Operationalizing OSINT Full-Spectrum Military Operations
Ron Penninger
Introduction
Cyber resources available in abundance online, offline, locked in enterprise systems of record, or even in dusty hard copy libraries offer the Department of Defense (DoD) unique insight for use in all military operations. Enemies of the United States are currently operationalizing these libraries effectively, and with global reach, at little cost. As Steve Banach, former Ranger Battalion commander and 21st century warfare visionary states:
The entity that controls the Virtual Domain and masters Virtual War Campaigning first, will indirectly achieve social control, and will win every war they engage in, at pennies on the dollar. (Source: Small Wars Journal, Virtual War – A Revolution in Human Affairs, Stefan J. Banach, URL: Link, accessed 13 December 2018.)
Adversaries of the United States rightly see the vast storehouses of seemingly innocuous data as key to understanding, undermining policy and goals, and potentially supporting kinetic, diplomatic, and economic victory over the United States. Operationalizing seemingly mundane data gives adversaries a powerful asymmetric weapon the DoD must recognize, plan for, counter, and themselves master.
Let us take a brief look at three examples of adversarial use of OSINT against the US. Recent examples of cyber operations run the gamut of counter-US strategy efforts at all echelons of command. The table below lists three recent events where competitors operationalized data against US interests:
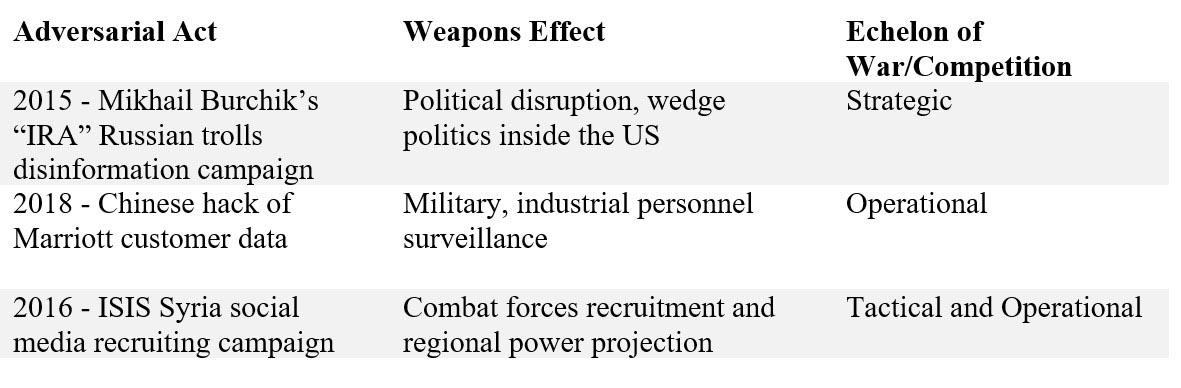
Military leaders should ask how much did these efforts cost? In the case of Burchik’s ongoing disinformation campaign using new bot-posting software, myriad servers and origination points, and skilled content creators, the cost is in the single digit millions of dollars for a couple of years of harassment and disruption. For ISIS’s successful media campaign recruiting fighters and inspiring bloodshed in Europe and the United States, there are zero enterprise costs. The real costs of the distributed influence campaign are negligible, possibly as low as the cost of a smart phone with local mobile cellular service. Let us call this $250.00 per ISIS poster. For mere thousands of dollars, a rag-tag group with decentralized media influence successfully killed dozens in the West and struck fear into millions. The cost of the Chinese hack of Marriott lies somewhere between millions and a few thousands of dollars. This is due to the low cost of hacker labor in China. Yet for around $200,000, China now owns millions of Westerner’s passport numbers, credit card data, and most importantly the pattern of life habits of millions of military, business, and civil servant travelers globally. China can easily operationalize this data to disrupt, surveil, or predict western business and government actions.
What is the counter from the United States for this cheap and deadly aggression, launched from desks and arm chairs in denied territory? The DoD alone will spend billions training Soldiers on information assurance, building digital firewalls, and conducting forensic cyber and legal investigations. Yet he DoD, is likely to be unprepared for the next morphic attack or breach. What weapon or capability can the United States marshal to counter the weapons effects of adversarial cyber operations to dominate this battlefield domain, and achieve victory in the next conflict?
The DoD can achieve a leap forward in operations by weaponizing the open source data it currently possesses with minimal investments now and in the future. Open source data is the digital exhaust most people on Earth emit daily: cell phone telemetry, social media bits, and biographical insights are revealed in normal business and social life via the internet today.
Additional insight into the habits of individuals or polities is revealed in blogs, video logs, resumes, creative writing, and curricula vitae. Smart phones now track users, even high-ranking military leaders, for the mundane purpose of selling them new shirts, ties, food, or gasoline. Phones are now tied to marketing advertisement applications that track exact locations, buying habits, travel routes and times, and time of day of store visits. Phones, applications, and opt-in marketing data reveal both joyful present buying and a family’s medical status, as people buy both gifts and drug prescriptions at big box stores. The army that collates, organizes, and operationalizes this data knows a great deal about their adversary.
The DoD must operationalize open source data to obtain the following states. And these are far from exhaustive:
- Grasp an unredacted, uncurated view of human behavior and natural phenomena in the operational environment, eliminating or reducing biases or filters.
- Why: Institutions and individuals in intelligence or military affairs possess biases. Unfettered access to what the humans in the operational environment are saying removes biases of many types.
- Early sense movements in populations, adversaries, or individuals.
- Why: Let the people on battlefield, victims in the humanitarian campaign, or combatants in low-intensity conflict tell US commanders their intent and their whereabouts, using the mundane data of social media, advertisements, or even elicited responses.
- Cause human behavior on the battlefield, across the continuum of conflict, via smart influence operations to comply with US goals.
- Why: Talk to populations in the manner, method, language, themes, and concepts they understand and desire.
- Conduct open source intelligence preparation of the operational environment ahead of military operations.
- Why: Understand the cultural, political, cyber, economic, and demographic traits of a region BEFORE US forces land to accurately and swiftly win the cyber terrain and influence high ground
The heartening aspect of this concept of operations is that it is not futuristic science. It is here now. The United States leads in data collection and its operationalizing. US product firms and technology companies know how to mobilize data to locate customers, present compelling options, and maintain a “constant touch” with clients. This is the same methodology this paper proposes for Army use in combat and peace.
Selected Military Missions
This paper covers a small selection of the many military missions all branches and echelons execute every day. These missions below are representative of the strategic, operational, and tactical levels of command. Furthermore, we offer the process definition and how emerging open source data can assist in showing commanders from COCOMs to Sergeants First Class unredacted, ground truth on what is happening in their area of responsibility.
Strategic – Understanding Demographics in Denied Areas
Problem: How can senior commanders fully understand population dynamics of friendlies, enemies, and neutrals in denied territory to support United States military operations?
Mission: Quantify large and small population groups into friendly, neutral, enemy. Commander’s intent is to mobilize these populations to service United States objectives in the region. We cannot do this until we understand scientifically the populations, their views, wants, needs, and fears. These operations range the full gamut from intelligence preparation of the battlefield to full scale war and reconstruction. Understand the proclivities, alliances, hatreds, and national and transnational influencers for each group. Develop a plan to mobilize each group to service United States objectives, through the application of soft and hard power.
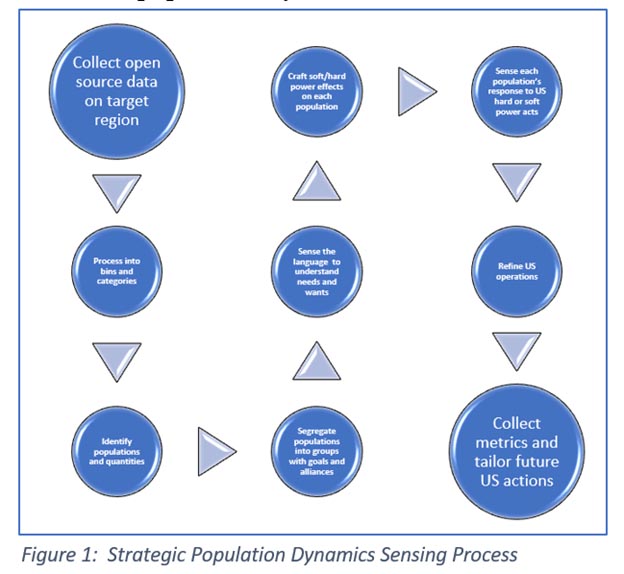
New Process: Figure 1 above offers a simplified revamped process. Using existing data and tools, DoD can deploy powerful open source data aggregator and machine-assisted analyzer. COCOMs now can collect extant data from all populations, including the enemy. This data is unredacted, unfiltered, and unbiased as it comes directly from populations engaged in conflict or in civil discussions with one another. OSINT tools categorize every part of speech in online published work, reads the meaning and intent of an online post, and can rack and stack the evidence documenting much of human behavior. In prior times, COCOMs paid legions of analysts, doctoral candidates, and regional experts to assess and proffer options to leaders. This tool and process does not alter that. Rather it provides both the expert class and leaders, unfiltered access to the speech of populations affected by US policy or military operations. The insights are truly amazing as they are understood by the machine in local languages using lexicons of language, slang, dialect, and jargon. This challenging new process is simplified by using machine learning and natural language processing tools.
Results: COCOMs now can peer deep into polities, sub-groups, and niche elements in a society without disturbing them or canting responses with such unreliable tools such as surveys, individual interviews, or scholarly digests of events. The leader, or his staff, is reading how people actually talk to one another and to the US. COCOMs possess extant, scientific evidence on how population stand on US presences and actions. In Figure 2 below, we show actual forces laydown of ISIS, Pesh Merga, and allied units in the Syrian/Iraq conflict of the last several years. ALQIMI, a DC-based analytical firm, used their tools to sense the social media posts of thousands of fighters engaged in counter-US and pro-US battle.
In Figure 2, we see one of the complexities of the conflict in Syria as collected via open source tools, analyzed by a small team of analysts, and presented in Analyst’s Notebook. This graphic shows the conflict in Syria in social media terms. This is no plaything. The Pesh Merga, ISIS, AL Qaeda, and Syrian militant groups are fighting a war of ideas, at the exact moment they are fighting a war with weapons. This relationship chart represents the confluence of these militant groups tweeting from the battlefield, where their tweets and posts provide actionable intelligence to US forces and State staff.
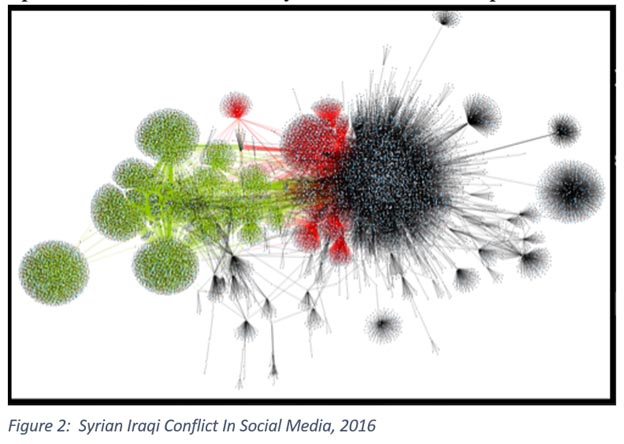
The green nodes represent Pesh Merga Kurds, many of whom taunt ISIS and Al Qaeda fighters live on the battlefield. The black nodes represent ISIS posters, and the red nodes pro-Syrian- government forces such as Al Nusra Front.
This network chart represents several thousand actual individuals on the battlefield in Syria and Iraq. Some of them we identified by a variety of techniques and they can be known and followed as they move around the globe.
Bottom Line: Once COCOMs can categorize populations’ alignments, COCOMs can craft operations scientifically and more accurately to mold populations to US goals. This state is achieved by automating the sensing process and removing biases.
Operational – MISO Preparation of the Operational Environment
Problem: How do military information support operations (MISO) troops create late-breaking, anticipatory outreach products to support US goals in a region?
Mission: Tailor outreach products, especially online and social media speech, to meet populations where they are. MISO troops shall create messaging that uses the concepts, speech, and words of local populations in ways, means, and frequency they prefer. The commander’s intent is to shape a local population’s actions or understanding of US policy in terms they prefer and are most effective.
New Process: In future conflicts, MISO staff will scientifically sense local populations’ preferred means of communications (see Figure 3). MISO staff will then tailor communications products to these populations by the following parameters:
- Topic, themes, concepts that resonate with that population.
- Use the exact language and word choice that locals use, in a digital form of speech and behavior mirroring[i].
- Select the best time of day, week, or month to release MISO products.
- Select the best social media, news, web, or broadcast medium to communicate with a group or a mass market approach to messaging.
- Select the right key influencers, leaders, or mass media personalities to influence in a region with targeted communications.
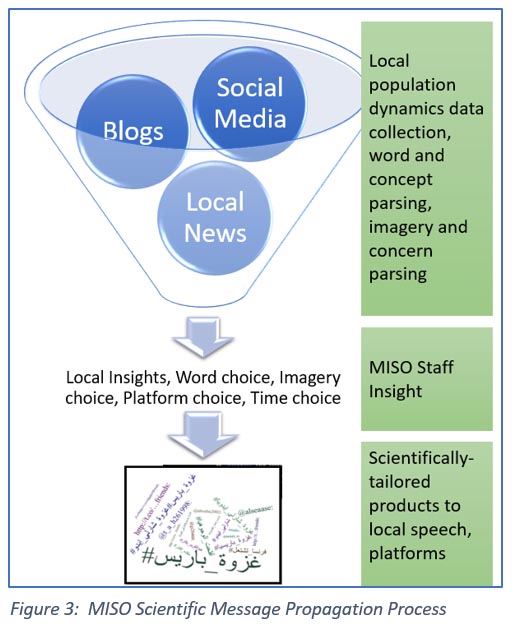
Success is achieved if one understands the ever-changing dynamics of local social media, political alliances, and speech used by large and small populations. Open source tools are currently collecting metrics on social, news, and official speech. These metrics detail specific speech and word choice, time of day of communications, and details on the social media platforms cellular devices and exact posting applications used by different groups and individuals. ALQIMI pioneered a “digital pattern of life” for social media. Figure 4 below shows the frequency and times of social media posting for an individual, taken from ALQIMI’s tool dashboard. These data points mean MISO staff can tailor messages to exactly fit targeted populations or individuals.
Results: MISO staff will use a machine to tell them the many detailed parameters, including exact word choice used by local populations. Figure 3 above shows an extant Arabic word cloud obtained by open source tools in the Arab world. Using this data MISO troops will tailor the words, time of day, social media platform, and reach of influence of their messaging. US leaders can be assured, due to tracking of reach/influence/response/textual fingerprinting, exactly how many people see and react to US messaging. Guessing will be all but eliminated from MISIO staff metrics.

Bottom Line: US messaging campaigns will be targeted, influence known scientifically, and pivots crafted in minutes or hours vice weeks or months as the US does now.
Tactical – OSINT Real-time Intelligence for Ground Missions
Problem: Troops on mounted or dismounted patrol do not know the latest sentiment or mood of local sites, towns, or villages, especially while they are on patrol – the most critical time for survival and mission success.
Mission: Give troops on ground missions the ability to continuously sense and understand popular sentiment and mood towards their patrol during approach to site and during the mission.
New Process: Figure 5 shows a process whereby we set up a social media, blog, web data scrape capability ahead of the mission. This pre-mission automated assessment is our “village baseline.” Much like an HUMINT Soldier performs a behavioral baseline assessment on a captured prisoner of war, we shall now perform this on target villages ahead of a mission. Now the G2 and mission commander know “what is normal” for our target village. As the mission steps off from the US base, convoy, or air insertion, the same system provides updated assessments to the G2 Soldier as the unit is on the mission. These insights could be as simple a RED-AMBER-GREEN lights on village mood or sentiment towards the US actions. They could also be very detailed, to even delivering the translated speech of villagers or their leaders to the G2 Soldier in real time. This gives the mission commander insight into what is actually happening in front of him that he cannot see/hear with US-oriented eyes/ears.
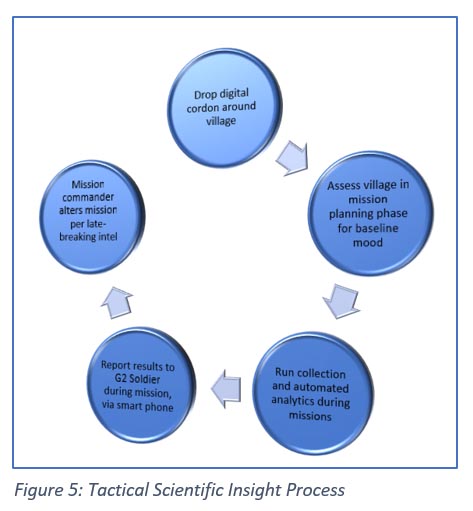
Results: Figure 5 below shows a cartoonish visualization of US Soldiers receiving reports while they are engaged in mission execution. Open source tools can be tailored to report only upon threshold breaching. For example, if the baseline of Abu Samir village is calm with minor agitations on Friday afternoon, but agitating speech online hits 45% threshold just prior to entering the village, the mission commander may elect to call off the mission or avoid the likely agitated neighborhood. Because in many cases social media or smart device users call out their physical location, we can now vector US forces to, or away, from such areas, per the mission requirements and rules of engagement. Right now, open source tools can sense social media and web posting by the following parameters:
- Time of post
- Duration of conversation
- Tone of post (negative, positive, neutral)
- Word choice inside posts
- Reach/influence of poster
- Translation on-the-fly of posts
- Topic, theme, concept, meaning of post
- Retweets, forwarding, reuse of text (textual fingerprinting)
- Geolocation of post to near 10digit grid accuracy
- Inferred geolocation, by reading and sense-making on post text
- Type of device used
- Type of posting application use (these vary by phone, network, and local conditions)
Because we now possess details on individual and group behavioral dynamics, ground mission leaders can make informed decisions. Even if events are unsensed or unknown by mission commanders, such as an untimely death of a village leader, mission commanders can know how a village feels about an event and infer how they may respond to US actions that day. Mission commanders can shape their acts to best attain the result intended by higher command. They will do this based on scientific data, not only gut leadership reaction. No longer should US small units walk into a hornet’s nest because they simply did not know a village or region had tipped into hostility due to an outside influence or event unknown to the unit.
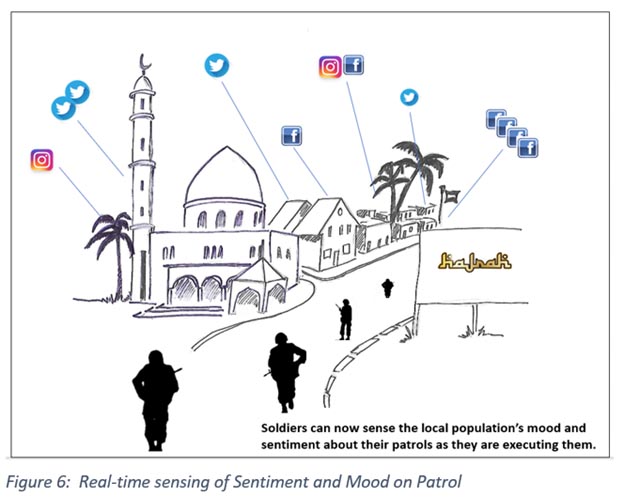
Bottom Line: Mission commanders receive late-breaking intelligence reporting on local sentiment or actions during the mission. This information means the difference between a pitched firefight, a positive civil affairs engagement, and success or failure on the field of battle.
Conclusion
At its most basic, this article intends one core goal: to drive critical information, unbiased, to the troops and leaders who need it most. Richards Heuer, the noted CIA analyst and thinker, published the seminal work on bias in security studies. His work entitled “Psychology of Intelligence Analysis,” details nineteen cognitive biases intelligence, and we posit, operational thinkers, may have. These biases led the CIA, and many others, to misread the ballistic missile imbalance of the 1950s, the fall of the Iron Curtain of the 1990s, and the rise of ISIS in the 2000s. But Heuer’s salient thesis, which he proves exhaustively, is that reliance on any one analytical lens, any one intelligence discipline, or any one set of data will lead to strategic surprise, to operational failure, or to tactical blunders. For the analyst ensconced in labs or offices inside the Beltway, these are esoteric and academic debates. For the Soldier, Sailor, Airman, Marine, or Guardsman, they pay for blunders personally.
Heuer says:
People construct their own version of "reality" on the basis of information provided by the senses, but this sensory input is mediated by complex mental processes that determine which information is attended to, how it is organized, and the meaning attributed to it. What people perceive, how readily they perceive it, and how they process this information after receiving it are all strongly influenced by past experience, education, cultural values, role requirements, and organizational norms, as well as by the specifics of the information received. (Source: CIA Center for the Study of Intelligence, Psychology of Intelligence Analysis, Richards J. Heuer, Jr., URL: Link, accessed 20 December 2018.)
If people construct their reality based on the information received, then should not the information received be as close to the target as possible? This new capability in sensing human and natural phenomena turns every human on, close to, or interested in the battlefield into a sensor for the US to collect and exploit. Remarkably, in the ISIS example in Figure 2 above, the US can turn the enemy into a sensor for extant, unredacted, unbiased views of the battlefield from his eyes. We were able to see ISIS bomb damage assessment of US strikes, from the ISIS point of view. Several ISIS posters took geolocated photos using their smart phones and posted them. At no point in military history has this been possible outside of interrogation or source debriefing. In the past, we waited until Privates and Generals published memoirs to understand how they viewed a campaign or an act on the battlefield. We now sense it as he posts it.
United States Soldiers, Privates and Generals, deserve access to unbiased, unredacted phenomenological reporting from the battlefield. In no way does this diminish the value, skills, and cognitive ability of the G2 or of national agencies. Rather, this capability is a much needed and as of yet, unmined treasure of data on the enemy, neutrals, and friendlies. DoD should place this tool in the hands of every leader from COCOM to fire team NCO.
End Note
[i] Mirroring is the subconscious mimicking of another person’s behavior, speech, body position, breathing patterns, or speech cadence. When used purposefully and expertly, mirroring can create positive bonds of rapport, ease, and comfort in another person.
