A Game Theory Approach to Battlefield Interrogations
Geoffrey Goff
When the smoke lifts and the dust settles after a successful assault, a special operations force is confronted with a cluttered compound to comb for evidence and a gaggle of disheveled individuals to interrogate. The SOF raid itself may be a nearly perfected art, some may even say a thing of beauty, but site exploitation, at least as practiced, still leaves a lot to be desired. What has made SSE (sensitive site exploitation) such a stubborn riddle to solve is the coincidence of enormous complexity and minute time windows. In a time-span that can just as easily be measured in minutes as hours, the assault force must pore over every tiny scrap of information to determine what, if anything, is worthy of further exploitation and what is better discarded in the dirt. In terms of materials gathered: documents, media, etc. a prevailing strategy quickly emerges: err on the side of over-collection. After all, there is virtually no apparent downside to taking too many documents off target and analyzing them back at base where you have the time and personnel to the really appreciate their significance. Deciding the human dimension, however, can have life and death ramifications. Leaving a terrorist on target could mean a future attack is not prevented. People may die. On the other hand, arresting innocent people could cause the local population to start supporting terrorist activities which would lead to even more senseless deaths.
Ratcheting up the tension even more is the fact that barriers spring up in tactical questioning that simply do not appear in document and media exploitation. Cultural differences, deception, mistrust, and miscommunication all obscure the process of evaluating which individuals have information that would be helpful to US forces and which do not. In other words, interrogations take place against active participants on a densely fogged, obstacle-laden cognitive battlefield. Certainly it is not in the terrorist’s best interest to acknowledge that he may have any useful information and an innocent civilian can only assume he is being viewed as a terrorist after his home has been successfully raided.
So how then does one go about questioning a person in a manner that will get him to reveal that he or someone he knows is indeed a terrorist in the extraordinarily short interval between assault and exfil? How does one negotiate this coincidence of complexity and brevity to effectively accomplish the mission?
For starters, one must maximize the use of available time. One way to do this is to anticipate the enemy’s strategy. How will he respond to questions in attempts to frustrate interrogation efforts? What can you do to preemptively counter these efforts? Where will the enemy let down his guard? How can an interrogator infiltrate that area of weakness and retrieve a piece of information that is self-identifying (as a terrorist or non-terrorist)? The answers to these questions will help us make predictive statements about what strategy the enemy is likely to employ in an interrogation situation and what strategies he will almost certainly avoid. Once a reasonable prediction of the enemy’s defense strategy is made, an appropriate offensive strategy can be developed that promises to yield the desired results in the shortest amount of time. In part this can be accomplished by determining what answer will yield the desired result first and conduct backward reasoning to determine how to get the PUC (person under control) to reveal that answer (or again conspicuously not reveal it).
These methods: anticipating your opponent’s behavior, backward reasoning from a desired outcome, and developing a preemptive counter-strategy are all principles of Game theory[1]. Game theory is the formal study of conflict and cooperation.[2] Developed in the 1920’s and solidified into a field of study in the 1940’s, this mathematical theory has been overwhelmingly applied to economics. However, in the 1950’s and1960’s game theory was broadened to areas of war and politics and subsequently into other social sciences[3]. The theory lends itself neatly to battlefield interrogations/tactical questioning (BIT/TQ) in that the process can easily be understood as a sequential-move “game”, a series of questions and responses, that is not entirely zero-sum, but in which generally the players’ interests conflict.
Spelled out a little further, BIT/TQ is a competition between the interrogator (BIT, Battlefield Interrogator) and the person being interrogated, the PUC, in which each participant is attempting to obtain information from the other while simultaneously protecting his own critical information. In other words, both the interrogator and the subject of the interrogation are practicing operational security (OPSEC) and elicitation simultaneously. The primary objective in BIT is to get the PUC to reveal information that identifies him as A) a terrorist or B) not a terrorist. At the same time, BIT must be careful not to reveal anything that would lead the PUC to a fuller understanding of US operational priorities. The objective of the PUC, on the other hand, may be to protect the information that BIT might use to identify him (avoiding detention) or someone with him as a terrorist while probing for information on US forces. Both participants do not know the other participant’s background knowledge. That is, the PUC does not know what information BIT is using to identify terrorists. BIT, conversely, does not know what if anything the PUC knows about terrorist activities and personalities. The information that is not mutually held is each side’s key advantage. For example, the PUC (in the state of being a terrorist) must lie about any information that he believes will identify him as a member of a terrorist organization, knowing that evidence of any terrorist activities will lead to his incarceration. But what about being an associate of a wanted terrorist? Or being located at a place where terrorist activities were planned? Maybe someone has given a description of him and labeled him as a terrorist, rightly or wrongly. If so what information did they provide? Did they give his family tree? A physical description? The PUC has to guess at what BIT knows (or believes) in order to properly prepare his counter-strategy. BIT can exploit the PUC’s uncertainty by leading the PUC to believe that the interrogator is interested in one piece of data when in fact the key identifier is something else entirely.
If it is assumed the PUC has information about an HVI (high value individual), be it himself or someone else, it must also be assumed that an attempt will be made to leverage the prospect of acquiring this information to entice BIT into exposing US intelligence sources and methods. For example, if the PUC were to let slip some piece of information that was divulged only in a private communication or that only a certain individual would know and BIT keys on this information, then the PUC might assume that the US government is monitoring that communication or individual in some way. Of course, if one keeps following the game of elicitation and OPSEC down the long series of questions and responses, one is are eventually left with a convoluted tangle of intelligence, guesses, and innuendo that becomes increasingly difficult to sort out. It is, therefore, imperative that any BIT approach is simple enough to be conceptualized, while never losing sight of the two-way flow of information either.
The exact context in which BIT is conducted can vary widely, thus, for simplicity’s sake the scenario will be defined as such: There is only one individual to question and fifteen minutes in which to do it. In this example it will stipulate that BIT is experienced enough to be able to detect if the PUC is being generally deceptive. Even so, BIT will not be able to determine the truthfulness of each individual response since no reliable field lie detection apparatus is currently available. As in most BIT/TQ scenarios the only reliable leverage BIT has is the ability to detain the PUC. Other means of gaining compliance will only be effective if the PUC perceive them as credible. For example, it might be reasonable to suggest that others in the compound will be told that the PUC has provided information (when in fact he has not.) At that point the PUC must calculate if 1) BIT is both allowed and willing to lie and 2) If the PUC’s peers would believe such a statement made by US forces. This example may in fact be an empty threat, but will the PUC come to that same conclusion? Detention too, may be interpreted differently by different individuals in different theaters. Variables like these (and others) will all go in to assessing what the PUCs eventual dominant strategy is going to be. A dominant strategy is defined as a strategy that exists in some games which produces the best outcome for the player regardless of what strategy his opponent employs.
Here, for the sake of argument, we will posit that the direct effect of detaining a non-terrorist is that he will become a terrorist. (Note: this is simply to create pay-off tables (see below) and not to suggest anything about the root causes of terrorism). Conversely, the effect of detaining a terrorist will be that he provides actionable intelligence on a second terrorist. Leaving an innocent civilian on target will create a source for future operations and failing to detain a terrorist will mean the execution of a future terrorist attack that would have been prevented is not were detention initiated. To further simplify the equation, the PUC will exist in only two discrete states: terrorist and non-terrorist. In the real world, there may be many different levels of involvement in terrorist activities.
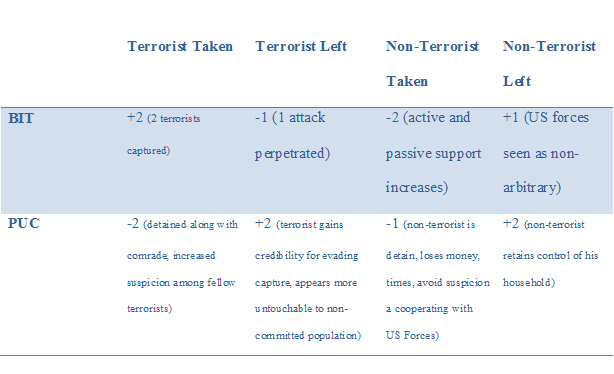
Notice that BIT and the PUC are not completely at odds. In fact, interest line up in a situation in which the PUC is innocent and left on target. This scenario could be considered win-win in the context of the interrogation, especially if the HVI (High Value Individual) is also identified. However, if the HVI is not identified, this would mean the US forces have wasted time and resources to follow faulty intelligence. Conflict and coincidence of interest become more obvious when the interrogation is looked upon as strictly a deception-detection game.
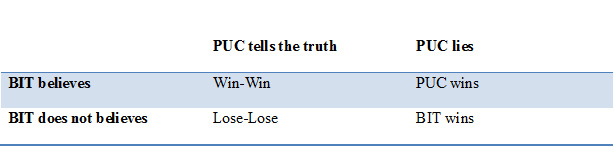
Here we can see that if BIT is convinced that the PUC is being truthful, then we have a win-win situation. However, if the PUC tells the truth but is not believed by BIT, a lose-lose situation occurs in which the PUC is detained by US Forces and may, because of that detention, become an enemy of the United States along with his entire social network. BIT only wins out-right if deception is successfully detected; that is to say, if the PUC is attempting to conceal the identity of the HVI and BIT is able to see through the deception.
This may explain why people that conduct BIT tend to have a deception bias. Maintaining a deception bias may seem like a reasonable strategy, but consider this: several terrorist organizations have instructed their rank-and-file to maintain a very strident deception bias when it comes to dealing with US forces. This has made it not only easy, but legal for US Forces to deceive them into a grossly distorted intelligence picture. All they had to do was tell the truth and the enemy would take it for a deception. In fact, as Dixit and Nalebuff put it in their Game Theory Treatise, The Art of Strategy, “Some of the best lies arise when someone speaks the truth in order not to be believed.”[4]Additionally, excess deception bias tends to lead to lose-lose scenarios, since insurgencies and terrorist movements will leverage this to drive a wedge between US Forces and the local populace in order to shore up their base of support.
Defining the Opponents Objectives and Strategies
Our particular scenario predicts that the PUC will want to be left on target regardless of his state. While there may be unique situations in which the PUC would prefer to be detained to avoid suspicion, gain “street cred”, or even cooperate with US Forces, the vast majority of subjects will simply want to remain in their house, especially in the condition that matters to us, that of being a terrorist.
Thus, assuming this is the PUC’s objective, the natural strategy would be to provide the interrogator with as little as possible. However, the PUC must also be wary of being completely uncooperative as that would put BIT in a position which could lead to further exploitation, i.e. detention. Therefore, we can safely eliminate the PUC adopting a strategy of being completely uncooperative as it becomes a dominated strategy. A dominated strategy is one that produces the worst possible outcome regardless of what one’s opponent does, in this case certain detention for the PUC. An alternate strategy to be expected is that the PUC will attempt to provide as little information as he believes would be acceptable given the questions BIT asks. This is why most BIT/TQ courses instruct students not to ask yes-or-no questions. It allows the PUC to give one word answers that can be claimed to be the product of misunderstanding latter. If on the other hand, the PUC is forced to give a narrative answer, not only must he provide more information, but it is more difficult to claim misunderstanding with one’s own words.
To provide BIT with as little value as possible the PUC will mentally assign information different values, based on how incriminating it is. Information perceived to be innocuous will be given a small value and therefore will likely be provided more freely than information deemed to be of high-value, self-identifying or self-incriminating. Therefore, the PUC may attempt to filibuster with an excess of low-value information in an attempt to avoid revealing any high-value information. This will be part of his dominant strategy, since it allows him to seem cooperative and truthful, without providing any key indicators. If he is able to achieve this, BIT will have no reason or pretext to take the PUC off target.
When it comes to direct questions, the PUC will have no choice but to be deceptive about any identifying/incriminating information. Some PUCs will attempt to be generally deceptive. However, just as being uncooperative is a risky strategy, the PUC can only assume that BIT will detain them if deception is indicated. BIT can completely dismiss this as a dominated strategy when predicting the opponent’s strategy. In the cases in which the PUC will opt for this strategy, BIT will simply detain the PUC for rapport-based interrogations. Therefore, BIT does not need a plan to counter this strategy. The process of eliminating strategies that make no sense for the adversary is called Iterative Elimination of strictly (or weakly) Dominated Strategies (IEDS).[5]
Now through the IEDS process we have eliminated the strategies of being generally deceptive or generally uncooperative. We might also be able to eliminate providing high-value information. Providing a large amount of low-value information may become statistically dangerous for the PUC in such a way that we can assume it will not be PUCs primary strategy.
It is in the PUC’s best interest to lie only about the most incriminating information. When the PUC feels like he can be truthful without arousing suspicion, it is likely he will default to the truth. This is not only a game strategy, but it is also a cognitive strategy to minimize the cognitive load. Lying requires more mental processing than telling the truth. The more lies the PUC will tell the larger the cognitive load and the more likely the PUC will experience leakage, or display some behavioral indicators of deception[6]. And so from the physiological level to the strategic level, being selective about truthfulness is the PUCs dominant strategy, or his preferred course of action regardless of what BIT does.
Defining the Enemy’s Dominant Strategy
Regardless of what BIT does, the PUC’s strategy should always be the same: answer questions in a complete manner without adding extra detail, lie in response to any question believed to be used by BIT to identify the HVI, lie about any derogatory information, and otherwise be truthful, provide as little high-value information as possible, but do not appear reluctant to provide information in general. Therefore, be willing to provide a significant amount of low-value information and if possible, attempt to control the direction of the interrogation with low-value information. This is the PUCs dominant strategy and is therefore the one most likely to be adopted by any particular PUC on target.
A Generalized Solution: Countering the Enemy’s Dominant Strategy
Given the opponent’s dominant strategy, we can devise a counter strategy that in the majority of cases will be effective.
Step One
Determine what information would lead you to believe that you have the HVI in question. For example, if you know that the HVI owns a shop in the bazaar but only goes there on Tuesdays, this become BIT’s high value information. From that BIT can determine what question(s) would lead the PUC to provide this information. These becomes BIT’s high value questions. This type of backward reasoning will allow BIT to develop an approach and a line of questioning capable of educing this information. Note that the questions may not always be direct, e.g. What do you do on Tuesdays?
Step Two
Write a tactical questioning plan that increases the likelihood that the PUC will provide the high-value information. This should include disguising the value of the information that will be provided by the PUC through placement in the line of questioning, i.e. hiding the important question in the middle of the interrogation, negation (asking the opposite of what is being sought), or elimination (asking other possibilities that once eliminated leave only the identifying information)
Step Three
Disarm the PUC as much as possible. Defensiveness, guarding high-value information, is likely integral to the PUCs dominant strategy. In order to neutralize the dominant strategy, BIT must disguise the seriousness of the endeavor. Chances are that disarming alone will not be enough to get the PUC to self-incriminate. However, it may make the difference between the PUC providing ten deceptive statements versus eleven, the one statement being truthful thereby providing the information BIT needs to identify the HVI.
Step Four
Implement misdirection by spending a short amount of time focusing on something which has no bearing on the investigation. A primacy bias will naturally make the PUC believe that the first questions you ask are the most important to you. By misleading the PUC as to what is important, BIT accomplishes two key tasks. First, US targeting TTPs are protected and second the PUC is forced to reevaluate what information is significant. The result is the PUC is forced to move cognitive resources needed for deception to cover that which is meaningless. It is an intellectual feint in the same way militaries have used maneuver feints for millennia. Ruses are part of any game. They can make one’s opponent act against his own strategic interests, and they are especially useful and short-term interrogations.
Step Five
Inject a question that will educe the identifiable information. Again, it is best to be deceptive about what is truly being sought. For example, ask if the PUC was at the compound after second prayer when the real information is whether he was at a shop in the bazaar. This gives an opportunity to provide the identifying information in the form of what BIT has led him to believe is an alibi. At this point if the PUC admits to being at the compound after second prayer it can reasonably be assumed that he is telling the truth and therefore not the person that you are looking for. After all, why would he admit to something incriminating if it were not the truth? In the conventional approach to tactical questioning in which yes-or-no questions are discouraged the question then becomes “Where were you after second prayer?” That approach avoids indicating what location has been surveilled and what method were used, but the PUC will likely perceive this as a high-value answer and simply lie about it. Even if BIT detects that deception, BIT cannot attribute it to the fact that the PUC was at the same location as the HVI, but merely that BIT has made the PUC nervous which is far too often, in all manner of interrogations, conflated with guilt.
Perhaps the most important lesson from Game Theory is that in business, war, or any competitive enterprise, one must anticipate his opponent’s strategy before developing one’s own strategy. If the opponent does not have a dominant strategy, a strategy that produced the optimal outcome regardless of what moves the other player makes, one must determine what the strategy is most attractive to the opponent. This can be done through an iterative process of eliminating first the dominated strategy, the strategy that produces the worst outcome regardless of what the opponent does, and then slightly better and better strategies until only a single strategy is left. When one does this for battlefield interrogation in counter-terrorism environment, one estimates that terrorist will attempt to hide their identities during post-assault activities through selective deception, delay, and filibustering with low value information. With this in mind battlefield interrogators must devise strategies that are able to educe very specific information within a short period of time. Even with a great deal of training and the adoption of this or a similar process, battlefield interrogation is an art form that must be constantly developed and refined. The process laid out in this paper is intended only to be the beginning of a long-term refinement of battlefield interrogation/tactical questioning function.
End Notes
[1] Dixit, Avinash K., and Barry Nalebuff. The Art of Strategy: A Game Theorist's Guide to Success in Business & Life. New York, NY: W.W. Norton &, 2008, Kindle Edition, LOC 241 of 7827.
[2] Turocy, Theodore, and Bernhard Von Stengel. "Game Theory." CDAM Research Report. October 8, 2001. Accessed March 15, 2015. http://www.cdam.lse.ac.uk/Reports/Files/cdam-2001-09.pdf.
[3] Ibid
[4] Dixit, Avinash K., and Barry Nalebuff. The Art of Strategy: A Game Theorist's Guide to Success in Business & Life. New York, NY: W.W. Norton &, 2008, Kindle Edition, LOC 3960 of 7827.
[5] Talwalkar, Presh. The Joy of Game Theory: An Introduction to Strategic Thinking. Kindle ed. 17.
[6] Patterson, Terri. "The Effect of Cognitive Load on Deception." FIU Digital Commons. October 2, 2009. Accessed March 23, 2015.
About the Author(s)
Comments
This webpage is quite good…
This webpage is quite good. Even though gambling is mostly a thing of the past, many people still think that it should be prohibited and regulated. Many individuals today prefer to spend their time doing this, and players automatically seek the greatest offers and services. Canadian casinos that accept quick payments could be useful in this situation. Visit https://casinosanalyzer.ca/online-casinos/fast-payout for more details. Almost every player considers a speedy withdrawal casino in Canada to be one of the most crucial elements when selecting a casino. Everyone who gambles wants to join the winning club. However, because they had to wait so long for a withdrawal, players could occasionally lose patience when they accomplish their aim.
Tämä on erinomainen…
Tämä on erinomainen verkkosivusto. Se inspiroi minua lähtemään pyörittämään pyörää! Jos et ole koskaan pelannut online-kasinolla ja haluat kokeilla käsiäsi joissakin kasinopeleissä, asiat voivat aluksi tuntua hieman ylivoimaisilta. Saat tietoa nettikasino paras palautusprosentti vierailemalla täällä. Paras kasinon voittoprosentti, miten ne ymmärretään ja miten ne vaikuttavat peliisi, on melko yleinen kysymys kaikkien pelaajien keskuudessa. Yksinkertaisesti selitettynä, maksuprosentit viittaavat kasinon voittomahdollisuuksiin suhteessa pelaajan sijoittamaan rahamäärään.
Because the procedure can be…
Because the procedure can be easily understood as a sequential-move "game," a sequence of questions and responses, the theory lends itself well to battlefield interrogations/tactical questioning. If you want to play games from the brand, go to <a href="https://runcasino.com/software/betsoft-slots/">https://runcasino.com/software/betsoft-slots/</a>. If you're seeking free betsoft slots, you won't be disappointed because the supplier offers a variety of free video slots.
A well planned and conducted "circular questioning" technique is far better than a "game theory" approach in detecting lying and can in fact be conducted in under 15 minutes...but it demands an interrogator who fully understands how to use it and who is fully aware of the environment of the operations and the various players.
"Circular questioning" technique came out of the JAROC-B (Joint Allied Refugee Operations Center-Berlin) in the mid 70s, was then incorporated for years into the US Army Intel School Strat Debriefing course and then in the 2005/2006 in the EAIT courses and was a strategic questioning technique.
Problem was and is that it never was fully successful for those trained in say the EAIT course because those trained were young, never fully understood jihadism, Islam and the ME...and never fully understood AQ/IS.....
One of the hardest things of any interrogator regardless of unit is tactical questioning in civil societies where lying is an inherent survival skill set regardless if one is an insurgent or one is a "common person" especially if it is to be done inside 15 minutes...
I watched numerous polygraph testing fail in Abu Ghraib to this problem especially since what we in the west ie US view as lying is common in these countries as it is what they do to survive the countless shifts in the military and political fronts during the fighting on going around them.
The person being TQ'd has a multitude of thoughts that is ongoing as we try to talk to them...protect me, protect my family, protect my fellow fighters, protect my village, protect my tribe etc......and especially the thought that this American truly believes I am the enemy.....so whatever I say he is not going to believe anyway....so I will just give him what he thinks he wants to hear.....
The true "art" and it is a "black art" is to detect the lying and then ascertain what the lie is trying to "protect"....once that is done when one can zero in on the "thing being protected" and do it inside 15 minutes....is it accurate...not really but it keeps you in the "game"....
One of the core problems with being an interrogator in these countries is that our "system" makes the interrogator...judge, jury, defense lawyer and prosecutor all in one person...and whoa if you make a "mistake".....then the national IC comes down on you as to why you made a "mistake"....
I once re-questioned a JSOC detainee in Abu G about some of his reports and with time and a lot of tea later he changed everything and that led to a large number of accurate follow on raids...when JSOC asked why he had possibly had lied to them my answer was...you did not take the time to "understand" and he was under massive pressure to just say something....
The job is one of the hardest there is in this business and it takes years to develop a really good interrogator especially if he or she does not speak say the local language and you are using interpreters....but as usual the system throws numbers at the problem not highly selected, highly trained and totally self confident individuals who are allowed to grow and develop over years not days and months.
In 2006, for example the Army was short 6000 interrogators....they just opened the flood gates and trained/retrained anyone and everyone to hit their numbers and then threw them into the "fight" to TQ or interrogate hardened jihadi's and or just locals in the wrong place/time and that led to Abu G having in mid 2006 thousands of "so called insurgents" interned of which roughly were....99% innocent when they arrived.....but 300% convinced fighters when they left...as by late 2006 Abu G had become the world's finest jihadi training center with three meals, medical coverage and AC.......let's not even get into the jihadi training center inside Bucca.....
