Author's Note: This article is a part of thesis presented in partial completion of the requirements of The Certificate-of-Training in United Nations Peace Support Operations. The views expressed in this article are those of the author and do not necessarily reflect official policy or position of Ministry of Defence of BiH or PSOTC.
This article examines some of the major “lessons learned” by ISAF while conducting Counterinsurgency (COIN) and Stability Operations in Afghanistan. Focus is on the following key operational areas: Establishing and maintaining the “legitimacy” of the mission and the operations of ISAF; Comprehensive Approach; Use of Force; Protection of Civilians; Intelligence; Cultural Awareness; Information (Influence) Operations and the use of Female Engagement Teams (FET).
Introduction
ISAF was created in concert with the Bonn Conference in December 2001. The idea was to deploy UN-mandated international force to assist the newly established Afghan Transitional Authority in creating a secure environment and support the reconstruction of Afghanistan. In 2003, NATO launched International Security Assistance Force (ISAF) to support a wide ranging peace process in Afghanistan that was based on five (nation-building) pillars: Military Reform, Police Reform, Government Reform, Economic Reform and Drug Growth Eradication. Over the course of NATO’s lengthy intervention the mission in Afghanistan has proven difficult and operations have been adapted to the changing conditions on the ground. It may be instructive to look back to see what lessons have been learned by ISAF that could possibly be used to inform and instruct both current and future missions that may have to operate in a similar environment.
The issues presented in this article are addressed as “lessons learned”; the term itself implies process of learning even though, after almost 12 years of the ISAF mission, NATO still struggles operationally and a number of what have been identified as “lessons learned” remain “lessons to be learned”!
Background to NATO Operations in Afghanistan: The “International Security Assistance Force” (ISAF)
ISAF is a UN-mandated, NATO-led international military force operating in Afghanistan. Following the successful ousting of the Taliban government of Afghanistan in October-November 2001 by Operation Enduring Freedom, the U.S. led invasion, ISAF received authorization by UN Security Council Resolution 1386 on December 2001. Broadly stated, its initial mission was to assist in creating a secure environment and to provide security assistance for the performance of other tasks in support of the Bonn Agreement. When ISAF was initially deployed, it covered only a small area around the Afghan capital Kabul. But in the time, the mission area expanded over the whole of Afghanistan. Since August 2003, NATO has been responsible for the command, coordination and planning of the force, including the provision of a force commander and headquarters on the ground in Afghanistan.[1]
ISAF is NATO’s first major out of area deployment (IFOR in Bosnia was in NATO’s “backyard”) and the first time the Alliance has invoked Article 5 of the North Atlantic Treaty which states that an attack against one member country is to be considered an attack on all. It has also been viewed by some to be a key test for the relevance of the Alliance in the post-Cold War world. ISAF tests not only NATO’s capabilities but also its relevance in a new geopolitical context.[2] In operating over more than a decade, ISAF grew not only in numbers but also witnessed a number of specific improvements in terms of NATO doctrine development for stability and counterinsurgency operations. “Operations during the first half of the decade were often marked by numerous missteps and challenges as the U.S. government and military applied a strategy and force suited for a different threat and environment. Operations in the second half of the decade often featured successful adaptation to overcome these challenges”.[3]
Mission
Latest ISAF’s mission statement reads: In support of the Government of the Islamic Republic of Afghanistan, ISAF conducts operations in Afghanistan to reduce the capability and will of the insurgency, support the growth in capacity and capability of the Afghan National Security Forces (ANSF), and facilitate improvements in governance and socio-economic development in order to provide a secure environment for sustainable stability that is observable to the population.[4]
On behalf of the international community’s overall effort, ISAF is working to create the conditions whereby the Afghan government is able to exercise its authority throughout the country. To achieve this goal, ISAF conducts security operations to protect the Afghan people, neutralize insurgent’s networks and deny sanctuary in Afghanistan to extremists. ISAF also trains, advises and assists the Afghan National Security Forces, so that they can take over security responsibilities. Currently, NATO’s primary objective in Afghanistan is to enable the Afghan authorities to provide effective security across the country and ensure that the country can never again be a safe haven for terrorists. The transition to Afghan full security responsibility is due to be completed at the end of 2014, when ISAF’s mission should end. As of January 2013, fifty nations are contributing troops to the mission, including 22 non-NATO partner nations from around the globe, and 28 NATO Allies.[5] NATO is now deeply into civil–military stabilization and counterinsurgency tasks, far greater than anyone anticipated when the mission began.
Counterinsurgency
“At its heart, a counterinsurgency is an armed struggle for the support of the population”
FM 3-24.2, Tactics in Counterinsurgency
Former ISAF Commanding General, U.S. Army General David McKiernan, stated in November 2008: “The fact is that we are at war in Afghanistan. It’s not peacekeeping. It’s not stability operations. It’s not humanitarian assistance. It’s war.”[6] What has been described as a war by General McKiernan, due to level of violence, was in fact counterinsurgency (COIN)[7]. However, for several years, both NATO and the United States, its top troop contributing country, struggled to properly define the “fight” they faced in Afghanistan. Immediately after the first forces were deployed to Afghanistan, operations there were defined as counterterrorism. When the threat from Al Qaida and the Taliban was alleviated, some troop contributing countries were of the opinion that operations should be conducted under a peacebuilding framework. The U.S. however, through their unilateral operation ENDURING FREEDOM, conducted alongside but separate from ISAF operations, continued with counterterrorism operations. For a number of years, ISAF troop contributing nations had different approach to conducting operations in Afghanistan.
Only when COIN was adopted as a unified “approach”, did ISAF begin to make significant progress in Afghanistan. However, ISAF’s transformation from counterterrorism (isolating and killing terrorists: Al Qaida and Taliban) to counterinsurgency (protecting the population) has not been easy for a number of reasons.
In the early period of ISAF’s mission, a coherent and accepted Counterinsurgency (COIN) doctrine had not been developed. COIN doctrinal publications were not released before late 2006 when U.S. COIN manual FM 3-24 was published.[8]. This new counterinsurgency doctrine inspired by lessons learned from Iraq began to be used as the basis for operations in the hopes of “stabilizing” Afghanistan. Key to progress in ISAF’s use of COIN as the operational basis in Afghanistan occurred after U.S. General Stanley McChrystal assumed command of ISAF in 2009. Gen. McChrystal's initial assessment of the war in Afghanistan in August 2009 defined ISAF’s operations as a comprehensive counterinsurgency campaign with the requirement to conduct classic counterinsurgency operations in an environment, described as uniquely complex.[9] Gen. McChrystal's assessment stressed “the need to change ISAF’s operational culture in two key ways: to more closely interact with the population, and to significantly improve internal unity of effort.”
The counterinsurgency guidance issued soon after his assessment strongly echoed the counterinsurgency principles employed in Iraq:
- Legitimacy is the main objective
- You must understand the environment
- Unity of effort is essential
- Intelligence drives operations
- Prepare for a long-term commitment
- Political factors are primary
- Security under the rule of law is essential
- Insurgents must be separated from their cause and support.[10]
The classic “clear, hold, and build” model of counterinsurgency AKA “oil spots” was adopted and executed in three phases:
• Clear to create a secured environment;
• Hold to establish government control over the populace and areas;
• Build to gain the populace‘s support.
However, once adopted, the complexities of implementing COIN still generated a number of major challenges for ISAF’s campaign in Afghanistan. This was due to reasons such as: ISAF’s complicated command structure; unrealistic expectations and unclear political guidelines regarding the end state; continuing varied interpretations by military coalition members of the operational concept (was it counterinsurgency, counterterrorism, or peace building); national restrictions over use of forces (caveats) from troop contributing countries; and, NATO’s constant struggle for adequate troop contributions with the appropriate capabilities.
ISAF Tactical and Operational Lessons Learned
“The purpose of a Lessons Learned procedure and processes is to learn efficiently from experience and to provide validated justifications for amending the existing way of doing things, in order to improve performance, both during the course of an operation and for subsequent operations.”
NATO Lessons Learned Policy
Lessons learned come from experience from which organizations can improve their work or operational practices. A lesson should be specific in nature and contain enough detail to be useful. Lessons learned can be both positive and/or negative experiences and should be articulated as “advice and recommendations” for the activity being assessed. It must be emphasized that a lesson is not deemed to have been learned until an organization has changed operational methods or procedures as a result of a specific lesson. Otherwise, these are only lessons that have been identified; they remain to be learned. ISAF, claiming to be learning organization, identified number of enduring lessons for NATO operations that present opportunities to learn and improve future practices. Different sources such as studies, scholarly articles and reports were reviewed and considered for operational and tactical lessons learned in preparation for this article.
Many lessons were learned by ISAF but I will discuss only few that are applicable for future operations. These lessons are not discussed in order of importance, but it is important to note that they are interrelated as success or failure in one area may impact on the other areas.
1. Establishing and maintaining the legitimacy of the mission and the operations of ISAF
“In war amongst the people the strategic objective is to capture the will of the people and their leaders, and thereby win the trial of strength.”
General Rupert Smith
“All governments rule through a combination of consent and coercion. Governments described as “legitimate” rule primarily with the consent of the governed; those described as “illegitimate” tend to rely mainly or entirely on coercion. Citizens of the latter obey the state for fear of the consequences of doing otherwise, rather than because they voluntarily accept its rule. A government that derives its powers from the governed tends to be accepted by its citizens as legitimate.”[11] FM 3-24 is clear that the “primary objective of any COIN operation is to foster development of effective governance by a legitimate government.” There are two aspects of legitimacy in Afghanistan: legitimacy of the Government Islamic Republic of Afghanistan (GIRoA) and legitimacy of the NATO force and its operations in the eyes of the Afghan people as well as of international authorities and the contributing nations.
In terms of international military operations, legitimacy comes from UN Security Council authority and the council’s decisions are seen to be representative of the will of the international community. But, legitimacy also needs to be sustained on the ground through the mission’s conduct and actions, through firmness and fairness in exercising the mandate, use of force, respect for local customs and respect for national sovereignty. ISAF possesses proper authorization from the UNSC but sustaining this legitimacy in the eyes of the Afghan people proved to be difficult. COIN doctrine is rather clear on this issue: the main objective of COIN operations is to develop effective governance through promotion of a legitimate government. Conveying of legitimacy occurs when the government achieves popular acceptance of its authority. Only the population can grant legitimacy so both insurgents and counterinsurgents compete for it. Once legitimacy has been lost by political actor, military action can only address the symptoms of a loss of legitimacy.
ISAF operates in an environment where the host nation government (GIRoA) is weak and not viewed as legitimate by large parts of the population. The problem with this is that ISAF can only address the symptoms of GIRoA’s lack of legitimacy: provide security for the population by eliminating insurgents and support the rule of law to some degree. ISAF will not achieve lasting success unless GIRoA establishes its own legitimate claim to Afghan leadership and effectively clear out the current insurgency and prevent new insurgencies from forming.
Consent of the Afghan population is a key component in achieving legitimacy. Failing to keep the Afghan population safe decreases the legitimacy of the GIRoA. Legitimacy in the Afghan context is influenced by local perceptions where mix of national, provincial, district, village and tribal agendas compete for legitimacy with the national government. This creates a huge barrier for the promotion and acceptance of GIRoA legitimacy. To overcome this, ISAF and GIRoA are trying to demonstrate control over security, provide a basic level of relevant governance and expected essential services in local areas, address the corrosive effects of corruption, and provide swift and fair justice system. However, it was not easy for ISAF to operationally help legitimize GIRoA. Main obstacles along the path came from the political level: corruption and nepotism that dominate Afghan politics, inability of GIRoA to provide rule of law and good governance.
Another major problem dealt with the Afghan justice system which is based on accepted legal codes that originated in Islam and tribal customary law. Making this compatible with international norms and laws concerning human rights is a huge challenge of GIRoA. The Taliban, so called “Shadow Governors” are focused on traditional systems and structures that are the essence of traditional legitimacy in Afghanistan. ISAF was rather late to recognize this within its Comprehensive Approach and to include this in the training programs it developed for the judicial system. Rule of law was late too: while the Afghan National Army (ANA) received substantial training in the first years of ISAF, this was not the case with Afghan National Police (ANP). Lack of training within ANP produced significant problems on the ground for both ISAF and GIRoA especially in the areas of corruption and human rights. These issues were eventually addressed with a major reorganization of ANP and greater investments in police training and equipment. Today, training for both ANA and ANP is ISAF’s top priority.
Other initiatives that ISAF developed to help legitimize GIRoA were: promoting an “Afghan face” by labeling all positive activities as Afghan-led; ensuring ISAF military actions contributed to reinforcing the GIRoA’s legitimacy; adequately planning security transition from ISAF-led to Afghan-led operations (through ANA/ANP capacity building) to demonstrate to the population the capacity of the GIRoA to provide security; and, to deliver basic essential services (through PRT efforts). To increase public perceptions of legitimacy ISAF executed an extensive Information Campaign targeting the Afghan population.
However, the main effort for ISAF is still focused on establishing a safe and secure environment by defeating the insurgency and enabling the GIRoA to takeover security responsibility throughout the country. Without defeating the insurgency, the legitimacy of the GIRoA will remain in doubt.
2. Comprehensive Approach
“NATO experiences in Afghanistan, Kosovo and other operations confirm the complexity of contemporary crises. Complex crises do not lend themselves to simple definition or analysis. Today’s challenges demand a comprehensive approach by the international community, including the coordinated action from an appropriate range of civil and military actors, enabled by the orchestration, coordination and de-confliction of NATO’s military and political instruments with the other instruments of power. This needs to be a broader cooperation and planning in accordance with the principles and decisions of relevant senior NATO bodies.”
NATO AJP-01(D) Allied Joint Doctrine
The “comprehensive approach”, defined above in NATO doctrinal publication AJP-01 is a concept that NATO uses in crisis management situations. This approach is sometimes described as a “whole of government approach” while in the UN context it is known as an “Integrated Approach”. The comprehensive approach is a conceptual framework intended to address the need for actors involved in a stabilization mission to work together, from planning to implementation.
As stated in AJP-01: “implementing the comprehensive approach requires sensitivity, rapport, respect, trust, patience and tact, as well as determination to collaborate in all actors, military and civilian, at all levels.” Interagency coordination between these actors is exceptionally difficult due to incompatible planning, training, and conduct of operations and differences in organizational culture. The comprehensive approach for ISAF is a key to success since historically an insurgency cannot be defeated by military action alone. The aim of the comprehensive approach in ISAF is to link the military operations with other efforts that are of importance to the population in order to win their support. As stated previously, security is the main objective for ISAF operations, however, to be fully effective security needs to be followed by good governance, justice, the rule of law and then be reinforced by reconstruction and development, all of which cannot be delivered by military. Former NATO Senior Civilian Representative Mark Sedwill characterized ISAF as “a civil–military experiment in real time and under conditions of stress that only combat can deliver”. This unique civil–military integration in the difficult security environment of Afghanistan posed serious challenges in the absence of clear doctrinal guidelines on how to conduct joint, combined civil-military efforts, to include governance and developmental programs.
The establishment of Provincial Reconstruction Teams (PRTs) throughout the country was one way to provide both security and reconstruction. The Afghan National Development Strategy provides the general framework for PRT efforts: security, good governance, rule of law and human rights, and economic and social development. The PRTs were developed as joint civil–military units specifically to implement the comprehensive approach. NATO doctrine defines the PRT as “an interim civil-military organization designed to operate in complex environments.” ISAF PRT mission statement taken from ISAF’s Operational Plan is as follows: “Provincial Reconstruction Teams (PRTs) will assist the Islamic Republic of Afghanistan to extend its authority, in order to facilitate the development of a stable and secure environment in the identified area of operations, and enable Security Sector Reform (SSR) and reconstruction efforts.” The PRT is supposed to improve stability in a given area by building the host nation’s capacity, reinforcing the host nation’s legitimacy and effectiveness and bolstering the view that the host nation can provide security to its citizens and deliver essential government services. In short, the PRT concept was to blend security, governance and development in a joint, integrated military-civilian organization, staffed and supported by ISAF member countries, and operating at the provincial level throughout Afghanistan.
A PRT is operated by a single nation or a coalition of two or more nations. The PRT can vary in size and composition, depending on the needs of the local area and community but also depending on the lead nation. In Afghanistan there are three dominant PRT models: U.S., British and German. In the U.S. model, the PRT is led by a military commander. Its focus is on delivering quick impact projects. The British model has a higher percentage of civilians and is led by a civilian. The emphasis is local capacity-building. The German PRT model is rather large, and is run by a joint civilian and military command with a focus on long-term development strategies.[12] Each PRT is answerable to their home country, not to the COMISAF or NATO leadership which has resulted in different approaches throughout the mission.
Today, there are 28 PRTs operating across Afghanistan. Structurally, the PRT has number of elements that are intended to focus on reconstruction and development rather than fighting. These generally include a civil–military relations team, engineers, medical teams, linguists, military observer teams, interpreters, political advisers, development specialists and security personnel. Daily PRT activities range from building roads, schools and health clinics, to digging wells, providing micro-grants for small businesses, training and advising public administrators, and helping farmers grow legal crops.
However, PRTs have faced number of challenges: lack of clear objectives against which to measure success or from which to identify alternate ways and means for achieving success; lack of clear, unified chain of command to achieve unity of effort; lack of right resources both in terms of funding and in terms of qualified personnel.[13] Also, NGOs have voiced the complaint that in some cases PRTs have hindered their ability to access the Afghan populace and that they have had difficulty coordinating with the military. As noted earlier, even though the massive PRT effort is integral to ISAF’s COIN strategy, most of their development partners are beyond the command and control of NATO. Despite this criticism, most observers rate the PRT effort as being successful.
3. Cultural Awareness
“COIN is about gaining the support of the local population. This is not achievable without understanding the local people.”
COMISAF COIN Training Guidance 10 Nov 09
History has recorded many military failures which can be traced to a lack of cultural understanding by operational forces. Cultural awareness is critical for forces operating in a population centric counterinsurgency campaign. In the words of many ISAF veterans, the lack of cultural awareness and understanding was perhaps a single greatest weakness of NATO operations in Afghanistan.
Culture refers to everything that makes certain environments unique. This includes: values, attitudes, meanings, hierarchies, religion, notions of time, roles, spatial relations, knowledge, experience, beliefs and more. Understanding of the cultural aspects of a specific operational environment begins with local history, religion, culture, customs, and laws. A thorough understanding of the operational environment will also require understanding the roles of all actors in the area of operations. All this combines to create a living body of cultural knowledge which must be updated, increased, and improved over time using both direct and indirect knowledge sources. Direct knowledge is acquired by direct interaction with the people. Indirect knowledge is acquired through research and study. Indirect knowledge is then verified through interaction with and monitoring of the local population. ISAF learned rather late that cultural awareness was absolutely critical. Initially, military operations in Afghanistan were conducted with limited understanding of the country and its culture. When ISAF identified the people of Afghanistan as the principle object for attention, ISAF focused on better understanding of the people, local cultures and languages.
Cultural and language training to individuals and units is now delivered during pre-deployment preparations and continues throughout the deployment to insure soldiers grow in their knowledge of local customs and cultural norms. Overall responsibility for cultural awareness training rests with unit leaders. U.S. FM 3-24 states: “Effective leaders ensure that Soldiers and Marines are properly trained and educated. Such training includes cultural preparation for the operational environment. In a COIN environment, it is often counterproductive to use troops that are poorly trained or unfamiliar with operating close to the local populace. COIN forces aim to mobilize the good will of the people against the insurgents. Therefore, the populace must feel protected, not threatened, by COIN forces’ actions and operations.”[14]
Some of the broader “Lessons Learned” by ISAF regarding cultural awareness in planning and conducting military operations are: cultural awareness helps in overall situational awareness and effective decision making; cultural awareness provides a better understanding of how the planned military actions will affect both the population and insurgents; cultural awareness can assist in predicting how the population and individuals will behave; cultural awareness can lead to increased communication and prevent unnecessary tensions; cultural awareness helps in force protection. Furthermore, cultural mistakes or culturally inappropriate actions and behaviour in an operation can easily escalate into “bigger problems” and lay the groundwork for increased risk in future operations.
To operationalize lessons learned regarding cultural awareness ISAF instituted several organizational initiatives. These included fielding of Human Terrain Teams (HTTs); emphasizing importance of Key Leader Engagements (KLE); fielding of Female Engagement Teams (FETs) and developing Company Intelligence Support Teams (CoISTs).
Human Terrain Teams (HTT) of 5-6 members, all trained in the social sciences were attached to each U.S. Brigade Combat Team. The teams were responsible for providing a constantly updated, user-friendly ethnographic and socio-cultural database of the brigade’s area of operations. This information was then used to advise the commander on all aspects of the “human terrain” when planning and conducting operations.
Key Leader Engagement (KLE) is military leader’s meeting with important local officials to cultivate and/or manage the “leaders” in local communities. KLE’s were not meant to engage only the key civilian leaders during crises, but to build relationships over time so they can then support the military’s interests when a crisis arises.
Female Engagement Teams (FET) consist of female ISAF soldiers assigned units on patrol who would deal with Afghan females when necessary during an operation because interaction of ISAF male soldiers with Afghan females is not socially acceptable.
Company Intelligence Support Teams (CoIST) are an effort to expedite the flow of information and intelligence gathering from company size units to higher headquarters. One member of each company size unit receives specialized training on information and intelligence gathering and is responsible for submitting a summary of observations and findings through the operational chain as quickly as possible after an operation.
Another interesting and effective tool for enhancing cultural awareness was a concept called “one family - one soldier.” The idea was to generate cultural expertise at the lowest level in any given area where each soldier would develop knowledge about a specific family and conduct daily interaction with that local Afghan family.
4. Intelligence - The need to understand the environment
“In counterinsurgency, killing the enemy is easy. Finding him is often nearly impossible. Intelligence and operations are complementary. Your operations will be intelligence driven, but intelligence will come mostly from your own operations, not as a product” prepared and served up by higher headquarters. So you must organize for intelligence.”
David J. Kilcullen, Twenty-Eight Articles
Intelligence support in COIN operations is focused on gaining a greater understanding of the operational environment. The Operational Environment is defined as “a composite of the conditions, circumstances, and influences that affect the employment of capabilities and bear on the decisions of the commander.”[15] Simply put, the operational environment is everything, everybody and every event occurring around us. In planning for conventional operations at the tactical level, we focus on the physical environment (obstacles; avenues of approach; key terrain; observation and fields of fire; and, cover and concealment) and then the enemy. When operating in a COIN environment, the focus must shift from “enemy centric” to “population centric” intelligence gathering. The cultural and human environments in the area of operations become key pieces of our operational environment.
In order to include cultural and human aspects of the operational environment, it was necessary for ISAF to use different approach in its intelligence gathering. A key aspect was the strong reliance on human intelligence (HUMINT) gained from the population and then fusing this with other information gathering disciplines to produce intelligence products. As prescribed by the U.S. FM 3-24, the purpose of intelligence in COIN is to facilitate understanding of the operational environment, with focus on the population, host nation, and insurgents – three dimensional approach. When analyzing received information, it is necessary to view it though these three perspectives. The key “lesson learned” here is that there is no substitute for direct interaction with the local population through means such as patrols, meetings (shuras), and KLEs. Thus, it is essential to ensure that everyone is prepared to collect information through proper questioning techniques and observation skills. And, every soldier must be trained and conditioned to be a sensor and information gatherer.
Often “intelligence organizations” in Afghanistan were unable to answer fundamental questions about the environment in which ISAF forces were operating or about the people they were trying to protect and persuade. This was attributed to the fact that ISAF intelligence resources focused mainly on insurgent groups, insurgent attacks, and their use of Improvised Explosive Devices (IEDs). Key information about the environment and the Afghan people was not making its way to decision-makers. The tendency was to overemphasize the collection and analysis of information about the perceived enemy ("red" information) - at the expense of information about the political, economic, and cultural environment ("white" information).”[16]
Understanding the cultural and societal aspects of a population demands a careful study of:
• Organization of key groups in a society
• Relationships and tensions among groups
• Ideologies and narratives that resonate with groups
• Values of groups (tribes, etc.), interests, and motivations
• Means by which groups communicate
• The society's leadership system
Before ISAF leaders and operational units could begin to understand the cultural and societal aspects of the Afghan population, it was necessary first to focus the intelligence collection effort. Commanders and leaders had to specify and prioritize what information to collect, identify and direct who will collect what information, and then organize and analyze the collected information. A concept/tool known by its acronym “ASCOPE” was used to drive this holistic information gathering effort.
A - Area: Where do people live, work, play, meet, worship?
S - Structures: Why are structures in the area important? Bridges, mosques, market places, tea houses, internet cafes, hospitals, etc.
C - Capabilities: Who in the community is capable of providing for the people?
O - Organizations: What are the different groups of people in the area?
P - People: How do the people communicate/interact?
E - Events: When are things occurring?
It must be emphasized that collection of information alone is not intelligence. The various information collection disciplines (human intelligence (HUMINT), signals intelligence (SIGINT), imagery intelligence (IMINT), open-source intelligence (OSINT), data from imagery platforms: satellite and unmanned aerial vehicles (UAV)) must be merged with information about on-going significant activity (SIGACT) in an all-source analysis cell that will then address and answer the commander’s Priority Intelligence Requirements (PIR). The key is to have actionable intelligence that is quickly provided to tactical units to inform them in planning and executing operations.
As pointed out previously, one intelligence gathering and processing technique mastered in ISAF was the organization of company level intelligence teams called Company Intelligence Support Teams (COIST). Most of the company level units in ISAF are organized for conventional combat and do not possess an Intelligence operations capability. Intelligence for company operations is normally provided by the company’s higher headquarters. However, this intelligence often arrives late and is not focused enough and therefore may be of little direct value to the company’s pending operation. One of COIST’s goals was to provide a company level unit with information on the effects of the weather, enemy, terrain, and local population on the company’s operations, to reduce uncertainty and aid the company commander in decision making.[17] COISTs were also tasked with studying and reporting on the local population in their area of operations. A further goal in using COISTs was to integrate intelligence from bottom-to-top and from top-to-bottom. For example, the company’s squad and platoon patrol reports were to be brought to Company COIST who would forward these up the chain-of-command for use in planning and follow on operations. The “hope” was for establishing a more open and responsive two-way information exchange from platoon/company level up to the battalion/brigade level and back down. ISAF recognized that unit-level intelligence sections gathered considerable amounts of information on the operating environment and population centers/groups/leaders that can be used by higher-level analysts to create comprehensive, periodic narratives - pulling together all aspects of what is occurring in each district. These wide ranging narratives that describe such things as changes in the economy, projects, markets, trade, development, atmospherics, mosque activity, governance, security, crime, corruption, concerns/irritants when provided back down would be of help in planning and conducting company level operations.[18]
5. Influence Operations
“The effective employment of IO to influence primary target audiences, including the population, local leaders, host nation security forces, government officials, and insurgents, is a key component of counterinsurgency (COIN) operations.”
U.S.M.C. Information Operations in Afghanistan Lessons Learned Report
Influence Operations (IO) are increasingly being recognized as a significant combat force multiplier. In COIN operations they constitute a powerful “non-kinetic” weapon in the commander’s arsenal; however it is a concept whose military application in terms of doctrine is still in development.[19] Influence operations comprise all “non-kinetic/non-lethal” tools available to affect the opposite sides decision-making. Influence Operations or Information Operations in the form of an Information Campaign are a supporting line of operation in the COIN’s operational design reinforcing other COIN lines of operation.
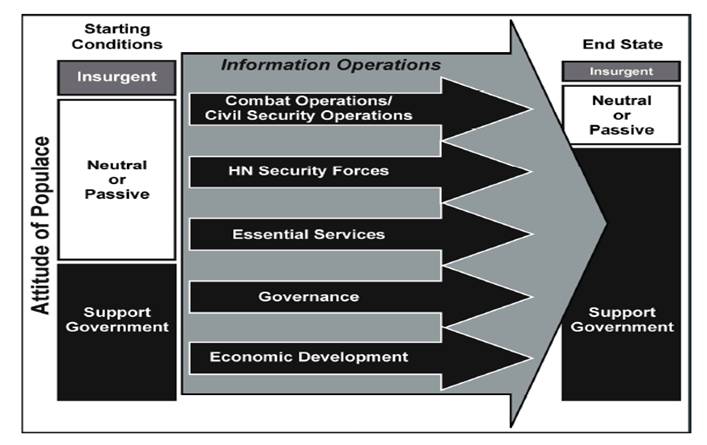
Figure 1: Logical lines of operations for a counterinsurgency[20]
One of the definitions for Influence Operations states: ”it is an overarching term that subsumes or subordinates the capabilities of information operations and other activities to achieve influence objectives.” Another definition states: “the art of integrating lethal and non-lethal capabilities to affect the information environment.”[21] In one doctrinal construct Influence Operations or activities include the following: Information Operations, Civil Military Coordination (CIMIC), Operations Security (OPSEC) and Public Affairs (PA). The aim of all these activities is to “influence” the perceptions of selected target audiences in ways and directions that are favourable to on-going military operations and thereby contribute to overall mission accomplishment. Considering the complexity of COIN operations, some have suggested that successful coordination and execution of Influence Operations may even become a prerequisite for mission success.
Information Operations are the main component of Influence Operations. NATO defines Information operations as: “a military function to provide advice and coordination of military information activities in order to create desired effects on the will, understanding and capability of adversaries, potential adversaries and other parties in support of Alliance mission objectives.”[22] Information Operations include a number of activities and techniques that are employed to influence attitudes and behavior of selected targeted audiences. These activities can include one or more of the following: Psychological Operations (PSYOPS), Electronic Warfare, Presence Posture Profile, Computer Network Operations, Deception, Physical Destruction and Information Security. These tools are used to deliver certain messages intended to influence selected target audiences. Use of these various “tools” of Information Operations must be carefully coordinated and closely monitored to insure that the messages delivered are consistent, culturally acceptable and meet local conditions.
Civil Military Coordination (CIMIC) and Public Affairs (PA) are viewed doctrinally as being closely related to Information Operations and can support an Information Operations campaign. Both CIMIC and PA functions are to be integrated with Influence Operations in an Information Campaign supporting a military force executing a COIN campaign.
The goals of ISAF Influence Operations in Afghanistan have been defined as:
• Gaining the support of the population
• Denying support for the insurgents
• Destroying, degrading, disrupting, denying, deceiving, exploiting and influencing enemy actions
• Enhancing legitimacy of the Host Nation government
• Utilizing the capabilities of positive influencers
• Denying the capabilities of negative influencers[23]
ISAF’s IO “lessons learned” were identified through numerous “after action reviews” and in several studies. Overall, these reviews and the “lessons learned” focused on IO organization, training, planning and messaging. Preparations for IO in the pre-deployment phase should focus on increasing the non-physical knowledge and understanding the operational environment. This knowledge will help to create culturally acceptable IO products and define how the IO messages could be delivered. Some means of message delivery identified for Afghanistan’s operational environment are: Jirgas/Shuras, Local Media, Key Leader Engagements, word of mouth, Leaflets and Pamphlets, Radio in a Box (RIAB), and various Host Nation Government activities.
IO can become a key component in the fight for establishing and maintaining the legitimacy of both NATOs ISAF forces and the Afghan government in the minds of the Afghan population. It was noted that unfortunately for ISAF, the insurgents in Afghanistan also used and were masters of Influence Operations. Insurgents do not use sophisticated printing facilities or over-complicated and creatively designed messages to influence the local population. One example of a simple but very effective use of Information Operations by the insurgents was the use of “night letters” to intimidate (i.e., influence) the local population. A “night letter” is a written message to an individual or group of villagers which are posted during the night on the door of targeted person or local leader. The content of those letters is mostly intimidating by threatening a target to stop activities which are supportive of ISAF or the Afghan government.[24] This method was particularly effective because ISAF patrolled during the day while for the night they moved back to their Forward Operating Bases (FOBs). By not protecting the population “24/7” ISAF exposed the local population to the insurgents at night. Overall, the insurgent’s main advantage in the information operations contest with ISAF was found to be their intimate understanding of local culture.
Due to the complexity of Influence Operations and the number of players involved, coordination is essential in order to achieve coherence and synchronization in an information campaign and the synchronization of that campaign with on-going with maneuver/kinetic activities. A technique developed by ISAF was to establish an Influence/Information Operations Coordination Boards. Membership on this board is directed by the commander and depends on his objectives for the information campaign. However, all influence operations actors must be represented in some way to insure the coordination of all “messages” with actions on the ground. A recurring problem area was the slowness of this coordination process and hence the long time required to receive approval for delivery of an information operations “message”.
Influence operations narratives and messages should be developed early in the planning process and become integral part of any operational plan from the beginning. During a specific military operation the need for information operations support should be anticipated and, when undertaken, the response should be executed with speed, accuracy, and truth. Lying is not an option! When exposed, an information operations message that was a lie will taint all future information operations messages. It was also noted that some commanders on the ground in Afghanistan tended to use influence activities only in crisis situations as some sort of “damage control” mechanism when situation appeared to be out of control.[25]
Successful transmission of an IO message will be heavily dependent on relationships built with the local population by ISAF units operating in an area. Everything a unit does can have either a positive or negative impact and will be used by the local population in how they interpret and view an IO message. It is not only what ISAF says in its IO messages, but also what soldiers do on the ground and on daily patrols. Soldiers’ actions must support and reflect IO messages.
In regards to transmission or delivery of IO messages, a unique and positive example is ISAF’s “Radio in a Box” (RIAB) program. ISAF troops have given tens of thousands of hand crank/solar powered radios to Afghan district governors and Afghan National Security Forces for distribution among the general populous. Program content is varied. The station plays traditional Afghan music, reports the news, and plays messages provided by the Government of Afghanistan and ISAF. These programs have proven to be very successful and have helped counter Taliban propaganda. Commanders on the ground also have cleverly used soldiers on patrol to distribute paper flyers that promoted RIAB and encouraged local population’s interaction in the program.
Bottom line - IO involves every ISAF soldier at every level. IO programs can range from the very simple to the complex. In Afghanistan, contact with the population occurs daily at the small unit level; each soldier’s behavior carries a message to the population (aggression, respect, kindness). Since in Afghanistan, “word of mouth” is the main communications channel, such things as creating simple talking points for small unit leaders to be used on patrols can be a very effective method for distributing key messages. Given that small units have the most interaction with local populations, they should be allocated additional capabilities which can range from trained psychological operations (PSYOP) personnel, combat camera, to Radio in a Box (RIAB) transmitter. IO billets should be established and manned by trained and capable IO personnel. IO training should be conducted for all personnel beginning with the individual soldier who interfaces with the population while on patrol, to commanders and staff at battalion and higher headquarters.[26]
6. Use of Force
“We must assume that civilians are present unless we can establish otherwise.”
COMISAF Tactical Directive, 2011
The measured and precisely calibrated use of force is a critical aspect of contemporary military operations since, in words of former British General Rupert Smith (in his book titled “Utility of Force”), most future military operations will not take place on a conventional battlefield but rather in populated areas and amongst the civilian population. All military application of force must comply with the Law of Armed Conflict (LOAC). Avoiding collateral damage, principally civilian casualties (CIVCAS), has therefore become a paramount criteria in planning and conducting military operations. Population centric COIN advocates the use of force that must be seen as legitimate by the local population. That means the civilian population must view the level of force used as being judicious, appropriate and proportional to the threat which, in turn, will contribute to achieving overall legitimacy of the military. This is a fundamental requirement for success in COIN operations. Studies have shown that ISAF-caused CIVCAS have undermined trust and credibility in ISAF and have harmed relationship with GIRoA. They have also created grievances exploitable by the insurgents.
Several high-profile CIVCAS incidents in 2008 and 2009 served to focus the various commanders of ISAF on ways to reduce civilian casualties. Since 2009, each ISAF commander has issued a “Tactical Directive” to provide his guidance and intent for the "disciplined use of force." Stated in another way, the Tactical Directive gave guidance to subordinate commanders for making tactical choices based on limited use of force while maintaining force protection. Tactical directives also emphasized that the center of gravity of the struggle in Afghanistan is the Afghan people and firmly places dealing with the presence of civilians at the center of every decision involving the use of force.
Operational as well as tactical procedures were modified. Rules of Engagement (ROE) and Escalation of Force procedures were reviewed and modified to reduce CIVCAS. These actions have all served to communicate COMISAF’s intent to minimize CIVCAS and that ISAF was willing to accept the tactical risk of greater casualties in order to avoid a strategic failure by losing support of the population. ISAFs strategic goal remained to defeat the insurgency. To achieve this, ISAF must separate the insurgents from the Afghan population.
The U.S. Army’s Center for Lesson’s Learned (CALL) published a study that identified three types of fires that resulted in CIVCAS: direct-fire engagements, indirect-fire engagements, and escalation of force (EOF) engagements. A direct-fire engagement is when coalition forces are in contact with the enemy and engage with organic weapon systems. CIVCAS resulting of a direct-fire engagement happen for two reasons: the presence of unobserved civilians in the target area and civilians being misidentified as enemy. Indirect-fire engagements are coalition forces’ mortars or artillery fire to engage the enemy. CIVCAS from indirect-fire engagements occur because rounds fail to strike their intended target. EOF engagements occur in order to reduce a threat during a convoy/patrol or to reduce a threat on some sort of control point. The tricky part of EOF engagements is to identify hostile intent and, based on this, when or whether to escalate force. This is the main reason for so called “fog of war” incidents. These occur when ISAF forces misinterpret the actions of the civilian population. The local population often behaves in a manner that is misinterpreted by ISAF troops, who perceive hostile intent. This often results in CIVCAS. These incidents are more common for troops who lack cultural and situational awareness.
In addition to the Tactical Directives, the various commanders of ISAF have issued other directives, all with the aim of minimizing civilian casualties. Some of the more important one’s are:
- COMISAF Night Operations Tactical Directive,
- COMISAF Tactical Driving Directive,
- COMISAF Directive on Medical Facilities,
- COMISAF’s Guidance Concerning Civilian Causalities,
- Direction and Guidance on Escalation of Force.
Each of these directives builds upon the base Tactical Directive and further provides guidance and direction to ISAF troops on engagement with local population.
Despite these many CIVCAS reduction focused directives, ISAF has not been as successful as desired in preventing CIVCAS and additional procedures have been instituted. CIVCAS Mitigation Working Boards and CIVCAS Lessons Learned panels were established to investigate in the immediate aftermath of a CIVCAS incident. The main purpose for these quick response actions was to record, study and learn from the incident and then disseminate the findings quickly so that similar incidents could be prevented in the future.
IO is another tool which is well suited to CIVCAS mitigation and prevention. During pre-and-post operations IO personnel could provide talking points to inform and influence the population before an operation and, if needed, in the aftermath of a CIVCAS incident, to counter any insurgent propaganda and to get the truth out about what actually happened. ISAF found the key is to be first with the truth, followed by condolences, solatium payments, use of a KLE and media engagements to deliver messages of regret and to inform the local population of precautions they can take to avoid incidents when ISAF is conducting military operations in their area. KLE is an important part of the incidence “consequence management process.” Through a KLE, local Afghan leaders would be informed of the actions being taken by ISAF after a CIVCAS incident. ISAF leaders would also ask the Afghan leaders to explain to their villagers what actions on the part of the villagers were perceived as hostile by coalition forces and to inform the villagers how they should act in the presence of ISAF forces to minimize any misunderstandings of their intentions. It was noted that a good prior relationship of the military with local leaders increased the chances of successful situation management after an incident occurred.
Reporting itself is an important part of the mitigation process. ISAF took the position that it must be “first with the truth” in order to initiate appropriate messaging and the KLE process. Further aspect of CIVCAS prevention is proper training for deploying units where a “CIVCAS mind-set” should be developed during pre-deployment training through familiarization with COMISAF’s CIVCAS Directives and other guidelines. [NOTE: from my personal experience, this is rather difficult as units do not perceive this sort of training particularly “exciting” and would rather focus on battle drills and procedures than practicing soft measures focused on engaging the civilian population.]
The ISAF COIN Center in Kabul, a leading institution for COIN training for both ISAF troops and for Afghan National Security Forces, promoted so called “courageous restraint” and “tactical patience” concepts. Courageous restraint means having the courage to restrain from overreacting to contact with the enemy. This is particularly important for decisions made at the lowest level. Certain decisions can produce unwanted 2nd and 3rd order effects which can seriously harm relationships with the local population. The “pay-off” for exercising courageous restraint comes when the local population (when they observe the exercise of courageous restraint) begins to understand, that ISAF is acting in their best interests. This builds public confidence in a unit’s efforts and support for their presence and operations.
Tactical patience means waiting for a situation to develop and unfold before reacting to it. Tactical patience can last from a few seconds to hours. It should be wargamed in unit and leader training programs using the “decision loop” methodology steps of: observe, orient, decide, and then act when the best conditions for success are present that will obtain the most advantageous outcome. Both courageous restraint and tactical patience should be trained at every level.
Another important aspect in minimizing CIVCAS is the need for a thorough understanding of the local patterns of life and the operating environment and to use that in planning of all military operations. An in-depth knowledge of the human terrain can help to alleviate CIVCAS. For example, the earlier described ASCOPE planning tool develops knowledge that enables units to identify risky areas with a high potential for CIVCAS.
Another positive initiative to mitigate CIVCAS was to place a Legal Advisor (LEGAD) in a military unit’s Tactical Operations Centers (TOC) who could provide immediate legal advice on the use of fires during operations, especially if air support and indirect fire support was requested. This made a legal opinion and advice immediately available to commanders on the ground while fire requests pending approval.
7. Protection of Civilians
“Protecting the population from insurgent coercion and intimidation demands a persistent presence and focus that cannot be interrupted without risking serious setback.”
COMISAF Initial Assessment
Protection of civilians (POC) is intimately related to the “use of force.” It is a “hot” topic both within NATO military community as well as within UN and the humanitarian relief and assistance community. However, there are significant differences in how ISAF and the United Nations view and define this issue. The UN takes a very broad view by defining protection of civilians as “efforts to protect civilians from physical violence, secure their rights to access essential services and resources, and contribute to a secure, stable, and just environment for civilians over the long-term.”[27] POC, by UN standards, lies on three tiers: protection through the political process, protection from physical violence and more broadly through the long-term establishment of a comprehensive protective environment. As highlighted in the discussion on the use of force, in terms of POC, ISAF is more narrowly focused on preventing its forces from causing civilian casualties. SOLLIMS, a U.S. Army program that provides a Knowledge Management/Lessons Learned for Peacekeeping and Stability Operations provides a noteworthy lesson here: “ … placing a focus on the international force's operating procedures is insufficient with regard to protecting civilians in cases where the environment has a major insurgent threat. Although civilian casualties (CIVCAS) caused by the international force can indeed be reduced/minimized through various command-directed measures – i.e., training, discipline, and the judicious application of force – stability can still be significantly impeded by the perpetuation of civilian harm by others, particularly by the insurgent threat ... meaning that other options should be considered by the international force ... Civilians may care more about the total number of deaths than who is actually responsible.”[28]
While ISAF has implemented a population-centric counterinsurgency strategy, there remains the criticism that its view and execution of POC is inconsistent with that strategy. The COMISAFs initial assessment in 2009 highlighted this when he reflected that ISAF is pre-occupied with protection of its own forces, which distances itself, both physically and psychologically, from the people that should protect.[29] Most of the units operating in Afghanistan are stationed in large Forward Operating Bases (FOBs) from where they conduct daily patrols and other operations and then return to those bases at night. COIN doctrine calls for “24/7” protection of civilians with the emphasis on security forces leaving among the population. However, lack of security and protection is the major complaint by Afghan population. When Afghans were asked what the main problems were in their area most respondents stated that ISAF was not able to protect them “24/7”, both physically and psychologically from insurgents. Even after particular area is “cleared” of insurgents as a result of ISAF operations, threat from insurgents is still present. Insurgents take advantage of this extending their influence through intimidation and attacks on civilians and the infrastructure they use. This fact turns the local population against ISAF and GIRoA as they are not able to live up to the promises of security. So everything goes back to legitimacy.
Another observation from SOLLIMS regarding the protection of civilians in peacekeeping and stability operations: “The imperative of protecting civilians should be at the forefront of every peacekeeping and stability operation. Although many international missions have not been mandated or sufficiently resourced to meet this imperative, experience has shown that populations can turn against the foreign force (stabilization force) when they perceive that they are not being adequately protected by this force.”[30] UNAMA’s Report on Protection of Civilians in Armed Conflict-2012 reports that “Anti-Government elements have increasingly exerted influence or control. Such perceptions influence the extent to which people feel secure to exercise their rights to free movement, political participation, education and healthcare.”[31] And, people do not feel protected, although they feel that ISAF is adequately resourced to protect them.
One interesting initiative to deal with the difficult problem of POC in Afghanistan is the so called Village Stability Operation (VSO). VSO is a program that provides security, governance and development to village or district communities in Afghanistan through a "bottom up" approach. The concept was developed by U.S. Special Forces supporting local defense and community watch programs with the goal of fostering an enduring stability for the people on a local level. VSO in one village or district includes a small Special Forces team (sometimes reinforced with infantry squads) that lives among the people and uses the COIN methodology of Shape-Clear-Hold-Build. The focus is on protecting the local community, but significant effort is also put to undermining insurgent influence and control, and building support for the GIRoA from within. Within each village, small security elements have been formed as local police (Afghan Local Police) trained and mentored by Special Forces teams. Living among the population in the villages also allowed the soldiers to learn local culture and gain greater understanding of the population’s vulnerabilities. The end result is a protected village where local capacity can be built and where the insurgents remain separated from the population.
8. Use of Female Engagement Teams (FET)
“History has taught us that most insurgent fighters are men. But, in traditional societies, women are extremely influential in forming the social networks that insurgents use for support. Co-opting neutral or friendly women, through targeted social and economic programs, builds networks of enlightened self interest that eventually undermines the insurgents. To do this effectively requires your own female counterinsurgents.”
David J. Kilcullen, Twenty-Eight Articles
As has been amply noted, ISAF found it difficult to fully engage with the local population which is a fundamental COIN precept. A major problem was finding ways to engage women, who make up half the population. The Afghan cultural context of segregating females from males results in the predominantly male coalition security forces being prohibited from interacting with 50% of the population. If coalition forces are to get information from the female half of the population, then military coalition females must be the one‘s getting that information. As stated by Major Maria Vedder, Civil Affairs, US Army ISAF HQ, Afghanistan’s culture is unique in terms of segregation by gender.[32] Segregation has historical and cultural roots. During the Taliban rule of Afghanistan, segregation was particularly severe. Women were almost totally excluded from public life. They were denied access to schools and other sorts of interaction, had to wear the burqa in public and had to be accompanied by male family members when outside of home. After the Taliban were removed from power this situation has improved but mainly in urban areas while in rural areas the role of women remains severely restricted. Female Engagement Teams (FET) were developed to engage the female Afghan population which could not be done by male ISAF soldiers due to cultural sensitivities.
During ISAFs initial operations in Afghanistan, the issue of having to reach out to and deal with Afghan females was not addressed and most likely not even thought of. Consequently there was neither a doctrinal basis nor tactics, techniques and procedures (TTP) for FET-like activities. Over time, through experience and adaptation, a broad doctrinal consensus emerged for FET operations. It is roughly along these lines: FETs are tasked with engaging local female population to find out information on female needs and problems; address their security concerns; and form links between them and the military. FET conducts information engagements with the female population in a culturally respectful manner in order to build confidence and support for GIRoA and ISAF.
The first FET was founded as an ad hoc team by U.S. Marine Corps to support military operations in 2009 based on lessons from Iraq when female service members were used to access, engage, and search Iraqi women. Since then, the U.S. Marine Corps has led the way establishing a FET training program to meet the tenets of the ISAF FET directive.[33]
In the early beginning, FETs were rather ad hoc female teams composed of female soldiers in theatre with the idea to engage the local female population to support specific missions given by ground commanders. After action reports from units employing FETs have found that they provide significant benefits in the areas of intelligence gathering and information dissemination. The FETs have been employed in a variety of operations and activities including intelligence collection, search, seizures and cordon-and-knock operations, key leader engagements, civil affairs programs, enhancing information operations and dissemination for PSYOPS.[34]
There is no fixed FET organization. The team is structured to support a specific operation and to carry out specific tasks in support of that operation. However, some basic organizational tenets have been prescribed. These are: FETs should have as a minimum 2 females per mission with preferably one being a female linguist. When possible, FETs are also to be accompanied by an ISAF female medic, ANSF female partners and/or female GIRoA officials.
During 2010 ISAF initiated in-theatre FET training for female soldiers. Adding to this, in February 2011, COMISAF requested that all units deploying to Afghanistan after 31 August 2011 should deploy with FET trained and qualified female soldiers. Key “takeaway” from FETs is that the ISAF military unit gains greater acceptance from the local population and is able to collect information that can be used in subsequent operations. FET is about building relationships with the Afghan female population which was previously beyond ISAFs ability to influence. FET does engage both men and women. Afghan men often see western women as a “third gender” and will approach coalition forces’ female soldiers with different issues than are discussed with men.[35] FET is not the only ISAF initiative for closer engagement with the Afghan population. The success of the Female Engagement Teams spawned other gender based teams such as Female Search Teams (FSTs) and Female HUMINT Exploitation Teams (FHETs).
Conclusion
Collectively, NATO’s lessons from Afghanistan point to the fact that contemporary conflict is constantly changing its face and multinational forces conducting operations in this sort of environment must constantly learn and adapt. At the tactical level, unit commanders must have a complete understanding of their operational environment and adopt a flexible posture and approach to all operational and tactical problems because issues will overlap either reinforcing or negating each other. A priority for the mission leadership is to establish and maintain the “legitimacy” of the mission. As ISAF lessons learned demonstrated, this is heavily influenced by mission’s approach to Protection of Civilians. The more civilians feel protected, the higher the credibility of the force which, in turn, reinforces legitimacy. The importance of cultural awareness is another major lesson from ISAF. Proper cultural understanding will inform and be a guide to developing the right rules of engagement, develop situational awareness and serve to minimize civilian casualties. Influence operations can be a gigantic force multiplier and have a major impact on all aspects of military operations. A well developed Information Campaign can communicate a wide array of information to the public which will help to gain and keep their support for the operations of the military force. Comprehensive approach is a basic requirement for effective counterinsurgency operation. ISAF’s Provincial Reconstruction Teams allowed for the synchronization of civilian and military efforts at provincial and district levels which contributed to all ISAF’s lines of effort. The use of Female Engagement Teams was innovative techniques in reaching out to Afghan females and dealing with them in a culturally acceptable manner resulting in enhanced cultural and situational awareness. So, it’s all connected!
ISAF’s lessons learned have been purchased at a high cost. More than 3,200 coalition troops have died serving in Afghanistan. Throughout its lengthy operational deployment in Afghanistan, ISAF has been adapting its strategy, operational approach, tactics, techniques and procedures to face evolving challenges. Some of these operational initiatives have been drawn from “dusty” lessons learned from Malaya, the Philippines and other colonial-time insurgencies and counterinsurgencies as well as the American experience in Vietnam and Iraq. Although these lessons are mainly counterinsurgency in nature, they are relevant for other types of operations, to include UN peacekeeping operations.
Bibliography
Bowman, Steve. and Dale, Catherine. “War in Afghanistan: Strategy, Military Operations, and Issues for Congress.” CRS Report for Congress. 03 Dec 2012, http://fpc.state.gov/documents/organization/139352.pdf.
Center for Army Lessons Learned. Afghanistan Civilian Casualty Prevention. CALL Handbook. No. 12-16, 2012.
Center for Army Lessons Learned. Company Intelligence Support Team. CALL Handbook. No. 10-20, 2012.
Center for Army Lessons Learned. Commander’s Guide to Female Engagement Teams. CALL Handbook. No. 11-38, 2011.
Center for Army Lessons Learned. PRT Playbook: Tactics Techniques, and Procedures. CALL Handbook. No. 07–34, 2007.
Chaudhuri, Rudra and Farrell, Theo. “Campaign disconnect: operational progress and strategic obstacles in Afghanistan, 2009–2011.” International Affairs. 87:2, 2011: 271–296.
Collins, Joseph J. “Understanding War in Afghanistan.” Washington, D.C.: National Defense University Press, 2012.
Egnell, Robert. “Lessons from Helmand, Afghanistan: what now for British counterinsurgency?” International Affairs 87:2, 2011: 297–315.
Erwin, Stephanie K. “The Veil of Kevlar: An Analysis of the Female Engagement Teams in Afghanistan.” Master’s Thesis, Naval Postgraduate School, 2012
Flynn, Michael T. Pottinger, Matt. Batchelor Paul D. "Fixing Intel: A Blueprint for Making Intelligence Relevant in Afghanistan", Voices From the Field, Center for a new American Security, 4 January 2010.
Hodžić, Hazim. “Afghanistan – The War for Perceptions?” Katastrofy Naturalne i Cywilizacyjne, Polish Military Academy Vraclov, 2011: 361-376.
Johnson, David E. “What Are You Prepared to Do? NATO and the Strategic Mismatch Between Ends, Ways, and Means in Afghanistan - and in the Future.” Studies in Conflict & Terrorism, v. 34, iss. 5, May 2011, p. 383-401.
Joint and Coalition Operational Analysis. Decade of War Study. 2012
Knight, Andrew J. “Influence as a Measure of Success.” Military Review January-February 2011: 64-72.
Larson, Eric V. “Understanding commanders’ information needs for influence operations.” RAND Corporation, 2009.
Mattelaer, Alexander. “How Afghanistan has Strengthened NATO.” Survival: Global Politics and Strategy, 53:6, 2011: 127-140.
Marine Corps Center for Lessons Learned (MCCLL), Information Operations in Afghanistan. Public Intelligence. 28. Dec 2012, <http://info.publicintelligence.net/MCCLL-AfghanIO.pdf>
McChrystal, Stanley. “COMISAF Initial Assessment (Unclassified) -- Searchable Document.” Washington Post. 01. Dec 2012, < http://www.washingtonpost.com/wp-dyn/content/article/2009/09/21/AR2009092100110.html>.
Morelli, Vincent. and Belkin, Paul. “NATO in Afghanistan: A Test of the Transatlantic Alliance.” CRS Report for Congress. 22 Dec 2012 <http://www.fas.org/sgp/crs/row/RL33627.pdf >
Peacekeeping and Stability Operations Institute (PKSOI). Protection of Civilians Military Reference Guide. United States Army War College. 2013.
Vedder, Maria. “Engaging the Female Populace, Proposal for Military Females to Engage Afghan Females.” Public Intelligence. 28. Dec 2012 < http://publicintelligence.net/isaf-afghan-female-engagment-teams-proposal>.
Watson, Julia L. “Female Engagement Teams: The Case For More Female Civil Affairs Marines.” Marine Corps Gazette. 28. Dec 2012, <http://www.mca-marines.org/gazette/article/female-engagement-teams-case-more-female-civil-affairs-marines>.
Williams, M. J. “Empire Lite Revisited: NATO, the Comprehensive Approach and State-building in Afghanistan.” International Peacekeeping, 18:1, 2011: 64-78.
U.S. Army. Field Manual (FM) 3–24: Counterinsurgency. Ft. Leavenworth, KS: Government Printing Office, 2006.
U.S. House of Representatives - Committee on Armed Services. Agency Stovepipes vs Strategic Agility: Lessons We Need to Learn from Provincial Reconstruction Teams in Iraq and Afghanistan, April 2008
[1] ISAF Homepage, available at: http://www.isaf.nato.int/history.html.
[2] Vincent Morelli, Paul Belkin, NATO in Afghanistan: A Test of the Transatlantic Alliance, available at: http://www.fas.org/sgp/crs/row/RL33627.pdf
[3] Joint and Coalition Operational Analysis, Decade of War Study, at 1 (2012).
[4] ISAF Homepage, available at: http://www.isaf.nato.int/mission.html.
[5] NATO webpage, available at: http://www.nato.int/cps/en/natolive/topics_69349.htm.
[6] Steve Bowman, Catherine Dale, War in Afghanistan: Strategy, Military Operations, and Issues for Congress, available at: http://fpc.state.gov/documents/organization/139352.pdf.
[7] Counterinsurgency has been defined in NATO AJP-3.4.4 as: “the set of political, economic, social, military, law enforcement, civil and psychological activities with the aim to defeat insurgency and address any core grievances.” Same source defines insurgency as: ”the actions of an organised, often ideologically motivated, group or movement that seeks to effect or prevent political change of a governing authority within a region, focused on persuading or coercing the population through the use of violence and subversion.”
[8] U.S. FM 3-24 Counterinsurgency doctrine has intellectual roots to the writings of David Galula.
[9] Stanly McChrystal, COMISAF Initial Assessment (Unclassified) -- Searchable Document, available at: http://www.washingtonpost.com/wp-dyn/content/article/2009/09/21/AR2009092100110.html
[10] U.S. FM 3-24, Counterinsurgency at 1-20 (2006).
[11] U.S. FM 3-24, Counterinsurgency at 1-21 (2006).
[12] M. J. Williams, Empire Lite Revisited: NATO, the Comprehensive Approach and State-building in Afghanistan, International Peacekeeping 18:1, at 64-78 (Feb. 2011).
[13] U.S. House of Representatives - Committee on Armed Services. Agency Stovepipes vs Strategic Agility: Lessons We Need to Learn from Provincial Reconstruction Teams in Iraq and Afghanistan, (2008).
[14] U.S. FM 3-24, Counterinsurgency at 7-1 (2006).
[15] US JP 1-02, DoD Dictionary of Military and Associated Terms at 230 (2010).
[16] Observation from Peacekeeping and Stability Operations Institute based on the article "Fixing Intel: A Blueprint for Making Intelligence Relevant in Afghanistan," by Major General Michael T. Flynn (U.S.A), Captain Matt Pottinger (U.S.M.C.), and Paul D. Batchelor (DIA), Center for a new American Security, (Jan. 2010).
[17] Center for Army Lessons Learned, CALL Handbook Company Intelligence Support Team (2012).
[18] Observation from Peacekeeping and Stability Operations Institute based on the article "Fixing Intel: A Blueprint for Making Intelligence Relevant in Afghanistan," by Major General Michael T. Flynn (U.S.A), Captain Matt Pottinger (U.S.M.C.), and Paul D. Batchelor (DIA), Center for a new American Security, (Jan. 2010).
[19] There is division within the NATO in regards to term Influence operations where some nations prefer term Information operations or Inform and Influence Operations.
[20] U.S. FM, 3-24 Counterinsurgency at 5-3 (2006).
[21] Larson, E. V. Understanding commanders’ information needs for influence operations. RAND Corporation, (2009).
[22] NATO AJP-01(D) Allied Joint Doctrine (2010)
[23] COIN Center Afghanistan briefing, available at: http://ronna-afghan.harmonieweb.org/CTCA/Pages/index.aspx.
[24] Hodžić, H. Afghanistan – The War for Perceptions? Katastrofy Naturalne i Cywilizacyjne, Polish Military Academy Vraclov, 361-376 (2011).
[25] COIN Center Afghanistan briefing, available at: http://ronna-afghan.harmonieweb.org/CTCA/Pages/index.aspx.
[26] Marine Corps Center for Lessons Learned (MCCLL), Information Operations in Afghanistan available at http://info.publicintelligence.net/MCCLL-AfghanIO.pdf.
[27] Peacekeeping and Stability Operations Institute. Protection of Civilians Military Reference Guide at x (2012).
[28] SOLLIMS Lessons Learned Sampler – Protection of Civilians (2010).
[29] Stanley McChrystal, COMISAF Initial Assessment (Unclassified) -- Searchable Document, available at: http://www.washingtonpost.com/wp-dyn/content/article/2009/09/21/AR2009092100110.html.
[30] Strategic Lessons in Peacekeeping & Stability Operations, Strategic Lesson Number 13: The Imperative of Protecting Civilians, (Nov. 2012).
[31] UNAMA&UNOHCHR, Afghanistan, Mid-Year Report 2012, Protection of Civilians in Armed Conflict. (2012).
[32] Vedder, M. Engaging the Female Populace, Proposal for Military Females to Engage Afghan Females. Public Intelligence, available at http://publicintelligence.net/isaf-afghan-female-engagment-teams-proposal.
[33] Erwin, S. K. The Veil of Kevlar: An Analysis of the Female Engagement Teams in Afghanistan, Naval Postgraduate School (2012)
[34] Ibid.
[35] Center for Army Lessons Learned, Commander’s Guide to Female Engagement Teams (2011).
About the Author(s)
Comments
Since NATO has failed to pacify Afghanistan, build the nation or prevent guerrilla training there "Lessons Learned" would be better termed "Hope & Hubris Unfulfilled".
Here are the actual lessons:
1) A COIN campaign waged by the host state and one run by foreign occupiers are completely different animals. The host government can defeat the insurgency by cleaning up it's act and providing fair, efficient and honest government backed by a professional army and police (see Latin America). The foreigners will always be seen as occupiers and the rebels will expect to be able to wait them out. The old imperial powers weren't going anywhere and approached occupations with a long term view. NATO was looking for an exit from day one. It showed and the Taliban saw it as well.
2) If an American cop is expected to have grade 12, pass background checks and attend a four-six month academy just to go on field training why would we think a two-three week course for illiterate Afghans will have a happy ending. If you are building an indigenous security force the training must be longer than usual and if needed preceded by literacy training. This is especially true for army officers. We should have been sending thousands out of country for multi-year long courses. Quality is far more important than quantity. Focus on raw numbers kept the best potential recruits out of ANSF as few sensible educated Afghans would want to associate themselves with riff raff and drug addicts.
3) You can't be an imperial power on year long tours. How did we expect to get anywhere rotating our forces out after six or twelve months and failing to ensure that people who would deal most closely with Afghans has language training before they went.
4) Imperial powers command they don't advise. The documentary "This is what winning looks like" (on You Tube) gives a very good view of how useless advisers (despite being intelligent and hard working) are who can't communicate with the local forces. We should have formed Afghan units under the command of US officers who has attended DLI. Recruits would have been well paid and literate. These units would have served as incubators for army professionalism- much like the Reichswehr. Some would have been CS, CSS etc so we could build an army and not just a series of rifle companies incapable of existing without direct US support. Expansion of the army should have tied to the ability to fill the command structure with professional officers and not simply based on a conveyer belt approach we took.
That's enough. The idea that we could use development to bribe the Afghans into putting up with a corrupt government backed by a criminal police service and incompetent army is laughable. As one USSF Col said "We're not building an Afghan Army that's good, only one that's good enough[to let us leave quickly]". "Good enough" turned out to be bad and led to 12 years of unnecessary casualties and hundreds of billions of wasted dollars.
I don't expect any western military, diplomatic corps or foreign service to be willing or able to adopt an organizational culture as I've described that would allow for successful COIN in a medium to large sized country. The real answer is to not occupy such places. A few skilled advisers fluent in the local language may be useful on the ground but the mass of our help should be to host their people on high quality courses and at universities- if we really believe the host government is honest and working it's way to competent.
I wouldn't say I disagree with anything in your essay here, but I do think you can take many of these points further and to their logical conclusion. Although, working in a military environment myself, I am concious of the difficulties of offering wholesale rather than incremental changes.
First of all I think you need to state more explicitly that COIN is not an 'armed' struggle for the support of the population. It is a political struggle with an armed element. I think this is a fundamental lesson that needs to be learnt - or at least to be much better operationalised as compared with our efforts in Afghanistan.
Secondly you talk about symptoms and causes of illegitimacy and how ISAF can only treat the symptoms. Again though, you do not take this to the logical conclusion that I see and state explicitly that the insurgency itself is a symptom of this illegitimacy, not a cause of it. The causal relationship is almost certainly endogenous and interactive between insurgent strength and government legitimacy as it happens, but I think we should definitely focus on the insurgency as a symptom of illegitimacy in terms of our mindset in order to not give the military aspect of the insurgency too much primacy within the overall COIN approach. It's possibly fair to say we have defeated this insurgency many times over in terms of people taken off the battlefield, yet overall victory seems as far away as ever given its regenerative capacity borne out of the politics of Afghanistan.
Finally, and with these other two points in mind, I think your points on Influence Operations can go further. We need to understand that the whole effort is an influence operation and should be treated as such - if legitimacy is the key then that is a function of politics writ-large not just security. Influence operations should not be run to support kinetic activity or as a combat multiplier. Kinetic activity influences behaviour as well, and information operation teams should be in charge of making sure that all lines of operation send the same message to people and that our words are not undermined by our actions. In essence this means making IO the overseeing and coordination of kinetic and non-kinetic activity, not an aspect of the latter. Dividing operational lines in this manner is symptomatic of our approach in Afghanistan, and, as above, making sure we do not allow this division to occur in future theatres should be the key lesson learned.
