Since the dawn of time, when one caveman first struck another, humans have relied on a natural understanding of their physical environment to conduct warfare. We have an inborn ability to understand the laws of the physical world. In order to shoot an artillery round farther, just add more powder; to provide cover for protection against bullets, hide behind a rock. A private might accidentally shoot the wrong target, but the potential damage is limited by the maximum range of his or her rifle. The laws of physics, however, are counterintuitive in cyberspace. In cyberspace, our understanding of the “laws of physics” is turned on its head. Weapons can be reproduced instantly, “bullets” travel at near the speed of light, destroyed targets can be brought back from the dead, and a seventeen year old can command an army. As human beings we are at a distinct disadvantage when thinking intuitively about cyber warfare. In this article we study where our intuition fails us in cyber warfare and suggest alternate ways to think about the conduct of cyber war that account for the vast differences between the kinetic and the non-kinetic fight. A correct understanding and appreciation of these differences and common misconceptions is absolutely necessary to conduct cyber warfare and to integrate cyber effects into the kinetic battlefield. To ground this work we need to define the term “cyber.” There is significant and evolving debate regarding the precise definition of cyber. For purposes of this article we define cyber as a spectrum of cyberspace operations including Computer Network Attack (CNA), Computer Network Exploitation (CNE), and Computer Network Defense (CND).
The Attacker has the Advantage over the Defender
In classic military doctrine, the defender has a distinct advantage over the attacker. In today’s model of cyber security, defenders build layers of defenses to protect the confidentiality, integrity, and availability of critical assets. Security professionals pour millions of dollars into such defenses, but with only limited success. A Maginot Line strategy rarely works in cyberspace because attackers need only find a single flaw to launch a successful attack. Perfect defense is impossible; the astronomic complexity of the software and hardware woven into our information systems and networks is beyond human comprehension. As an example, the Windows XP operating system alone has more than 45 million lines of computer code, creating an immense attack surface. Many aspects of computer security cannot be solved by computers, such as determining the exact operation of a piece of untrusted software. Attackers however, can probe these complex systems to find a flaw and are frequently successful. Hardware and software monocultures, such as widespread use of a single operating system or web browser, amplify the impact of these discoveries by facilitating widespread compromise. Against a determined adversary, many security experts believe we cannot keep our computers secure, compromise is simply a function of time and dedicated resources. Common defenses, such as antivirus systems are reaching the end of their usefulness and cannot be relied upon for effective defense. Even air-gapped networks, not directly connected to the Internet, have proven vulnerable to mobile malicious code. Recent research indicates that defenders must field 1,000 times the resources (money, people, time, compute power, etc.) to reach parity with attackers in cyberspace; this is not a winning proposition for the defender.

Figure 1: In cyber warfare, adversary tactics evolve on a daily basis, unlike the notional Krasnovian Army formerly used in training exercises. (Image Source: Krasnovia.com)
We aren’t Fighting the Krasnovian Army
During the Cold War, military planners could rely upon relatively fixed threat doctrine, see Figure 1. We knew the capabilities of threat units and could plan accordingly. In the cyber domain, threat Tactics, Techniques and Procedures (TTPs) are constantly changing. One day we may have a distributed denial of service attack, the next day a phishing attempt. We could also have a drive-by download, a USB stick dropped in a parking lot or something else entirely new. The list goes on and on because new capabilities and TTPs are developed on a daily basis. Adversaries include well-resourced nation states and large online criminal organizations; however, even small groups and individuals can join the fray and have a tremendous impact. In some ways we are already at war. We have much to learn by studying insurgency and applying those lessons in cyberspace.
Reserve Forces may be more Capable than Active Duty Troops
In kinetic operations, reserve forces have always been at a distinct disadvantage, often equipped with older equipment and less frequent training opportunities. However, reserve personnel are at their best when their civilian careers match their military roles. Truck drivers are a textbook example. Great opportunity lies for the military to recruit Reserve and National Guard personnel who are experts in cyber security; and we need to. The high churn of active duty forces between assignments inside and outside cyber continually degrade their skills. Embracing the value of reserve cyber experts, and civilian cyber experts, bears great promise for the future cyber workforce.
A Computer Can Be Turned into a Brick
Cyber Attacks can have devastating real world effects. We tend to think in terms of lost or corrupted data as a result of an attack, however computer hardware can be destroyed, or “bricked,” by corrupting its internal firmware and other means. This happens fairly rarely today because many malicious applications are tied to online crime and avoid harming their host. However, we should assume that our adversaries in a time of war will not be reluctant to destroy our information systems, weapon systems, and our Nation’s critical infrastructure, including financial systems. Beyond just disabling or destroying computer hardware, software, and data, malicious software can also cause significant physical damage. Experts have warned of vulnerabilities in the SCADA systems which control water, power, communication, transport, and manufacturing systems. Stuxnet provided a very clear example of such capabilities by reportedly destroying centrifuges used to enrich uranium. We shouldn’t forget that our weapon systems are heavily reliant on computer technology and may be vulnerable. The recent virus found in a military drone command center may be a warning of things to come. Our military depends on its technical advantage. If we lose our communication and information processing systems we will be severely degraded as a military and possibly rendered combat ineffective.
Cyber Terrain is more like a Parallel Dimension than Physical Space
We have been navigating physical terrain since birth, but networks aren’t physical space. Cyberspace crosscuts the physical domains of air, land, sea, and space, and touches at myriad points. Networks aren’t physical battlefields. Attacks can transit the globe at near the speed of light. Battles can be won or lost in milliseconds. In this virtual world, distance approaches zero. Enemies can teleport, appearing from numerous locations around the globe in the blink of an eye. Cyberspace is a man-made domain, it is constantly shifting as new nodes are added and others disappear. Grid squares can move (by changing a network address) or lie (spoofing a network address). Laws and military doctrine were written with physical boundaries in mind, but national borders in cyberspace are intertwined in complex ways unanticipated by the law. Unit boundaries, measured in kilometers of dirt are frequently meaningless. A cyberspace attacker may instantly appear in a brigade operations center in Afghanistan or a game console in New Jersey.
Adversaries Can Easily Camouflage, Deceive or Disappear
Deception is easy on the Internet. Identities can be spoofed or stolen. Age, date of birth, gender, appearance, and marital status are all malleable. Adversaries can operate invisibly or leave little trace behind by cleaning logs. Attackers may disappear and reappear instantly on the other side of the world, by simply changing network connections or paths.. History itself may even be rewritten by altering system log files or other data. The nature of the Internet allows many people to share the same identity (by sharing the same authentication credentials) and one person to appear as many (by creating numerous user accounts). Trust is often misplaced. The end result is that is that things aren’t necessarily what they might appear to be in cyberspace.
The Law of War and Cyber Policy Cannot Keep up with Technology
The law of war is well understood around the world and briefed to every service member. The law of cyber war is unsettled. Most legal professionals and judges have limited understanding of technology. One leading cyber warfare legal expert describes the situation in stark terms – explain technology to lawyers at the third grade level and to judges and juries at a first grade level (Clark’s Law). Of course, technically savvy legal experts and policy makers exist, but the rapid advance of technology guarantees law and policy will lag years, if not decades, behind what is technically feasible today. For the foreseeable future, military leaders will be constantly challenged with navigating this legal and policy morass and petitioning policy makers for updated laws.
Your Weapon Systems May Work Once, Twice, or Not at All
If you’ve seen Star Trek, you are probably familiar with the Borg. In numerous episodes the Enterprise crew attempts to defeat borg drones by calibrating their phasers. However, the Borg quickly adapt and the phasers are no longer effective. The same holds true for cyber weaponry.
We see this cycle repeated on a daily basis. New vulnerabilities and exploits are discovered and weaponized, but once used or disclosed vendors will patch systems, antivirus companies will issue new signatures, and security professionals will develop countermeasures. Unlike our M16’s, we cannot be assured that cyber capabilities will work after first use, if at all. The result is an ongoing cyber arms race and a burgeoning malware economy to acquire newer and better techniques.
Any Sufficiently Advanced Technology is Indistinguishable from Magic
Without an understanding of technology and networks, computers are just magic black boxes that sit on our desks. In the kinetic realm, warfighting leaders are developed over decades of developmental assignments, operational experiences, and training programs that are among the best in the world. While work is ongoing to develop cyber career paths, we are in the early stages. At the same time, there is a common misconception that “leaders are leaders” and that anyone can effectively lead cyber warfare units. Cyberspace is a new operational domain, and as we have tried to illustrate in this article, many of our instincts are wrong. The generalist leader model, where everyone is replaceable, may work within an operational domain (Air, Land, Sea, Space, Cyberspace), but leaders forced into other domains are at a distinct disadvantage, at best. There is a reason why we don’t place Army officers in charge of aircraft carriers. That being said you go to war with the Army you have, not the Army you wish you had. We need to fight to understand the domain of cyberspace and learn to effectively lead cyber warriors.
A Seventeen Year Old can Command an Army
Adversary leaders in cyberspace need not be seasoned fifty year old General Officers, and unless they are part of a traditional nation-state military organization, they almost certainly will not. Adversary leaders will likely emerge based on merit and possess significant experience online. Some will possess traditional schooling, but others will be self-taught and may have tapped the exceptional free resources available online from organizations including Wikipedia and Khan Academy, even MIT or Stanford. Some will have experience in leading distributed teams, possibly Clan Armies in online games and virtual worlds. Their weapon systems can be actively controlled or passively controlled via pre-programmed logic. Lawyers won’t be involved (a major agility advantage), and organizational structures will be more like a fluid New Model Army than a rigid hierarchical organization. As a result, adversaries will be very agile. The command post, where a commander monitors maps and receives briefings from their staff to make decisions often has little utility when fighting in the cyber domain. The speed of decision making required is beyond human capacity. In an era where a network packet can travel around the globe in milliseconds carrying an attack payload, by necessity, algorithms will increasingly do much of the fighting. Future cyber warfare will be far more like high-speed trading on Wall Street than briefing the commander on potential courses of action.
You Can’t Fire Cannons at the Internet
The infrastructure of the Internet is remarkably resilient. The ability to route around physical destruction is built into the Internet’s design. There is no Internet kill switch, but there are certainly weaknesses that could be exploited by a determined adversary to disrupt its proper function. When we move above the physical and logical infrastructure planes which comprise the Internet, we should think in terms of specific end users and computing systems. Spear phishing via email accounts has long proven to provide precise means of targeting end users. Drive by downloads of malicious software hosted on compromised websites is another well known way to target users. Social networking sites are yet another means of spreading malicious software and targeting users. Attackers can destroy companies overnight by humiliating leaders or stealing intellectual property. However, as we’ve discussed elsewhere in this article, false identities can be easily created, complicating targeting. Attacks also bring the real possibility of collateral damage and limited effectiveness. For example, data can be replicated on multiple servers in various locations around the world, so even a successful attack may be quickly negated as a mirror-image of the server is brought online.

Figure 2: Any networked device, including consumer electronics such as the digital picture frame, is a potential enemy combatant. (photo source: Wikimedia Commons)
An Enemy Combatant can be the Digital Picture Frame at Grandma’s House
In cyberspace virtually any computing device is a potential threat or ally. The rise of the Internet of Things, where many physical items will include computer processors and network connectivity, means we will face many potential combatants in cyberspace, see Figure 2. These devices may be compromised during design, manufacture, or anytime thereafter. Imagine if attackers discovered a flaw that allowed successful compromise of a common gaming console. We could be fighting an Army of tens of millions of PlayStations. This scenario isn’t out of the realm of the possibility; botnets of more than one million hosts exist today. Research indicates that bot armies can be rented for as little as nine dollars an hour. Your next combat kill may be a robot or a refrigerator.
You Probably Won’t Know Who is Shooting at You
In Internet combat you likely won’t know who is shooting at you. Anonymity was built into the design of the Internet. Network traffic is comprised of packets that need only a source address and a destination address. Theoretically, the source address would be that of the attacker and the destination address would be the target. In reality, the source address can be easily spoofed and set to any network device anywhere in the world. To blindly return fire, you could, and most likely will, hit an innocent. Even if the source address is accurate, the attacker could have routed the attack through numerous intermediary nodes, some of which are in the United States, in allied countries, or in countries with no desire to help the US military. In most cases, attribution requires tedious step-by-step analysis—walking back node-by-node to the attacker—and patience to cope with legal and bureaucratic barriers at every turn. There are even anonymity networks that are designed to protect against such attribution attempts that are remarkably resistant to analysis. Note that these anonymity networks, and the design of the larger Internet, were designed to allow open sharing of information, not to facilitate cyber warfare attribution. As a result, accurately identifying aggressors may take weeks, months, or even prove impossible.
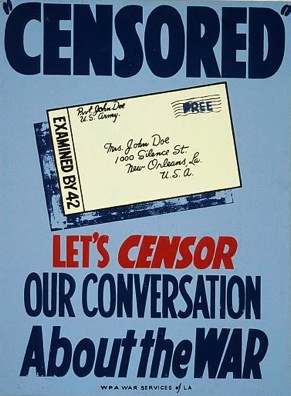
Figure 3: WWII-era censorship poster from the U.S. Library of Congress. Censorship in the digital age is far less simple.
Digital information is slippery. Even the most aggressive attempts at limiting disclosure are not foolproof. Previous attempts at censoring communications, see Figure 3, look quaint in an era where an easily concealed 20 dollar thumb drive can hold 21 million pages of text. Encryption provides an all but impenetrable layer to mask malicious activity. Military censorship is an uphill battle that will only catch a few honest or inept people; true threats will likely take much longer or may never be detected. Censorship attempts also have a counterintuitive secondary effect—they often make the information more available. Coined the Streisand effect, attempts to remove information from the Internet tends to increase proliferation. For example, attempts to prevent dissemination of Wikileaks data (that was widely available online) only drew additional attention to the disclosure and prevented law-abiding Department of Defense personnel from studying the documents. To compound the problem of information disclosure, social networking sites entice disclosure of sensitive personal information from government employees and service members, opening the door to misuse.
Calling for “Cyber Support” is not the same as “Calling for Fire”
There is a trend now to consider cyber operations as being analogous to artillery fire missions. Fire missions are straightforward: get on the radio, pass along target grid coordinates, and moments later artillery rounds come raining in. The same isn’t true for cyber operations. As we’ve discussed earlier, cyber weapons aren’t guaranteed to work and even if they do their controllers may be reluctant to expend them against many objectives. Targeting is difficult and may span multiple countries, far beyond the sector of a tactical unit. Even a single bit in error could result in collateral damage. While details of government cyber operations are not publicly available, civilian red team and penetration testing operations require extensive, time consuming planning. The murky law of cyber warfare compounds the problem, whereas the law of kinetic warfare is largely settled. Lawyers will be involved in cyber warfare, and you can be certain the timelines of many cyber operations will rarely approach the responsiveness of simple artillery fire for the foreseeable future.
Like it or not, Geeks are Warfighters
Cyberspace is the domain of technical experts, in some ways a hybrid of traditional Signals Intelligence and Communications domains, but in other ways altogether different. This cultural shift is uncomfortable for many. Technologists have historically not fared well in the military. Those with technical expertise may be reluctant to lead, lest their skills atrophy, and those without technical skills may not like the shift in power and status to the technologists. Human resources processes are a significant part of the problem. Military human resource systems were designed for interchangeable personnel in well defined specialties. Current guidelines in the Army require frequent moves and check-the-block career progression. Manning documents are based on outdated and slow-to-evolve specialty codes. Given the critical shortage of cyber security professionals, restrictive manning documents artificially constrain available positions to only a small, and often ill prepared, percentage of the force. One potential solution is the creation of a Special Forces-like model where candidates can be rigorously assessed and the best can be selected from across the force.
Conclusions
Cyber operations, alone or in concert with traditional kinetic operations, are intrinsic part of all future warfare. This article was designed to highlight how our physical world instincts often fail us when thinking about cyberspace. Cyberspace operations present both a critical national threat and a significant advantage to the defense of our country. By better understanding cyberspace and its laws of physics we will be better prepared for both.
The views expressed in this article are those of the authors and do not reflect the official policy or position of West Point, the Department of the Army, Army Cyber Command, US Cyber Command, or the United States Government.
About the Author(s)
Comments
I don’t like this article for many reasons but the most basic reason is that it equates the Maginot line with network defense. Current cyber defense techniques are very dynamic and not static like the Maginot Line was at all. The article misleads the reader by presenting computer network defense as futile effort because TTP's are constantly changing. On the contrary network defense can consistently repel malicious attacks when trained professionals are on hand to effect proper security and they have a sound strategy in place to work from. I am really baffled that we still have the mind set expressed in this article. Things are not as grim as this article makes it seem.
There are many things about this article that I disagree with. But number one on my list is that you cannot have a computer network installation and data that is totally secure. I would like to say that I am not an IP specialists, but I am as serious a software engineer and architect as you are likely to meet.
First let's separate the out the insolvable problems. Tor and bot networks. Enough said.
Network and data security then. Lets start with a single precept. You buy a new computer, scramble whatever is on the hard drive and completely install a new sealed verified OS from a media. Put it in a safe and the computer is secure. However it is not really very useful. Connectivity is also relatively easy. Buy a router and run some Ethernet cabling. Disable reading/writing external media on every computer. Remove the ability to change executable permissions. Run all network traffic 1024 bit encrypted or much greater. Or even better add in PK protocols over the top. Extend indefinitely, buying lots of safes and it is still secure.
Removable media is also fairly straight forward. Rewrite device drivers. Encrypt all disk information. Removable media must then have encrypted check sums on each sector and for the media as a whole. Everything onto and off of those devices are only usable on the installations computers. Anything not adhering to the designed architecture causes alarm bells and flashing red lights. Need to get a PP presentation out? Limit the access to boxes that can handle writing unencrypted information to media. No encryption related devices allowed out of the building. Other information access points can likewise be controlled.
You can control the pipes connecting the secure network to the external world. PK protocols, serious encryption of traffic, propitiatory handshake protocols overlaid. Disable all tunneling protocols. It is only limited by the number of CPU cycles you are willing to throw at it. How does anyone even figure out an attack vector on such a system? Sandbox everything. Decrypt the information. Scan however you want for as long as you want. Remove execution privileges from everything. Encrypt to the site specific standard. On and on and on.
The approach is scalable as demonstrated. It then is only a matter of discipline and will to keep the site and its data secure.
But the majority of the items on the list are solvable by a combination of hardware, software, and processes.
I think it would be more helpful, frankly, if the author's spent more time reminding us how much alike the information environment is to the other environments and domains in which we operate. Adding to the litany of different communities chanting "look how different we are" is tiring, not effective, and generally wrong.
We train military members, as a matter-of-course, to operate in various environments. To live in the cold, to pick routes in the jungle, to gain a position of advantage in the mountains, to camouflage themselves in the desert, to deceive in the urban.
Is this somehow different in the information environment? Hardly. The author's are right - we are operating in the information environment right now, we are competing in it right now, regardless of whether we want to or not. What we have not done is make this reality intellectually accessible. Concentrating on similarities is more helpful than concentrating on differences.
For example, operations in the information environment right now are all about defense - OPSEC, control, etc. We have set up FOBs in the information environment. We are concentrating on controlling static points while the environment swirls around us. Static defense doesn't work - we need to stop being information environment Fobbits.
We leave tracks in the snow, we leave trails in the jungle, we leave spoor in the information environment. We teach servicemembers to minimize tracks while maximizing the purpose for making them in the first place - maneuver. This is not different in the information environment, just the TTPs.
We camouflage ourselves in the jungle and in the urban environment, how do we do this in the information environment? No camouflage is perfect, we can be discovered - but we use camouflage to give us an advantage in the short-term, until springing an ambush.
What is an ambush in the information environment? What are fires in the information environment? Rather than focus on differences - even an idiot understands we're not firing a 7.62mm bullet in the information environment - teach the similarities. We exercise specific actions in the information environment to achieve specific effects. Why can't we call that shooting or firing if it increases understanding in the force and with decision-makers.
I want to disrupt a C2 network, I want to shut down the electrical grid, I want to explode centrifuges...I...WANT...TO...SHOOT...SOMETHING. How do I do that in the information environment? That's where understanding lies.
We communicate faster, but that doesn't not necessarily change what we are communicating. We can access more information faster, but that doesn't not necessarily change what information we choose to seek. We fight in all sorts of different environments, but that doesn't change the reasons for conflict, the willpower behind conflict, or even the relationships between offense and defense - just the TTPs for that environment.
In sum, the greatest successes I've witnessed in creating an understanding of the information environment has occurred when the environment is placed in a context that can be understood - the similarities.
My intuition about "cyber warfare" is that cyber is a domain where warfare can be waged, like land warfare or maritime warfare or air warfare.
My intuition about "cyber warfare" is that much of our defense against attacks in this domain fall in the realm of civil and commercial due diligence. Just standard cost of business precautions one must do in order to operate in that cyber domain. Airlines assume tremendous costs to ensure they can operate in a reasonably safe manner. Airlines could be far more profitable is they ignored those costs altogether, or could get some government agency to bear the burden of those costs on their behalf.
My intuition about "cyber warfare" is that the idea of calling this "warfare" and creating a Cyber Command and taking this mission primarily into the Defense Department will rob critical resources from other aspects of national defense that actually rely on military capability to be performed. That is not particularly smart. I think we should look to how we handled the opening of the Space Domain. Yes, much of our national defense required developing both offensive and defensive capabilities to optimize advantages and mitigate military risks within this new domain. A percentage of the military budget went to this new domain, reducing the percentages to all other domains by that amount. But as a nation we created a new civil agency, NASA, who had the lead for the space domain. Not everything NASA does goes toward our national defense directly, but indirectly they have provided the majority of the space capacity that DOD relies upon. By creating NASA we in effect expanded our defense capacity without either robbing from or adding to our defense budget. This is smart. As the Defense budget prepares to take a big hit we need to press for the creation of a civil Cyber agency to play the role for that domain that NASA has played for the space domain.
My intuition about "cyber warfare" is that not all violence or all forms of attacks are "warfare." Who commits the act and why they commit the act are critical factors, the nature of the act is interesting, but not the decisive factor. If an individual or even an organization (such as AQ) attacks the power grid in New England trough the cyber domain, it is most likely a criminal act. If a state commits that same act is it most likely an act of war. We need to be careful that we do not allow an over-militarization of our national cyber capacity lead us to a place where we begin to see all such attacks as "war" or "warfare." They aren't.
My intuition about "cyber warfare" is that our military needs to be able to maximize the cyber domain for the conduct of all manner of warfare, from very regular to very irregular - and that we need to be able to conduct all of our missions across that same spectrum even when, for whatever reason, our own cyber-based capabilities are denied. To me, this should be the primary focus of Cyber Command. Let the new civil cyber agency worry about taking lead on the rest.
Those are my intuition about "cyber warfare" - but as the authors point out, I am probably wrong.
Overall a good article, but despite learning a bit from reading this I also disagree with some of the points the authors made. For examples the laws of physics are laws of physics and I see no evidence they have been turned on their head. Just because a weapon can be produced faster doesn’t mean a law of physics’ has been violated. It simply means we’re constantly developing upon our knowledge base and using that knowledge more effectively.
The authors tend to use military lexicon where it isn’t appropriate, which is common in our ranks. We now call money a weapon, when in fact money is money, and money can be used to influence a variety of outcomes, and we can wage economic warfare, but that doesn’t make money a weapon any more than information in itself is a weapon. Both can influence desired outcomes, but are they weapons? Is that the best way to think of them, or does using that paradigm limit our view of how these means and ways can be employed? On the other hand a virus, worm, etc. that causes damage should it be categorized as a weapon? In this case they’re information packets (instructions) that are intended to harm. I think this gets after the author’s point about lawyers and judges being behind the power curb.
I think the authors are wrong when they said military planners could rely on a relatively fixed threat doctrine. This is a typical conventional army view because much of the Army was focused narrowly on the Fulda Gap scenario, yet the Cold War was never waged there, it was fought globally and in many regards the threat doctrines were the same type of irregular war we’re fighting now, and there was even some cyber operations employed (before cyber was cool). TTPs have always been constantly changing throughout history, but that doesn’t invalidate their important point that TTPs are also constantly evolving in the cyber domain, and perhaps at a much faster rate than we’re accustomed to.
The human resource management challenge they address is very real, but perhaps especially crucial for so called cyber warriors. Perhaps the best answer is not to have uniformed service members do this, but to recruit DOD civilians. The only military grade that allegedly allows a service member to focus on their technical specialty is the Warrant Officer, but the reality is the Warrants have relatively recently pursued a management system that too closely parallel’s regular officers by creating a check the block career path. Why can’t we use civilians as our cyber warriors? Reservists don’t fit the bill if the assumption is we can suffer a cyber-attack at any time (and the authors give numerous examples of what could happen). Can we really afford to wait for a response until we can mobilize the reservists?
I think the authors could have strengthened their article by adding how Autnomous employs cyber operations and how the Russians employed it in Georgia. Those are the not the end all, be all examples, but these examples and others would add further urgency. Despite the minor critical comments I made, I thought it was a great article.
