Withering Influence in National Security
Billy Carter
Author’s Note: This essay was inspired and guided by my colleague and co-worker, Mr. Jerry Orban. His guidance and expertise helped me to understand the depth of this issue and brought into focus the consideration to develop a solution that is feasible and attainable.
It is our position that in order to achieve strategic influence goals we require a unified national structure with systems and methods, policy and doctrine appropriate for its charter. Prior to the Church-Pike Hearings such a structure existed in the Operations Coordination Board as part of the NSC. While the US enjoyed strategic influence successes after the structure was initially federated out to DOD, the CIA, and USIA, we posit that it was legacy cadre with institutional acumen that facilitated the design of those programs, such as Solidarity. We raise the concern that such institution and its knowledge does not exist now but can be revitalized. We anticipate that a unified structure would offer operational efficiencies and eliminate redundancies and ultimately allow the US to achieve overmatch in the influence domain. Finally, we have the lessons learned in the formation of the ODNI to model a unified influence system after, expecting and mitigating some of the challenges that such a policy change would mean for the stakeholders as well as internal and external political concerns.
Introduction
This essay examines two situational cases regarding how influence is used at the national level. The first case will focus on unified influence efforts. The United States employed unified influence from the end of World War II up through the Church-Pike Committee Hearings in 1975. After the Church Hearings, strategic influence was federated with Psychological Operations remaining with DoD and Covert Influence remaining with the Central Intelligence Agency. Other aspects of influence, particularly psychological warfare and political warfare left the lexicon as the social and cultural environment latched on to the negative connotations associated with these terms, despite their utility. We remain in a federated system now. Our threat environment remains persistent, unified, and adaptive with emerging platforms and methods of power delivery.
A significant portion of this essay will focus on the threat environment. Russian ambition to achieve the status previously held by the U.S.S.R. and the People’s Republic of China (PRC) emerging from a regional hegemonic state to one of global import are our two primary competitors in global influence. Russia will be examined first due to their highly active hybrid threat campaign, which has been present since the early 20th century. PRC will be examined second. From a long term perspective, China may actually represent the greatest existential threat. While Russia’s program is more defined, they lack a critical component that China has in abundance, an economy.
Following the threat environment will be the actual case reviews. The first case will be a discussion of unified influence structure. The case study will reveal that the US was exceptionally capable of a unified strategic communications and influence activity in the first half of the twentieth century. Foreign malign influence was present and it exploited American cultural diversity at a time when related activities, particularly counter intelligence took on a great deal of scandal and abuses and excesses. There was a cultural shift and the American leadership responded by reshaping intelligence (and by extension) and influence institutions. The influence organization was small but the personalities was committed and so American influence thrived into the 1980s and 90s. The second case will be a review of the influence structure, strategy, and policies present today. The cadre of personal from the unified era have since retired or have passed away and the crop of influence practioneers today are working under a federated system that does not effectively coordinate and synchronize strategic influence. Where interagency (IA) coordination does happen, its usually by DoS or the CIA tasking DoD support towards an operational objective. However, strategic objectives are withering and are doing so at a time when the threat environment is growing more complex and the information environment is flattening.
Based on the threat environment the current influence structure is inadequate to effectively defend against the threat and certainly not designed to go on the offensive. The conclusions will address this gap with policy and structure proposals.
Threat Environment
Since WWII, security, economic and ideological differences with China and Russia, our closest “near-peer” competitors, have remained constant. Chinese development of their footprint in the Spratley Islands, the 9-line zone and Russian exploitation of their fuel relationship with members of the European Union, our NATO partners, are simple examples of the tenuous conflict between the U.S. and them. Since WWII, China and Russia have pursued their objectives which, according to the Chinese Three Warfares and the Russian New Generation Influence Warfare (hybrid warefare) strategy for global control, have always included undermining U.S. national interests and security (Maxwell, 2017).
The Russian Threat
When the USSR dissolved, losing the cold war was a difficult time for Russia. The transition from global leader to a state with a broken economy and will resulted in recognizing that the first step in regaining even domestic power was going to be through controlling the information space. (Kovaleva, 2018). The art of deception in Russia, Maskirovka, is a complete set of actions short of war (armed conflict) to achieve victory. Actions short of war include subversion, sabotage, propaganda, proxy warfare, legal warfare, economic and psychological warfare. It includes fake news, robo-trolling, and certainly military and strategic deception (Allan .et. al, 2018). Maskirovka dates back to 1919, was later practiced by the KGB and as of late is the principle doctrine of the FSB, which President Vladimir Putin served in and later led. The Soviet Union was abundant in resources, which Russia alone does not possess. But, Russia has remained steadfast in their commitment to be a regional hegemon and a global contender. Their doctrine speaks directly to the undermining of western influence. This adversary was best defined by the ‘Long Telegram’ by George Kennan in 1946, “Soviet policy, as Department implies in its query under reference, is conduct on two planes: (one) official plane represented by actions undertaken officially in name of Soviet Government [overt]; and (two) subterranean plane of actions undertaken by agencies for which Soviet Government does not admit responsibility [covert]. Policy promulgated on both planes will be calculated to serve basic policies (A) to (D) outlined in part one. Actions taken on different planes will differ considerably, but will dovetail into each other in purpose, timing, and effect.” (Kennan, 1946). This excerpt demonstrates the Russian model was conceived as a unified effort and one can infer that covert and clandestine activities were in support of overt goals; which provide legitimacy under challenges.
National Security Council Report 4, 1946 also defines the threat posed by the Soviet Union, “The USSR is conducting an intensive propaganda campaign primarily against the US…” This same threat is present in Rogers and Tyushka’s 2017 article presented to NATO, Hacking into the West. The Russian threat to undermine the west, and the US in particular, has been consistent and persistent for 100 hundred years.
Russian Goal and Strategy. The primary goal of President Putin and Russia is to assume the mantle of global power. In ‘The Long Telegram’, the Russian psyche is presented, wrought with insecurity (Kennan, 1946). The strategy of Russian influence is one of divide and cause crisis, to erode stability and resources, to reduce competitor capacity to occupy the influence space that Russia wants. Russian influence will antagonize all available groups to generate or exascerbate rifts, forcing the target state to expend resources to address the rift; and fuel the media coverage to amplify the effects. (Perhaps a lesson learned from Samuel Adams quote, “We cannot make events. Our business is wisely to improve them.” For example, Russian military air and sea craft have violated Finnish territory in an attempt to provoke Finland. Upon complaint by the Finns to Russia, the Russian response is to offer a meeting to arrange some bilateral agreement. Finland refuses to meet and proffers the issue up through the European Union. (Molsa, 2018).
The Chinese Threat
The Chinese threat as a regional hegemon may be traced back to their participation is the War in Korea but it really started to manifest itself with economic primacy in the late 90’s. In 1999 the Chinese government adopted a policy of ‘Unrestricted Warfare’ (Liang & Xiansui, 1999). This policy is clearly present in the Three Warfare Strategy and is exemplified by the Chinese territorial expansion in the South China Sea as well as their conditional cooperation with global entities such as Google. Google, a company that clearly presents a liberal agenda in the United States is complicit in violating those same principals to gain access in China. One may consider this hypocritical of Google, or may assert that as a capitalist enterprise they are merely adapting to the environmental factors while in pursuit of profit. Either way, this paper is not about Google but rather is about China is also adapting itself to exert considerable regional power, attaining global power, and molding western institutions to accommodate their security goals, which run counter to U.S. national security. The Chinese development strategy includes significant ‘economic coercion’ to gain access to raw materials. Chinese incursions against U.S. cyber domains are public record and clearly demonstrate that China is willing to exploit that lack of international norms in emerging warfare domains such as cyber and space. Chinese unrestricted warfare is an adaptation of Clausewitz, in that all states are in a constant state of warfare and it incorporates all available means with a requirement that “information will be omnipresent”. (Liang and Xiangsui, pp12)
In Unrestricted Warfare, in Chapter 7, the authors title the section ‘Ten Thousand Methods Combined as One’ (Liang & Xiansui, 1999). This section of the book speaks to the employment of all available methods to support objectives. This combination of coordinated and cooperative strategy is proving effective and efficient as China continues to expand territorial control in the South China Sea. Vietnam continues to erode its internal policies that were developed to establish resilience against Chinese influence (Vu & Nguyen, 2017). The Three Warfare Strategy places emphasis on economic coercion as a lead activity to achieve Chinese strategic interests.
The Three Warfares, Strategic Psychological Operations, Overt and Covert Media Manipulations, and Exploitation of national and International Legal Systems is explicit in its synchronizing the efforts of influence (Livermore, 2018). The unified effort, nearly all short of armed conflict, pose significant threat because they are working “within” accepted systems. China seems to accept that their previous historical claims to islands in the South China Sea did not meet the International Court’s opinion on ‘continuous occupation’ ( derivative - Ferraro, 2012). China, known for its patience, has established settlements with the intent to achieve ‘continuous occupation’. As the settlements themselves are both military (without conquest) and commercial, they do not meet any standard to reasonable assume the risk associated with forced removal. The Chinese anticipate they will win this particular conflict based on time and influence. The Chinese adaptation of unified political warfare is modeled after the Russian concept of Maskirovka.
Chinese Goal and Strategy. “In peacetime and wartime alike, the application of the three warfares is intended to control the prevailing discourse and influence perceptions in a way that advances China’s interest, while compromising the capability of opponent to responds.” Kanjaa, 2016). China is a patient adversary, though there are some indications that due ot the explosion of a middle class in china, that the public demand for goods, services, and access are accelerating the PRC’s timeline to achieve their goal of resuming the moniker of ‘middle kingdom’ and to erase their centuries of shame (Maxwell, 2017). In addition to having a long vision China has learned the value of legitimacy. China, where possible, uses international systems, exploits vulnerabilities in codified international norms, and thus their actions are ‘consistent’ with those international norms because they did not violate any law. In my opinion, China’s longer vision, deep capacity through economic means, and using international systems to their advantage, makes them the greater existential threat.
CASE 1: Unified Influence
The United States maintained an Isolationist view until WWI. The people were against getting involved however President Wilson employed the Creel Committee to create the Committee on Public Information. After WWI the public gained a leeriness with domestic propaganda. However, with the bombing of Pearl Harbor, public sentiment was galvanized in support of defense.
During WWII the Office of Strategic Services (fig 1) was a national level activity that included the Psychological Strategy Board, the activity responsible for political and psychological warfare, including military psychological operations. Later, with Eisenhower’s Executive Order 10483, the Psychological Strategy Board was subsumed by the Operations Coordinating Board (OCB – figure 2). This unified activity of strategic influence was designed for the purpose of countering the Soviet threat and later grew to include responsibility for IndoChina and other areas around the globe. Activities by the OCB continued to undermine soviet influence domestically and abroad. The FBI assumed a ‘down and in’ approach to both intelligence collection and active measures to disrupt Soviet influence programs while the State Department overtly acted through diplomacy and aid while the CIA were tasked with covert psychological operations (4-a). The critical point was that these activities were mutually supportive and were channeled through the OCD and the NSC.
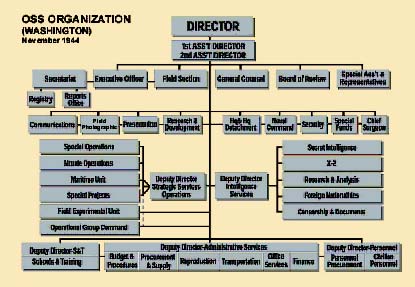
Figure 1: OSS Structure. Downloaded From https://www.cia.gov/library/publications/intelligence-history/oss/OSSChart_t.jpg/image.jpg
After WWII the public again gained some leeriness with public information programs and so provisions such as the Smith-Mundt Act gained traction. Smith-Mundt limited the U.S. Information Agency, a function of public diplomacy, from targeting U.S. populations. The DoD adopted this policy, though was not mandated by it. At this same time period, the Long Telegram and the report by Clark Clifford in 1946. The US had a growing concern for Soviet infiltration and the Smith-Mundt Act had a deliberate objective to eliminate state sponsored propaganda mechanisms.
In the 1970s, following Watergate and the War in Vietnam, there was a cultural paradigm shift in the United States. COINTELPRO, infiltration by the USG into organizations in the US became scandalous and the Church Committee was formed. While the Church Committee was focused on intelligence abuses, the second and third order effects included eliminating all domestic influence platforms, except political campaigns – a private enterprise, not one of government.
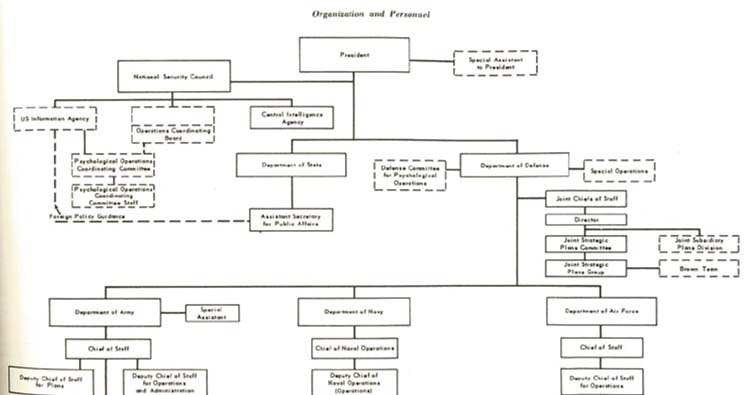
Figure 2: OCB Structure (Daugherty, 1958)
CASE 2: Federated Influence
The Church Committee hearings was focused on excesses by the intelligence community and the report emphasized measures that could be taken to better manage this vital security activity. However, among the second and third order effects was the federating of influence activities between Defense and the CIA. DoD focused on tactical and operational Psychological Operations and later, related Information Operations activities such as Operational Security, Electronic Warfare, Cyber Operations, Military Deception, Public Affairs and Defense Support to Public Diplomacy (JP 3-13).
In the 1990s, with President Bush’s “Peace Dividend” another facet of American Public Diplomacy was eliminated, the United States Information Agency (Cull, 2012). A possible perception was with the downfall of the Soviet Union that the USIA had outlived its utility and removing it could be seen as a positive gesture.
Counter to federated intuitions, President Reagan with National Security Decision Directive 130 declared ‘information’ as an instrument of national power. “… there is a need for sustained commitment over time to improving the quality and effectiveness of US international information efforts…” (NSDD 130). The USG as well as the public is aware that information (influence) is a vital component to security. Sharing information, informing adversaries and friends alike, shapes and influences expectations leaving options other than armed conflict as a preferred alternative.
The 2017 National Security Strategy continues to identify subversive actions by the Russian and Chinese governments. The NSS also specifies the use of ‘information statecraft’ to counter these adversaries. President Trump and the NSC recognize that political and psychological warfare are excised through the manipulation of information and information platforms; that we must defend from these national-to-localized threats and harness that capacity ourselves. Among these ideas is ‘activate local networks’. The ability to engage local-to-national requires a coordinated whole of government approach with clear objectives that each department and agency work towards; including the notion that covert supports the overt rather than the other way around.

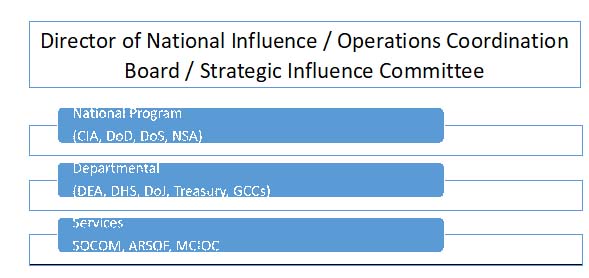
Figure 3: The Influence Structure for the US
From 1992 to 2016 I served in the U.S. Army Psychological Operations. I can attest that while the military routinely supports various lettered agencies and the State Department, the relationship remains ‘one-way’. PSYOPers serving in embassies, though funded through title 10, are regularly bound to support the embassy objectives and its hit or miss whether or not the GCC’s objectives are worked on. The army PSYOPer is regularly invited (late) to strategic planning, yet is then regulated to operational tasks. The US military did not establish the PSYOP Officer Branch until after 2004. Currently the PSYOP regiment includes some of the most diverse and educated enlisted and officer personnel in the military, yet this activity remains neglected and immature. The capacity to generate influence, untapped, allows our adversaries to continue to meddle and leaves us on the defensive.
Military Psychological Operations
Psychological Operations (PSYOP) performed by the military was not immune to the fleecing of capability and employment. As mentioned previously, PSYOP and by extension, military deception (MILDEC) carry negative connotations, are labeled as sneaky, dishonorable, and spreading lies. Of course, Joseph Goebbels comes to mind, how he coaxed a nation of people to support the Nazi party and Hitler by providing a common enemy. After the Vietnam War, US PSYOP consisted of several organizations but in 1975 more than two thirds of the PSYOP force was transitioned to the U.S. Army Reserve, leaving only a handful of battalions to support global PSYOP missions (PSYOP, 2018). Today, active PSYOP units constantly face manpower and resource constraints in the face of increasing demand from each of the global combatant commands as well as increased demand from the DoS.
Conclusion
In order to respond to the threat environment, the U.S. should consider revising a unified influence system with direct liaison with the president of the United States. The model would fashion similarly to that of the Director and National Intelligence.
Much like the Office of the Director of National Intelligence, a revitalized OCB or ‘Director of Influence’ could centralize strategic influence and coordinate, synchronize, and collaborate with the various institutions of influence. From an economy of force perspective, most of these institutions already exist; little would be necessary with regard to creating infrastructure or institutions. The proposal may look something like this:
The lessons learned regarding the centralizing human engagement are present today and in modern history. J.C. Masterman explains clearly that is was essential that the XX Committee operate independent with direct access to the highest levels of decision makers. (Masterman, 1972).
The Finnish model of ‘Comprehensive Security’ is a system that incorporates all departments and ministries in a unified, centrally planned effort to thwart Russian malign influence (Molsa, 2018). Their model includes a down and in approach to foster resilience with both information and a measure of reinforcing Finnish nationalism. The down and in information approach, in the U.S., may not be as successful due to not having a homogenous society like Finland, however that does not mean that it shouldn’t be explored. A unified effort could petition, not mandate, private and commercial sectors to advocate resilient themes. Ensuring transparency would be crucial to achieve any galvanizing effects with public support. Any indication that the U.S. government is manipulating perceptions would be met with devastating consequences. (NDU-Finland, 2017) Successful advocacy of US interests across private, commercial, and government sectors; a unified voice, may expand American brand recognition and generate additional soft power that would then translate into improved position during negotiations with international, bi-lateral, multilateral prospects.
National Influence Risk #1 – Excess. This national activity must safeguard against abuses against the U.S. population. Some laws are already present, such as the Smith-Mundt Act. Defense has strict guidance for the conduct of influence activities under DoD Instruction 3110.05F and CJCS Instruction 3607.02. By precedence, going back to a reflection of what was expected of psychological warfare officer, paraphrasing the Psychological Warfare Casebook, ‘credibility remains the biggest factors in the [effective] conduct of the cold war’. Influence agents recognize that this credibility is not limited to the receptiveness of influence by the target but also must encourage confidence in the fidelity given to U.S. national interests. Excess will undermine credibility, as we have witnessed with recent events in the intelligence community.
National Influence Risk #2 – Politics. Any institution that functions in Washington D.C. develops a cadre that start beholden to the institution but as seen with the DNI, the FBI, and other agencies, personalities may become politically beholden to the party that appointed them. Even the once heralded independent institution of the U.S. Supreme Court finds its nominees instantly labeled either liberal democrat or conservative republican. As with the USSC, independence is critical, particularly when lost and the first risk becomes readily apparent.
National Influence Risk #3 – Inaction. The primary reason to unify strategic influence is to achieve efficiency, synchronize collaborative action across all influence and influence related activities to achieve national security objectives. To not unify these efforts activities like psychological operations by DoD and covert influence by the agency will fail to maximize potential effectiveness.
The secondary reason to unify strategic influence is to achieve institutional unity. Under the current structure there is no whole-of-government approach as the majority of government departments do not have deliberate or supporting influence activities. State, Defense and the Agency, who do have influence mandates, continue to develop unique institutional character that do not run parallel to each other but actually grow further diversity. Currently, title 50 and title 22 activities task title 10 support but the relationship is not reciprocal, even though Defense possesses the greatest amount of resources.
Reporting inefficiency. Unifying planning inherently reduces and streamlines reporting activities and eliminates conflicting perspectives. Influence, being a singular goal with a myriad of methods requires efficiency to optimize effectiveness.
Due to the global information environment, national influence goes well beyond Defense’s Psychological Operations and State’s Public Diplomacy and the Agency’s Covert Influence. Influence is exercised through provisions in trade, sanctions, development, alliances, and through an unprecedented level of commercial activity. The American brands, Coca Cola, McDonalds, Levi’s, Bank of America, Ford, Boeing, Hollywood (the list goes on) represent an extension of American exceptionalism. (Many frown upon this phrase. I embrace it. These activities are exceptional as no other brands from any other state have the global footprint that they do.) This global presence also represents Soft Power. A phenomenon that the U.S. has never attempted to harness, let alone direct.
Summary
This essay is not meant to demean the very important advances made by U.S. influence after 1975. The solidarity movement and the collapse of the Soviet Union may be considered extreme successes for U.S. influence. However, the piece that is missing is the institutional construct that develops under a unified system. The people planning and directing and participating in support to solidarity and orchestrating the collapse of the Soviet Union were developed and mentored by the cadre of personnel that understood unified planning. That body of knowledge, that institutional savvy is gone. Along with it is a loss of understanding psychological warfare and political warfare.
This essay is meant to demonstrate that a unified influence activity achieves the greatest efficiency necessary to challenge the persistent efforts of our traditional adversaries, to seize initiate in the information domain, to exploit opportunities with emerging methods and technologies. Political Warfare by our adversaries are present in common rhetoric: “Russian Election Meddling, Islamiphobic, Chinese Hacking”. This language can be found in any newspaper and blog on a daily basis across the US, across political boundaries. That is a measure of success on their part – that factoring them in affects our decision making and keeps us on the defensive.
Case 1 presents that we started with a unified system that created momentum and effectiveness that continued even after the influence system was federated. However, in Case 2, the federated system, the observation is that the cadre, the momentum, is losing ground. That while the threat remains persistent, while addressing other fixes, a second order effect was breaking something that was otherwise working. With that cadre of influence practitioners having retired or passed away, the institutional momentum is gone. A new cadre with centralized efficiency is necessary to regain that advantage.
Expansion of the information environment, the realm of influence, has presented many missed opportunities, some of which are currently exploited by our adversaries.
Works Cited
Cull, Nicholas J. (2012). The Decline and Fall of the United States Information Agency; American Public Diplomacy, 1989-2001. Palgrave MacMillan. New York, NY.
Iona Allan, Jente Althuis, Alexander Averin, Giulia Conci, Sarah Dooley, Erin Duffy, Douglas Gray, Leonie Haiden, Mitchell Ilbury, Natalia Kantovich, Chelsea McManus, Celeste Michaud, Emma Moore, Kierat Ranautta-Sambhi, and Siri Strand. (2018) “Fake New. A Roadmap. Executive Summary”. NATO StratCom COE / King’s Center for Strategic Communication. Accessed online on 1 October, 2018) at https://stratcomcoe.org/fake-news-roadmap
Daugherty, William E. (1958). A Psychological Warfare Casebook. Johns Hopkins Press, Baltimore, MD.
Fingar, T. Office of the Director of National Intelligence: From Pariah and Pinata to Managing Partner. In R. George & H. Rishikof (Eds), The National Security Enterprise: Navigating the Labyrinth (pp. 185-203). Washington DC: Georgetown University Press.
Fishel, J. T. (2017). American National Security Policy: Authorities, Institutions, and Cases. Lanham: Rowman & Littlefield.
Ferraro, Tristan (March 2012). Expert Meeting: Occupation and Other Forms of Administration of Foreign Territory. Report: International Committee of the Red Cross. Geneva Switzerland. Accessed online on 25 September 2018 at https://www.icrc.org/eng/assets/files/publications/icrc-002-4094.pdf to define occupation
Kanja, Elsa (August 22, 2016). “The PLA’s Latest Strategic Thinking on the Three Warfares.” The Jamestown Foundation. The China Brief, Volume 16, Issue 13. Accessed online on 15 Sept 2018 at https://jamestown.org/program/the-plas-latest-strategic-thinking-on-the-three-warfares/
Khanh Vu and Mai Nguyen (11 June 2018). China Warns Citizens in Vietnam. World News Rueters. Accessed online on 25 September 2018 at https://www.reuters.com/article/us-vietnam-protests/china-warns-citizens-in-vietnam-after-protests-over-economic-zones-idUSKBN1J70NS
Kovaleva, Natalya. (Spring, 2018). Russian Information Space, Russian Scholarship, and Kremlin Control. Defense Strategy Communications, Vol 4. NATOSTRATCOMCOE
"George Kennan's 'Long Telegram'," (February 22, 1946). History and Public Policy Program Digital Archive, National Archives and Records Administration, Department of State Records (Record Group 59), Central Decimal File, 1945-1949, 861.00/2-2246; reprinted in US Department of State, ed., Foreign Relations of the United States, 1946, Volume VI, Eastern Europe; The Soviet Union (Washington, DC: United States Government Printing Office, 1969), 696-709. https://digitalarchive.wilsoncenter.org/document/116178
Livermore, Doug. (25 March, 2018). China’s “Three Warfares” in Theory and Practice in the South China Sea. Georgetown Security Studies Review, Center for Security Studies at Georgetown University. Accessed online on 22 September, 2018 at http://georgetownsecuritystudiesreview.org/2018/03/25/chinas-three-warfares-in-theory-and-practice-in-the-south-china-sea/
Masterman, J.C. (1972). Double-Cross System. Yale University Press, 2012 ed, Lyons Press.
Maxwell, David. (5 June, 2017). Strategy & Special Warfare. A presentation given by retired U.S. Special Forces Colonel David Maxwell to the Military Information Support Operations Program Design and Assessment Course at the United States Army Special Warfare Center and School (USAJFKSWCS) at Ft. Bragg, NC.
Qiao Liang and Wang Xiansui (February, 1999). Unrestricted Warfare. PLA Literature and Arts Publishing House, Beijing.
Rishikof, H. The US Supreme Court: The Cult of the Robe in the National Security Enterprise. In R. George & H. Rishikof (Eds), The National Security Enterprise: Navigating the Labyrinth (pp. 300-319). Washington DC: Georgetown University Press
Rogers, James and Tyushka, Andriy. (2017). Hacking into the West: Russia’s Anti-hegemonic Drive and the Strategic Narrative Offensive. NATO STRATCOM Center of Excellence. Accessed online on May 29, 2018 at https://www.stratcomcoe.org/james-rogers-andriy-tyushka-hacking-west-russias-anti-hegemonic-drive-and-strategic-narrative
Government Sources
Joint Publication 3-13, 20 November 2014, Information Operations, Published by Joint Chiefs of Staff
National Security Council 4. Memorandum from the Executive Secretary to the Members of the National Security Council. Source: National Archives and Records Administration, RG 273, Records of the National Security Council, NSC Minutes, 4th Meeting. Top Secret.
"American Relations With The Soviet Union", September 24, 1946; Report by Clark Clifford, American Relations With The Soviet Union; Subject File; Conway Files; Truman Papers.
NSDD 130 (March 6, 1984).
Molsa, Jouni (1 October, 2018). Comprehensive Security in Finland. Presentation given to the SOF Captains Career Course at USAJFKSWCS
Press Release (July 11, 2017). National Defense University (Finland). “Finland’s Model for comprehensive security viewed effective against hybrid threats”. Accessed online on 1 October 2018 at https://maanpuolustuskorkeakoulu.fi/en/article/-/asset_publisher/finland-s-model-for-comprehensive-security-viewed-effective-against-hybrid-threats
United States Army PSYOP History Handbook. (2018). Published by the United States Army Special Operations Command History Office, Ft. Bragg NC. (2nd Edition)
This essay was inspired and guided by my colleague and co-worker, Mr. Jerry Orban. His guidance and expertise helped me to understand the depth of this issue and brought into focus the consideration to develop a solution that is feasible and attainable.
