactions), as described in more detail below.
Relative deprivation
An individual will engage with those with whom he has high status homophily (i.e., with those in his status network). Through this engagement, he gains information about his own social condition or quality of life relative to those in his status network. This allows him to determine what is called his relative deprivation.[37] Thus, an individual compares himself to others, not to an objective standard, in order to determine his satisfaction. Efforts by individuals or groups to correct feelings of relative deprivation that emerge from the comparison of oneself to others are likely to lead to social strife or to stimulate the rise of large social movements.[38],[39],[40] When these perceptions of relative deprivation are combined with attitudes of ‘blame’ for that relative deprivation (which we address in the next section on stance), the possibility of social unrest increases.
Stances
A stance, as we use it in our model, is an expression by an individual of whether or not he holds some particular group responsible for his condition (be it good or bad). Stance is distinguished from relative deprivation; the latter is an individual’s assessment of his condition. A member of the local population will consider what he knows about the imposition of costs and benefits from various actors on his value network when determining his stance. His stance will vary over time based on the stances of those with whom he engages and of the groups to which he belongs. (We will discuss how groups develop stances later.) Since stances represent the assignment of a positive or negative value to the group perceived to be responsible for his condition, they are an expression of social identity as distinct from identity (recall the earlier discussion on social identity theory and identity theory), and thus are a function of membership in a value network.
Grievance
The combination of an actor’s relative deprivation and his stance will yield his grievance level. An actor’s grievance is a surrogate for how much he cares about his situation (his relative deprivation) combined with an assignment of responsibility identifying whom he thinks is responsible for his situation (his stance). Figure 2illustrates this. This formulation allows us to avoid the now-discounted theory that deprivation alone (whether it be absolute or relative) leads to violent activity.[41]
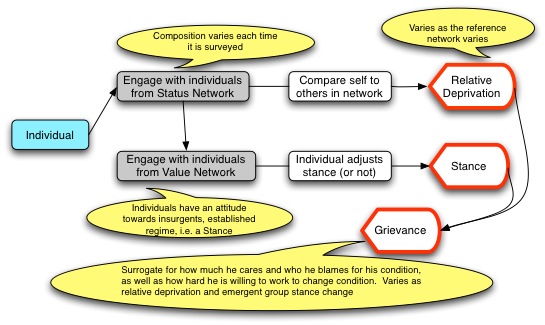
Figure 2: Conceptual model for determining grievance
Risk attitude
An individual actor’s level of grievance will determine how hard he is willing to work to affect his situation. The types of activity in which he is willing to engage will be determined by his risk attitude.[42] Risk attitude describes decision making over quantifiable alternatives under conditions of uncertainty. The classic approach to risk attitude evaluates the behavior of an individual when faced with choices between outcomes quantified in probabilistic terms.[43]
Canonical expected utility theory[44] assumes that all individuals will use the same formula to calculate the riskiness of a given decision, and that a given individual’s risk attitude is not decision-dependent.[45] Therefore, for a given individual, risk attitude will remain constant from one decision to the next. [46] There are, however, differences in risk attitude between one individual and another, with the distribution favoring the risk-avoidant end of an objectively determined scale. Evidence from the literature shows that most individuals show a concave risk function,[47] that is, they are risk-seeking over small stakes and risk-avoiding over large stakes.[48] Evidence from neuroeconomics research is now showing that there also is a significant affective component to what had historically been considered a purely cognitive process. [49]
Our actors face decisions of a relatively limited type and their time frame and social context are highly constrained. Therefore, we feel comfortable in discounting the constructivist approach for this application, in which different responses to the same decision are a function of factors far more complex than just risk attitude.[50] We therefore have randomly assigned each member of the local population a risk attitude which is unchanging over time, accounting for the affective component by the introduction of some randomness. We also skew the assignment curve to represent a population concavely skewed in the direction of risk aversion.
The local population summarized
During his interaction with other actors in his geographic and social space, a member of the local population acquires information about his environment. He uses this information to determine his condition relative to others. This ‘condition’ has two dimensions. One is his general welfare, which we characterize as ‘relative deprivation’ and which is actually determined relatively, not absolutely. As described earlier, this is determined based upon a comparison of himself with others in his status network, where his status network is defined by status homophily. The other dimension of his condition is his attitude towards various collectivities (e.g. insurgents or the established regime). We call this his stance, understood to be his attitude towards those whom he thinks ‘are responsible’ for his relative deprivation. As this stance reflects values and attitudes, it is conditioned by members of his value network, defined by value homophily.
The combination of the actor’s perceived relative deprivation and his stance generate his grievance toward various collective actors, a surrogate for the level of activity in which he is willing to engage. His risk attitude tells us in what types of activity he is willing to engage. An individual with high grievance and high risk aversion may be willing to work very hard to support the established regime (if he has a pro-established regime or anti-insurgent stance), but may not be willing to do it in ways that put himself in significant harm’s way. For example, he might be willing to provide information secretly but not to become a policeman. Figure 3 summarizes this progression to action on the part of an individual member of the local population.
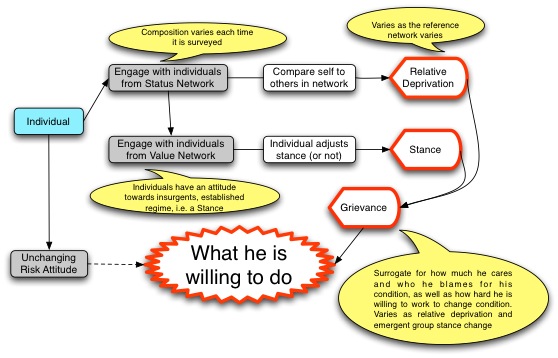
Figure 3: Progression to action- local population
Consequences of social dynamics: emergent groups
A critical outcome of interactions among the members of the local population is the appearance of emergent groups. These collectivities may form and dissolve very quickly, creating a shifting yet significant social landscape. Our discussion of emergent groups will show, among other things, how social memory can be important, how groups which form around key individuals can or cannot affect the flow of resources and influence through a population, and what the consequent impact is upon grievances.
Emergent groups are collections of members of the local population. Each collection has a purpose and performs activities that help it fulfill that purpose. For example, an emergent group may have as its purpose to provide security for a neighborhood. Associated activities might be acquiring weapons, shooting at intruders, patrolling, and the like. Each activity requires a certain set of skills which are provided to the collection by its members. Recall that each population member has a set of skills. Skills exist within the group in a Hayekian sense[51]: if one member of an emergent group has a necessary skill, then the group has that necessary skill.
We base our construct of emergent groups on Robert Axtell’s model of firms,[52] with some modification of his initial assumptions. Like Axtell, we assume an emergent group (in Axtell’s terms, a firm) is a collection of individuals who are motivated (working) to change the status quo. We believe this is as applicable to the socio-political domain as it is to the economic domain because, for example, one way of characterizing insurgent groups is as firms whose product is violence.[53]
We represent three distinct emergent group types that members of the local population may choose to join. Each type provides benefit or welfare differently to its members. The groups are as follows: 1) decreasing returns to scale groups where the addition of an individual decreases the benefit or welfare produced per unit of labor (for example, common pool resources like water or grazing land may become stretched more thinly by the addition of new group members); 2) constant returns to scale groups, where the addition of an individual has no impact on the amount of benefit or welfare produced per unit of labor (as may be the case with religious, social or ideological groups); and 3) increasing returns to scale groups where the addition of an individual increases the amount of benefit or welfare produced per unit labor (think of a traditional western economic group or firm, where adding an individual with some unique skill can significantly enhance others’ productivity).[54]
Members of the local population join emergent groups and devote their limited time to engaging in the activities of the emergent groups of which they are a part in order to improve welfare. The amount of welfare a group member derives from his actions as a member of that emergent group is a function of two things: the overall size of the group and how much the member’s endogenous skill set is valued by the group. Members with high value skills (i.e. skills that are scarce but essential) receive more welfare than members with low value skills.[55] Consistent with Axtell, new increasing returns emergent groups can be started by anyone; however, in our construct these individuals must have accumulated welfare or be funded to do so. Resources to start a new increasing returns group may also come from a source exogenous to the local population, i.e. the established regime or the insurgents.
Members of the local population learn about emergent groups by interacting with members of their status networks. A member of the local population will check the emergent group memberships of the members of his status network. He then checks the emergent group’s risk attitude and stance (the group’s risk attitude and stance are a function of those of all of its members) and, if it is compatible with his own, he might join. He also will assess the riskiness of exercising his particular skill in the execution of the group’s activities based on its history over some time period. We approximate his incomplete information and possibly suboptimal decisions by bestowing bounded rationality upon the local population.[56]
A new emergent group reflects the founding member’s stance and his risk attitude, as he is the only member. As new members join, their stance and risk attitude modify the stance and risk attitude of the group (its persona). As a result, over time the older members may leave the group if the stance and/or risk attitude of the group moves too far away from their own. Furthermore, as the risk attitude changes, the types of activities in which the group will engage also will change (e.g. a group may move more towards violent activities as its risk aversion decreases). It is also possible that an actor will re-join an emergent group he previously left as it moves back towards his own risk attitude and stance. It is movement in the endless social dance.
Emergent groups will go ‘dormant’ if they have no members. Dormant groups still exist in the social memory, holding the risk attitude and stance they had at the time they went dormant. Such groups can be revived if actors’ stance and risk attitude match with the dormant emergent group’s ‘remembered’ attitudes. This feature allows us to account for the power of history/myth.
New increasing returns to scale groups require an investment which may or may not come from the founding member (i.e. it could come from an exogenous source such as the established regime or the insurgents). If the initial investment comes from the established regime or the insurgents, the founding member of the group is the initial recipient of those resources. He then uses those resources to start an increasing returns emergent group or a patron-client network, which we describe in the next section.
The persona of a new increasing returns group (unlike decreasing or constant returns groups) is a function of the risk attitude and stance of both the source of resources (which may be exogenous) and the new increasing returns group founding member. If the founding member is also the resource provider, his risk attitude and stance alone create the group’s persona. As the group gets larger and as time progresses from when the group was founded, the founder’s influence will wane. Eventually, the character of the emergent group may diverge sufficiently from that of the founder that the group severs the tie with the founder.
We have illustrated the relationships and dependencies that create emergent groups in Figure 4.
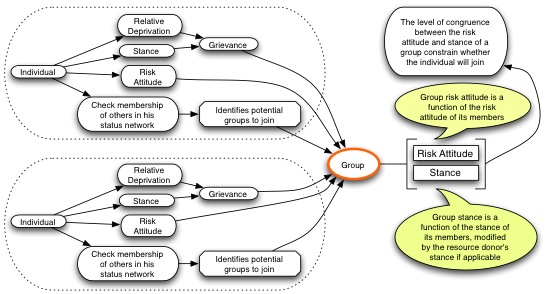
Figure 4: Joining a group
Patron-client relationships
The emergent groups described in the previous section are groups based on horizontal connections – they are peer-to-peer groups, where a member of the local population makes a decision whether or not to join based on interactions with his peers through exploitation of homophilitic connections. However, there are other types of relationship based on differences in power (asymmetries) rather than on similarities of attributes in a group of equals. Of interest to us here is the patron-client relationship.
The inclusion of emergent group dynamics allows us to address the special case where resources are provided by a source exogenous to the local population. A patron, by definition, provides a bridging function for his client to resources to which the client otherwise would not have access. We will define this in greater detail later – but we note here that this source could be (but is not necessarily) ‘international’ in nature. This allows us to explore the impact of selecting a particular recipient of resources provided by (e.g.) the established regime to the local population. We note particularly that that success or failure of an increasing returns group will be highly dependent on the characteristics of the individual to whom the resources are initially given, as the group’s immediate and distant future are conditioned by the founding member’s horizontal (homophilitic) relationships. This suggests that the selection of the recipient of these resources in the COIN environment may indeed be important,[57] as the recipient may start an increasing returns group that is embedded in the existing social structure, or instead start a patron-client network that could potentially compete with the existing power structure.
Patron-client relationships tend to emerge in social environments in which not all participants have equal access to necessary social resources. These societies are often characterized by significant power differentials, in practice usually a strong center and a weak periphery.[58] Patrons often perform a bridging function between powerful and outwardly focused organizations (e.g., a centralized government) and local, less powerful individuals often found at the periphery of states.
Patron-client relationships, in our intended sense, are typified by the following characteristics.[59],[60],[61],[62] Patron-client ties are relationships between inherently unequal individuals (not groups) . One member of the dyad is always more powerful than the other. These relationships are mechanisms to facilitate exchange, thus they depend upon reciprocity. That said, the nature of the thing (whether it be something concrete or more abstract like money or favors) that flows up the dyad is usually different in kind from that which flows down. Although their locally determined value is roughly equal,[63] the exchange is asynchronous. The relationships are extra-legal if not illegal. If extra-legal, they are generally ignored rather than negatively sanctioned by the formal legal system. Patron-client relationships often emerge in times of social disturbance, although this is not the only time we see them.[64] Patron-client relationships are usually entered into voluntarily, although there is often significant social pressure for individuals to enter into them, and there are strong social sanctions for violating the local norms regarding entering, engaging in, and exiting such relationships.
The asynchronous nature of the exchanges is an important characteristic of the relationship. It is possible that generations will pass before the exchange is completed.[65] This asynchronicity establishes solidarity over time between the receiver and the giver, a solidarity based on trust. Marcel Mauss called this a type of generalized exchange.[66],[67] He explained it in terms of gifts (e.g., I give you a birthday gift and I have established an obligation on your part to reciprocate at some time in the future), but generalized exchange describes many other types of exchange such as returning favors.[68] In addition to solidarity, the notion of asynchronicity provides an historical depth that is lacking in a transaction-based system.
The primary strong connection in a patronage relationship is a vertical one, so patronage networks have the potential to challenge, undermine or complement the strength of horizontal or peer-to-peer relationships.[69] Our emergent increasing returns groups lie at the nexus of vertically defined patronage networks and horizontally defined groups, such as status and value networks. Suppose the insurgents or the established regime give resources to an individual. The resource recipient can then create a patronage network by disbursing the resources, serving a bridging function between the larger world of the insurgents and the established regime and the more circumscribed world of the local population. However, once those resources ‘hit the streets,’ horizontal ties may draw peers of the client into the group. This would then create an emergent group, diluting the influence of the patron and his sponsors. Including patron-client relationships in our model thus introduces a necessary tension between the vertical ties generated by power differentials and the horizontal ties stimulated by homophily. This tension illuminates the consequences of a critical COIN activity – the disbursement of resources to a local population.
Power and legitimacy
The patron-client relationship with its strong social sanctions in cases of violation introduces notions of power and legitimacy. It is worth taking some time to explore this concept as legitimacy for a regime[70] is the end game of IW/COIN. Furthermore, power (which can be exercised through the disbursement of benefits as well as coercion) is often confused with legitimacy, although they are qualitatively different concepts.[71]
Power is a mechanism to shape the behavior of others. It is exercised either by threatening or using coercion to deter or change undesired behavior or by promising rewards to promote desired behavior (i.e. to engender satisfaction).[72] This is an instrumental or conditional means of social control (‘if I do this, then you will do that’)[73] and is a function of the amount of coercion exerted and the benefits provided.
Power, which results from the combined exercise of coercion and reward, generates compliance with particular authorities (people) or particular directives issued by the regime.[74] It thus is particularistic as it is support for a specific action or a specific person, not for an institution or a system of government (i.e. regime).
Instrumental power of the type we just described is a very expensive means of social control because of the element of coercion or benefits provision.[75] Coercion and the provision of benefits are socially expensive as they require the investment in individuals who can continuously monitor behavior and apply either positive or negative pressure to induce compliance whenever necessary. Achieving legitimacy is another way in which regimes can exercise social control, in this case without the threat of coercion or the promise of rewards.[76]
Legitimacy is often defined as a function of procedures that are perceived to be fair, where “fair” is defined by the target population.[77] There are three important elements to this definition. First, it is critical to recognize that legitimacy is the function of a populace’s perception of a regime, not of characteristics of the regime itself. Second, the entity which has legitimacy is a procedure or set of procedures, often embodied in institutions which themselves may be collected into regimes. And third, the focus is on process credibility or fairness.
Thus the end game of a COIN or insurgency operation is the establishment of the legitimacy of the regime that each participant supports. Establishment of legitimacy requires the shaping of the perceptions of the population. Changing the regime may be necessary to establish legitimacy but will not necessarily be sufficient. Legitimacy cannot be legislated or decreed and may emerge in unplanned ways. For example, earlier we introduced an informal power structure constructed around the patron-client relationship. We emphasized that this relationship is generally extra-legal if not illegal, yet carries strong social sanctions in instances of violation. We also pointed out that the asynchronicity imbues the relationship with historical depth that allows for the assessment of the process over time. In this way, a patron-client network (patrons with their several clients) can be perceived to have ‘legitimacy’ in many of the same ways as a governmental structure. As such, it should be explicitly considered in the COIN environment.
Kinetic activity
In our earlier description of the insurgents and the established regime, we said that they could both impose costs and provide benefits. By introducing notions of cost and benefits, we introduced a notion of power. Recall also that IW (and COIN as a particular type of IW) is “a violent struggle for legitimacy and influence over the relevant population”[78] (emphasis added). A model of the COIN environment is thus incomplete without consideration of the exercise of power through violence.
Our primary actors in the kinetic domain are the insurgents and the established regime. The local population engages as one of the targets of the kinetic actions, as a participant through the insurgent job or jobs with the established regime, and as a provider of information to the insurgents and/or the established regime (see Figure 1). Thus, although the local population is the ‘prize’ of a COIN operation, it also can be an active participant supporting either player in the COIN struggle or can become a target or collateral damage.
The violent activities we represent center around the employment of IEDs and direct fire weapons. We understood the IED process to involve bomb-makers and emplacers. Members of the local population who join the job group ‘insurgents’ also can choose to become emplacers if their level of risk aversion is low enough. If their risk aversion is high but their anti-established regime stance is strong, members of the local population can engage in information gathering activities for the insurgents instead of becoming emplacers.
The IEDs are emplaced along routes traveled by the established regime. Members of the established regime patrol, or travel in convoys, both of which are vulnerable to IEDs. They also perform operations to find and defuse IEDs.
The interaction between members of the established regime and insurgents will affect the number of IEDs that are actually emplaced and so detonated. Members of the local population can affect the number of IEDs emplaced by providing information to insurgents or to the established regime. Information provision actions will be taken by individuals who are (for example) supportive of the established regime but with a risk aversion high enough to preclude them from taking jobs such as army, police, or government.
If an IED explodes, everyone (local population included) within the blast radius is a potential victim. Both the insurgents and the established regime collect information about each IED event in a ‘corporate’ memory; this allows the insurgents to adapt their activities to the regime, and vice versa.[79]
Civilian deaths and injuries from IEDs and other costs are recognized as negative actions by the victim’s value network, causing its members to adjust their stance negatively towards the perpetrator. A change towards a more negative stance also will change grievance levels and therefore the actions actors are willing to take. (Note that the individual’s risk attitude does NOT change.) Conversely, if a group bestows benefits on another group or on an individual, the group’s or individual’s stance will adjust positively. Figure 5 illustrates the change in an individual’s propensity for violent action.
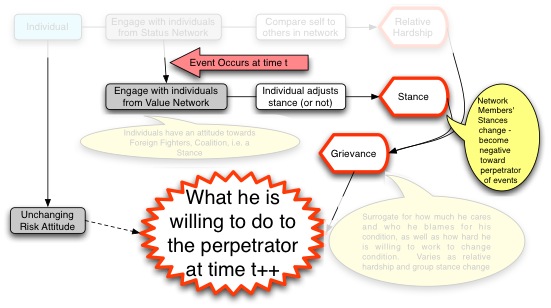
Figure 5: Change in propensity for violent action
Conclusion
This formulation is an essential first step in the development of a theoretically grounded simulation of the COIN environment. The socially rich environment we have articulated here allows us to account for various phenomena that have contributed to the ‘messiness’ and difficulty of prosecuting irregular wars, including the link between social interaction and kinetic behavior. It allows us, for example, to account for the ‘accidental guerrilla’[80] – the individual who has no particular ideological stance but who reacts to very locally imposed costs and who looks toward some insurgent group to help address his relative deprivation (i.e., provide financial incentive, other economic opportunity, or other benefit). While economic deprivation is arguably not the primary motive for all insurgents, we must allow this as a possibility. We also account for the ‘good guy by day, bad guy by night’ phenomenon that often characterizes the COIN environment. A member of the local population may belong to several emergent groups as each provides him with a different or additional benefit. Since he can belong to several emergent groups simultaneously, he can hold what might appear to be contradictory beliefs simultaneously (e.g. pro-established regime, pro-insurgents). As a result, we are able to differentiate (to some first order) among behaviors that may look the same but be driven by different motivations. Our inclusion of the patron-client dynamic along with the dynamics of emergent groups shows how an initial distribution of resources can affect their ultimate disposition, and stimulate the emergence of legitimate social structures. Finally, the interdependence between the kinetic and socio-cultural dimensions, which we have illustrated with our preliminary results, show that it is possible to represent these dynamics with potentially useful results for planners and decision-makers.
We are hopeful that this approach to presenting and manipulating the intersection between the kinetic and socio-cultural domains will provide strategic-level decision makers and planners with a better understanding of how to achieve strategic goals such as the development of legitimacy. We also believe it may help on the operational level, illuminating such phenomena as counter-government behavior driven both by ideology as well as more instrumental factors such as local power struggles or financial needs. Ultimately, we are exploring the interdependent relationship between social and kinetic operations in the COIN environment. We have conceptualized that relationship as a proxy, to some degree, for the relationship between legitimacy and power, recognizing legitimacy as the desired end state of a COIN operation.
[1] See David Kilcullen. 2009. The Accidental Guerrilla: Fighting Small Wars in the Midst of a Big One. Oxford University Press. New York, NY
[2] Koehler, M. and P. Barry (2004). Case Study: Using Agents to Model Stability and Support Operations. Proceedings of the Agent 2004 Conference. Argonne National Lab, Chicago, IL.
[3] Bohorquez, J. C., et al. (2009). Common Ecology Quantifies Human Insurgency. Nature, vol. 462, pp. 911-914; Johnson, N. Spencer Carran, K.Fontaine, N. Laxague, P. Nuetzel, J.Turnley, B. Tivnan. (2011). Dynamic Red Queen explains patterns in fatal insurgent attacks. Science, vol. 333, no. 6038, pp. 81-84; Tivnan, B., et al. (2009) COIN 1.0 Technical Report. Posted on Defense Technical Information Center (DTIC), http://handle.dtic.mil/100.2/ADA552516; Tivnan, B., et al. (2010). COIN 1.5 Technical Report, available from Joint Improvised Explosive Device Defeat Organization (JIEDDO).
[4] A more detailed description of the current formulation is posted on DTIC, see Tivnan, B., et al. (2010). COIN 2.0 Technical Report. http://handle.dtic.mil/100.2/ADA552522.
[5] United States. Department of Defense. 2010. Irregular Warfare: Countering Irregular Threats. Joint Operating Concept Version 2.0 17 May 2010 (IW JOC) p.9
[6] Unites States. Department of the Army. 2007. The U.S. Army/Marine Corps counterinsurgency field manual. U.S. Army FM3-24. With forewords by General David H. Patreaeus and Lt. General James F. Amos, and by Lt. Colonel John A. Nagl; with a new introduction by Sarah Sewall. University of Chicago Press. Chicago, IL. ¶ 1-113
[7] ‘Regime’ is a collection of institutions (themselves structures and processes) that provides a governance function for a group of people. It may or may not be institutionalized as a nation-state. Tribal areas such as the Federally Administered Tribal Areas are governed by a tribal regime, in addition to the governance the Pakistan government provides.
[8] Ibid. p.5
[9] See for example the U.S. Department of Defense Human Social Cultural Behaviour Modeling Applied Research program http://comptroller.defense.gov/defbudget/fy2010/budget_justification/pdfs/03_RDT_and_E/Vol_3_OSD/OSD_PB10_RDTE-BA_1-3.pdf. P.49ff;; National Research Council. 2003. Dynamic Social Network Modeling and Analysis: Workshop Summary and Papers. Ronald Brieger, Kathleen Carley, and Philippa Pattison. Committee on Human Factors. Board on Behavioral, Cognitive and Sensory Sciences. Division of Behavioral and Social Sciences and Education. The National Academies Press. Washington, DC.; Counterterrorism’s new tool: ‘Metanetwork’ analysis. Science. Vol 325. 24Jul2009 Pp409-411
[10] MG Michael T Flynn, CPT Matt Pottinger, Paul D. Batchelor. 2010. Fixing Intel: A Blueprint for making information relevant in Afghanistan. Jan 2010. Center for A New American Security Washington, DC.
[11] Page, Scott. 2006. Quarterly Journal of Political Science 2006 Path Dependence. Vol 1 Pp87-115
[12] Buss, S.R., C.H. Papadimitriou, and J.N. Tsitsiklis. 1991. On the Predictability of Coupled Automata: An Allegory about Chaos. Complex Systems, 5: 525-539.
[13] Axtell, R. L. (1999). Why Agents? On the Varied Motivations for Agent Computing in the Social Sciences. In C. M. Macal & D. Sallach (Eds.), Proceedings of the Workshop on Agent Simulation: Applications, Models and Tools (pp. 3-24). Chicago, IL: Argonne National Laboratory..
[14] Weinberger, S. Web of War: Nature vol 471 31 Mar 2011 Pp566-568 P.568
[15]If the reader is interested in details of our previous formulations, please see www.dtic.mil as cited above. Additional details on specific applications of this model to Iraq and Afghanistan may be obtained from JIEDDO, but distribution is limited to For Official Use Only and higher.
[16] Epstein, J.M. 2002. Modeling Civil Violence: An agent-based computational approach. Proceedings of the National Academy of Science. Vol.99. Pp7243-7250.
[17] Findley, M.G. and J.K. Young. 2007. Fighting fire with Fire? How (not) to neutralize an insurgency. Civil Wars. Vol.9. Issue 4. Pp.378-401.
[18] Cederman, L., (2003). Modeling the Size of Wars: From Billiard Balls to Sandpiles. American Political Science Review, vol. 97, no. 1. Lichbach, M., and T. Gurr. (1981). The Conflict Process. (1981). Journal of Conflict Resolution, vol. 25, no. 1, pp. 3-29. Lichbach, M., (1987). The Puzzle of Aggregate Studies of Repression and Dissent. Journal of Conflict Resolution, vol. 31, no.2, pp. 266-297 Lichbach, M (1994). What Makes Rational Peasants Revolutionary? World Politics, 46, pp 383-418. Lohmann, S., (1993). A Signaling Model of Informative and Manipulative Political Action. American Political Science Review, vol. 87, no. 2. Lohmann, S., (1994). The Dynamics of Informational Cascades. World Politics, 47, pp. 42-101. Moore, W. (1995). Rational Rebels: Overcoming the Free-Rider Problem. Political Research Quarterly, vol. 48, no. 2, pp. 417-454.
[19] See, for example, work from the U.S. Department of Defense Modeling and Simulation Coordination Office www.msco.mil
[20] U.S. Department of Defense. Defense Research and Engineering. Human Social Cultural Behavior Program
[21] See U.S. Department of Defense. Department of the Army. Op. cit
[22] Although we use the pronoun ‘he,’ we recognize that the local population is two-gendered. This recognition is explicitly represented in the model through the assignment of a male or female value to a gender attribute, explained later.
[23] In this regard, members of the local population are boundedly rational and may not make “optimal” decisions regarding how to improve their quality of life. See Simon, H. (1957). "A Behavioral Model of Rational Choice", Models of Man, Social and Rational: Mathematical Essays on Rational Human Behavior in a Social Setting. Wiley, New York, NY.
[24] See for example S.N.Eisenstadt and Louis Roniger. 1980. Patron-Client Relations as a Model of Structuring Social Exchange. Comparative Studies in Society and History. Vol.22. No.1 Pp.42-77 and David Kilcullen. 2010. Counterinsurgency. Oxford University Press. New York, NY. Pp.183-184
[25] United States. Department of Defense. Department of the Army. 2008. FM3-07. Stability Operations. October 2008.
[26] U.S. Department of Defense. Department of the Army. 2007. Op.cit
[27] See Jessica Glicken Turnley. 2011. Cross-cultural Competence and Small Groups: Why SOF is the way SOF is. JSOU Report 11-1, March 2011 Joint Special Operations University, US SOCOM. Hurlburt Field, FL. for a discussion of culture-general and culture-specific concepts.
[28] See for example Carley, K. (1991). A Theory of Group Stability. American Sociological Review , 56 (3), 331-354.
[29] Paul F. Lazarsfeld and Robert K. Merton. (1954). Friendship as Social Process: A Substantive and Methodological Analysis. in Freedom and Control in Modern Society. Morroe Berger, Theodore Abel and Charles H. Page, eds. Octagon Books. New York, NY. Pp. 18-66
[30] Ibid., p.24
[31] It is interesting to note that there has been a recent surge of interest in structural similarity in social network studies. It is now called ‘structural equivalence’ and is generally studied as a discrete phenomenon. See for example Ronald Burt who argues that physicians (his case study) may adopt a new drug through a phenomenon he calls contagion. Although the physicians may never meet face to face they ‘engage’ with each other by virtue of a common position in the social structure and adopt a new drug because of behaviors expected of someone in their position. Ronald Burt. 1987. Social Contagion and Innovations: Cohesion versus Structural Equivalence. The American Journal of Sociology. Vol.92. No.6. Pp.1287-1335. .
[32] Lazarsfeld and Merton op.cit P.32
[33] First introduced by Sheldon Stryker. 1968. Identity Salience and Role Performance. Journal of Marriage and the Family. Vol.4 Pp.558-564
[34] Michael A. Hogg, Deborah J. Terry and Katherine M. White. 1995. A Tale of Two Theories: A Critical Comparison of Identity Theory with Social Identity Theory. Social Psychology Quarterly. Vol.58, No.4 Pp. 255-269. P.257
[35] Henri Tajfel. 1982. Social Psychology of Intergroup Relations. Annual Review of Psychology. 33:1-39
[36] Hogg, et.al. op.cit. P.261
[37] Robert Merton. 1957. Social Theory and Social Structure. (Revised and enlarged edition). The Free Press. New York, NY. p.235
[38] Walter Garrison Runciman 1966. Relative deprivation and social justice: a study of attitudes to social inequality in twentieth-century England, University of California Press. Berkeley, CA.
[39] Merton, Robert K. 1938. “Social Structure and Anomie.” American Sociological Review 3 (1938): 672-682.
[40] Ted Robert Gurr. 1970. Why Men Rebel. Princeton University Press. Princeton, NJ.
[41] See, for example, Marc Sageman. 2004. Understanding Terror Networks. University of Pennsylvania Press.
[42] O’Neill. Op.cit.
[43] Allison B. Rosen, MD, MPH, Jerry S. Tsai, MS, Stephen M. Downs, MD, MS. 2003. Variations in Risk Attitude Across Race, Gender, and Education. Medical Decision Making (Nov-Dec 2003). Pp.511-517. P.511.
[44] See J. von Neumann and O. Morgenstern 1947 Theory of games and economic behavior, 2nd ed. Princeton, NJ: Princeton University Press
[45] Prospect theory, a variation of utility theory, requires that the mid- or risk neutral point of the risk attitude scale is individually determined by each decision maker rather than holding it constant across all decision-makers (See Kahnaman and Tversky). In our model we assume a mid-point and do not address how it is established.
[46] Ted Martin Hedesström. 2006. The psychology of diversification: Novice investors’ ability to spread risks. Department of Psychology, Göteborg University, Gothenburg, Sweden P.2
[47] Barry O’Neill. 1998. Risk Aversion in International Relations Theory. Projektbereich B: Discussion Paper No. B-445. Dec. 1998. P.4
[48] Helga Fehr-Duda, Adrian Bruhin, Thomas F. Epper, and Renate Schubert. 2008. Rationality on the Rise: Why Relative Risk Aversion Increases with Stake Size. Socioeconomic Institute, University o f Zurich. Working Paper No. 0708, February 2008, revised edition.
[49] Camerer, Colin F., Loewenstein, George F. and Prelec, Drazen, Neuroeconomics: How Neuroscience Can Inform Economics. Journal of Economic Literature, Forthcoming Available at SSRN: http://ssrn.com/abstract=590965 accesses 6/27/08
[50] John W. Payne, James R. Bettman and Eric J. Johnson. 1992. Behavioral Decision Research: A Constructive Processing Perspective. Annual Review of Psychology. Vol.43 Pp.87-131. P.91
[51] Hayek, F. (1945). The Use of Knowledge in Society. The America Economic Review, vol. 35, no. 4, pp. 519-530. And Hayek, F. (1960). The Constitution of Liberty. University of Chicago Press, Chicago IL.
[52] Axtell, R., (2001). Zipf Distribution of U.S. Firm Sizes. Science, vol. 293, pp. 1818 – 1820. And Axtell, R. (1999). The Emergence of Firms in a Population of Agents: Local Increasing Returns, Unstable Nash Equilibria, And Power Law Size Distributions. Center on Social and Economic Dynamics, Working Paper No. 3. Available at www.brookings.edu.
[53] Clauset, A. and K. S. Gleditsch (2009). The Developmental Dynamics of Terrorist Organizations. http://arxiv.org/pdf/0906.3287
[54] W. Brian Arthur’s 1994. Increasing Returns and Path Dependence in the Economy. University of Michigan Press, Ann Arbor.
[55] Johnson, N. (2009). Human group formation in online guilds and offline gangs driven by a common team dynamic. Physical Review E, vol. 79, 066117
[56] Simon, H. op. cit.
[57] Jerry Meyerle, Megan Katt, Jim Gavrillis. 2010. Counterinsurgency on the ground in Afghanistan: How different units adapted to local conditions. November 2010NCNA Analysis and Solutions. Washington, DC
[58] David Kilcullen and Thomas Barfield (among others) have characterized Afghanistan as such a society. David Kilcullen. 2010. Counterinsurgency. Oxford University Press. New York, NY. Pp.183-184. Thomas Barfield. 2010. Afghanistan: A cultural and political history. Princeton University Press. Princeton, NJ
[59] Karl D. Jackson. 1980. Traditional Authority, Islam, and Rebellion: A study of Indonesian political behavior. University of California Press. Berkeley, CA. Pp.188-192.
[60] Eisenstadt and Roniger, op.cit. Pp.49-50
[61] Alex Weingrod. 1968. Patrons, Patronage and Political Parties. Comparative Studies in Society and History. Vol.10. Pp.377-400, esp. Pp.378-380
[62] Domonic A. Bearfield. 2009. What is Patronage? A critical reexamination. Public Administration Review. Vol.69, No.1. Pp.64-76
[63] Jackson, op.cit. P.189
[64] Ibid. P.190
[65] See S.N.Eisenstadt and Louis Roniger. 1980. Patron-Client Relations as a Model of Structuring Social Exchange. Comparative Studies in Society and History. Vol.22. No.1 Pp.42-77. Pp.49-50; Alex Weingrod. 1968. Patrons, Patronage and Political Parties. Comparative Studies in Society and History. Vol.10. Pp.377-400, esp. Pp.378-380.
[66] Marcel Mauss. [1923] 1954. The Gift: Forms and Functions of Exchange in Archaic Societies. Ian Cunnison, trans. With an introduction by E.E.Evans-Pritchard. W.W. Norton & Co. New York, NY.
[67] Eisenstadt and Roniger, op.cit. P.52
[68] Mauss, op.cit.
[69] Jackson, op.cit. P.189.
[70] Recall our earlier definition of a regime as a collection of institutions (themselves structures and processes) that provides a governance function for a group of people.
[71] Much of the following discussion is taken from Jessica Glicken Turnley. 2008. Legitimacy and Power: An Exploration of Doctrine as it Relates to PSOM White paper prepared for U.S. Department of Defense, Joint Staff (J8), Warfare Analysis Division. Washington, DC
[72] Tom. R. Tyler. 2006. Psychological Perspectives on Legitimacy and Legitimation. Annual Review of Psychology. Vol.57. Pp.375-400 p.376
[73] Michael Bratton and Robert Mattes. 2001. Support for Democracy in Africa: Intrinsic or Instrumental? British Journal of Political Science Vol.31, no.3:Pp.447-474. P.448.
[74] M. Stephen Weatherford. 1987. How Does Government Performance Influence Political Support? Political Behavior. Vol.9, no.1. Pp.5-28. p.12
[75] Tyler. op. cit. p.376
[76] R. Ford and C. Johnson. 1998. The perception of power: dependence and legitimacy in conflict. Social Psychology Quarterly. Vol.61. Pp.16-32; JRP French Jr. and BH Raven. 1959. The bases of social power. In Studies in Social Power. D. Cartwright, ed. University of Michigan Institute of Social Research. Ann Arbor, MI. Pp.150-167.
[77] See Tom. R. Tyler. 2006. Psychological Perspectives on Legitimacy and Legitimation. Annual Review of Psychology. Vol.57. Pp.375-400 for a review of this literature.
[78] United States Department of Defense. 2010. op.cit., P.9
[79] Johnson, N. op. cit.
About the Author(s)
Comments
Pg Soft can be played on all…
Pg Soft can be played on all platforms. Supports all systems, 100% safe, can play 24 hours a day. The more you play, the richer you are.
Just a comment on figure 3;
"What is he (member of local population) willing to do?" is part of this regimented, systematized, and highly neo-positivist approach to warfare.
The 'what' appears, from my perspective, that the authors apply a universal explanation for human motivation here for COIN (and essentially all conflict). This 'rational actor' approach completely ignores non-western and alternate logics of various groups, ideologies, and individuals.
"What is he willing to do" is hardly as critical as exploring "why is he willing to do it"- the why seeks explanation of the deeper tensions; the 'what' leads to micro-tactical categorization, like tagging fish on a boat for catch and release. We may figure out how many fish are in a lake, but we never get to the larger issues of environmental change because we are too busy tagging fish.
This article spends a bit too much time attempting to "solve the COIN problem" and not nearly enough appreciating the system to understand that one tailored solution may work at one point for one set of local conditions, but IT WILL NOT WORK EVERYWHERE like some sort of checklist for the military.
When academia stops treating military professionals as desperate non-thinkers in search for lists, procedures, and idiot-proof products and begins to consider that creative, critical thinking in a combat environment while freed from the shackles of insitutional dogma may be what we need more of. Less charts and wire diagrams cooked up in a sterile classroom, and more critical approaches to reflecting on western logic, and why it continues to fail in conflict in the modern era.
Pepe
May be Im just a simplex guy but can the authors please explain how in reality on the ground these models are implemented? How does this impressive level of intellectual analysis play out in reality?
Arent we over-complicating an already complex system i.e. the human social ecosystem in a conflict? It reminded of the infamous slide put up to Gen McChrystal in 2010 who "quipped when we understand this slide we will have won the war."
Im not being flippant. Just trying to get to the bottom of whether we need to continue dissecting COIN in the hope of finding the right social network diagram that will unlock the key to winning. The fixation on one dimensional COIN "pop-centric" suggests we are simply going to continue to hammer that square peg into the round hole until it damn will fits.
For those active or recently rtd active personnel, does this type of analysis assist with what you are actioning or had to do in the field? It may well form a useful tool to the overall strategy - that would be a big help - but does it unfold out on the ground.
Thanks
Jason
<em>"We are hopeful that this approach to presenting and manipulating the intersection between the kinetic and socio-cultural domains will provide strategic-level decision makers and planners with a better understanding of how to achieve strategic goals such as the development of legitimacy."</em>
I have problems with that since it states that they are hopeful it "will provide decision makers with a better understanding of how to achieve goals". I think we should use these as tools- and only tools- to either wargame and/or as one of many ways with which we can analyze our continuing activities. To think we can understand something using models or that it will tell us how to achieve goals is- as someone else commented- dangerous. When our quant tools become the drivers of our decision-making I fear we will fail as surely as the great quant fund scandal organizations in our financial past have (Long-Term Capital Management anyone?). These are tools only- they should not help us arrive at decisions but instead assist us in refining decisions already semi-crafted and checking up on them later. If our quant past has taught us anything it is that quant tools have limitations when applied to complex-adaptive entities and understanding/predicting the future.
To Stan's point that, <em>"Our mistake was that we let policy drive doctrine."</em>- I'm not sure that is true (although I could be wrong). As I understood it, the politicians- both the past admin and this one- asked the military for options to reach their objectives (free from threat of AQ) and the military could only offer up nation-building as a COA (not at first, of course, but once we overthrew the governments of both countries- that was the only way we offered them as a choice to conduct COIN, a la 3-24).
The whole "if we break it we have to fix it" false metaphor limited our choices to conducting population-centric COIN- based on what we thought was best for the population, not what they might really want, mind you. This led us to do curious things like ignore the TRUE (I'd argue) will of the people- which was to fight all percieved external entities- starting with the Christian invaders and ending with their cousins from the next village...
And that brings me back to this paper and its conclusion comment: <em>"recognizing legitimacy as the desired end state of a COIN operation."</em>- - the problem with assuming that the key is winning over the population (read: providing them legitimacy) ignores the possibility that the enemy doesn't care about the population and is instead fighting to oust the foreigners, and that that narrative fits very well with the will of the people already (or some other deviation from the preferred narrative of "will of the people").
We assume instead that the will of the people is something more broad and universal like being treated fairly, having a vote, having a legitimate government, etc.- when, really, many of the people (surely not all want the same thing- another fallacy), just want to get back to some illusion of a glorious past when their group held some relative power and there were no outsiders bothering them... But even applying that narrative to all is not correct- and I'm sure the narrative changes over time (if not daily).
After a second reading I have a few of problems with the basic concepts of the model. The first (and my biggest heartache) is the same as Vitesse et Puissance; you appear to be equating risk factors in deciding whether to become and insurgent with those identified in rational person economic theory. People are partially rational about economic choices. Even so I have yet to have an economist fully explain a market crash on a purely rational basis or why economically any purely rational society would outlaw slavery. These are not rational decisions, they are emotional decisions. People get pissed-off when you tell them they made a bad stock choice but they get violent when you are insulting their family, religion, or you are taking away their their freedoms(in Western societies). Likewise, no rational self-interested actor decides to put his own life in danger unless his own death is imminent. The decisions to put your life on the line for a cause like religion is not rational, it is emotional.
Second, I like your idea to use patron-client relations but you should not limit them to insurgents. Particularly in Afghanistan many relationships there between those that control limited resources and those that wish to access them are patron-client relationships as are some tribal or clan relationships.
Third, relatedness as defined in Self-Determination theory helps to explain the dynamics of the patron client relationship but it also identified those daily relationships that have the same characteristics. For example, close friends will garner the same loyalty as a patron-client relationship. There will be a limited pool of potential friends - say 50 or so - but this pool will have a significant impact on the decisions of any actor in the population.
Concur...
Of course, one of the issues will always be that the military is generally a product of the same thinking and worldview as that of its civilian masters. If those at the head of government possess a certain worldview it is highly likely that the military will possess that same worldview and will end up reinforcing pre-conceived notions rather than inhibiting them.
Still, one of the Marine Corps' leadership principles is "know yourself and seek self-improvement." This would indicate that those whose profession is one of arms should strive to know their own capabilities and limitations (which ought to include their own biases and prejudices) and those of the force so as to provide sober and realistic assessments to decision makers on what the military can and can't do, and what the associated costs will be.
Hence, my earlier quote...
Sorry or the duplicate: this is meant as a response to ScottJK.
I understand what you are saying, but I still believe it is incumbent on the military to more fully understand and appreciate the ramification of different strategic choices in COIN and Stability Operations. I equate this (roughly) to nuclear weapons. Once they entered the inventory we conducted research on the consequences of their use so that ultimately we could tell a policy maker "Yes sir, we can preemptively attack the Soviet Union but they will get some shots off and this is what you can expect: contaminated water, contaminated food, large areas uninhabitable for years after the fight." Had we not gone down that road some fool might have given the order to use them and when it was all over they would explain themselves with the overused refrain "We just didn't know this would happen".
Now we just don't understand the politics of counterinsurgency, but we are learning. I am all for doing more research so that we can better advise our civilian masters on the costs of trying to democratize societies that don't have the same value systems as westerners do. Failing to do so and we will find ourselves back here in another 30 years or so using that same overused excuse.
I say this with tongue in cheek- but for empirical evidence- how about the Rand Study that "proved" the principles in 3-24 work---? ;)
I agree with you wholeheartedly on hearing from our politicians. Need someone to point out to them (NSC?) when the military's COAs (ways) don't seem to match up to what the political ends are.
Further to Gian's post, there are a number of unstated assumptions in this positivists' delight. Warning, minor vent to follow.
First, as pointed out by Gian, '..the local population, the key to resolving any insurgency'. Really? Could I have some peer- reviewed empirical evidence supporting this statement please? (Oh, and FM 3-24 and Galula do not constitute empirical evidence...)
Next, the assumption that 'relative deprivation' is at the heart of why men rebel. Ted Robert Gurr argued this (quite well, academically) over three decades ago, and the (discredited) COIN doctrine of the Kennedy era would have us believe it as well. But the theory has taken some severe critcism, ranging from those in the Kennedy Administration (Bundy) through to RAND scholars (Leites and Wolf), Shafer (1988) and more contemporary scholars and writers such as Alex Marshall and Dave Kilcullen. Stathis Kalyvas and Jeremy Weinstein in their respective works offer quite different interpretation as to why men might rebel.
Then we get to the the model. Only three 'types'of insurgent actor? Wow, wish we had known that a while ago, so then we could have ignored the hundred other types of insurgents who keep bugging us...
Ok, so it is obvious that this piece annoyed me. As a soldier I do not mind help from the Social Sciences. But the scholar side of me rebels when it involves lazy assumptions that some of my peers might not pick up on (and hence be possibly mis-directed). My hunch is that we are way past N+1 with the Social Science's useful contribution to contemporary COIN debates (where N= saturation point with Liberal Peace Theory). I would like to see and hear less from Anthropologists, Sociologists etc about these issues. Instead, I would like to see and hear more from the one group in our societies who need to engage more meaningfully and account for their strategic choices - our Politicians.
Regards,
Mark
PS Gian - a minor quibble. I think American 'campaign' strategy should determine if the people are the COG. American strategy
would be better off thinking harder about whether to 'do the campaign' in the first place.
Well, clearly the model has as an essential part of its conceptual underpinnings the pop-COIN thesis. From a modeler's perspective, there is nothing wrong with this. A model does not have to explain everything or simulate everything. I do have the concern that the modellers are travelling on the most faddish and heavily travelled highway in HSCB modeling - that of the "agent-based" approach to modeling human behavior. Irrespective of the modellers' attempts to ingest group influences on individual behavior, and somewhat indirectly, the patron-client relationships predominant in a traditional society, the thing still looks, smells, feels, and acts like that greatest of fictions in Western social science - the "rational actor" model. To be more specific, utilitarian functions imply utilitarian values, and there is an ocean's worth of demonstrable human behavior that does not fit the utilitarian function. So if the model even approximates real life, one should beware the fallacy of face validation. What you see may not in fact be what you are getting.
While I certainly appreciate the scope and scale of the effort, I am unsure that if we need any more "models," "checklists," "frameworks," etc. Gen Mattis (USMC) stated "doctrine is the last refuge of the unimaginative." Coming from a warrior/scholar this was not an indictment of doctrine, nor was it an invitation to chaos - but rather it was a reminder and caution of the siren call of the easy fix. The weak mind, when challenged, either cannot, or will not, seek to solve the problem so much as find refuge in the lies and promises of pre-determined solutions.
The purpose of doctrine is to provide "compelling guidance" to commanders for planning and execution - guidance...just that. Or, as I like to say, provide a common language and common ground from which to deviate. Commanders get paid, and rather well, to solve the problems with which they are presented, not serve as mere action arms for digital publications. Doctrine, in this case COIN doctrine, which dictates operational frameworks and approaches, COG, and even commander's intent - in advance and in a vacuum - is not just wrong or unhelpful, it is dangerous.
While I appreciate the effort of the authors my concern remains that their model, rather than a help, will serve merely as fodder for weak minds who will expect success because a computer told them - in the end - that someone was angry, joined some other angry people, and did something violent.
Well, to a certain extent, policy will always drive doctrine. At its highest levels, doctrine is about the fundamentals and enduring principles that drive how the force approaches and conducts the fight. But even at that lofty level, how a force thinks it can approach and conduct the fight is certainly limited by the constraints and restraints of policy.
That said, the ability of the Joint Chiefs to truly stand up and articulate ways and means with policy makers is always the subject of speculation, usually cynical. I've always been fond of the story that LtGen Hal Moore relates in his book "We Were Soldiers Once...and Young,"
"On that day, convinced that the President's escalation without a declaration of emergency was an act of madness, General Harold K. Johnson, Chief of Staff of the U.S. Army, drove to the White House with the intention of resigning in protest. He had already taken the four silver stars off each shoulder of his summer uniform. As his car approached the White House gates, General Johnson faltered in his resolve; he convinced himself that he could do more by staying and working inside the system than be resigning in protest. The general ordered his driver to turn around and take him back to the Pentagon. This decision haunted Johnny Johnson all the rest of his life." (pg. 16)
Or in the words of James Webb (and I paraphrase) - "how many stars are enough, General?"
Although I think I largely agree with you I also think you chose the wrong Clausewitz maxim. I would have used his observation that political goals in war must be limited to what the military can accomplish. Since current COIN doctrine amounts to armed democratization, which has proven to be nearly impossible (Walker, Scott. "Does Forced Democratization Work?." Taiwan Journal Of Democracy 7.1 (2011): 73. EDS Foundation Index. Web. 28 Feb. 2012.), it is incumbent on the military to explain this to policy makers.
Our mistake was that we let policy drive doctrine. It is not a bad thing to more fully understand the limits of what we can expect the military to accomplish in counterinsurgency operations if we want to be able to explain that to those who chose where and when we will fight.
Yet the piece violates what Clausewitz tells us about a center of gravity:
that it is something to be discovered, and not predetermined.
Yet as this article states its entire model of coin is based on this fundamental principle of population centric coin:
"We devote most of this paper to an elaboration of the local population since COIN doctrine states that it is the center of gravity in a counterinsurgency effort"
Herein rests the problem: American strategy should determine whether or not the population is the center of gravity or if it might be something else, or even nothing at all (hence a negative strategy of no involvement).
Instead once a model like this uses a predetermined principle that the population is the cog, invariably it pushes toward a narrow operational response of pop centric coin. This is why American defense thinking has become dogmatic and doctrinaire.
